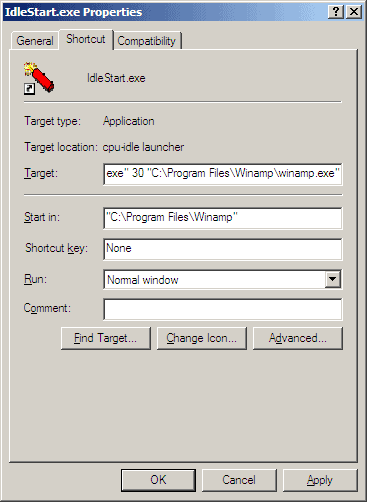
Idle Time is the time where the computer is just sitting idle using little to no cpu power. This happens on my computer for instance if I leave it on to finish a download and after that download finishes it wastes some power doing nothing. A good way to put your cpu to good use during that time is to start a program once the computer has been idle for some time.

Torrent websites are much like Linux distributions, there are so many out there that it is easy to lose the track. Torrent search engines can be divided into two categories: Site search engines and meta search engines. Site search engines obviously only search the torrents that are hosted on one selected website while meta search engines crawl the databases of several torrent websites which often leads to better results.

Am I the only one that is starting to get confused by all the online services offered by Microsoft, Yahoo, Google and others ? Microsoft seems to have jumped fully on the "Live" bandwagon branding every new online product with it. The newest is called Office Live Workspace [link] and is currently in public Beta.
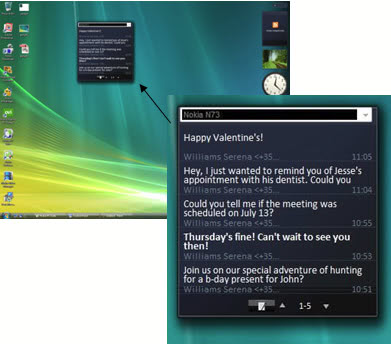
Although I'm not a big messaging fan, this is one gadget I would find really useful. I owned Nokia phones for about ten years and I loved every one of them. The […]
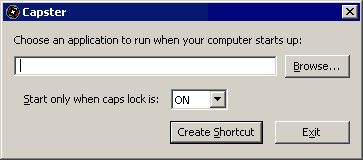
Ever felt the need to start an application during Windows startup every now and then but not all of the time ? Maybe you want to quickly start and play the new game that you recently installed, or just browse through your emails as quickly as possible without having to go the extra mile and start the application manually.
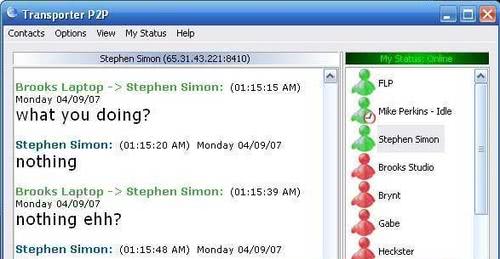
I have been testing an application called Transporter P2P for the last few days which can be described as a elegant way to share files and chat with contacts using P2P connections. A main difference between Transporter P2P and Skype for instance is that the former is server independent which means more privacy and security. The setup on the other hand is a little bit complicated because of the serverless design.
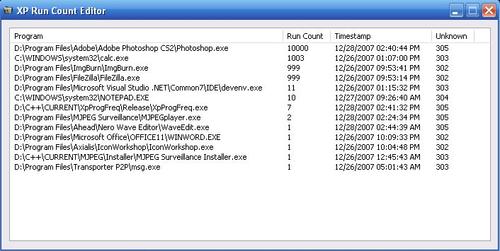
Windows XP keeps track of how many times an application has been started by a user of the system and displays the most frequently used programs in the start menu. That's a pretty convenient feature for some users but there is no obvious way to control which applications are listed in the start menu.
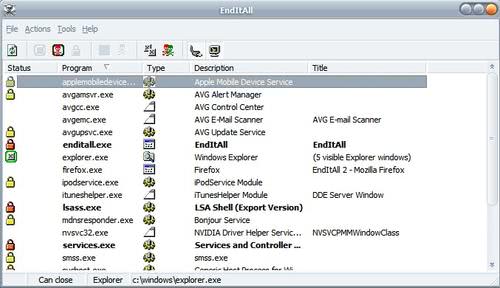
It sometimes is a good idea to close most processes and programs at once. Could be helpful if you want to run a very resource intensive program or an application asks you to close all programs open before continuing. This happens when you install some programs or run utilities like scandisk or defrag.

