
VeraCrypt 1.26.7 update brings major changes: read this before updating
It took the developers of the open source encryption software VeraCrypt more than 18 months to release VeraCrypt 1.26.7. It is a big release that addresses several issues and makes other important […]

Google Authenticator's mysterious security update does not enable end-to-end encryption
Google has released a new update for its Google Authenticator application. The changelog reveals that Google "added device encryption to storage of secret value". Users who have hoped that Google would integrate […]

Dropbox acquires cloud encryption service Boxcryptor
The founders of the cloud encryption service BoxCryptor announced this week that Dropbox has acquired the company's intellectual product. According to the announcement on the official Boxcryptor blog, Dropbox acquired IP technology […]

VeraCrypt 1.25.9 Encryption Software fixes BSOD on Windows
VeraCrypt is a popular open source encryption software that is based on the abandoned TrueCrypt application. VeraCrypt 1.25.9 was released on February 19, 2022 to the public. The new version of the […]

VeraCrypt 1.25.7 update reintroduces support for Windows Vista, 7 and 8 systems
The latest version of the open source encryption software VeraCrypt brings back support for the operating systems Windows Vista, Windows 7 and Windows 8. The developers of VeraCrypt released VeraCrypt 1.25.4 in […]

VeraCrypt 1.25 drops Windows 8.1 and 7, and Mac OS 10.8 and earlier support
VeraCrypt 1.25, a new version of the open source cross-platform encryption software, is now available. The new version is the first release of the application for over a year; the last release […]

WhatsApp encryption - does Facebook want to overcome it?
Facebook has confirmed that they have hired a team of researchers to figure out a way to get past end-to-end encryption. One of the privacy features that we appreciate about the WhatsApp […]
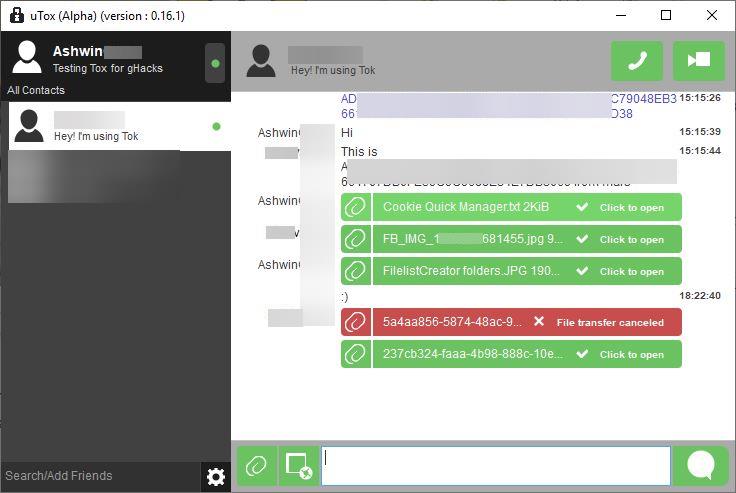
Tox is a peer-to-peer instant messaging protocol with end-to-end encryption, voice calls, video calls and file transfers
Instant Messaging is one of the most popular forms of electronic communication. You don't have to pay extra fees (not counting data charges) for chatting with family members, friends or colleagues regardless […]

Speed up the migration of encrypted drives to another software
DiskCryptor has been my go-to program on Windows when it comes to encrypting entire hard drives and the system partition since 2012. Development stopped, however, several years ago. While the program works […]

VeraCrypt 1.22 encryption software update released
VeraCrypt 1.22 is a new version of the popular cross-platform encryption software that parent company Idrassi established as the primary unofficial successor of the encryption software TrueCrypt. TrueCrypt development ended under mysterious […]

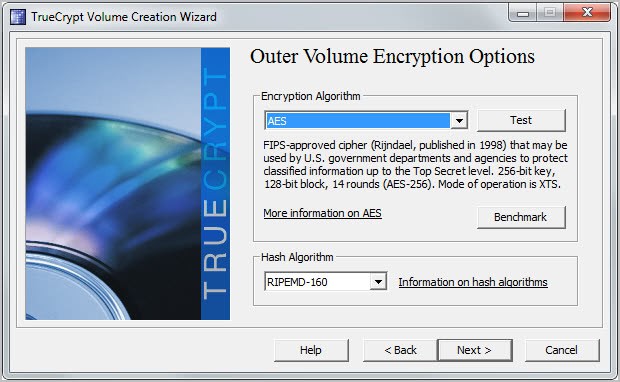
A second look at VeraCrypt, an unofficial TrueCrypt successor
When the TrueCrypt developers announced that they would quit developing the encryption software because of it not being secure, many users of the software did not know what to make of the […]
TrueCrypt may live on after all as CipherShed
The developers of TrueCrypt made the decision to retire the encryption software a couple of months ago. The reason given by them was that TrueCrypt was no longer secure and that users […]

