Using Bitlocker in Windows (Best Practice Guide)
If you use a laptop for work, or it you carry important or sensitive data with you then it should be encrypted. Put simply the repercussions of not using encryption are far too serious to imagine with substantial fines being probably the least significant to a loss of customer and market confidence being the worst. For a small company though the fines for not complying properly with data protection regulations and leaving information "in the open" can shut a company down. For the individual you could find that suddenly everything a criminal needs to steal your identity is in the public domain.
Note: Bitlocker can be found in Windows Vista and Windows 7 Enterprise and Ultimate editions
There are various encryption technologies available, many great ones for free, but it is becoming more common now for laptops to ship with Trusted Platform Module (TPM) chips. These chips help store encryption keys for Microsoft's Bitlocker full-disk encryption technology. Using Bitlocker means that even if a hard disk is physically removed from a computer, the data can never be accessed as the TPM chip on the computer's motherboard isn't able to verify the unlock password.
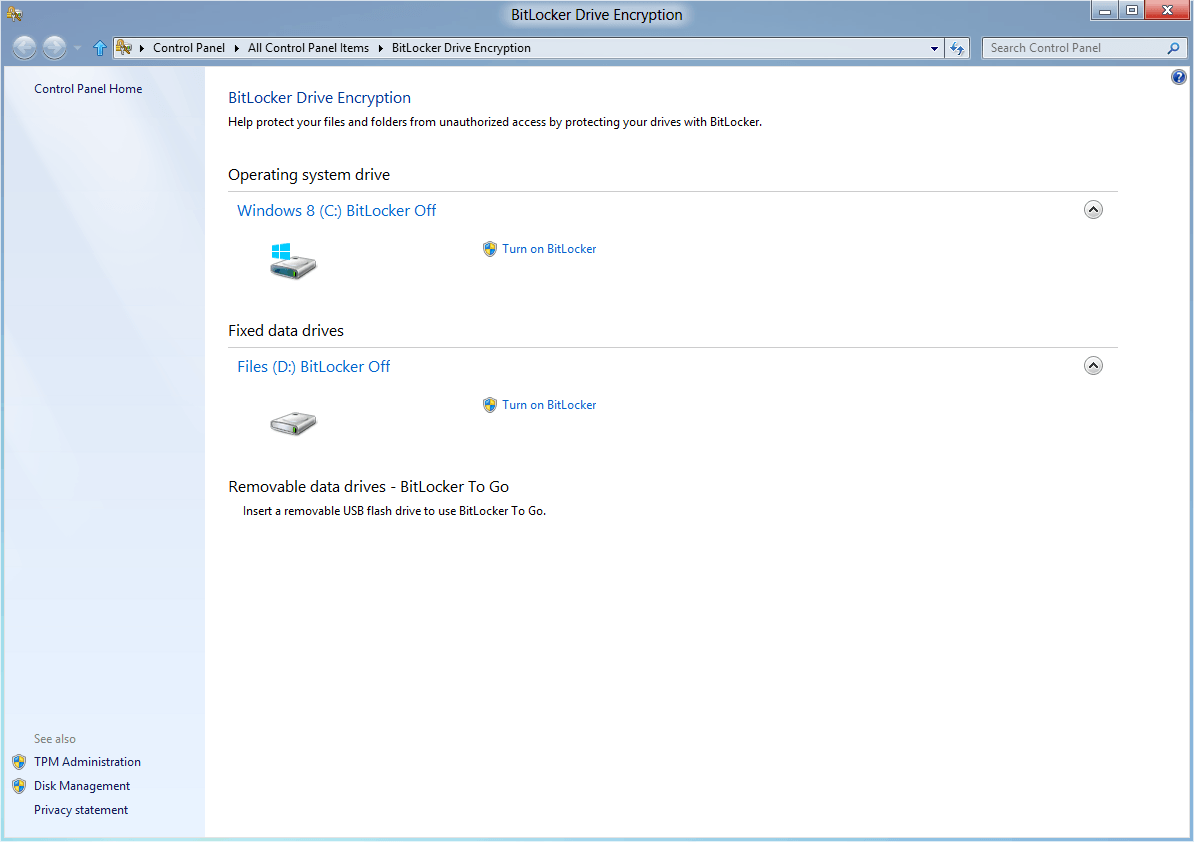
Bitlocker is a highly effective technology but like all encryption it needs to be used with care. If you have a TPM chip on your computer's motherboard then the full Bitlocker options are available to you and it is very easy to set up. In the main Bitlocker window you can choose which drives you want to encrypt. The main OS drive will always need to be encrypted so you will need to do this first, you cannot encrypt any secondary drives unless the main drive containing your copy of Windows is encrypted first.
Note: Bitlocker does not support dual-boot systems and you will find yourself locked out of your computer regularly under this circumstance.
As with most encryption technologies you will need to keep a copy of your unlock key. In Windows Vista and Windows 7 you have the choice of keeping it on a USB Pen Drive, as a file or to print it. Windows 8 adds the option of saving it to SkyDrive.
My personal recommendation, as someone who has used Bitlocker and even been locked out of my own computer by it due to a Startup fault with Windows, is that you should always keep a copy on a USB Pen Drive and a secondary copy in the cloud on a service such as SkyDrive. If you have a problem starting Windows for whatever reason, as I once did, you will be completely locked out of your computer unless you provide the proper unlock key(s); there will be one for each drive that is encrypted. You should keep this Pen Drive safe and carry it with you when you go away just in case (though it should always) be kept separate to your laptop for obvious reasons.
The copy in the cloud is there just in case you forget it, lose the Pen Drive or delete the key accidentally. From the cloud you can download a copy to another Pen Drive that you can then use to start your computer.
Bitlocker also offers additional security options that you might want to consider. These include automatically unlocking drives when a user logs onto Windows. If you know the password to access Windows, and that password is itself secure (usually a minimum of 10 characters and a mixture of upper and lower-case letters, numbers and symbols) then this will normally suffice.
For drives containing particularly sensitive data however you can set Bitlocker to require an additional password to unlock the drive, or to require the use of a smart card, if supported by your hardware with a slot loading or contactless smart card reader, to gain access. This can provide an additional level of security that might be very useful for research, military, health, financial or governmental use.
Remember that if you ever lose your Bitlocker encryption key file(s) you can go back into Bitlocker in Windows and save addition copies. If you do not then you face the prospect of being locked out of your data forever. Thus it is always important to use any encryption technology in conjunction with a secure but unencrypted backup. This might seem folly, but there are ample ways these days to keep very secure backups without them requiring encryption. Don't forget that almost no desktop PCs come with TPM chips and neither support nor require the full features of Bitlocker.
As an encryption technology Bitlocker is incredibly secure and for laptops it should be mandated in business. If your company is buying new or additional laptops soon, then a TPM chip should be very high up on the list of purchasing priorities for each one. If you use a laptop at home that you carry out and about and can afford the price premium that a TPM chip costs, then the use of Bitlocker is both incredibly simple to use and worth every extra penny for the peace of mind.
Advertisement
















Well, considering that the NSA and various other US-Agencies don’t need your key, you should really use this…