HitmanPro.Alert review
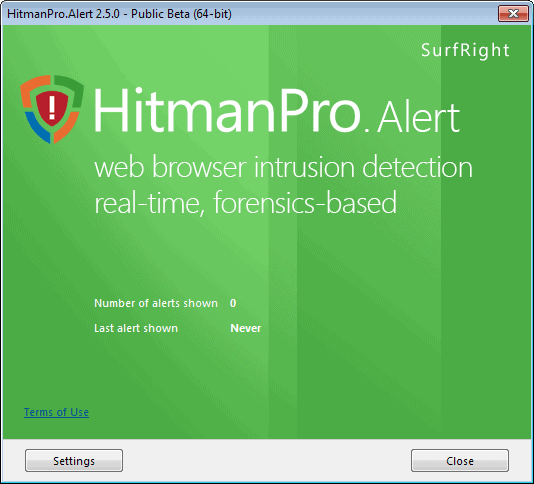
HitmanPro.Alert is a product by Surfright, the makers of the excellent HitmanPro security application, that has been designed to mitigate exploits, and here specifically browser attacks.
We reviewed it back in 2012 when it was first launched by the company and came to the conclusion that it was quite good at what it had been designed for.
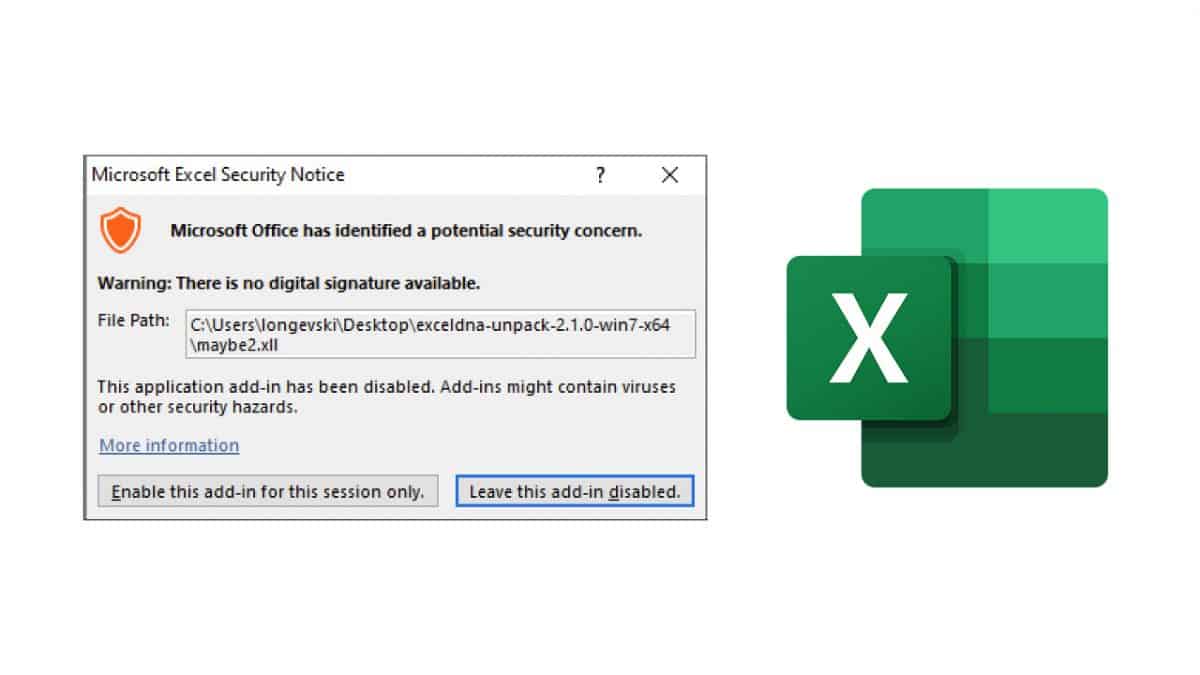
The program supports all major web browsers but acts as an anti-exploit tool on the whole system much like Microsoft EMET or Malwarebytes Anti-Exploit do.
While initially designed to protect against banking trojans and other malicious code affecting web browsers, it has since then been improved to provide protection against other forms of malware.
HitmanPro.Alert
You can download the most recent version of HitmanPro.Alert, currently version 3.1.8, from the official website.
You may try it for 30-days by requesting a trial product key when you run the program for the first time, or enter a Hitman.Pro product key to activate it. That's right, you only need to purchase HitmanPro and get this program as an extra free of charge on top of it. The program itself is not available for purchase as a standalone.