Quick Crypt creates self-expiring encrypted files
Quick Crypt looks on first glance just like many of the other file encryption tools for Windows. You can use it to encrypt files using 256-bit AES encryption, and also decrypt those […]

Secryptor file encryption software with Dropbox support
While it is often best to keep files on the local computer only and avoid cloud storage, especially for important files, it is sometimes not possible to do so. Maybe you need […]
No backdoors found in first part of TrueCrypt Audit
The revelations of Edward Snowden's leaks confirmed that security agencies spend time and money trying to undermine cryptographic software. Potential backdoors in cryptographic software or protocols would be disastrous, and that is […]
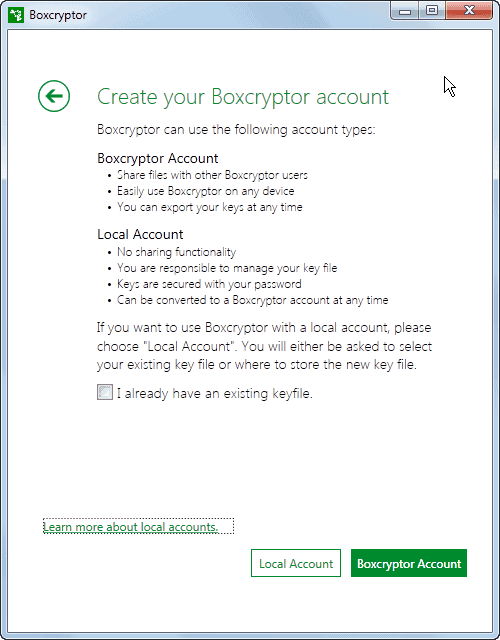
Cloud encryption solution Boxcryptor launches local key feature
We have covered the cloud encryption solution Boxcryptor before here on Ghacks. First in our initial review of the service back in 2011, and then again when the company released its Chrome […]
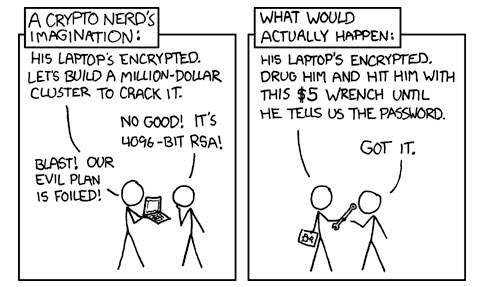
Why you should encrypt your PC fully
What is the worst thing that would happen if someone steals your PC? I'm not talking about the financial loss here but about the data that you have on your computer system. […]
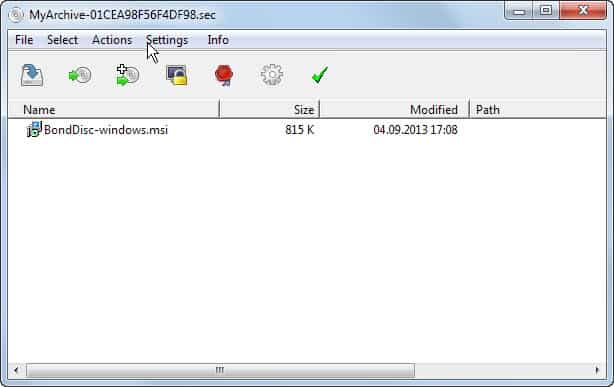
Put important data in a RAM-mounting encrypted data archive with Bond Disc
Encryption is a great start to protect important data against prying eyes. Computer users have an arsenal of tools at their disposal to do just that, from built-in solutions like BitLocker to […]
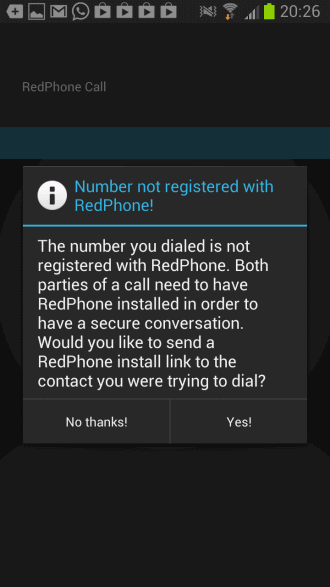
Encrypt Android phone conversations with RedPhone
The Prism surveillance scandal has shown that the NSA and other agencies can tap into most communication channels. One of the proposed solutions is encryption and here especially open solutions that anyone […]
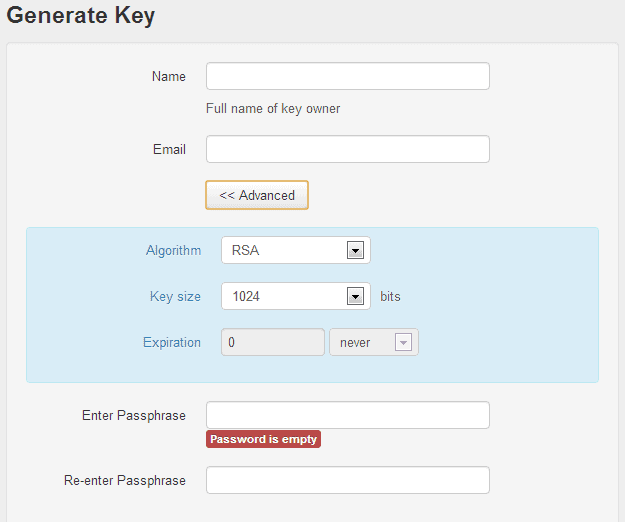
Mailvelope: use OpenPGP encryption on Gmail, Yahoo, Hotmail and other webmail services
If you prefer to use a webmail interface such as those provided by Gmail, Hotmail or Yahoo! Mail, you probably know that you cannot really secure your data directly when you are […]

