Microsoft to discontinue EMET in July 2018
Microsoft announced yesterday that it has extended the support end data of the Enhanced Mitigation Experience Toolkit from January 2017 to July 2018.
Microsoft introduced EMET in 2009 as a standalone security program for Windows designed to block certain exploits from being executed successfully.
EMET was designed as a last line of defense against attacks carried out against Windows devices.
We reviewed Microsoft EMET back in 2012 for the first time, and published news updates whenever Microsoft released a new version of EMET that introduced new features. We have published a collection of EMET tips, and covered the latest release, EMET 5.5 as well here on Ghacks.
It appears that EMET 5.5 will be the last version of the Enhanced Mitigation Experience Toolkit that Microsoft will release.
EMET End of Support
EMET was born out of necessity according to Microsoft. Major operating system updates shipped every three or four years back then, and that was simply to long of a time to react quickly to new threats (read integrate defensive measures natively).
EMET provided users and companies with options to protect Windows machines from some of these attack forms.
And thus, EMET was born as a stop-gap solution to deliver tactical mitigations against certain zero-day software vulnerabilities.
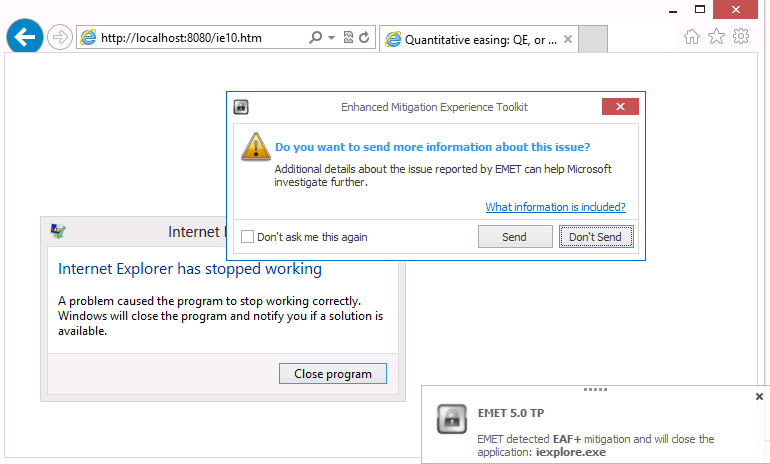
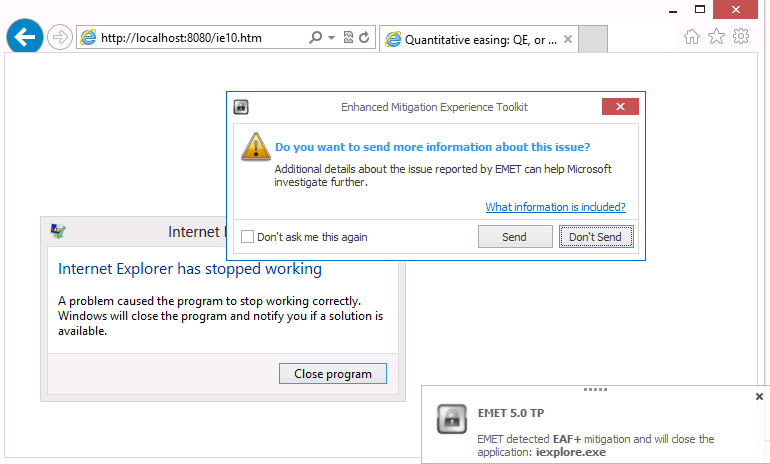
While EMET was useful in this regard, and for security innovations that Microsoft integrated into its operating systems directly, it had serious limitations as well according to Microsoft.
One being that EMET was not integrated in Windows which meant that its features were not "developed as robust security solutions". While EMET blocked techniques in the past, methods to bypass EMET entirely or partially were discovered eventually.
EMET had a serious impact on a system's performance and reliability on top of that due to its hooks into low-level areas of the operating system.
Windows 10 enters the picture
Microsoft integrated all mitigation features of EMET in Windows 10 directly according to Jeffrey Sutherland, the company's lead program manager for operating system security.
