TrueCrypt may live on after all as CipherShed
The developers of TrueCrypt made the decision to retire the encryption software a couple of months ago. The reason given by them was that TrueCrypt was no longer secure and that users should move to other encryption products instead.
No further information were given at that point in time and rumors began to spread. This included forced cooperation with America's NSA, severe security bugs that the developers found in the software and rumors that the security audit of it was going less than well.
It is several months later now and things have not changed since. The second part of the audit, the crypto-analysis is currently underway and results will be published to the public once it completes.
TrueCrypt development has stopped however and while there is still a chance that one or multiple of the original developers will start to work on the project again at a later point in time, it seems unlikely that this is going to happen anytime soon.
A project that gained some traction recently is CipherShed. It is a fork of the discontinued TrueCrypt project which means that it is based on the same code.
According to project information, the TrueCrypt license allows the forking of the program if it is not named TrueCrypt or referencing it.
That's why the fork is called Ciphershed and not TrueCrypt2 or TrueCrypt++ or something like that.
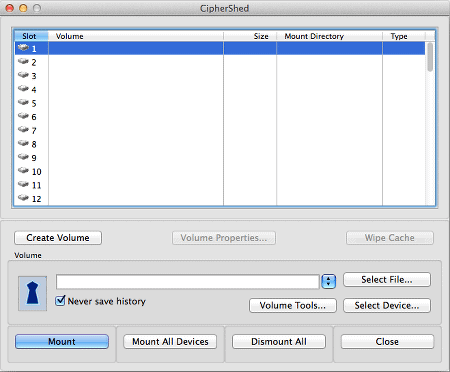
Downloads are not provided currently but a first screenshot shows how similar the interface looks to the original TrueCrypt interface.
The first version will be re-branded version of TrueCrypt 7.1a, the most recent version of the software. Binaries for Windows, Linux and Mac will be provided, and signed and verifiable binaries and compiled source code will be provided.