Mailpile: private, secure, open source, locally-run email service
PRISM was a wake-up call for many even though it is still not really clear how extensive the spying, logging and wiretapping really is. One reasonable approach to the issue is to […]
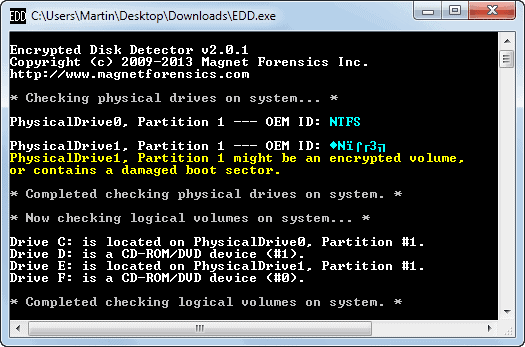
Encrypted Disk Detector finds encrypted partitions on PCs
Encryption is one of the most effective ways of protecting data against third party access. One popular option for home users and businesses alike is to encrypt part of or all of […]
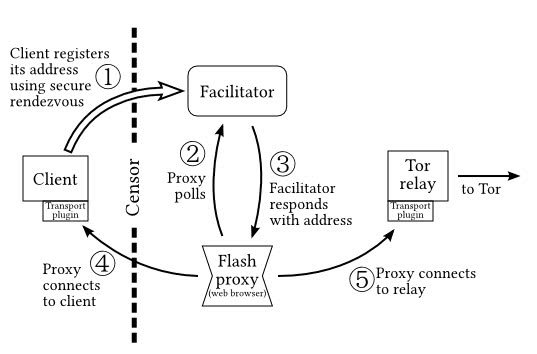
Flash proxies: circumventing Internet censorship with Tor
Depending on where you live, you may not be able to access select websites or services available on the Internet. This is not limited to countries where you would expect Internet censorship […]
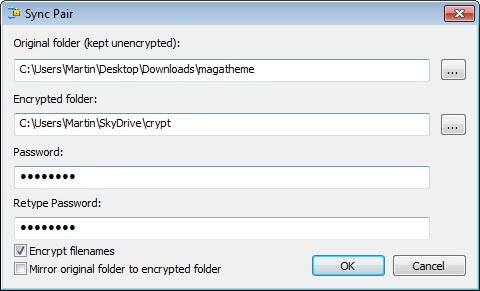
CryptSync: upload only encrypted files to online storage services
Several cloud storage services use encryption to protect data of user accounts from being accessed by third parties. While this may be reassuring for many users, some prefer to add encryption of […]
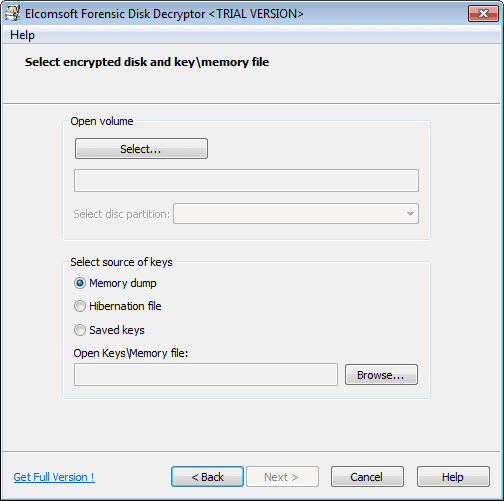
Forensic tool to decrypt TrueCrypt, Bitlocker and PGP containers and disks released