I received an email today from a reader who told me of a problem that he encountered lately on his computer. The message Say no to drugs appeared whenever he clicked on a shortcut to the My Documents folder. This sounded clearly like a virus and a quick search revealed that it indeed was the I Love Her virus.
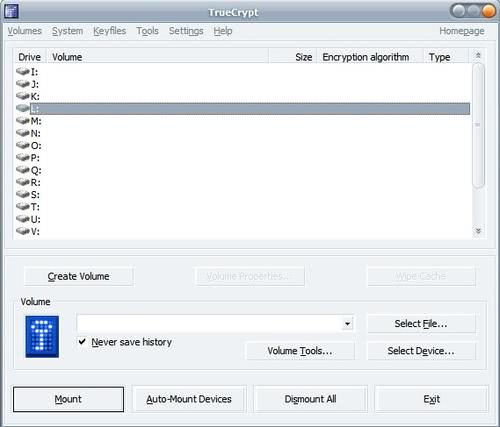
My last True Crypt guide dates way back and the purchase of my new shiny 500 Megabyte Maxtor USB drive made me think about writing a new guide that takes the changes of the software into account. My old Teac USB drive started to behave weirdly every now and then which I saw as a first sign of reaching the end of its life cycle and since I did not want to take any chances I decided to buy a new drive, encrypt it with True Crypt and transfer all the files from the old device to it.
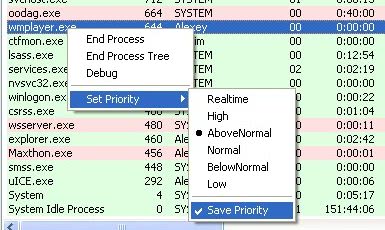
There is no automatic way to adjust the priority of a process in Windows using the default tools supplied by Microsoft. It is possible to adjust the current process priority but this setting is only valid for the current setting. Once the process gets killed, for example by closing the application or rebooting, it reverts the priority back to the default one.

I always thought that free meant that I did not have to do anything to get the free item or service. I had a problem with the Adobe PDF Reader and a huge 35 Megabyte PDF which took ages to load and decided to install all the latest versions of alternative PDF viewers. The Adobe PDF Reader was not rendering the pdf file properly and it took ages to scroll and change settings.
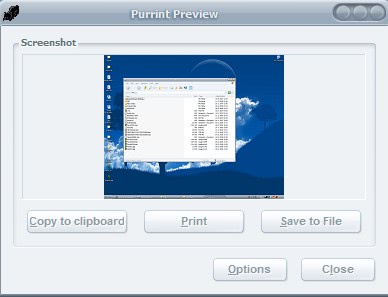
Have you ever wondered why the Print key does not do what it's label says - that is print - but copies a screenshot to the clipboard instead? Why is it doing […]
Avedesk was mentioned on one of my favorite websites Donation Coder and it sounded so incredible that I had to give it a try immediately. One could say that Avedesk adds widgets to your desktop, not the kind of useless widgets like the clock in Windows Vista. I'm talking about widgets that look great and provide enough functionality to justify their presence on the desktop.
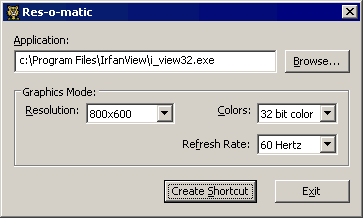
Did you ever run an application that was designed for a specific resolution on your new shiny 1920x1200 monitor only to find out that it was almost impossible to work with it in that resolution ? I'm not only talking about old DOS games here but also about presentations for instance or applications that have been developed in house. Basically everything that goes full screen automatically could be affected as well.

Msconfig is a standard system tool in Windows where users can, among other things, disable startup items. It's a great tool if you do not have any other software like Autoruns or Starter in reach that deal with startup programs more efficiently. If you use Msconfig all the time you will notice that deactivated entries will not disappear and that there is no way to delete them permanently from being displayed in the tool.
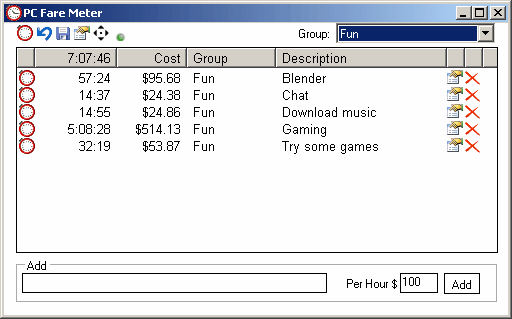
You are gonna love the PC Fare Meter software if you are paid by the hour and have difficulties keeping track of the time that you spend working for your clients. One could say it's a time tracking application but that would fall a bit short, it's more than that. The most important feature of this software is to keep records of the time each application has been used on a computer.
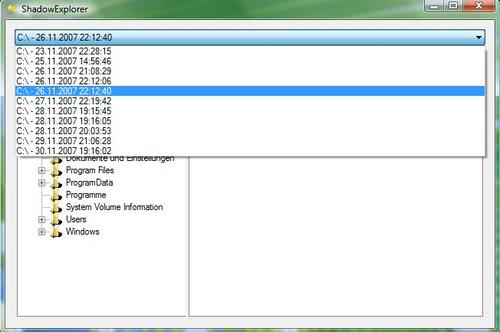
Shadow Copies have been introduced into Windows XP Service Pack 1 and been extended in Windows Vista where it is used in System Restore and backup utility. You might have come upon the problem that a file was in use when trying to copy, move or delete it. Shadow Copies are used to copy every file, basically state of the art read only copies of files on the hard drive. This means that even important system files that are running all the time can be backed up without difficulties.