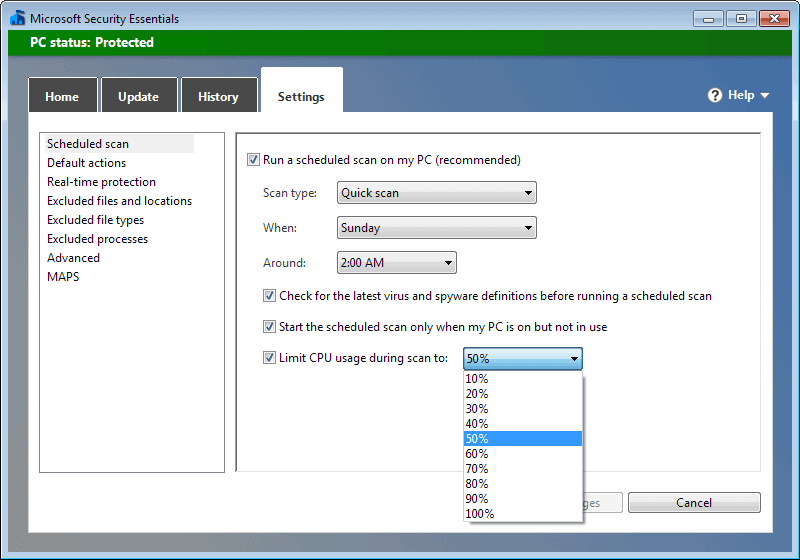
First thing you may want to do is click on the settings icon and there on the "advanced interface" option to display all options in the interface.
HitmanPro.Alert is an exploit mitigation tool which steps in when attacks target vulnerabilities in programs or the Windows operating system that have not been patched yet.
The program supports features that EMET or Malwarebytes Anti-Exploit don't support currently such as Process Protection, Man in the middle browser detection, or anti-ransomware functionality.
The program interface lists four main areas of interest:
- Scan Computer runs a malware scan using the same antivirus engines that HitmanPro ships with.
- Safe Browsing protects against man in the middle attacks while browsing.
- Exploit Mitigation identifies and mitigates attacks that use exploits.
- Risk Reduction includes several additional protective features.
Exploit Mitigation
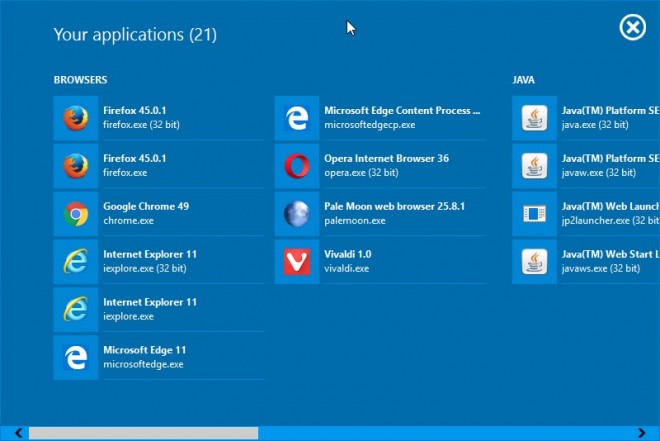
HitmanPro.Alert protects important applications automatically against exploits when it is running. You can add any running process to the list of protected programs which can be useful if the program has not been identified by HitmanPro.Alert automatically. That's the case for portable apps for instance.
You may exclude programs from being protected. This is only recommended if you notice that a program does not function properly anymore because of the exploit protection.
A click on a protected application displays options to enable or disable mitigations individually. The following mitigations are available currently:
- Application Lockdown - Stops attacks that bypass mitigations.
- Control-Flow Integrity - Stops ROP attacks.
- IAT Filtering - Prevents abuse of Import Address Table.
- Stack Pivot - Stops abuse of the stack pointer.
- Stack Exec - Stops attacker's code on the stack.
- SEHOP - Stops abuse of the exception handler.
- Enforce DEP - Prevents abuse of buffer overflows.
- Mandatory ASLR - Prevents predictable code locations.
- Bottom up ASLR - Improves code location randomization.
- Null Page - Stops exploits that jump via page 0.
- Dynamic Heap Spray - Stops exploits that start via the heap.
Risk Reduction

Another area where HitmanPro.Alert outshines other solutions is its selection of risk reduction tools. The security program ships with the following tools included:
- Vaccination - Stops sandbox-aware malware.
- CryptoGuard - Stops crypto-ransomware.
- Webcam Notifier - Warns you when your webcam is being accessed.
- Keystroke Encryption - protects against keyloggers.
- Process Protection - Prevents process hollowing.
- Network Lockdown - Stops backdoor traffic.
- BadUSB - Stops malicious USB devices.
- Block Untrusted Fonts - Stops elevation of privilege attacks.
You can disable any of those easily if you don't require them.
