
Bitwarden launches passkeys support in mobile apps for Android and iOS
Users of the password management solution Bitwarden are one step closer to full passkeys support. The organization launched new beta apps for Android and iOS earlier this month that introduced limited passkeys […]

Microsoft publishes new Registry security mitigation for Intel processors (Spectre)
About six years ago, vulnerabilities were discovered that affected most Intel and AMD processors. The vulnerabilities, Spectre and Meltdown, can be exploited to read sensitive data from attacked computer systems. Intel released […]

KeePassXC adds support for Passkeys, improves database import from Bitwarden and 1Password
KeePassXC has been updated to 2.7.7. The latest version of the open source password manager adds support for Passkeys, and has gained the ability to import your vault data from Bitwarden. Passkeys […]

First look at Malwarebytes 5.0
It took Malwarebytes nearly five years to release the next iteration of its Malwarebytes security program. Malwarebytes 5.0 is available now for all supported operating systems (Windows, Mac, iOS, and Android). Malwarebytes […]

RustDoor malware targets macOS users by posing as a Visual Studio Update
A new malware called RustDoor is targeting macOS users. The malware has been undetected for 3 months, and poses as a Microsoft Visual studio Update. The malware was discovered by Bitdefender. A […]

KeePass 2.56 released: options search and history improvements
The developer of the free password manager KeePass has released version 2.56 of the Windows application. KeePass is a local password manager by default; this means that it does not require a […]

70 million account credentials were leaked in a massive password dump
A security researcher has unearthed what appears to be one of the biggest password dumps ever. Over 70 million unique credentials have been leaked on the dark web. The news came to […]

Bitwarden: how to create and use Passkeys to sign in
Bitwarden users have a number of options already when it comes to signing-in to their vaults. They can use a master password and improve security by adding a two-factor authentication option to […]

LastPass is enforcing some security changes to user accounts
LastPass is making some changes to enhance the security of its to user accounts. The news comes as a follow-up to the company's plans to enforce stronger passwords a few months ago. […]

Its Groundhog Day at Microsoft! Vulnerability patched again
Remember the movie Groundhog Day? Bull Murray plays a rather self-centered weatherman who finds himself in a time loop on Groundhog Day. Windows administrators may have similar feelings to Murray's in regards […]

The most popular passwords of 2023 are easy to guess and crack
Each year, analysts at various Internet security companies release lists of the most used (and known) passwords. These lists are based on leaked password database data. The passwords that are on these […]
Protect your Discord account with a Security Key
Users of the chat app Discord may now protect their accounts using security keys. The developers of Discord have added the option to the existing arsenal of multi-factor authentication options that the […]
Scam or not? BitDefender's Scamio AI promises to have the answer
Scamio is a new AI tool that promises to help Internet users combat scams. Spam and scams are common on today's Internet. Especially users who are not tech-savvy may have difficulties distinguishing […]

If your Windows PC freezes, Avira security software may be the culprit
A recent update for Avira antivirus software for Windows seems to have a negative impact on system stabilization for some users. For a couple of days, Avira users have reported issues with […]

LogoFail vulnerability affects many Windows and Linux devices
Many commercial computers are vulnerable to a set of vulnerabilities that exploit flaws in the processing of startup logos during boot. Security researchers at Binarly have disclosed security vulnerabilities in system firmware […]
BLUFFS: new Bluetooth vulnerability discovered that affects most devices
BLUFFS is an acronym for a new Bluetooth vulnerability that security researcher Daniele Antonioli disclosed recently. BLUFFS, which stands for Bluetooth Forward and Future Secrecy, is actually a set of six unique […]

When will the cybersecurity company Okta ensure its own security?
On Tuesday, Okta revealed that hackers had stolen data from all of its customer support users in a major breach of its customer support system. The company had previously said that only […]

MDP warns parents about this iOS feature
In a recent social media post, the Middletown Division of Police in Ohio has put an iPhone NameDrop warning for parents. Introduced in the iOS 17 update, this feature allows users to […]
Enable 256-bit Bitlocker encryption on Windows 11 to boost security
Bitlocker is the default encryption technology of the Windows operating system. It is used widely on Windows, but some users prefer third-party solutions, such as VeraCrypt. What many users of Bitlocker don't […]

