Retrieve serial numbers, product codes and login information on Windows with recALL
Whenever you are switching from one PC to another, or upgrading your current one by installing a new operating system, you may want to take certain applications, programs and information with you.
If you paid for a program for example, you may want to keep on using it on the new PC.
The same is true when you about to re-install a software on the system or upgraded to a new version which did not carry over information stored by the old version.
One problem that can arise here is that you cannot look up the product key anymore. Maybe you have lost the email or cannot find it anymore.
The same is true for information. If you have configured the excellent WinSCP program to save username and password, you may want to carry those over as well to the new system.
recALL
The free program recALL can do that for you. It works similar to other programs of its kind but seems more extensive than programs that I came across until now.
The main reason for that is its impressive support of programs. You can check out the supported list of applications on the (Polish) homepage of the application. According to it, more than 3000 programs are supported by recALL at the time of writing.
The program can retrieve serial codes from numerous software programs including Fast Picture Viewer, Newsbin or Microsoft products such as Office.
In addition to that, it can retrieve login information from many communication programs including web browsers, ftp clients, messenger applications or database programs.
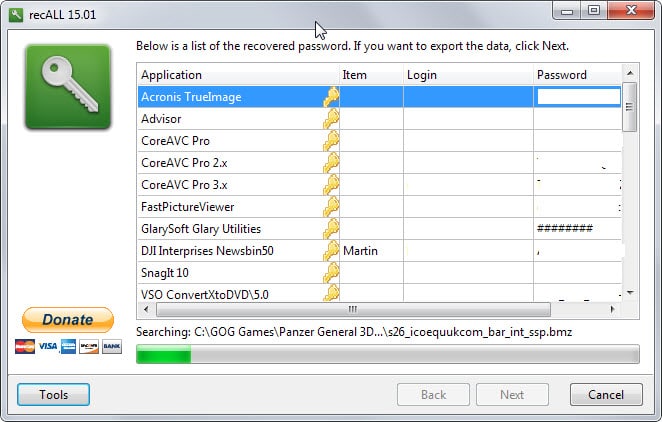
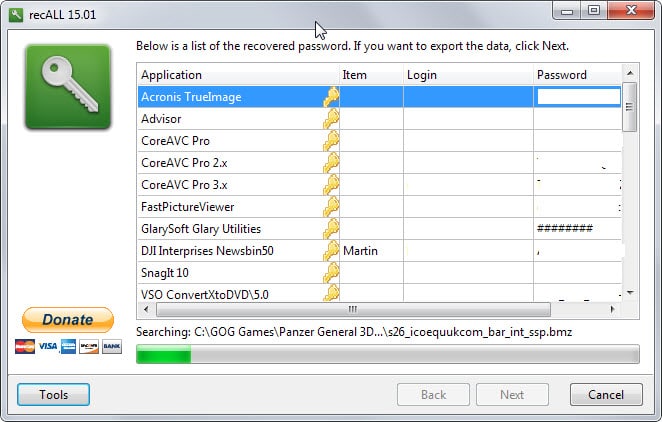
When you first start the program you get the option to run an automatic scan of the system, run a manual scan by selecting a file, or use the server emulation mode which recovers email program and ftp passwords (which the automatic scan may also be able to do).
The automatic scan searches the whole system for serial numbers and accounts to display all that it finds in the program interface.
You can use Ctrl-c to copy the information of the highlighted row or rows to the clipboard. The other option that you have is to double-click on a row to display the information in text fields that you can copy individually.
The information found during the scan can be exported after it completes. Formats supported include plain text and comma separated files, but also KeePass XML 1.x format files which can be useful to users of the password manager.
You can download a portable version of the program from the developer website.
Closing Words
recAll is a great program that can retrieve product keys and login information stored by Windows or programs running on the operating system.
It supports more than 2500 programs in total and is useful not only when you plan to move to a new PC or install a new operating system on the existing one, but also when you reinstall software and need that serial number again to register it or need the login information used by the application.


























It wasn’t to long ago that I covered a crap load of Product Key recovery programs and this one seems to be neat in that it can recover User Accounts and passwords. Here’s the ones that I did a few months ago:
Thanks for the Tutorial Martin, Now for a load of links that you can write about one day in a tutorial.
https://sites.google.com/site/cakirbey/
https://sites.google.com/site/cakirbey/softkeyrevealer
http://www.freewarefiles.com/downloads_counter.php?programid=18853
http://ychatsharp.com/
http://www.lazesoft.com/lazesoft-windows-key-finder.html
http://www.klinzmann.name/index.htm
http://www.abelssoft.net/apps/mykeyfinder/#/details
http://www.ottsolutions.com/products.htm
http://davehope.co.uk/projects/product-key-finder/
http://www.softpedia.com/get/System/System-Info/Product-Key-Informer.shtml
http://www.nirsoft.net/utils/product_cd_key_viewer.html (May get flag! with Malwarebytes warning!!)
http://www.rjlsoftware.com/software/utility/winproductkey/
http://www.majorgeeks.com/files/details/rockxp.html
http://www.sterjosoft.com/key-finder.html
https://www.magicaljellybean.com/keyfinder/
http://wpkf.codeplex.com/
http://unlockforus.blogspot.ca/2008/01/winguggle-get-your-windows-vista.html
https://www.winkeyfinder.com/
Other applications that maybe of interest:
http://www.lookinmypc.com/
http://www.gtopala.com/#axzz3OGVAEVqh (Purchase)
http://www.piriform.com/speccy (System Information and OS Product Keys)
I tried out this utility on my Windows 8.1 box. This utility is basically useless. Between Windows, Office, wireless passwords, and other applications it was all incorrect or empty.
