No backdoors found in first part of TrueCrypt Audit
The revelations of Edward Snowden's leaks confirmed that security agencies spend time and money trying to undermine cryptographic software.
Potential backdoors in cryptographic software or protocols would be disastrous, and that is one of the reasons why requests for audits became louder and more prominent.
The Open Source encryption software TrueCrypt ran a fundraiser for a public TrueCrypt audit last year and managed to collect enough money to make that happen.
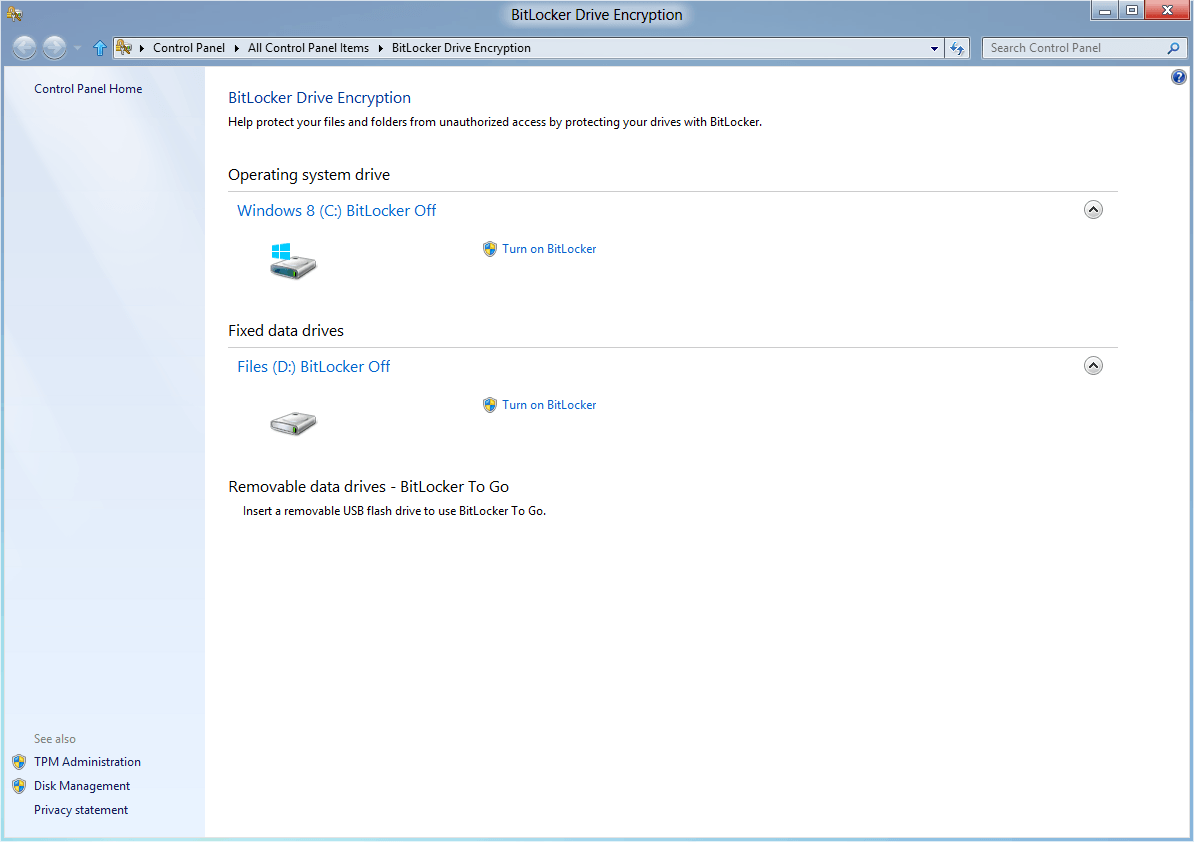
TrueCrypt is a cross-platform encryption software that can create encrypted containers on hard drives or encrypt entire hard drive partitions including the system partition.
Results of the first part of the audit have been released yesterday evening. You can download a PDF document with the audit's findings.
The researchers identified eleven vulnerabilities in total, of which none received the highest severity rating. Four issues were rated as medium, another four as low, and three as informational.