One of the things that you can do to protect your data is to use encryption. You can either encrypt individual files, create a container to move files in to or encrypt […]
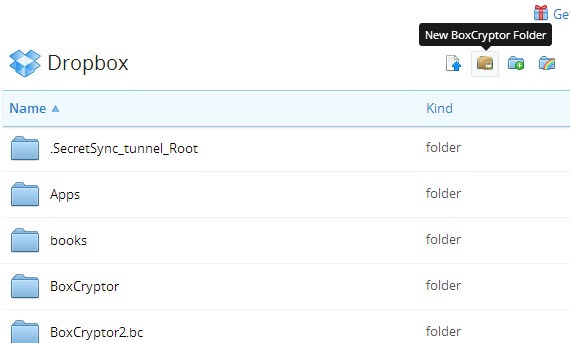
BoxCryptor for Chrome plugin
Remember Boxcryptor? The program, available for various operating systems including Windows and Android can encrypt files that you synchronize with online storage solutions like Dropbox, Google Drive, Box and other cloud storage […]
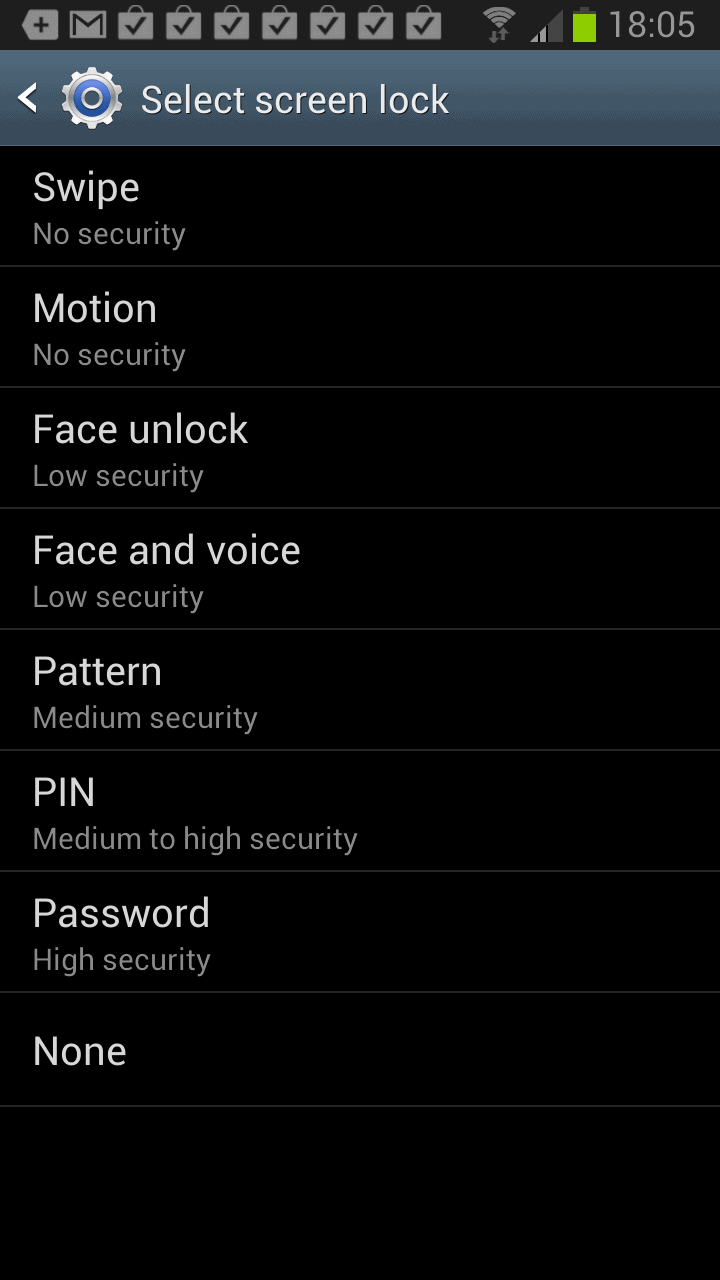
Encrypt all data on your Android phone
One of the first things that I decided to do of after getting my new Samsung Galaxy Note 2 smartphone was to protect the data stored on the phone's memory space from […]
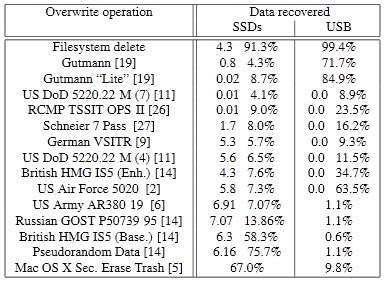
Encrypt and erase to delete data reliable on SSDs
The security of data on Solid State Drives (SSDs) is not only important for government agencies and enterprises, but also for end users. Even if you do not plan on selling or […]
Encrypt Files and Folders in Windows 8 with EFS
For those using Windows 8 there is built-in file encryption, called Bit-Locker, available, but only if you are using the Pro or Enterprise version of the operating system. Â However, every version of […]
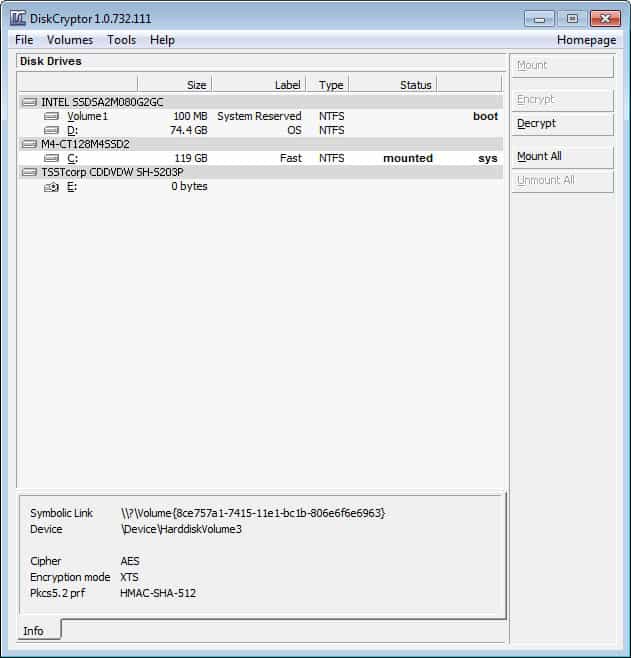