I discovered an interesting video at Hack a Day from the University of Princeton demonstrating how to break disk encryption using so called RAM Dumps. This basically takes into account that the encryption key is stored in RAM. While most disk encryption mechanisms are vulnerable while the computer is on or in sleep mode some are even vulnerable when powered off.

There are several third party applications that make it possible to create PDF documents from within Microsoft Office. Most of these add a virtual printer that converts the Microsoft Office document to PDF. There is however an official way to add PDF - and XPS - support to Microsoft Office 2007 and its various programs like Microsoft Office Word 2007, Microsoft Office Excel 2007 and Microsoft Office PowerPoint 2007.

There is no shortage of programs that tweak settings in Windows Vista. WinBubble is another addition to the growing assortment of tweakers, and not a bad one it is. The tweaks can be accessed through a series of tabs, like Security, Optimize and IE in the software.
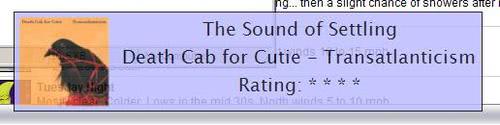
The application iTunes Control is an add-on for Apple's iTunes software. It mainly adds two functions to iTunes, the first is a customizable on screen display of the track that is currently playing and the second are more than 20 hotkeys that make it easier to run iTunes in the background.

Versioning is a pretty useful concept. It basically means backing up documents and files before changes are made to it so that the user can revert back to a previous version with ease. Versioning is not limited to text documents, it can also be used for images or coding applications.

You might know that I regularly check all running processes as part of a cleanup process. It is also important from a security point of view. I spotted the file vssvc.exe today running on my computer and I was pretty sure that it was not running last time I checked. A quick check reveled that it was related to the Volume Shadow Copy Service in Windows XP.

Several applications that connect to the Internet have options to limit the upload and download bandwidth. This is excellent if you need bandwidth for other tasks as well, for instance if you want to watch Internet TV while downloading from P2P networks. But what can you do if an application that connects to the Internet does not have such an option, if it regularly uses all of your bandwidth and slows down other applications because of it ?
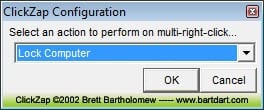
I have always asked myself why there is no way to configure a function for double right-clicking. You can configure the left mouse button double-click but not the right mouse button one. Click Zap is a small application that lets the user configure a function for a double-click on the right mouse button.

Shock Desktop is a Windows application to manage the desktop icons. Users can create profiles which save the current icon layout of the desktop. Loading that profile again resets the desktop to that icon layout. It happens for instance that icons get moved if the user changes the screen resolution. This can be undone with the application.
Piky Basket is a Windows shell extension that lets you add files and folders from different locations of your hard drive to a virtual basket to perform file operations on all of the files and folders at the end. You basically select as many files and folders as you like from your system and perform a file operation on them afterwards.

I have been in contact with the creator of the excellent DefenseWall HIPS application for some time now and he was so nice to give away ten copies of his software to Ghacks readers. Let me first explain what the software does. DefenseWall HIPS is a Host Intrusion Prevention System that uses sandboxing and virtualization to protect the computer from dangers that are not stopped by anti-virus applications.

I'm normally very cautious when I read about free offers on the Internet. It is often the case that free does not really mean free. This time however it seems to be the real deal, that is if you are a student from one of the following elven countries: US, UK, Canada, China, Germany, France, Finland, Spain, Sweden, Switzerland, and Belgium.

The glorious idea to kick file sharers off the Internet, effectively banning them from accessing the Internet, seems to be in consideration in Australia in an effort to fight Internet piracy. It does not happen very often that I'm left totally speechless but this proposal succeeded. I really don't know how to reply to such an idiotic proposal.

