Microsoft EMET update with new exploit mitigation technology
I have reviewed Microsoft's Enhanced Mitigation Experience Toolkit a few days ago here on Ghacks and have found it to be an excellent security program. The software basically mitigates several popular exploitation techniques, making it an effective last line of defense tool when a PC running Windows is attacked with vulnerabilities that are not known or at least not fixed yet.
What makes EMET special is not only the program's mitigation techniques, but also that it ships with an easy to use program interface. Even inexperienced users can use the program to add extra protection to their system, and while they sometimes may run into issues, it is nothing that can't be easily fixed with a few clicks of the mouse button.
Today, Microsoft is making available a technology preview version of EMET 3.5 which incorporates a new exploit mitigation technique that mitigates Return Oriented Programming (ROP) attacks. The following definition has been taken from Wikipedia.
Return-oriented programming (also called "chunk-borrowing à la Krahmer") is a computer security exploit technique in which the attacker uses control of the call stack to indirectly execute cherry-picked machine instructions or groups of machine instructions immediately prior to the return instruction in subroutines within the existing program code, in a way similar to the execution of a threaded code interpreter.
Because all the instructions that are executed are from executable memory areas within the original program, this avoids the need for direct code injection, and circumvents most measures that try to prevent the execution of instructions from user-controlled memory.
The technology that Microsoft has implemented into the technology preview was submitted by one of the contestants of the company's BlueHat Price challenge. The EMET team added four checks into the program to help prevent attacks using ROP techniques.
Installation and use
The Enhanced Mitigation Experience Toolkit 3.5 Tech Preview can not be installed on systems that run other versions of EMET. A prompt is displayed on those systems that is informing users that the current version needs to be uninstalled before the tech preview can be installed. Since it is a tech preview, it is not recommended to install it in a productive work environment. It is also recommended to export the current configuration using the file menu for backup purposes.
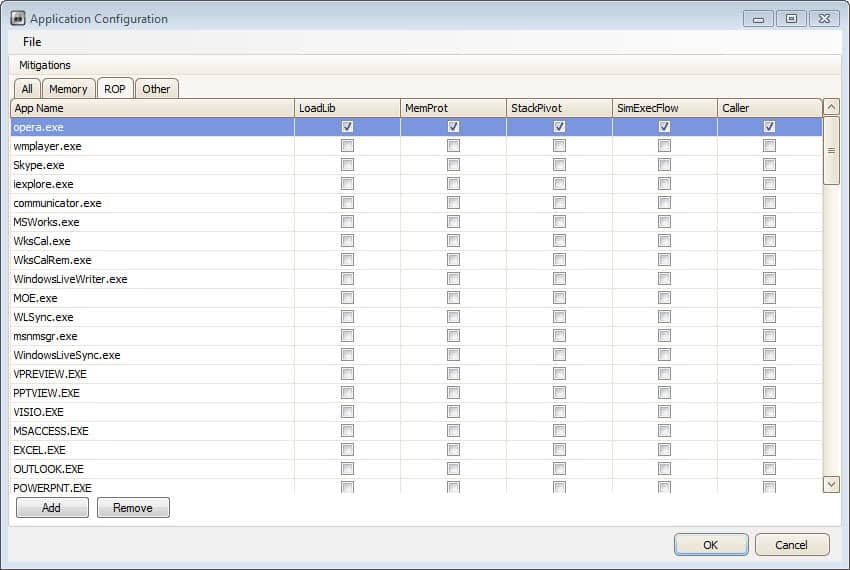
When you start EMET 3.5 for the first time you will notice that Microsoft has added tabs to the application configuration window. You can still display all mitigation techniques in a single tab, or use the memory, ROP or other tab to configure specific features.
Closing Words
Microsoft seems very dedicated when it comes to EMET and it may only be a question of time before the program gets integrated into the Windows operating system in one way or the other. For now though, Windows users need to download, run and configure it separately. Should they? Yes, definitely.
Advertisement















Hi there,
I wonder what you say on this:
http://repret.wordpress.com/2012/08/08/bypassing-emet-3-5s-rop-mitigations/
Plus,what do you think of adding ‘EMET_Conf.exe’ to be protected by Emet?
Best Regards.
I think that with enough energy, you can bypass nearly everything. Most attacks on the Internet on the other hand don’t, and while I hope that MS will fix those issues soon, I do not think they should prevent you from using the program to mitigate exploits of vulnerabilities that have not been fixed yet.
Does EMT co-exist with Microsoft Security Essentials?
I did not see this mentioned in the article or at https://www.microsoft.com/en-us/download/details.aspx?id=30424
Yes it does.
homecalling(spying) = firewall should block – do U have signs that it bypasses it ?
It doesn’t need connection to web to work.
To be sure give MS IP’s to hosts file ;)
Start-up = seems obvious that this app should be in start-up in default for ppl who are always online ( I think 99%) ,isn’t it?
and U can shut it down temporarily (like antivirus or firewall) if being unconnected U need more resources for something v.demanding ..
or move it to custom set delayed start-up time
my Foxit works OK ,starting with EMET I did a few recommended
exceptions that’s all.
I’ve been using EMET since v2. Since then I have mixed feeling about the direction of this app.
Pros:
It’s gotten noob friendlier with the configured XML files.
Cons:
-It’s gotten heavier.
-It calls home a lot more than v2
-Monitoring service forces itself into your list of Startup apps requiring msconfig to disable.
Features I like to see added:
-A check box to disable monitoring at startup.
-Update channel for XML config files.
I’d like to see a community driven XML channel too. Many popular but smaller apps (Foxit Reader etc) aren’t represented in the included XML and may need fine tuning to run properly.
Gonzo a community maintained XML file would be really cool.
Historically all what MS did for “security” (Windows Firewall, Security Center, UAC, Metro apps execution mode) looked and/or worked for me not as safeguard, but rather as hindrance, and I looked more for how to disable/avoid it than to embrace it.
And again, when I read about “tinkering” and possible compatibility issues, this reads not like improvement.
So this will be one more MS tool I won’t use.
there is no other software that do this?
also i created rule for KMPlayer its hanged!
hi
thanks for info.can you tell me how work this program.
or make guide how to mange other program with this tool?
also i am on xp and ASLR and SEHOP unavailable how active that?
Some technologies are not available under XP, and there is no option to activate.To use, you basically either load one of the default profiles to start with, or add your own set of applications to the program. It may take some tinkering at first to find out if the program is fully compatible with all features or not.
hi, thanks for replay
so when some technologies not available under XP so the hacker can not exploitat me?
also i found one bug to launch it in xp,when i want run it from start menu
it dont launch and say (title dialog:problem with shortcut) message:the parameter is incorrect.i think this problem with the installer.
please report to developer
Generally speaking it can still be exploited.