How to verify link targets before you click on links

Yesterday's post about a new virus attack on Skype has shown that it is important to verify link targets before you click on the links. Because if you do not, you may end up with some nasty virus, trojan or other malicious software on your PC. What makes the Skype attack work that well is that it spreads by messaging Skype contacts, people that you probably trust not to send you malicious links or files.
Skype is obviously just an example, and the same thing can happen on sites like Facebook, Twitter, Google, other messaging apps, your mobile phone or email app as well. Even a computer system with up to date protection can become infected if a new type of virus is being spread that the antivirus software does not identify as a threat yet.
There are two main types of link disguises that you will encounter in these attacks:
- A shortened link that does not reveal the main target
- An HTML link that displays a different link in the text than it actually links to.
Shortened links
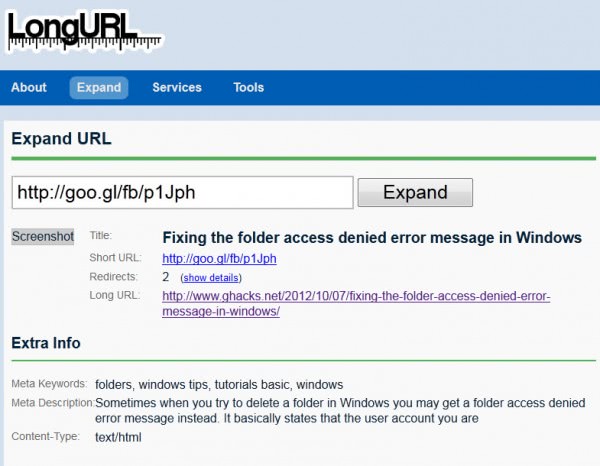
You can use web services such as LongUrl or CheckShortUrl to reveal link targets without clicking on the links to do that by yourself. All you need to do is copy the link, by right-clicking it and selecting copy, or highlighting it and using Ctrl-c to copy, to paste it in the form on one of the two sites linked above. You will automatically be taken to a page that reveals the long url here so that you know where the short link takes you before you click on the link.
Instead of using a web service to expand short urls, you can instead install and use a browser extension. These extensions are limited in reach, meaning that you usually can't use them to expand short urls that you encounter in other programs running on your system.
Firefox users can take a look at Long URL Please while Chrome users should try out Explode instead.
HTML links
The big issue with HTML links that throws many inexperienced users off is that the link text can look like an url as well. A HTML link consists of two main parts:
- The link target itself
- The link text
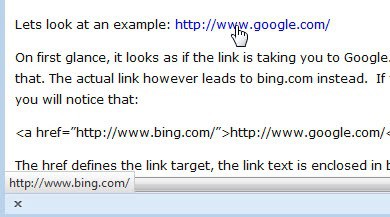
Lets look at an example: http://www.google.com/
On first glance, it looks as if the link is taking you to Google.com, right? The link text suggests that. The actual link however leads to bing.com instead. If you look at the actual source code, you will notice that:
<a href="http://www.bing.com/">http://www.google.com/</a>
The href defines the link target, the link text is enclosed in between the command. All you need to remember is that the link text is a string that can look like a domain name or url.
Instead of looking at the source code, you often can simply hover your mouse cursor over the link to find out more about the link destination.
As you can see in this case, hovering over the google.com link reveals that it actually leads to bing.com.
Closing words
It is important to verify links before you click on them. This is especially true for high profile links that point to financial websites or other websites that you have a connection with.
Advertisement
















Wait, what? It’s 2023? Have I been sleeping all this time?
Hi Martin, I just wanted to thank you for this great tip for how to reduce memory usage with Windows Vista. This website is the best in 2012, and I can only imagine how much better it will be 11 years in the future.
Whaaaaaaaat???? Comments date from 11 YEARS AGO now.
And new ones appear scattered randomly in old articles comment sections…
See for example:
[https://www.ghacks.net/2015/03/30/dont-read-the-comments-blocks-comments-on-all-sites-you-visit/]
[https://greasyfork.org/en/scripts/476362-ghacks-hide-older-comments-final-version]
What about server side redirects? Is there a way to know the actual destination your browser will land on before you click a link, when a server has been set up to redirect traffic straight away?