How to encrypt partitions with DiskCryptor
I have been using TrueCrypt ever since I discovered the encryption software years ago to protect data from being accessed by third parties. It is a great open source software that has […]
The Importance of Using Mobile Encryption
This might come as a surprise to you, or perhaps even alarm you, but on the city of London’s public transport system alone, around 200 laptops are handed into lost-property offices every […]
Will Bitlocker's Security Flaw Remain in Windows 8?
I write a lot about security, and about Microsoft's Bitlocker drive encryption technology. Frankly I really like Bitlocker because it is easy to deploy and because its tied to a TPM (Trusted […]
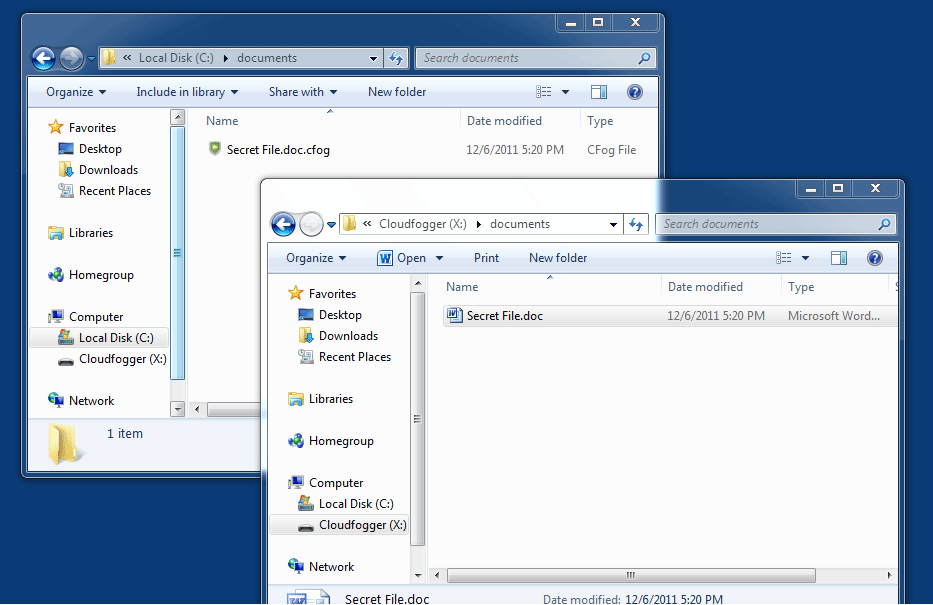
CloudFogger, Secure File Storage In The Cloud
Services like Dropbox, Microsoft OneDrive or Spideroak make life more comfortable for users who work on different devices regularly. They are file sync and online storage solutions that act as backup storage, […]
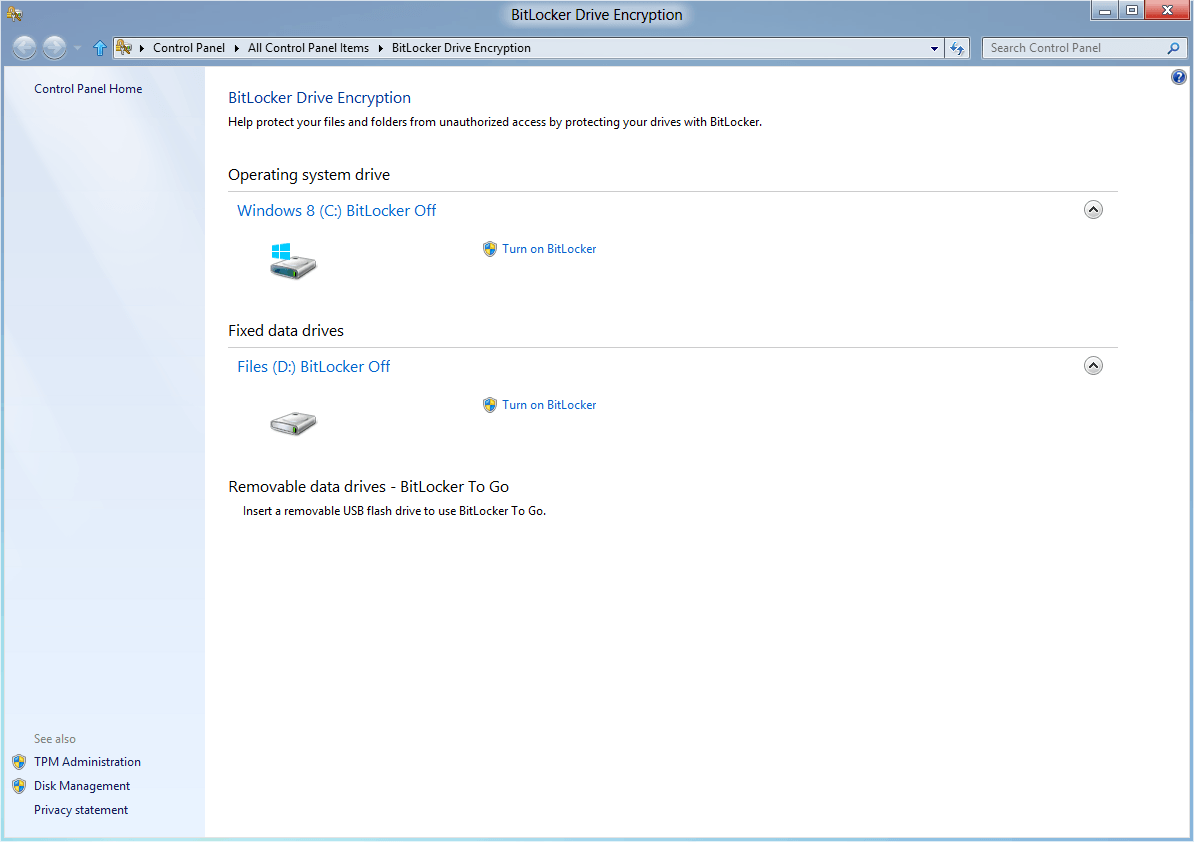
Using Bitlocker in Windows (Best Practice Guide)
If you use a laptop for work, or it you carry important or sensitive data with you then it should be encrypted. Put simply the repercussions of not using encryption are far […]

