Mullvad's public encrypted DNS Servers run in RAM now

Sweden-based VPN provider Mullvad announced today that its public encrypted DNS servers run fully in RAM. The announcement comes less than two months after Mullvad completed the migration of its VPN infrastructure to RAM.
The main benefit of running servers in RAM is that all traces of activity on disk are removed. Mullvad uses its own custom infrastructure to power its services and engineers are constantly working on improving it.
Encrypted DNS, widely known as DNS over HTTPS, protects DNS traffic by encrypting it. Network spies, such as the ISP or malicious actors, don't get cleartext information anymore when the security feature is enabled.
Data is encrypted, which prevents third-parties from finding out about the sites that you access while connected to the Internet.
Mullvad's encrypted DNS solution is available free of charge for everyone. The company advises customers of its VPN service, which is available for a flat-fee of 5 EUR per month, not to use the encrypted DNS service as the DNS resolver of the VPN server is handling this automatically. The performance of connections could be slower, if users make the switch.
Interested users may check out Mullvad's extensive guide on setting up the encrypted DNS solution on their devices. The company operates several different DNS solutions. You may configure various content blocking options, besides the unfiltered DNS server option.
Here is the overview of the available hostnames and their content blocking level:
- No content blocking: dns.mullvad.net
- Ad and tracker blocking: adblock.dns.mullvad.net
- Ad, tracker and malware blocking: base.dns.mullvad.net
- Extended ad, tracker and malware blocking: extended.dns.mullvad.net
- Extended blocking plus adult, gambling and social blocking: all.dns.mullvad.net
Here are the full URLs and IPs of these options:
- https://dns.mullvad.net/dns-query -- 194.242.2.2
- https://adblock.dns.mullvad.net/dns-query -- 194.242.2.3