It may be that the displayed link and the “a href” tag are both giving one url, but if you click it it instantly redirects you somewhere else because the server is set up to do this. (This just recently happened to me).
Is the redirection detectable before you follow a link, so you don’t end up somewhere you wouldn’t want to be?
Correction:
Wherein, in the 2nd-to-last paragraph, I wrote, “Apparently, people from the WWW or WAN world can get access to my PC and maybe that’s because a router was added last week.”, there’s a slight typo. error.
It should be, “Apparently, people from the WWW or WAN world can’t get access to my PC …”.
There’re some other typo. errors in my prior post, but I think readers will quickly realize what the correct text would be, so I won’t bother explaining these errors.
Quote: “It is important to verify links before you click on them.”
Definitely, but as aware as I am about this, I sometimes forget and just blindly trust the text shown for a link. There haven’t been any nasty surprises for me, not yet, but it could happen. People should try to never forget to check what links lead to, before using the links.
That’s when I used Firefox or another Web browser. With email, which I use Thunderbird for, I never open links directly from the bodies of the emails. Instead, I always use right-click on a link, select the copy option, and then paste the URL in the Web browser’s address bar or field. That guarantees always seeing what the URL is, before pressing the Return key, so it’s less likely that I’ll get “skunked”, say, when it’s a link from an email. It’s links in Web browsers that I need to try to never forget to properly check before opening whatever the corresponding pages are. Using Firefox over 99% of the time and Having Long URL Please Mod installed for Firefox extension is often useful, but I’ve recently found that this add-on didn’t seem to be working for some shortened URLs. I think that that’s now corrected, but it’ll take a while to be able to see if it is, or not.
It may’ve possibly been for shortening links that the add-on wasn’t yet programmed for, but I’m pretty sure that this wasn’t the case. And some other things were no longer working correctly in Firefox over the past couple or few weeks. It all seems to now be corrected, after I shut down and restarted Firefox yesterday. And I just updated Firefox to v16.0.1 this morning.
Your example using google.com (for hyperlink text) and bing.com for the actual URL is a good one, and I wonder if I would’ve checked what the real URL is, if I wasn’t reading the text of your tutorial or advice. By far most websites I use are very reliable, so I can easily navigate through them without double-checking what hyperlinks actually link to, and this can be a problem, for then we can easily come to develop the habit of opening links before hovering the mouse point over them in order to see what the real linked pages are. And habits are sometimes a little difficult to cease, until we “burn” ourselves one or two times; if not three.
I think that I’m very safe, anyway. For the past couple of hours, I’ve been running GRC.com ShieldsUp! tests and the very initial page finds a “machine name” for my PC or connection, though also says that this may or may not be permanent, so I’ll have to check again after rebooting the PC, eventually. Other GRC ShieldsUp! tests say that all of my ports are stealthed though. Apparently, people from the WWW or WAN world can get access to my PC and maybe that’s because a router was added last week. I have only one PC connected to the Internet, but learned last year that passing through a router, rather than directly through a hi-speed modem, provides a considerable amount of security. So, and having learned that from both experienced users as well as college teachers in computer network administration, I definitely wanted a router for my personal connection.
Nonetheless, we should always double-check what hyperlinks actually link to, as a matter of personal Internet usage policy, say. What would be possibly good to have is an add-on that would automatically run a verification of every URL users try to open; but, that would surely not be fail-proof. How could a developer do that in a fully fail-proof way? And there’d surely be a fairly serious performance hit/impact, I imagine anyway.
Thanks for the good tips.
I check my spam email to make sure their is no legitimate email and often find fake emails. So, when I hover the mouse over a link it goes to a different URL than the text.
If you are not sure of an email, type the URL in the web browser, don’t click the link in the email
Davin Peterson wrote, “… If you are not sure of an email, type the URL in the web browser, don’t click the link in the email”.
Rather than typing in the URL, why not simply right-click on the hyperlink in an email, choose to copy the actual or real link, paste it in the address bar of the Web browser that’s open, and then the user will immediately see what the real URL is? Pressing Return shouldn’t be done until having carefully examined the URL pasted in the address bar.