DataLocker, File Encryption For Windows, Mac, iOS
With cloud hosting taking over much of what we are hosting locally right now in the next ten years or so, it becomes important to protect your remotely saved data from unauthorized […]
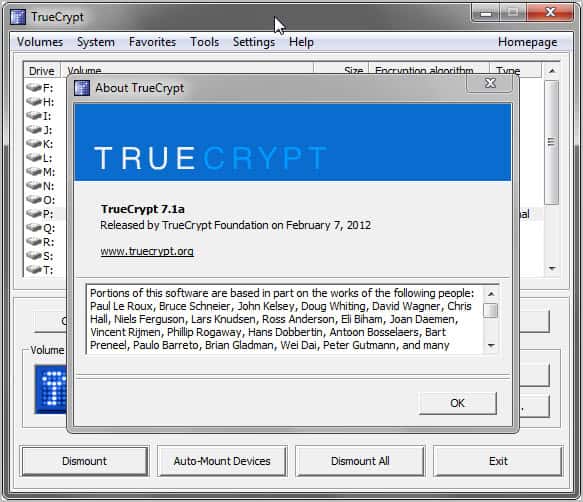
Disk Encryption Software TrueCrypt 7.1a Released
I have been using the open source encryption software TrueCrypt for a long time to keep my data secure on connected hard drives. The program has evolved over the years, and can […]