- https://base.dns.mullvad.net/dns-query -- 194.242.2.4
- https://extended.dns.mullvad.net/dns-query -- 194.242.2.5
- https://all.dns.mullvad.net/dns-query -- 194.242.2.9
Configuring Mullvad's Encrypted DNS
The configuration in the web browser depends on the browser. In Firefox, you would select Settings > Privacy & Security > Max Protection under Enable secure DNS using > Choose provider > Custom and paste one of the URLs into the field.
In a Chromium-based browser, e.g., Chrome, Vivaldi, Opera or Brave, you would go to Settings > Privacy and Security > Security, enable the option use secure DNS. Select custom and paste one of the available URLs into the field.
You may check out our full guide on enabling DNS-over-HTTPS in browsers.
Microsoft uses different terms for some of the menus. Instead of Privacy and security, it uses Privacy, search, and services. The Custom option is replaced by Choose a service provider in Edge as well.
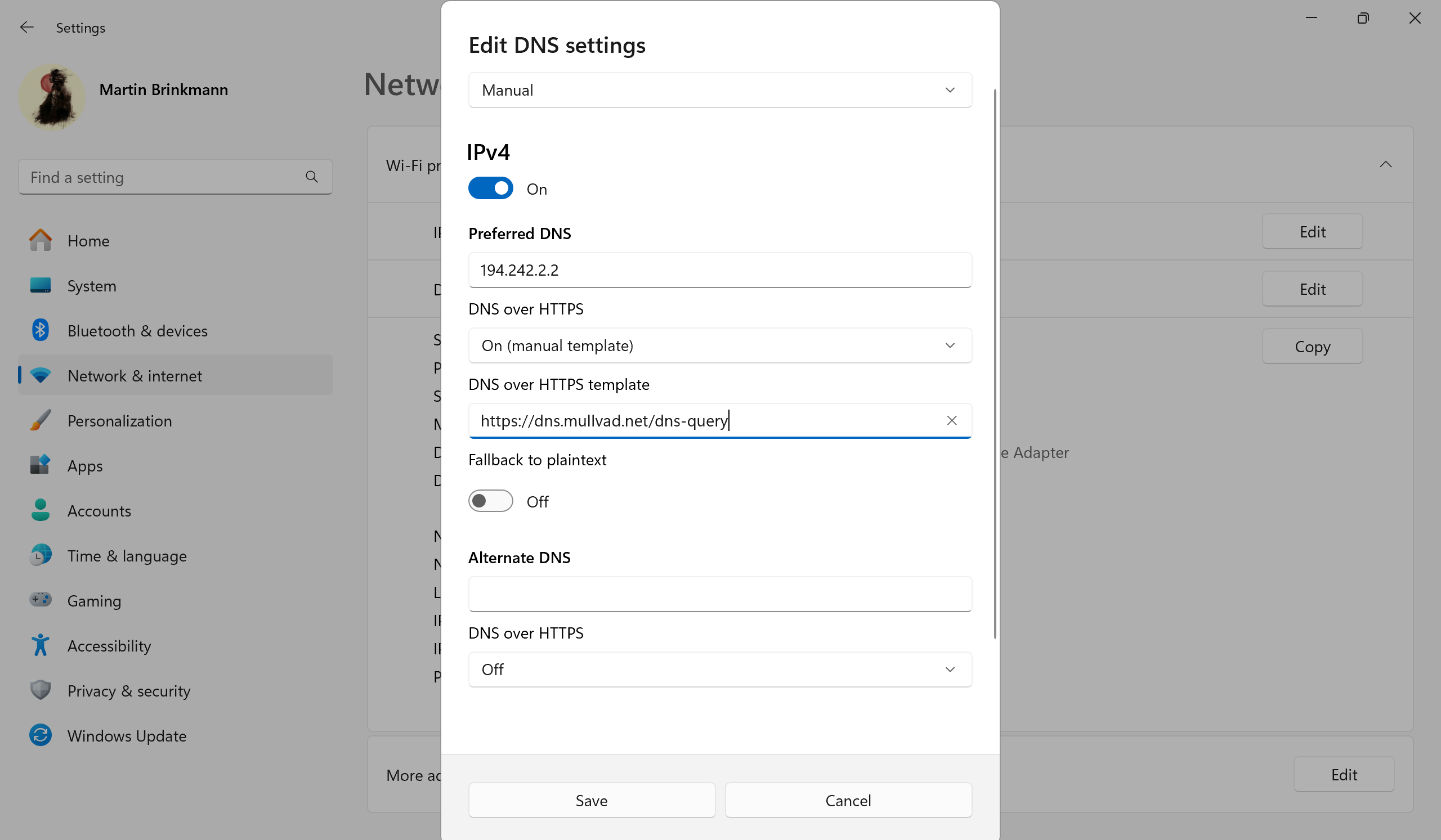
On Windows, you'd go to Settings > Network & Internet > Wi-Fi / Ethernet. If you have selected Wi-Fi, click on Hardware Properties to proceed.
Select the Edit button next to DNS server assignment, switch to Manual and toggle IPv4 to On. Paste the IP address of the encrypted DNS version that you want to use in the field. Turn DNS over HTTPS to On (manual template). Paste the URL of the selected service under DNS over HTTPS template. Select Save. Repeat the steps for IPv6.
On Android, you'd go to Settings > Network & Internet > Private DNS > Private DNS provider hostname and paste the URL of the selected service into the field.
Things are more complicated on iOS. It requires that you download the base or extended profile from Mullvad's GitHub repository to install it on the device. Check out the full instructions by following the link provided above.
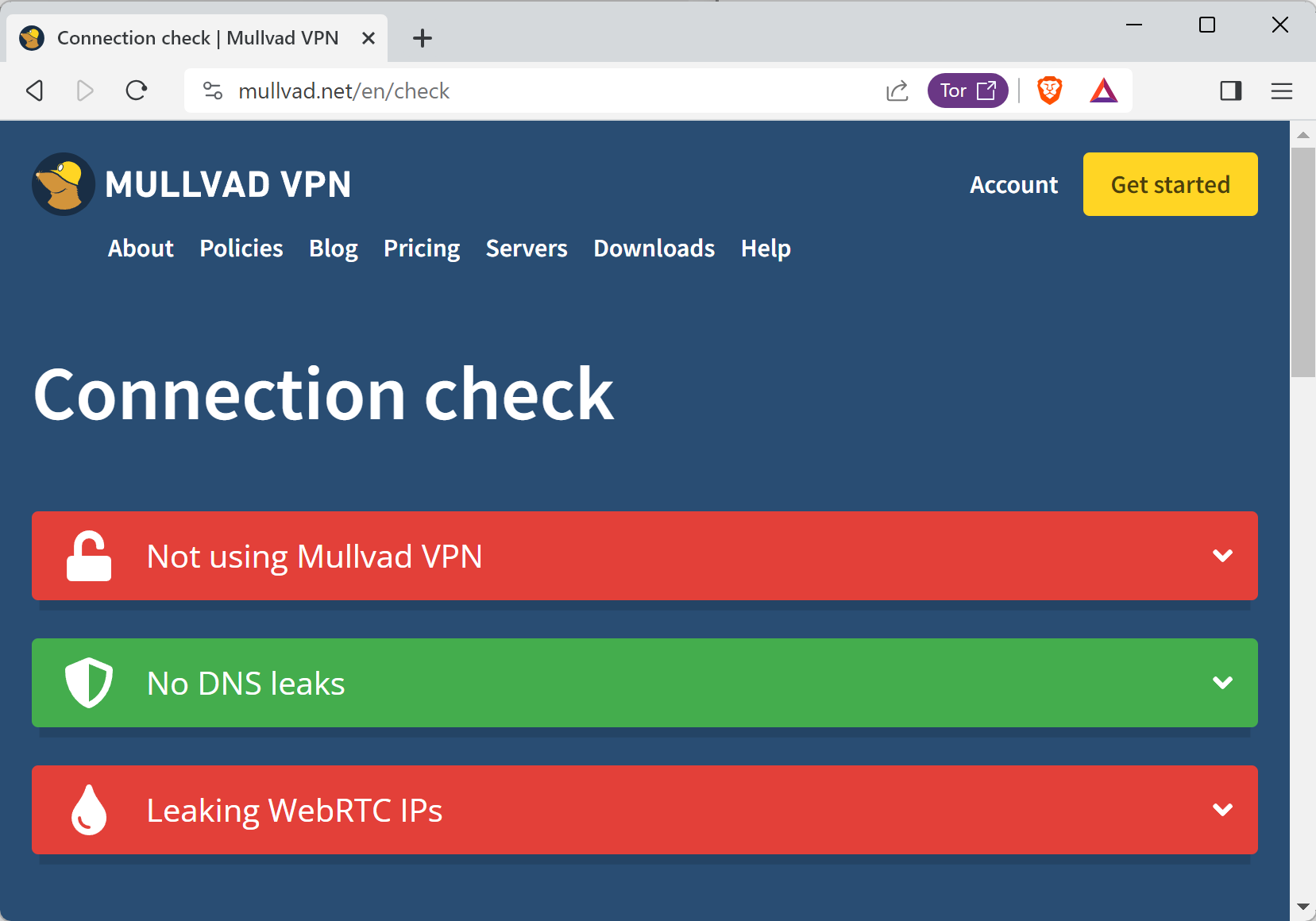
You can check if encrypted DNS is working on Mullvad's website. You can alternative check for Secure DNS here.
