Microsoft launches EMET 5.5 Beta with Windows 10 support
Microsoft EMET 5.5 Beta, the Enhanced Mitigation Experience Toolkit created by Microsoft, is now available for download for all supported operating systems.
The program, designed to mitigate exploits that slipped by system defenses, has been designed as a security tool that blocks exploits from being carried out successfully on machines running Windows.
While EMET offers by no means 100% protection against all sorts of exploits -- researchers have shown in the past that it is possible to bypass some or even all of EMET's anti-exploit measures -- it is quite useful generally speaking as the majority of malicious software has not been designed to bypass EMET or other anti-exploit software such as Malwarebytes Anti-Exploit.
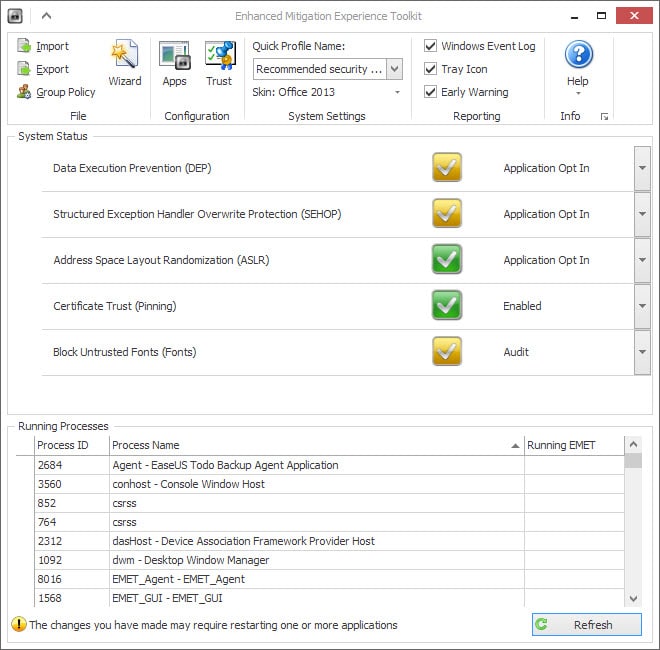
Microsoft EMET 5.5 Beta
Update: Microsoft EMET 5.5 final has been released in the meantime.
The main Enhanced Mitigation Experience Toolkit website over on Microsoft's Technet site links to the latest stable version of EMET -- currently version 5.2 -- and the latest beta download that Microsoft released yesterday.
Probably the biggest change in EMET 5.5 is (official) support for Microsoft's new operating system Windows 10. While EMET 5.2 ran fine on Windows 10, it never supported the operating system officially and this changes with the new release.
When you run the Beta version of EMET after installation you will notice another change right away, provided that you run Windows 10 and not an earlier version of Windows.
The main interface lists the new "Block Untrusted Fonts" option which is set to audit by default. This is a Windows-10 specific feature that is not supported on previous versions of Windows.
Windows 10 ships with settings to block untrusted fonts. The feature is not enabled by default, and can be set to on or audit if desired.
On prevents any font from being loaded that is not in the Fonts directory of the Windows installation, while audit writes untrusted font events to the log but won't block access to them. There is also an option to exclude apps so that they can load untrusted fonts regardless of the global preference.
Configuring untrusted fonts blocking in Windows 10
- Tap on the Windows-key, type regedit and hit enter.
- Confirm the UAC prompt if it is displayed.
- Navigate to the key: HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Session Manager\Kernel\.
- Right-click on "Kernel" and create the QWORD (64-bit) Value preference MitigationOptions if it does not exist.
- To turn untrusted font blocking on, set the value to 1000000000000.
- To turn it off again, set it to 2000000000000 or delete MitigationOptions.
- To set the feature to audit, set the value to 3000000000000.
Please note that you need to add existing mitigation values to the number. For instance, if MitigationOptions exists already on your system and is set to a value of 1000, you need to add 1000 to the value, e.g. 1000000001000 when turning the untrusted font blocking feature on.
Other EMET 5.5 improvements
The new EMET version ships with a handful of additional improvements:
- Better configuration of various mitigations via GPO.
- EAF/EAF+ pseudo-mitigation performance improvements.
- Bug fixes.
Microsoft notes that EMET 5.5 mitigations do not apply to the company's own Edge browser on Windows 10 due to " the advanced technologies used to protect Microsoft Edge, including industry leading sandboxing, compiler, and memory management techniques".
Now Read: Microsoft Enhanced Mitigation Experience Toolkit Tips




















I can’t find any documentation from Microsoft on the EMET 5.5. Final Build 5.5.5871.31892 . I’ll hold off installing it until a Microsoft source says it’s actually intentionally released and documented. But that’s just me….
Note an EMET user of EMET 5.5 final under Windows 10 notes it’s stricter than EMET 5.5 beta.
“In EMET version 5.5.5871.31892, Canon Digital Photo Professional 3.15 (DPPViewer.exe) won’t open due to DEP mitigation (EMET detected DEP mitigation and will close the application: DPPViewer.exe).”
“Up to and including EMET 5.5 Beta is has been OK with EMET, but with EMET 5.5 you now need to disable DEP mitigation for Canon DPP software in order to use it on Windows 10.”
__________
Quote from https://social.technet.microsoft.com/Forums/security/en-US/1e70c72b-67b2-43c4-bd36-a0edd1857875/application-compatibility-issues?forum=emet#071303f5-ef00-4d86-992f-f68cff8c41c0
EMET 5.5. Final Build 5.5.5871.31892
DL:
https://www.microsoft.com/en-us/download/details.aspx?id=50766
https://download.microsoft.com/download/8/E/E/8EEFD9FC-46B1-4A8B-9B5D-13B4365F8CA0/EMET%20Setup.msi
Changes:
• Windows 10 compatibility
• Improved configuration of various mitigations via GPO
• Improved writing of the mitigations to the registry, making it easier to leverage existing tools to manage EMET mitigations via GPO
• EAF/EAF+ perf improvements
• Untrusted font mitigation for Windows 10​
It’s the same beta and old news. Deron
Since this beta have several issue with strongest settings, especially since TH2 I recommend to better use ANTI-Exploit which works a bit better on several things (and it’s getting a bit faster updates).
Your article refers to “the latest beta download that Microsoft released yesterday”. The only beta I could find was the one I already had, which was released in October. Did they publish a new beta and then pull it back?
Can I trust Microsoft EMET 5.5 itself … not to invade my PC privacy or spy for Microsoft ?
Haha. I would worry that it would install Windows 10.