A visitor was asking me a while ago if there were really download managers for websites like Rapidshare and I simply told him at that time that they would exist. JDownloader is a Rapidshare Download Manager that comes with a lot of functions to make downloading files from Rapidshare and dozens other file hosting websites a breeze.
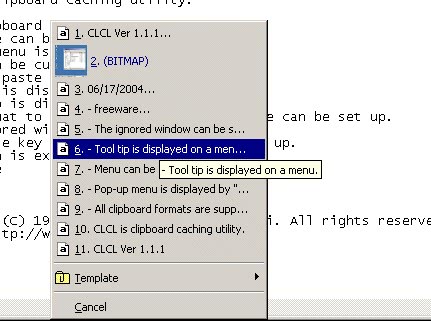
The Windows clipboard function is not really practicable. It stores only the last text string that you have copied and once you copy another one the previous one is not longer available. It happened more than once that I lost a text phrase that I still needed because I accidentally copied another item to the clipboard.
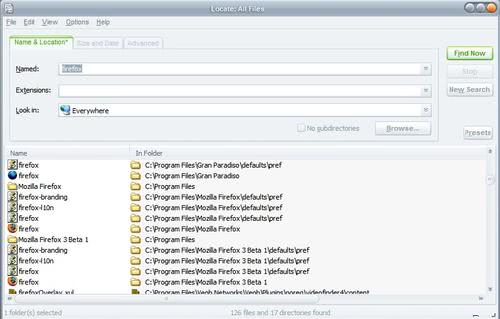
Locate is one of the fastest ways to search for files and content in files in Windows. It uses a file database which is created once at first run and then updated […]
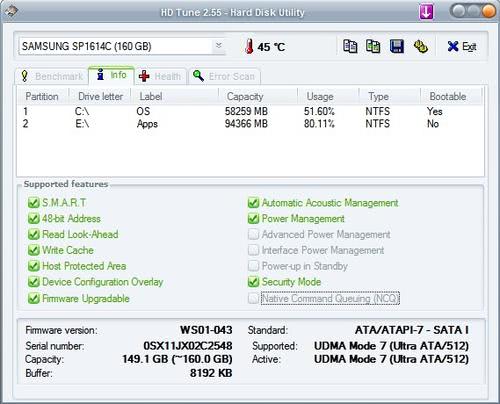
HD Tune is a hard disk analyzer that offers a wealth of information about the internal hard drives that are connected to the computer. It does display general information like the type of the hard drive, the serial number, capacity, firmware version and buffer size which are nice to know because it allows you to check if that hard drive is the correct one. I remember more than one instance where a friend of mine bought a hard drive only to find out that the clerk handed him one that had a lower capacity and different model number.

I regularly have to create pdf invoices which some companies seem to prefer over other forms of documents and I have been using doc to pdf online converters until now that would convert the Microsoft .doc file into the Adobe .pdf file. I have two major problems with this procedure however.
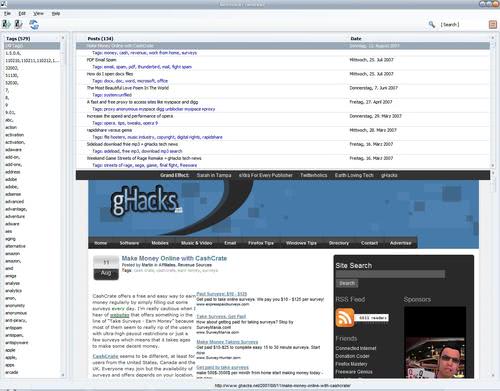
Delicious is a nice website to discover new interesting websites. I was however never that fond of using it to store my own bookmarks but for the reason to promote my websites to a large audience. If I want a way to store bookmarks I rely on my browser and not a website that does that for me. Call me old fashioned but that's how I think about this.

Where do you store your usernames and passwords ? In a text document on your computer ? In your wallet ? Storing sensible information like passwords, but also other type of data like information about medication or credit card numbers, unencrypted is a security risk. If someone is after those information he immediately knows how to use them against you.
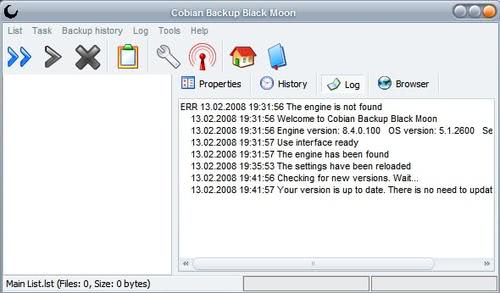
I'm using three dedicated servers at the moment with more than a Terabyte of free hard drive space. I thought of some good uses for that space and came up with the idea to use it to store backups from my computers. The plan is to use the backup software Cobian Backup 8 to create scheduled backups and upload those backups straight to my root server using an ftp account I created for that purpose.

Microsoft released their monthly security bulletin yesterday which listed 11 security bulletins containing a total of 17 patches for operating systems and software like Internet Explorer and Microsoft Office. Six of the eleven security bulletins are critical while the remaining five are considered important.