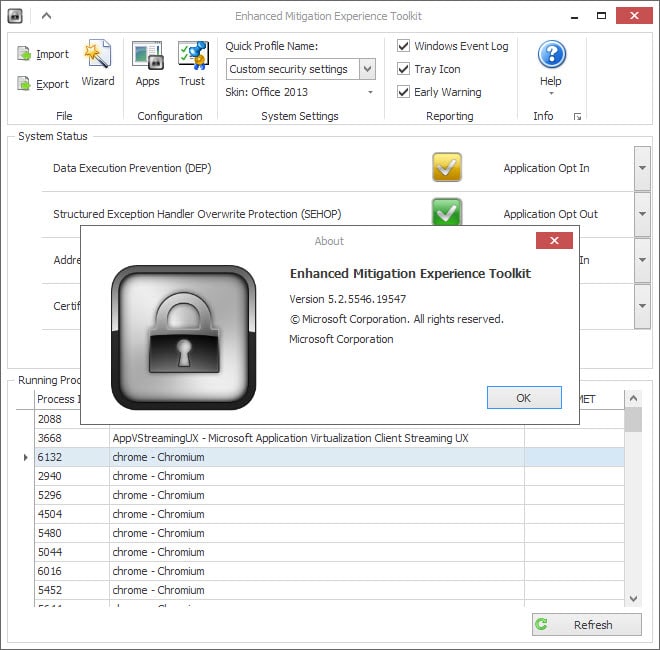
Microsoft EMET 5.2 with Control Flow Guard now available
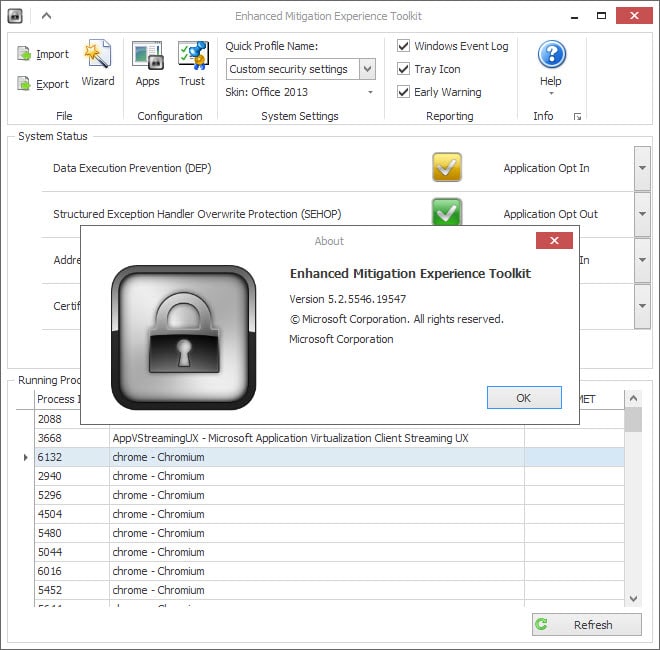
Microsoft's Enhanced Mitigation Experience Toolkit is one of the programs that I install on Windows PCs that I set up for myself or others.
The program attempts to block exploits from successfully running on Windows machines. The most likely scenario where this happens is when attacks managed to sneak past system defenses.
Without EMET, these attacks would be successful whereas you still have a chance of blocking them with EMET.
While EMET is not a catch-all solution that protects you from every piece of malicious code out there, it is not using lots of system resources and adds another layer of protection to Windows machines.
Microsoft has just released EMET 5.2, a new version of the Enhanced Mitigation Experience Toolkit that updates the previous version 5.1.
Note that the company offers two different versions of EMET right now. First the 5.2 version which is the latest, and then version 4.1 Update 1 which it will support until June 9, 2015.
So what is new in EMET 5.2?
Microsoft EMET 5.2 ships with three new features of which two enhance the protection on all supported operating systems and one only on Windows 8 and newer versions.
All EMET installations benefit from Control Flow Guard, a new feature of Visual Studio 2015, that "helps detect and stop attempts of code hijacking". Control Flow Guard is only supported by Windows 8.1 and newer versions of Windows including Windows 10 which means that it benefits only systems that run these operating systems.
The second change improves the program's Attack Surface Reduction mitigation which tries to "stop attempts to run the VBScript extension" when loaded in the Internet Zone of Internet Explorer. According to Microsoft, this protects against the exploitation technique known as VBScript God Mode.
The third and final change affects Internet Explorer as well. EMET supports alerting and reporting with Enhanced Protected Mode enabled from desktop Internet Explorer and Modern Internet Explorer now.
