Defeating Disk Encryption
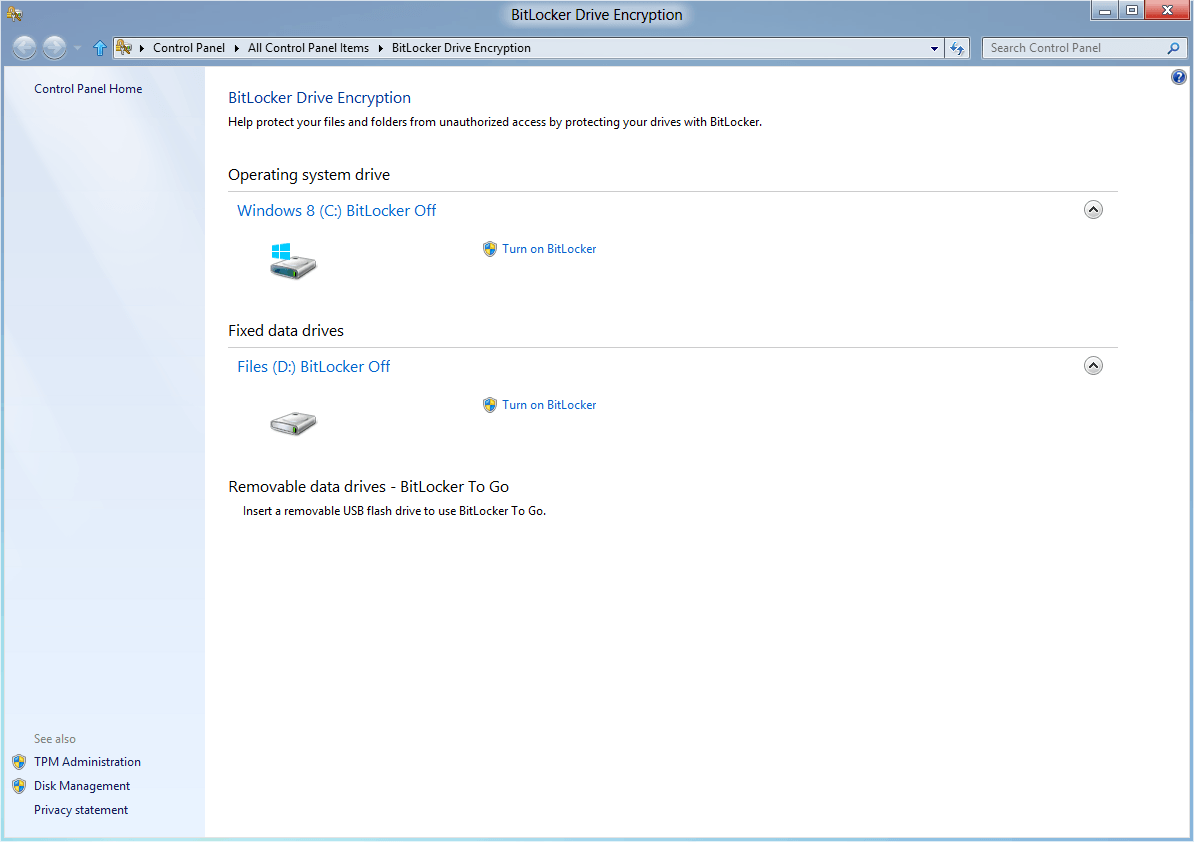
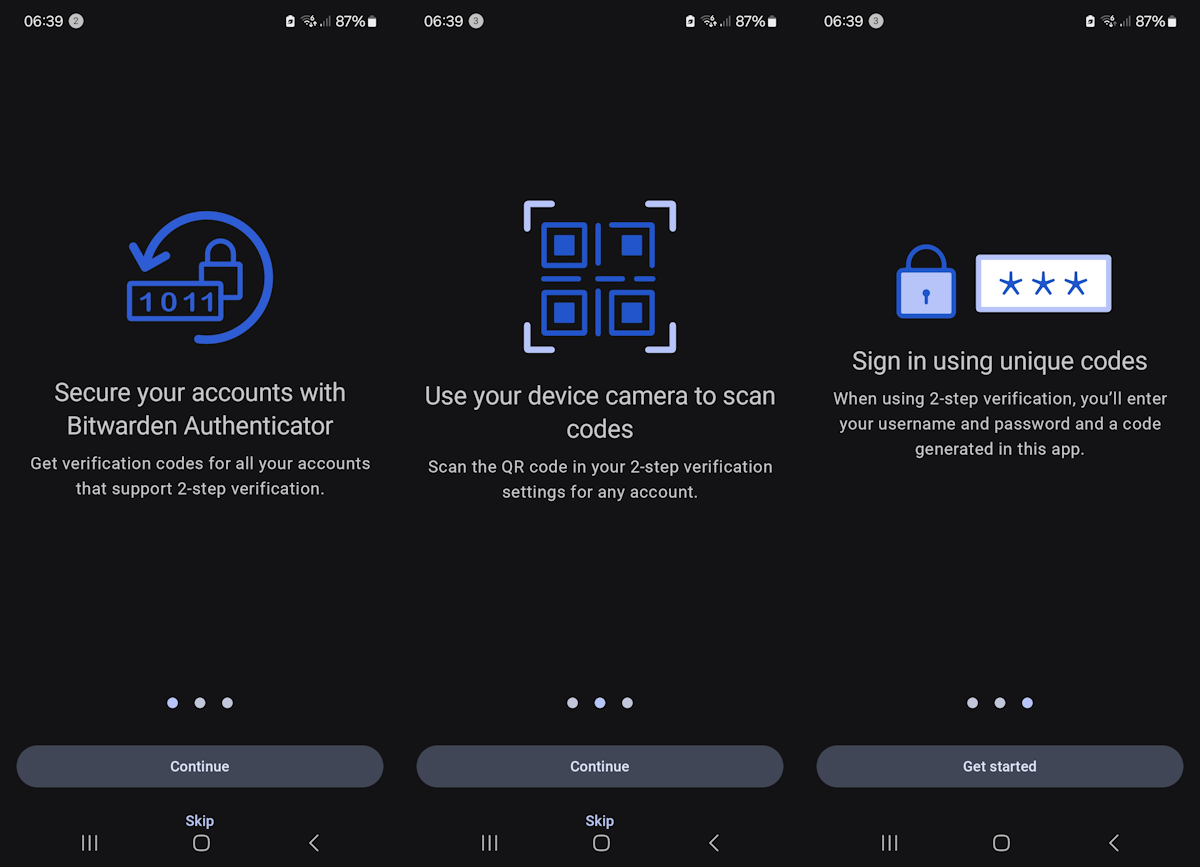
I discovered an interesting video at Hack a Day from the University of Princeton demonstrating how to break disk encryption using so called RAM Dumps. This basically takes into account that the encryption key is stored in RAM. While most disk encryption mechanisms are vulnerable while the computer is on or in sleep mode some are even vulnerable when powered off.
What the researchers did was to boot the computer from an USB drive that loads a RAM dumping program. Tests conducted by the University of Princeton showed that it took between seconds and minutes before data that was stored in RAM was completely erased. The RAM also vanished in a predictable manner.
It's interesting to see that cooling the RAM down to minus 50 degrees prolonged the time the data was readable, it was clearly readable after ten minutes. It's a very interesting video in my opinion.
If you never thought about using a BIOS password and disabling booting from USB devices and CD / DVD before you should start thinking about it right now. That is if you use disk encryption.
Physical access to the PC is obviously required for this method, and that requires some level of preparedness on behalf of the people who try to dump the RAM and extract the encryption key this way. There is no sure fire way to protect the system against this attack if the attackers are prepared. While you can add a BIOS password to the PC and block booting from USB drives or CD and DVDs, it is still possible to take the RAM out of the attacked PC to insert it into a portable reading station or even another PC or mobile device.
Advertisement


















I dont think its possible to do this on Drivecrypt before it loads into operating system anyway.
So don’t leave notebook turned on and unattended. Actually this was very good idea even before these possible attacks. :)
wow … that was clever !!! :)
Probably the next step in encryption would be mapping RAM’s capacitors and deliberately storing the key at different locations and different RAM modules (most of us have dual channel RAMs now, isnt it). Is that even possible??
Also, adding redundancy to confuse the hacker should be useful too!!
Hehe you are right of course, but it’s better than nothing :)
“If you never thought about using a BIOS password and disabling booting from USB devices and CD / DVD before you should start thinking about it right now. That is if you use disk encryption.”
<-That doesn’t really help you, if you put the RAM into another computer, like in the video mentionend! The BIOS settings aren’t stored in RAM :-)
I wonder if they can defeat the TrueCrypt 5.0 encryption using this technique?