I wouldn’t bother doing that, either, for I simply hover the mouse pointer over hyperlinks in emails using Thunderbird and this permits being able to immediately see what the hyperlink really links to. But, copying and pasting would often be quicker than retyping whatever the real link is.
I begin by checking if the domain names are the same. If they aren’t and a reason isn’t provided in the email, then I surely won’t bother using the real url. Otherwise, I’ll check the rest of the real address shown when hovering the mouse pointer over the hyperlink. If there happened to be a redirection included in the full link, then we have a number of options:
1) We can just ignore the link altogether.
2) Copy the full link and paste it in a CTRL+D prompt for making bookmarks, but without saving the link as a bookmark; permitting us to scroll across the full length of the link to be able to carefully examine the whole thing.
3) If options 1 and 2 aren’t convenient, then we can alternatively paste the real url in the address bar for a new Web browser tab, f.e.
4) And if options 1, 2 and 3 aren’t convenient, due to the length of a url (being too long to be able to see the whole thing without needing to scroll or cursor over a lot of it, say), then we can paste the url in a temporary text file that provides wrapping of long lines.
When we don’t choose option 1, then we can view the whole url and then decide whether we want to use it, or not.
Retyping URLs is fine, if they’re not too long, but they often are. It would often be quicker to use one of the above 4 approaches, and maybe there’re other safe options that I’m not thinking or aware of. But retyping URLs isn’t going to be something I’d do, except for short ones; and I don’t mean links that’re just shorteners for the real URLs, for I won’t use these shorteners. It’s an interesting concept, but it’s unfortunately untrustworthy. Imo, no one should use services like TinyURL and likes. Nice little concept, but users need to know where they’re going, before going to wherever it is. Internauters, everyone for that matter, have an inherent right to know in what direction others try to lead them to.
A good middle-aged Catholic priest I momentarily met during the 1980s, and yes, there’re some good RCC clergy, it happens, he told me the first evening of a weekend retreat, a little secret, or something the overall RCC at least appears to want to keep secret. He said that I had two bosses. First, there is God. And, next in line, is …, well, guess? Yourself! In another manner of speaking, no one should “mess†with the inherent rights of another. And I detest services like TinyURL, et cetera, being used. If it’s done at websites that I know to be reliably/trustworthily managed, then I don’t mind the presence of these links, though still don’t like the idea of using them, so I do so only on very rare occasion. Having plenty of security for my PC, I can, on rare occasion, make use of such links; but, I always detest that they’re used. I’ve only used such links maybe twice over the past several years and it was only at websites that I know to be very trustworthy.
Thankfully, there’re add-ons for Firefox and these extensions will show the real URLs of short-cut, say, links; but, I don’t know if there’s such an add-on for Thunderbird and I won’t use Microsoft Outlook, Live, and other email services. I use other Web browsers, first Opera and then MSIE, but only when I’m trying to troubleshoot a problem. Otherwise, it’s always Firefox and Thunderbird. My main Firefox profile (having several of them in one Windows user account and using the -P option to select which profile to open with Firefox, and similar for Thunderbird) has plenty of security. GRC.com’s ShieldsUp! tests this morning reported that all of my ports, the first 1,085 or so, are all stealth-protected and I have basic Windows XP Firewall, Avira Antivir, Threatfire (from PC Tools) and WinPatrol always running. So I’m not worried; but, I still detest the usage of TinyURL and such services. It’s of no service to me, for what I want to see is the real url.
Preferable to using such services is to just use a short name or title for a hyperlink, but a meaningful title; preferably. If the title attracts a reader’s attention, then the person can just hover their mouse over the hyperlink’s text in order to see what the real link is. With services like TinyURL, et cetera, the real links are completely masked, unless we use, f.e., Firefox with the Long URL Please extension, or the Long URL Please Mod one.
Typing in the url manually is a good tip provided that you go to a legit site and not a fake one. So, if it shows paypal.com but the link is pointing to somesite.example.com, typing in paypal.com in your browser will do the trick. Then again, there is no need to do that if you have identified the email as fake.
Thanks Martin for the warning and tips on how to prevent possible headaches.
Best regards