Now You: do you use encrypted DNS?

















I’ve noticed now that turning off Max Protection for which network.trr.mode is “3” in about:config slows down search results considerably when connected to the VPN even with a Mullvad DNS configured. That’s probably because turning it off also switches network.trr.mode to “5” which is Off.
It may be confined to the browser I’m using which is Floorp and I haven’t checked it yet in vanilla flavored Firefox, but if Max Protection is set to enabled it’s supposed to slow down searches with the VPN enabled, but it does the exact opposite so I think I’ll continue to leave it on.
I’ve noticed a small problem which occurs when turning DNS over HTTPS to Off when using the VPN as recommended by Mullvad on their site at: https://mullvad.net/en/help/dns-over-https-and-dns-over-tls
Doing that switches network.trr.mode to “5” which is off. This assumes the user has configured one of the five DNS server options described on the same page since the VPN takes care of the security side of things.
However, when exiting the VPN network.trr.mode remains at “5” which will cause problems when searching for sites. So you either need to go to about:config again and reset it to “3”, or checkmark “Maximum Protection” again in the Settings.
I guess Mullvad envisages users being permanently connected to the VPN, but in the Netherlands at least there are occasions when a given site will only work if the ISP IP is enabled and not that of the VPN.
Hi Martin,
a small error in the article to correct. You wrote:
“The company advises customers of its DNS service, which is available for a flat-fee of 5 EUR per month, not to use the encrypted DNS service(…)”.
But of course you meant: “(…)customers of its VPN service(…)”.
Cheers.
Hi Malik, thank you for the tip. You are right of course :)
Mullvad recommends setting “DNS over HTTP” to “Off” in the browser when connecting to the VPN since the VPN handles DNS queries. I’ve configured that as such on Floorp, but have to remember to enable “Maximum Protection” again when disabling the VPN. The latter is necessary in the Netherlands when visiting certain sites which demand my ISP’s IP address.
I’ve tested it in both cases on the BrowserLeaks.com site and everything works properly, but it might seem a bit confusing to be turning DNS over HTTP to Off since the Firefox setup describes it as “Use your default DNS resolver” even though it will still connect to the Mullvad DNS server which has been configured. In my particular case those are “base.dns.mullvad.net” | 194.242.2.4 (IPv4) | 2a07:e340::4 (IPv6).
DNS: No.
VPN: Yes (if properly setup).
Interesting. Personally I use DNScrypt-proxy and Mulvad has 5 public servers listed : [https://dnscrypt.info/public-servers] which means that it’d be no problem to choose one of them :
mullvad-doh
Public non-filtering, non-logging (audited), DNSSEC-capable, DNS-over-HTTPS resolver hosted by VPN provider Mullvad Anycast IPv4/IPv6 with servers in SE, DE, UK, US, AU and SG.
[https://mullvad.net/en/help/dns-over-https-and-dns-over-tls/]
mullvad-adblock-doh
Same as mullvad but blocking ads and trackers.
mullvad-base-doh
Same as mullvad but blocking ads, trackers and malware.
mullvad-extend-doh
Same as mullvad but blocking ads, trackers, malware and social media.
mullvad-all-doh
Same as mullvad but blocking ads, trackers, malware, social media, adult and gambling.
All these servers use the DoH protocol; personally I rely only on the Dnscrypt protocol because it is the only one to provide ‘Anonymized DNS’ natively and effortlessly [https://github.com/DNSCrypt/dnscrypt-proxy/wiki/Anonymized-DNS].
DNSCrypt-proxy runs system-wide hence no browser-specific DNS settings required.
Tried dnscrypt but it wouldn’t allow RT through, mullvad dns works.
Will this stop ISP DMCA notices?
By default no. But with ECH possibly, if the server (website) you’re connecting to supports it.
if yu use MullvadVPN you wont get any. Been using it for years and never got one. It’s the best VPN for privacy.