Data of 8.5 million patients compromised in the United States
Healthcare SaaS provider Welltok has disclosed a data breach that has compromised the personal information of nearly 8.5 million patients in the United States. Welltok works with healthcare providers across the US, […]

Security researchers bypass Windows Hello fingerprint authentication
Security researchers at Blackwing Intelligence managed to bypass Windows Hello fingerprint authentication on devices with the three most used fingerprint sensors on Windows. The researchers were asked by Microsoft's Offensive Research and […]
Protect your eBay account with Authenticator apps
Users of eBay had several options up until now to improve account login security using 2-step verification. They could get texts or emails from eBay that contain the code, or get codes […]

CVE-2023-4966 vulnerability becomes a global problem
Threat researcher Kevin Beaumont has been tracking attacks against various companies, including the Industrial and Commercial Bank of China (ICBC), DP World, Allen & Overy, and Boeing, and found they had something […]

Mullvad's public encrypted DNS Servers run in RAM now
Sweden-based VPN provider Mullvad announced today that its public encrypted DNS servers run fully in RAM. The announcement comes less than two months after Mullvad completed the migration of its VPN infrastructure […]

Suspicious Microsoft Authenticator requests don't trigger notifications anymore
Microsoft Authenticator will suppress suspicious authentication prompts to protect users against social engineering attacks. Microsoft has now enabled the security feature, which it unveiled back in August 2023. Microsoft Authenticator is a […]

Be careful if you use Apple's Find My network
Apple's "Find My" network is a powerful tool that can help users locate their lost or stolen devices. It works by using a combination of GPS and Bluetooth signals from other Apple […]
CVSS 4.0 standard has been released
The Common Vulnerability Scoring System (CVSS) is an open standard for assessing the severity of computer security vulnerabilities. CVSS scores are used by organizations and individuals around the world to prioritize vulnerability […]

Latest Bitwarden update introduces support for saving passkeys
A new version of the open source password manager Bitwarden is now available. Bitwarden 2023.10.0 introduces a number of important features to the password manager. Noteworthy additions are supported for saving passkeys […]

And the phishing Oscar goes to...
Cybercriminals are constantly evolving their tactics to exploit the latest trends and technologies. One way they do this is by using the names of popular celebrities to create phishing scams and other […]

Watch out for StripedFly malware
Cybersecurity researchers have discovered a sophisticated cross-platform malware platform named StripedFly malware that has infected over 1 million Windows and Linux systems since 2017. The malware, which was wrongly classified as just […]

Tor Browser Security Audit reveals 2 high security issues
The Tor Browser project asked the penetration testers at Cure53 to audit core components of the project. Among the components were the BridgeDB software, building infrastructure, specific Tor Browser alterations and rdsys […]

The fallout from the Okta breach continues
On September 29, 2023, 1Password discovered suspicious activity on its Okta tenant. The investigation revealed that the threat actor used a HAR file stolen in the recent Okta breach to access the […]

VMware Workstation 17.5 Player fixes a security issue
If you use VMWare Workstation Player to run virtual machines on your devices, you may want to update the existing version of the application to the newly released 17.5 version. VMWare Workstation […]

Dashlane limits Free users to 25 passwords starting next month
Users of the free version of the Dashlane password manager will soon have to cope with a severe limitation. Starting on November 7th, 2023, Dashlane Free will support a maximum of 25 […]
Old WinRAR vulnerability is exploited by government-backed actors
WinRAR users who have not updated the archiving software in some time may want to do so immediately. A report by Google's Threat Analysis Group TAG suggests that government-backed actors are exploiting […]

Password Manager KeePass 2.55 warns users about weak security settings
A new version of the password manager KeePass is now available. KeePass 2.55 is a smaller release that improves security, imports and introduces some new features to the application. The new version […]