The company did add "many new mitigations" on top of that to Windows 10 that EMET does not support.
And, of course, Windows 10 includes all of the mitigation features that EMET administrators have come to rely on such as DEP, ASLR, and Control Flow Guard (CFG) along with many new mitigations to prevent bypasses in UAC and exploits targeting the browser.
Considering that Microsoft's sole focus is on Windows 10, it comes as no surprise that the decision was made to end support for EMET. The main reason why the end of support has been extended by another 18 months is that Microsoft's enterprise customers who deployed EMET on previous versions of Windows demanded more time to cope with the new situation.
While EMET won't receive any new updates anymore, it is not the only anti-exploit software available for Windows. This is especially important for Windows machines who are not updated to Windows 10. Windows 7 and 8 are supported until 2020 and 2023 respectively for instance. Since Windows 10 is the only Microsoft operating system the mitigations were integrated in, other means of protection may need to be found for previous versions of Windows.
There is Malwarebytes Anti-Exploit and HitmanPro.Alert for instance that support previous versions of Windows and will continue to do so long after Microsoft ends support for EMET.
Now You: Do you run anti-exploit software on your Windows machine?

















I think this is why Malwarebytes now supports blocking personally unwanted programs (PUP). What, you didn’t want McAfee’s tentacles in your registry when you automatically updated Flash?
I don’t think Microsoft is going there…
So I guess I will uninstall EMET and remain with Win10’s internal security features and Avast’s HIPS feature.
dang it…
I really depended on EMET. I have MS office, Picasa, movie and music programs, 7zip, pdf reader, Thunderbird, basically any programs with deep hooks and access to file types known to be targets. Which is a lot of programs.
I was under no impression that EMET would halt a determined hacker, but everyone knows including MS that EMET went a long way to stop those casual mass drive by exploit attempts that happen so frequently and much more likely. I really don’t see MS side on this, just yesterday Google published a known in the wild Edge exploit. I don’t think Windows 10 security is what MS makes it out to be.
I disagree with MS that EMET is strictly unnecessary because of Windows 10. While Windows 10 does incorporate all of the mitigations and more into Windows 10, the issue that EMET was built to solve was older and/or crappily developed applications who never used the proper API for proper security procedures in the first place.
Windows 10 can offer all of the security protections under the sun, but if the application developer doesn’t tie into the proper APIs and use them, then it is of no use to the users. That’s the real purpose of EMET.
EMET – beta tested by users on W7/8 for W10. Microsoft then pulls the plug on W7/8 so they can brag that W10 is more secure than W7/8. This is getting a bit droll.
An anti-exploit is one of today’s required security layers for business, government and consumers alike. This 2018 EOL announcement is no less ‘a nudge’ to go to W10. Everyone is being bombarded by DDos attacks, ransomware exploits and website drive-by malware. Fortunately, EMET made Windows systems a lot more insulated from these intrusions.
I will have to take a closer look at MBAE and HMPA as W10 is not an option for my business.
when you say unnecessary (in win 10), does that mean it does nothing? in which case, why is there win10 support? surely it does something, like allowing you to pick certain protection for certain applications. does it mean ms actively provide tailored protection for all those different applications?
it talks about device guard, credential guard, etc.. but they are all enterprise stuff, not home.
I’m getting the impression from this article that 3rd party programs like MBAE and HMPA are not necessary if running Windows 10. Am I correct?
i wish someone would elaborate on this as i’d rather not install and have extra process’s that i don’t need. Anyone ?
Yes, MS added several new protection mechanism like cf-guard. The thing is that it not protects you if the developer of your software which you installed on the OS not supported it. That means he needs newer Visual Studio version + the binaries must be compiled and optimized for it.
I not (currently) saw much apps which supporting all new protection mechanism. Even Chrome and others not supporting e.g. PGO, pkr, cf-guard and co. But’s it’s planed.
Wait, so does that mean I don’t need EMET 5.5 on my Win10 machine? Well, goodbye extra bloat.
According to Microsoft, yes that is the case.
OK, thanks !