It is interesting to note that the project goals go beyond a mere fork. The project goals include efforts to secure the code "through audits, simplification and a secure architecture", and to cooperate with existing efforts such as the Open Crypto Audit Project. The developers plan to fix the vulnerabilities found by the security audit of TrueCrypt in the next release.
Additional information about the roadmap and the team can be found on the official project wiki.
Closing Words
While some users may not want to go back to TrueCrypt or any fork of the software, others may appreciate that the software will live on albeit with a different name and maintained by a different team.
That's not necessarily a bad thing though considering that the Ciphershed team is not anonymous like the TrueCrypt team was.
What's your take on this?
Advertisement














TrueCrypt isn’t insecure at all, there are two possible attacks from what I know, the one is firewire related … Not all people use or have firewire (like me) and the other attack was a cold boot attack which also works on android and many other devices/os.
I think it’s unrealistic that most people are affected buy this, so I won’t call it insecure at all. It’s a risk but not insecure if you not use firewire or clear your cache at shutdown.
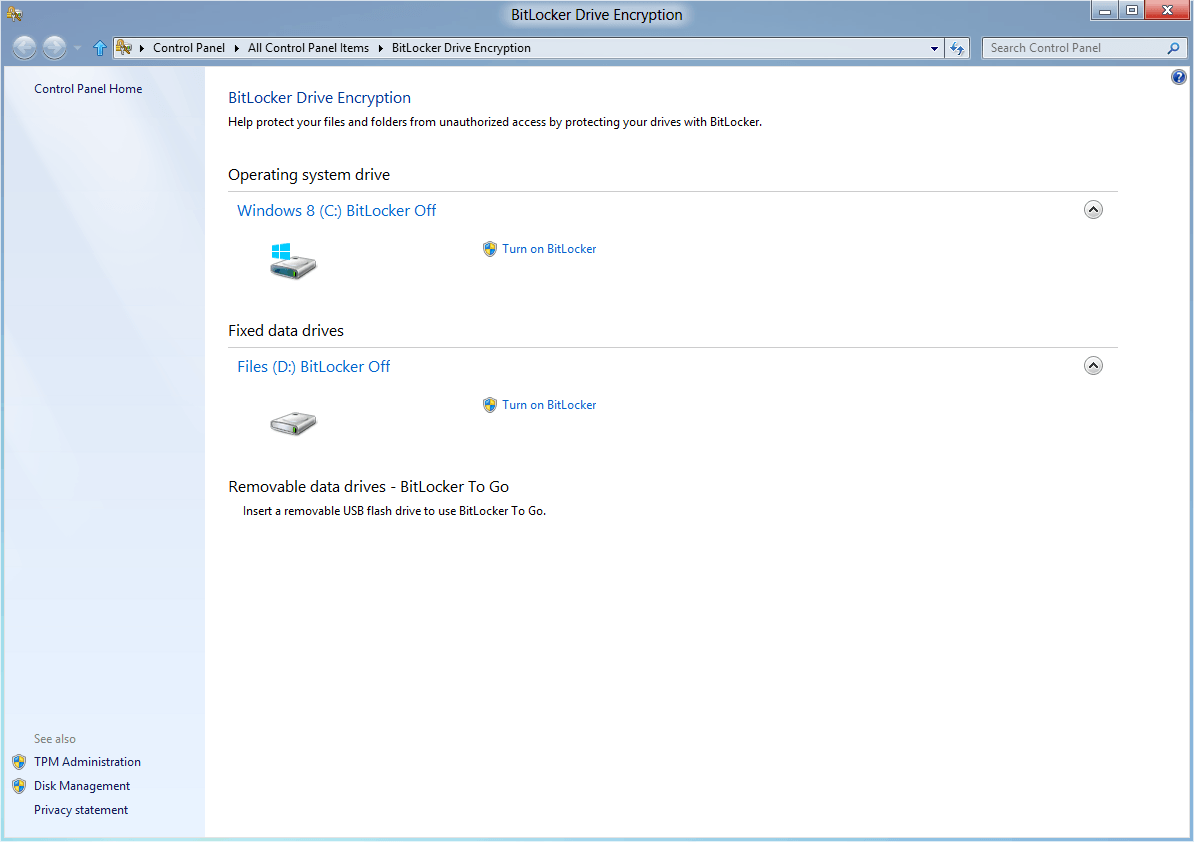
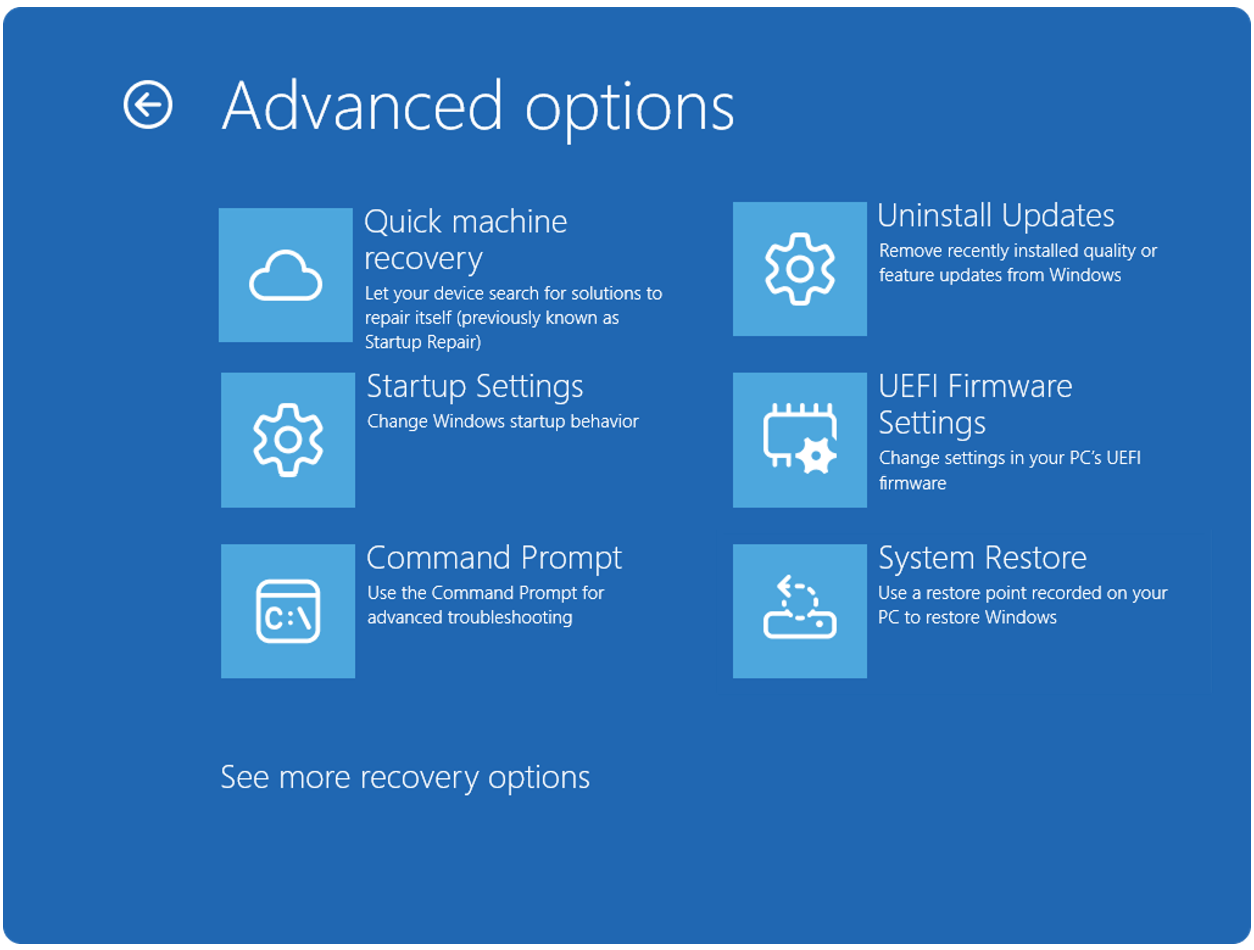
I think that story seems a bit over-hyped, nothing speaks against TrueCrypt, the only problem is that on newer systems like Win8/8.1 it not 100% use the internal mechanism like uefi system and such (but why use win8.x? – designed from and for kids :D) …..