Microsoft Defender for Endpoint Automatic Attack Disruption promises an end of ransomware
Human-operated attacks against computer systems are often difficult to detect. Microsoft promises that Microsoft Defender for Endpoint is now capable to "disrupt human-operated attacks like ransomware early in the kill chain without […]
Microsoft is phasing out VBScript in Windows to improve security
Microsoft announced plans to deprecate Visual Basic Script (VBScript) support in its Windows operating system. The company introduced VBScript, which is modeled on Visual Basic, in 1996. Web developers were the initial […]

Act Now! Android October 2023 Update patches 2 actively exploited issues
Google has published the October 2023 security updates for Android. The update addresses a total of 54 different security issues. Two of the issues are exploited in the wild, according to Google's […]
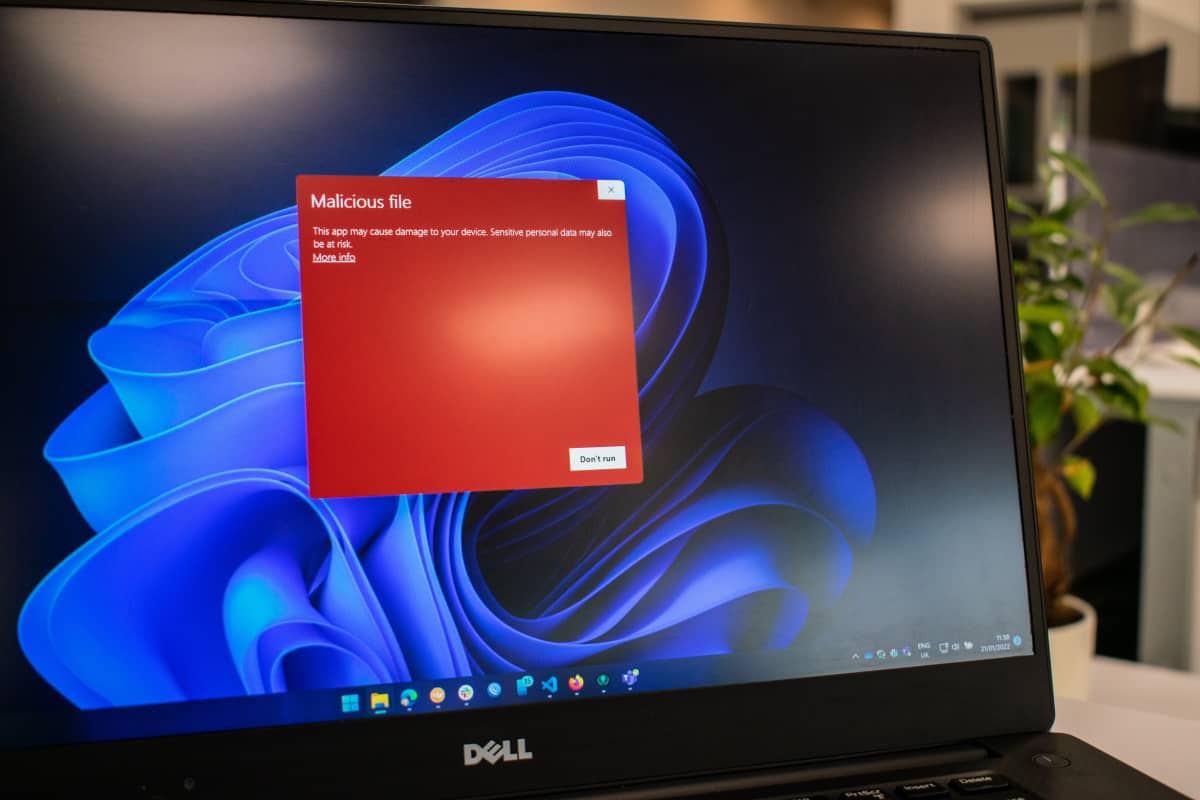
AI responses may link to malware
AI tools are probably the biggest hype in tech in 2023. Companies have pushed out products or are about to. Bing Chat is one of the most prominent tools available, but there […]