The following vulnerabilities were found:
- Weak Volume Header key derivation algorithm (Medium)
- Sensitive information might be paged out from kernel stacks (Medium)
- Multiple issues in the bootloader decompressor (Medium)
- Windows kernel driver uses memset() to clear sensitive data (Medium)
- TC_IOCTL_GET_SYSTEM_DRIVE_DUMP_CONFIG kernel pointer disclosure (Low)
- IOCTL_DISK_VERIFY integer overflow (Low)
- TC_IOCTL_OPEN_TEST multiple issues (Low)
- MainThreadProc() integer overflow (Low)
- MountVolume() device check bypass (Informational)
- GetWipePassCount() / WipeBuffer() can cause BSOD (Informational)
- EncryptDataUnits() lacks error handling (Informational)
The audit contains detailed descriptions of each vulnerability listed above, addresses exploit scenarios and short and long term solutions to address the issue.
While the researchers found several code related issues such as the use of insecure or deprecated functions or inconsistent variable types, they found no evidence of a backdoor in TrueCrypt.
Finally, iSEC found no evidence of backdoors or otherwise intentionally malicious code in the assessed areas. The vulnerabilities described later in this document all appear to be unintentional, introduced as the result of bugs rather than malice.
TrueCrypt users who use full disk encryption with reasonably long secure passwords should be mostly fine. All issues identified need to be corrected by the developers of the application and while that may take a while, it is reasonable to assume that users who follow these recommendations have nothing to worry about.
You can follow the audit on the Is TrueCrypt audited yet website.
Advertisement
















The audit was not carried out by the TrueCrypt project itself but by third parties.
one more reason i’ll keep using truecrypt
Mr. Brinkmann:
I use TrueCrypt quite a bit so hearing this comforting news gives me the satisfaction that I am using the right product to protect sensitive information!
Question: Do you have any idea when TrueCrypt will receive an Update as it has been awhile since the last one was released.
Thank You,
TR
No word sorry. They only update once or twice a year at the most.
Mr. Brinkmann . . . Thank You.
I still hear imbeciles tell me it’s”open source” so the mystical They have already gone all over the codes automatically.
Did they audit just source code or windows binary too by reverse engineering them (doubt that)? because that might be the place where the cheese is hiding as it is quite a challange to compile trucrypt windows binary yourself so windows folks won’t bother I guess.
Analysis of TC binaries: https://madiba.encs.concordia.ca/~x_decarn/truecrypt-binaries-analysis/
I believe part 1 included the boot loader and driver. That’s what I gathered from the Ars article.
According to the paper, the following areas were analyzed:
TrueCrypt Bootloader
Setup process
Windows kernel driver specifically including:
Elevation of Privileges from local user to kernel
Information Disclosure during disk operations
Volume parsing as it relates to system and drive partitions
Rescue Disks code paths that do not have the private key
Data Leakage
The following areas, and anything not mentioned above were not:
Volume parsing as it relates to a file container
Rescue Disks code paths activated when the disk does contain the private key
Cryptographic Analysis, including
RNG analysis
Algorithm implementation
Security tokens
Keyfile derivation
Hidden Containers
Linux and Mac Components
All other components not explicitly included
Did you know that Firefox by default uses RC4 cipher? check it, go to startpage.com or duckduckgo.com right-click View Page Info take a look at security information then go to about:config type rc4 and set all you see to false then see again.
Nice info. Thank you!
After some testing I found this breaks YouTube when used with https-everywhere.
After restoring RC4 defaults, using PaleMoon, I visited both duckduckgo and startpage. Startpage is using AES-128-GCM and DuckDuckGo is using AES-256.
Perhaps Palemoon has better defaults? security.tls.version.max is set to 3 in PaleMoon. Is the case in Firefox? If not, maybe this would be a better/stable option?
“elven vulnerabilities” … :) .. have you been watching The Hobbit again, Martin?
I blame it on a lack of coffee.
Pulitzer Prize 2014: The Guardian and Washington Post share acclaim for NSA spying revelations
The Guardian newspaper and the Washington Post were jointly honoured today with this year’s Pulitzer Prize for public service, recognising the lead roles they took in exposing the sweeping electronic surveillance methods adopted by the National Security Agency based on documents provided by fugitive Edward Snowden.
While few in the industry doubted that the impact of the NSA stories qualified them for recognition in this year’s awards, the most prestigious in America for journalism and the arts, there had been some suggestion they might be passed over because they were based on leaks from somebody branded a traitor by the US government…
http://www.independent.co.uk/news/media/press/pulitzer-prize-2014-guardian-and-washington-post-share-acclaim-for-nsa-spying-revelations-9259981.html