Encrypt Android phone conversations with RedPhone
The Prism surveillance scandal has shown that the NSA and other agencies can tap into most communication channels. One of the proposed solutions is encryption and here especially open solutions that anyone with expertise can analyze.
Update: RedPhone is no longer available. We suggest that you encrypt the entire storage of the device instead. End
RedPhone is an application for Android devices that can encrypt phone conversations on the device. It is open source, with the source code readily available on GitHub so that you can audit and compile it at anytime.
The app uses voice over IP technology (voip) to encrypt phone calls, which means that the calls made using it are handled by a data plan.
The first thing you are asked to to after you install RedPhone on your mobile phone is to register your phone number with the service. This is a semi-automated process, with the number filled out automatically. All you have to do is make sure it is correct before you hit the register button to continue.
The phone number that you have selected will then be verified with a SMS that is automatically detected by the application.
You are then taken to the address book displaying all your contacts. While you can call contacts from here right away, you need to be aware that the contact too needs to run RedPhone on the device. This is definitely a limitation as the app is limited to Android right now. If the recipient uses an iPhone, Windows Phone or a landline, it is not working at all.
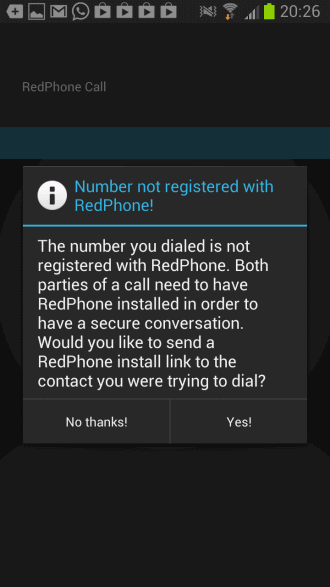
Anyway, when RedPhone notices that a phone number is not using the application as well, it is offering to send a RedPhone install link to that phone number via SMS, or to call it regularly.
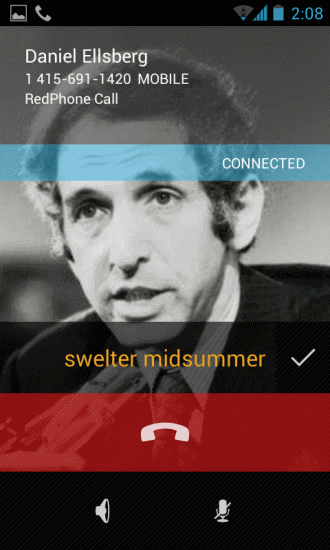
RedPhone is using SRTP to encrypt calls and ZRTP to negotiate the keys. If both parties use RedPhone, the app uses the keys from both users to generate a simple passphrase that is displayed on both screens. Users need to exchange the passphrase to make sure it matches and that no one tapped the line or intercepts it with a man-in-the-middle attack.
You can access additional information about the encryption used here on GitHub.
The core benefits of RedPhone are that it uses regular phone numbers to make encrypted calls, so that you can get started right away, that it is open source, and that it is using a wireless or data connection and not your plan's minutes.
The downsides are that it is currently only available for Android, that both parties need to have it installed, and that both parties need to verify the created passphrase to make sure that the connection is save.
Verdict
The Android limitation is probably the factor that is keeping the application from reaching a larger audience. It offers several benefits that make it attractive though, like the easy installation.
If you have a couple of contacts that use Android, and that you want to talk to using encryption, then you may want to give this application a try.






















AECall could encrypt iPhone phone call and APP(Skype, Messenger, Facetime….) call
It’s a hardware crypto. More convenient. Don’t JB. Don’t install other APP.
More photos:
http://mrhyper.blogspot.tw/2015/12/iphone-encrypt-phone-call_9.html
Its good that we can easily open piratebay in locked network !
“The Android limitation is probably the factor that is keeping the application from reaching a larger audience.” Are you kidding me?
In the April-June period, Android phones accounted for 79 percent of worldwide shipments, up from 69 percent a year ago. The number of Android phones shipped grew nearly 74 percent to 187 million. IDC says shipments of iPhones also grew, by 20 percent to 31 million. But market share fell to 13 percent from nearly 17 percent.
Microsoft’s Windows Phone was third in the second quarter, with a nearly 4 percent share, followed by BlackBerry, with almost 3 percent.
This is Beta-VHS all over again, Android is steamrolling the iPhone.
(from: http://www.foxnews.com/tech/2013/08/08/iphone-sinks-as-android-seizes-market-share/)
I’m not only talking about mobiles here. I agree that Android is the market leader in terms of units sold and in use, but if some or all of your friends or contacts are not using it, then you cannot use this application or at least not fully utilize it.
nice one :)
Great app. but too bad it’s only for Android devices….for now, maybe?!
My family and most contacts either use IPhone or Blackberry!
Why? I don’t know! :)
to Midnight: It’ll be pointless for iPhone or Blackberry as they keep the traffic on private servers that is easily subpoenaed by the U.S.
Martin, also for Android, CSipSimple. https://play.google.com/store/apps/details?id=com.csipsimple
The Guardian Project https://guardianproject.info/ is doing awesome work in the privacy space.
An account with them at ostel.co + CSipSimple and you are done.
There was a lot of echoing during calls with Redphone but I was was using an early beta version. Perhaps you could rate the in call quality of both these apps in a follow up article?
Thanks for all your informative articles. Keep up the good work.