I think we should seriously wait for the first final versions which can be inspected by crypto experts and than we can make some comments.
“Note that once TrueCrypt has been independently audited
it will be the only mass storage encryption solution to have
been audited. This will likely cement TrueCrypt’s position
as the top, cross-platform, mass storage encryption tool.”
https://www.grc.com/misc/truecrypt/truecrypt.htm
It is amusing, all of this talk about auditing- you have the source code, look at it. When was the last time you saw an outside security audit of a commercial product???
If you did see an “audit” from a large software company, could you believe it? “We had our secret source code “audited”, and we did great.” Ha ha. Even if they do find some serious problem, they are not likely to tell the customer first what is going on.
There is far more reason to be concerned trusting your information to software of any kind that is not open.
We now KNOW completely for sure that large companies and governments collude with one another to make our information and communications less secure in the interest of “security”
I do not expect the average idiot CIO or other “IT” idiots to take reality to heart- while poo pooing open software, and unwisely supporting the push for even more closed hardware and software, they will continue to trust companies that have lied to their customers and sold out their privacy.
If you do not see the source code, can not look at the algorithms used, and can not confirm there is no funny business going on, you can not be in any degree certain that software (or ANY TECHNOLOGY!!) is doing exactly what you think it does.
The ciphershed team are already calling their software “secure” on their website, even though it has not been audited AND they are making changes to the code that could accidentally break anything at anytime. Anyone who calls something SECURE without testing, knows nothing about programming. Even the TrueCrypt devs said that it would be better to re-write everything in order to get very familiar with every line of code. They said to please not ‘clone, fork and edit’. CipherShed ignored that and decided for full backward compatibility. Suggestions to make it new, lean, simpler and very secure were scorned. Beware.
Also, they moved all of their discussions off their forums and into mailing lists, secure VOIP, etc., and usually ignore any suggestions (better name, remove word “secure”, and more). This group is not being transparent, and they are already making implied warranties, ie., “Secure Encryption Software”, not Beta software. If they change one line of code, it’s Beta, not Secure. And we should trust them?
Amen to that. And there are other important questions:
– Who are the CipherShed developers?
– Where are the CipherShed developers based?
– Why can they only be reached via PR representatives?
If we have learned anything from past experiences it is that US citizens working from US territory can no longer be trusted. Just see what happened to Lavabit and other secure eMail providers over a year ago. At the time Lavabit’s founder Ladar Levison did the right thing by shutting down his service without notice. But can we trust others to act so honorably when they are coerced into compliance with requests by state agencies and when they are forced with the threat of severe legal penalties to shut up about this? Only now most people begin to realize that all those “anti-terrorist bills” that passed without much opposition can be (and were probably meant to be) used against Mr. and Ms. average-punter.
can’t edit sorry^^
please read here, seems they are working together
https://truecrypt.ch/2014/06/veracrypt-truecrypt-ch-working-together-towards-common-goal/
https://forum.ciphershed.org/viewtopic.php?f=5&t=52
The sucessor of TrueCrypt is VeraCrypt. But be careful, a lot of forks makes the round now, but as long there are no audits we can’t say it’s secure.
VeraCrypt not supports older TrueCrypt containers (or security reasons).
https://veracrypt.codeplex.com/
I’m with you Oxa, they need a better name.
But in this case I guess it’s better the techies are running the show, not the marketers.
Name is the last thing they (and we) should care about!
Wish they’d come up with a better name than CipherShed.
@Joe
The vulnerabilities are “developers move on” and “developers don’t give a shit anymore”. Anything else is just fear mongering by paranoids.
@OP
TC7.1a still works with Windows 7, so I am disinclined to look for a TC “alternative”. TC is as secure (or insecure) as it was before 7.2 came out. If there are real exploitable vulnerabilities, it will be found by a thorough audit, not by blind speculations and innuendo by internet ninjas.
Maybe when Win7 bites the dust in 2020, I will look for a new whole disk encryption software to replace TC.
I would not feel comfortable using this software until it has been completely audited and, even then, I would still wonder what kind of vulnerability caused the developers to pull the plug.
Yeah good luck for them but I wouldn’t use this before they meet those project goals of making sure it’s secure.
Happy about the possibilities but wait and see for now
I agree at this point in time. They have to build trust and can only do so by being fully transparent (which they want to be it seems).