You can download the EMET from the official Microsoft website linked above. It is suggested currently to use the direct link posted in the blog post on the Microsoft Security Research and Defense Blog as the main download site seems to be broken currently.
The installer upgrades existing versions of EMET on the system and also installs the software anew if it has not been installed on the system before.
Now You: Are you using EMET? What's your take on it?


























The reason EMET 5.2 silently won’t download on Chrome and Firefox will probably be that you (as I) have pop-ups forbidden.
You find this out by using IE11 which will ask if you want to allow pop-ups.
Another bonehead move, from a certain place. Who would think to require a pop-up? In 2015?
But anyway, the _actual_ direct link provided kindly by CHEF-KOCH above does appear to work. Whereas the ‘direct’ link in the original MS article just goes to the same place that fails unless you have thought to permit MS pop-ups. I ask you…
Redmond says this update kills the ‘VBScript God Mode’ exploitation technique used in “recent” attacks. The toolkit now supports alerting and reporting from Internet Explorer with Enhanced Protected Mode mode enabled. The final improvement includes Control Flow Guard for native DLLs such as EMET.DLL recently introduced into Microsoft Visual Studio 2015.
Sources:
http://blogs.technet.com/b/srd/archive/2015/03/12/emet-5-2-is-available.aspx#
http://blog.fortinet.com/post/advanced-exploit-techniques-attacking-the-ie-script-engine#
http://blogs.msdn.com/b/vcblog/archive/2014/12/08/visual-studio-2015-preview-work-in-progress-security-feature.aspx#
http://www.theregister.co.uk/2014/10/02/researchers_bypass_redmonds_emet_again/#
Microsoft reissued EMET 5.2 last week. The original version was digitally signed on 13 March 2015, the current one on 16 March. (See “Microsoft re-releases EMET 5.2, fixing IE problems under Windows 8.1” – http://www.infoworld.com/article/2897642/operating-systems/microsoft-re-releases-emet-5-2-fixing-problems-while-running-under-windows-8-1.html .)
I seen this Process running in Taskmgr one day in a screen shot and said what is he using there, quick search and like it right away. I was updating the link last night witch was crazy, because HTTPS seems to be taking over.
Thanks for the Preview Martin
Direct link:
http://download.microsoft.com/download/7/0/A/70AF5150-10DD-4838-ACFC-C4390B05620A/EMET%205.2%20Setup.msi
EMET 5.2 crashing IE > Workaround http://forum.thewindowsclub.com/windows-security/36691-emet-5-2-may-crash-internet-explorer-workaround.html
It’s not worth to use it with an installed and activated Antivirus solution but if you not prefer to use any AV it’s okay to use. No, atm there is no EMET hack (for now) because 5.2 already fix the 5.1 leak which cause to bypass emet. Emet is free for all so it’s a benefit compared to paid products and Microsoft “often” updates emet.
I can’t for the life of me, download this using IE, Firefox, Opera, or Chrome.
I am using Windows 10 Technical Preview.. is there a direct link?
There is a direct link embedded on the Technet blog article about it.
Microsoft EMET is too complicated to my taste and did crash Windows with some of the latest Windows Updates.
I use the simpler and which is as good as EMET – HitmanPro.Alert.
Just trying HitmanPro.Alert 3 with MBAE Free on Windows 8.1, and so far no probs.
I used to run EMET 5.1 as well on a Windows 7 machine but it crashed IE11 (known conflict with MBAE), so I removed it from that machine.
I would like to try EMET 5.2 on my Win 8.1 machine now, but according to the HMPA developer it is not currently compatible without disabling EAF (although 5.1 and earlier are) – but they are working on a fix.
It seems one can disable certain mitigations in EMET to have this and MBAE Free working together, but I guess that is probably OTT – any hassles and I would rather then just uninstall MBAE Free, as this offers browser protection only, and Java, which I don’t use.
Hi Martin…..
I see that EMET has been substantially upgraded. If you were to pick between EMET and Malwarebytes tool (I forgot the name) that does more or less the same, which would you choose??? Just curious…. I just remembered, Malwarebytes Anti Exploit…….
I’m running them both at the moment, no problems so far.
Okay….thanks for the tip …..
I think I read that EMET had been hacked a few months ago. Do you know anything about that?
I seem to remember reading that it can be bypassed. As I said, it is not a perfect “catch-all” solution but I do believe that it is better to have it than not to have it installed.