Protection against ransomware
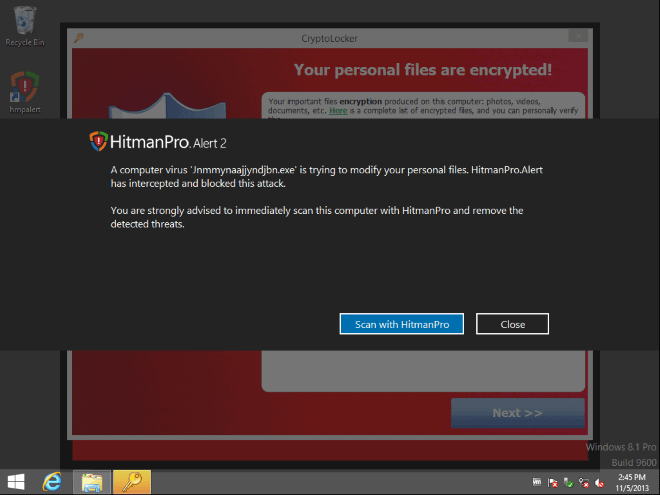
HitmanPro.Alert version 2.5 introduced protection against so called crypto ransomware. This type of malware encrypts data on the PC so that it cannot be accessed anymore by the user unless money is being paid for the decryption.
We have recently looked at Cryptolocker, a ransomware that is currently making the rounds on the Internet.
While there may be ways to restore files if malware did encrypt files on the system, for instance through backups or file versioning, it is fair to say that this is not always a possibility.
HitmanPro.Alert 2.5 introduced protection against these kind of attacks and the feature has been part of the application ever since.
The protection is enabled by default. According to Surfright, it protects against all kinds of crypto ransomware. There is no need to configure anything, the part of the program runs autonomously in the background.
HitmanPro.Alert 2.5 contains a new feature, called CryptoGuard that monitors your file system for suspicious operations. When suspicious behavior is detected, the malicious code is neutralized and your files remain safe from harm.
HitmanPro.Alert will display a notification on the screen that a computer virus has been discovered, and that the threat has been intercepted and blocked from execution.
Note: The files are not removed from your system by HitmanPro.Alert. You can click on the scan with HitmanPro button to run a scan with that application to have it removed. If it is not installed on your system, you are redirected to the website where you can download it to your PC.
Demonstration Video
Verdict
HitmanPro.Alert runs silently in the background for the most part. The process is light on resources -- it used only about 4 Megabytes of RAM while running in the background.
The program is fully compatible with all supported versions of the Windows operating system -- 32-bit and 64-bit -- and fully compatible with full disk encryption software such as BitLocker or TrueCrypt.
The only thing that may keep you from installing it right away is that it is currently listed as beta. Nothing speaks against installing the application once the final version has been released.



















HitmanPro Alert is an essential security tool that every Windows user should employ on their system. Cyber threats have increased and have morphed into highly sophisticated digital threat apparatuses which can literally brick your desktop hard-drive if you’re not careful.
Make no mistake about it!——-Ransomware has been on a sharp rise, with the Locky Ransomware Filecoder gaining new ground and knocking out peoples systems entirely because it latches on so deeply to the system that unless you’re an expert——you’re not going to be able to remove such and infection!
Users should be very afraid and should not hesitate to layer their system security as tight as possible!
There is a digital revolution taking place in the world of Cyber crime. One would be foolish to ignore this truth!
Hardening system security is the key to prevent APT’s and Zero-Day threats as well as common sense computing——-If you lack either one, you put yourself at increased risk of being exploited. It’s only a matter of time…
Don’t let yourself become a victim. Build your figurative brick-wall around your machine now while it is relatively easy to do so because once the smelly stuff hits the fan and viruses start unleashing huge payloads to instigate their attacks globally, you will not fair well if your machine has gaping holes in its network and un-mitigated security vulnerabilities in your OS.
You wouldn’t put off protecting your own life—don’t put off protecting the digital arbiter of that life—your own computer!
You provided a link for a December 4th, 2012, article of yours about HitmanPro.Kickstart and the piece says that this app. is to protect against ransomware.
Is that app. still worth installing if we use HitmanPro.Alert with CryptoGuard?
Mike, the two programs serve different purposes. HitmanPro.Alert adds a line of defense against ransomware on your PC. It attempts to block the PC from getting infected in first place. Kickstart on the other hand comes into play when your PC is infected with ransomware. So, Alert will only warn you more or less, while the core program HitmanPro will remove it (on its own or using Kickstart which is included).
Thank you Martin. Ransomware has given me the willies – it is such a personal form of malware.
Greetings,
SurfRight have updated HitmanPro.Alert to version 2.5.1.56 Beta, date-stamped 2013.11.12 @ 02:16:24 – http://www.surfright.nl/nl/alert/cryptoguard .
i just wanted to say thank you to all for the info and free software,it is nice to see someone is looking out for the folks and not just themselves:))lolwes
Martin,thank you sooo much….for the invaluable information!!….I really appreciate it!!