Protect Files From Unauthorized Access With Encoding Decoding
Full disc encryption or encrypted container files are useful to prevent unauthorized access to a larger number of files. This may feel like overkill though if you only want to make sure […]
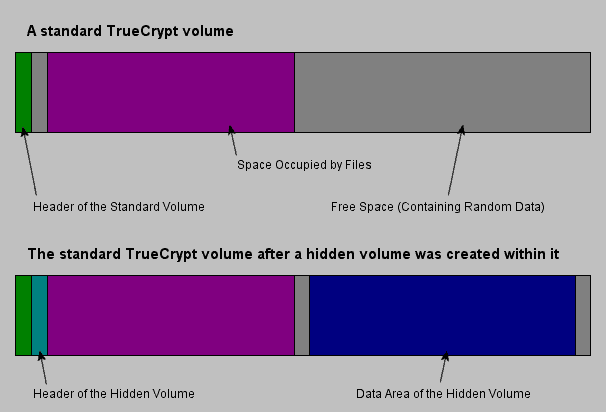
How to Create a Hidden Encrypted Volume With True Crypt
A judge recently ordered a US citizen to decrypt storage space on a computer so that police forces could analyze protected files on the system. In this particular case, the defendant was […]

Are Biometrics the most Important Portable Feature?
As we carry more devices around with us, smartphones, tablets, netbooks, ultraportables, than ever before and now I'm wrondering if biometrics are fast becoming the must-have addition for mobile computing in the […]
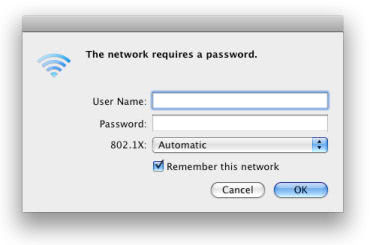
Why You Should Encrypt Your Wi-Fi
If you go out to the computer store and buy yourself a new router and take it home, you’ll probably find that it will work straight out of the box. Most these […]

