70 million account credentials were leaked in a massive password dump

A security researcher has unearthed what appears to be one of the biggest password dumps ever. Over 70 million unique credentials have been leaked on the dark web.
The news came to light when Troy Hunt, the owner of the popular breach notification service, Have I Been Pwned, wrote about the massive data leak on his blog. The usernames and passwords were leaked in a credential stuffing list, which is being called the Naz.API list.
Hunt says that a well-known tech company had pointed out the list to him, when someone had sent the company a bug bounty submission based on the list. After analyzing the list, which has been around for about 4 months on a hacking forum, the researcher found out the following.
The breach consisted of 319 files that totaled to 104 GB, and contained 70,840,771 unique email addresses (about 71 million). 427,308 individual Have I Been Pwned (HIBP) subscribers were affected by the leak. Hunt used a 1K random sample test, and came to the conclusion that 65% of the addresses were already in HIBP. Many of these accounts are used for popular web services such as Facebook, eBay, Roblox, Yahoo, Coinbase, Yammer, etc. The number 65% is critical here, as it means that the other 35% or one-third of the credentials in the leaked list have never been seen before.
Hunt's article, which was spotted by Ars Technica, goes into extensive detail about the credential leak. The credential list on the hacking site listed several usernames along with their passwords, and the website they belonged to, suggesting that the credentials were obtained using password stealers and similar malware.
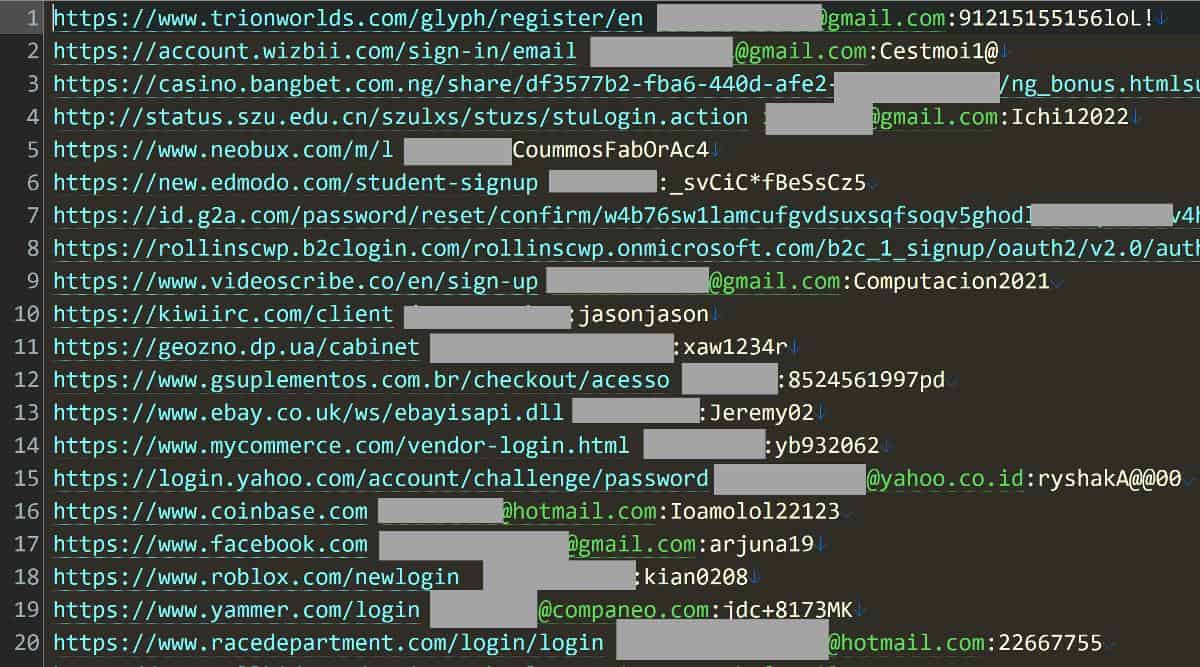
The screenshot here is a small example of the data that was leaked in the credential stuffing list. The actual list has 312 million rows of email addresses and passwords, that's scary, but to be fair, the passwords seen above aren't strong.
In order to verify whether the leaked credentials were legit, Hunt reached out to some HIBP subscribers, and asked them to verify if their data was accurate. Some of them reported that the leaked usernames and passwords were real, and that they were used in 2020 or 2021.
While password stealer logs and password stuffing lists were involved in the data leak, Hunt mentions that not all the credentials were sourced in the same manner. His own email address was leaked with a password that had not been used for a decade, and it was not accompanied by a website to suggest it was stolen by malware.
How to check whether your email address and password has been leaked online?
Have I Been Pwned offers an option that will notify you when your email gets leaked, all you need to do is enter your email address and let the service do the rest. Alternatively, you can check out Firefox Monitor which does the same thing, but uses k-Anonymity to protects your email by hashing the data before sending it to HIBP. Firefox Monitor uses HIBP as the source to keep an eye on data breaches and leaks, to monitor whether your email address has appeared in a known breach. In case it finds your email ID in a breach, you will be notified about it.
Don't sweat it if your email address ever gets leaked publicly, it doesn't mean you need to stop using it. All you need to do is reset the password of the account, and protect it by enabling two-factor authentication. Don't rely on SMS based codes, as they are prone to hacks, instead you should use an authenticator app, or a physical security key and use them to get TOTP codes for your accounts.
Use a password manager like KeePass or Bitwarden to generate strong, unique passwords for your accounts.


















The issue is that people don’t know what account has been compromised unless there’s a tool to interrogate this data.
Sincerely, what a mess that hackers can get access to passwords such in an easy way! :[