You are welcome ;)
US-CERT Warns of CryptoLocker On The Rise :
http://www.us-cert.gov/ncas/alerts/TA13-309A
Martin, I’ve installed cryptoPrevent, after you wrote it up. I like it because it’s totally passive. thanks.
Paul I did, and it is only protecting against cryptolocker if I’m not mistaken.
Thanks Dan. I see that keeping it updated is going to be important. There’s a premium version now, with auto update, for $15 – down from $25. If we have to pay that kind of money for every kind of malware out there, it’s going to get expensive. I’ve subbed to the blog’s RSS feed and will update manually for now.
It’s also interesting that CryptoPrevent’s Foolish IT is an affiliate of… Hitman Pro! I wonder what the tie-in is. It seems likely there is one.
You are in fact mistaken. ;)
Cryptoprevent is being updated frequently. In addition to blocking Cryptolocker it will also prevent .exes from running in Temp files locations. It will also protect users from files with multiple extensions (e.g. *.exe.zip)
Interesting, did not know that. Thanks!
I see. Thanks. I need to reread this article more closely.
Hallo Martin, I have already installed the latest version of Emet 4 and (the payed version) Eset endpoint antivirus 5, also I have installed a lot of security in main Mozilla Firefox browser. Do you think its wise to also install HitmanPro.Alert 2.5 or do you think its overkill?
I cannot say anything about the ESET product, but it makes perfectly sense to run EMET and the Hitman product. EMET basically mitigates a lot of exploits that would otherwise work, while the Hitman product blocks programs that do not necessarily use exploits to land on the system. While there are certainly areas where the two overlap, I see nothing wrong with running the Hitman product on your system as well.
I in fact run it next to EMET and Malwarebyte’s Anti-Exploit tool. Yes, may be overkill but better safe than sorry.
I use Firefox with a number of profiles in the same Windows XP user account in order to be able to have a main profile that has additional security add-ons, as well as to be able to simply run two different instances of Firefox at the same time, the second instance being started with the –no-remote and -P options, -P being needed because two different instances of Firefox running at the same time can’t use the same profile. In the main profile, I have NoScript, RequestPolicy and AdBlock Plus, albeit the latter isn’t really about security.
Then I have Avira Antivir Personal, so free, which I’ll be updating to Avira Free Antivirus 14.0.2.286 later today. This is run real-time. Also running real-time are WinPatrol and Malware Defender, a very serious HIPS app. In the latter, all guards are running real-time: file, Windows registry, network and application.
I also use a router and the basic Windows XP firewall.
With this setup I’ve had no problems, but then I surf the Web prudently, as well. NoScript and RequestPolicy are very helpful in this regard since Avira Antivir Personal doesn’t watch Web browsing or incoming email. For email app., I use Thunderbird and Antivir, when running full system scans, has alerted me about finding malware in my Inbox and Junk email files. Junk is easy, for I simply open the file with a text editor and completely erase all of the contents. After all, it’s junk. For the Inbox, I use the information provided in the Antivir report to locate the problem emails and I don’t know if they’re bad in terms of malware, but they’re always junk, so I edit the Inbox to remove this crap, carefully.
Anway, I feel quite safe as it is. But if adding HitmanPro.Alert could be beneficial, then I’d install it and leave it installed. It’s downloaded and will be installed, but if it’s not really going to be of any serious benefit when already using the aforementioned security software, then I’ll uninstall HitmanPro.Alert.
If that’s good to add and EMET and/or Malwarebytes Anti-Exploit also would be, then I’d install these as well, as long as all of this isn’t going to start impacting system performance too much.
The system is:
XP Pro SP3
Intel Core 2 Quad, 2.5 GHz
3 GB RAM (the max. XP can see, for I actually have 5 GB)
You may again reply saying, “Yes, may be overkill but better safe than sorry”, but I’ll run the question by you just in case you reply differently this time.
Mike, adding EMET or Anti-Exploit will improve your system’s security significantly, as they are a last line of defense against exploits that managed to bypass your core security. If you are particularly worried about ransomware, then Alert is a program that you may want to install as well. It runs silently in the background. I cannot say how much RAM it uses however, has been a while since I last used it.
Since ransomware comes usually in the form of executables that you need to run on your system, I do not really bother with the Alert program anymore on my PC as I know what to run and what not to.
Most valuable information of the day as far as I’m concerned. The info here is not crypto ransomware, but this new warrior application.
I’m not a fan of over-protection, but I admit that the spreading crypto ransomware really frightens me.
Beta stage or not, I’ve downloaded HitmanPro.Alert 2.5 and will install it after closing these words, hoping that in the eventuality of an infection this application be the correct defender.