* Wireless Networks – no passwords shown
* MS License keys – Looks correct but are some obfuscation of the original key
* Various other softwares – Nothing or bad data
* Vmware workstation 11 – this was correct
* Filezilla – extracted passwords from favorites
* Trillian – extracted login password to Trillian
* Firefox – Found the legacy FF sync system password
@chesscanoe My thoughts precisely!
@keit_co and the moment you turn the interwebnets connection back on, the program just behaves itself? If if we uninstall it before switching the net back on, there’s any number of ways the program could leave behind a ‘phone home’ scenario.
hello martin, i am not a techy guy, finally i am happy that situation came for me to ask my long lasting doubt,
i am using an asus netbook where windows 7 was pre installed. the product key was written on a sticker which was sticked at the back. now the sticker is araised. i dont have cd or anything which i got along with the laptop. now will this recall software help me to get my windows key? or is there a way other?
@ prabhu — You can use the command-line in Windows 7 itself to see your OS product key. No need to use or install 3rd-party apps. For the 2 methods below, start by *running Command Prompt as administrator*, then input the command as shown in italics.
systeminfo | find /i “product id”
[Method 1]: Type or paste the above (including quotation marks) at the command prompt. It might take a couple of seconds to output the product key of your OEM Windows. You will see this: Product ID: xxxxx-OEM-xxxxxxx-xxxxx
wmic
os
[Method 2]: Type “wmic” (without quotation marks) at the 1st command prompt, followed by “os” (without quotation marks) at the next command prompt that results. Scroll your command prompt window 60-70% to the right, & look for the label “SerialNumber”. Your OEM Windows product key will be indicated there.
You can use a program like http://www.nirsoft.net/utils/product_cd_key_viewer.html for that. Works in most cases and should display the product key to you.
Another answer which will also show much useful information is to run Belarc Advisor.
http://www.belarc.com/free_download.html
Right, good program!
Malwarebytes encrypts the product install code key. Is there any software that will unhide the product key, for folks who lose their copy after installing.
Thank You.
Amazing
This is very useful, thanks for sharing it with us.
V for being Portable.
Thank you for this review!
How does this compare to Belarc Advisor — more, less extensive?
Belarc servers a different purpose. When you compare the account/license finding, it is recAll which is more extensive.
Great little hack tool–doesn’t send a flag to antivirus, etc.
On the Polish website, it says the tool can be use to gather Product Keys and passwords on a “damaged” system. In what ways I wonder.
The program finds long forgotten passwords for sites rarely used or visited–ethical use of tool. Shows recurring patterns of password usage which can then be used to change weak or overused passwords.
If using it for reinstall, don’t I have to also use the Hard Disk Serial changer?
Where does Advanced Tokens Manager come into the picture–activation may fail?
> On the Polish website, it says the tool can be use to gather
> Product Keys and passwords on a “damaged” system. In
> what ways I wonder.
From another system, there is native registry support in program (REGF like SYSTEM, SOFTWARE, USER.DAT etc). If password is not DPAPI protected and doesn’t use UNIQUE ID (like serial number) you can recover data by selecting this files
> If using it for reinstall, don’t I have to also use the Hard Disk Serial changer?
after format HDD will have new serial id, reinstalling doesn’t change so in some apps you can recover passwords (like PowerArchiver which uses HDD serial)
> Where does Advanced Tokens Manager come into the picture–activation may fail?
Only string based password can be recovered.
I’d feel less paranoid if I had some basis for trust that the application would not use the info gathered nefariously.
@chesscanoe: you can turn off internet connection when scanning.
But … I only have two programs installed (excluding flash, silverlight, f.lux, open-dns, and about 10 other system behind-the-scenes items – none of which need keys). Everything else is portable, free &/or open source. Migrations are simply a copypasta from my backup portables dir [except system settings such as default programs]. Even the shortcuts are relative path [using PStart]. The two “programs” I have installed, FYI, are MS Office [because my clients use it so I need to be able to sort out their problems with it] and Photoshop [versions of which I have used for 15+ years and can’t be arsed moving to GIMP]. However, I should really move to Open Office / Office Libre – I forget which one I was more interested in.
However .. back in the day (and what I make my clients do], I always stored all installs and serial keys etc in subfolders in a folder called Apps and included it in the backup. Some software clients have is legacy and you just can’t get it anymore. Also included is any information on specific settings or dependencies (eg some old crap requires the borland database engine installed .. *sigh*).
Personally – I believe trolling thru the registry system to retrieve keys is a dirty fix caused by people not prepared to use any foresight :)
Class … discuss
Put it on a folder (even a backup) is risque due to possibility of file corruption, human error ( “I didn’t need this folder, right?” ), and other minor things that happens. I do agree it’s very convenient and many cases would work well but storing hard copies of the information is always the best bet. When I do a reinstall of their software, I put all the keys into a folder (physical) and have them store it with their tax information or other valuable information. Safe and secure and 90% of the time they know where it’s at.
Indeed. Backups are multiple (eg I have one client where the backup is automatically done on alternate external drives each day in its own daily folder – eg ext1 has a Mon, Wed, Fri, Sun backup folder and ext2 has the other three – using FreeFileSync) , as well as a manual once a month off-site external. So eight copies over three drives. The human error part (if he deletes a folder by mistake) is a worry, as FreeFileSync is set up to mirror local onto external. But the keys are safe/duplicated.
Part of this as well is KeePass – in which all information is stored (software keys, network settings, passwords & accounts, printer default passwords .. you name it, its in here). The only people with keys to this are 1. Client, 2. Me (I keep client keepass passwords in my own keepass) and 3. On death of client, the lawyer/estate. This particular client also has a printout of everything in KeePass (which is kind of a security hole, but then so is a rubber truncheon, and it’s the client’s choice). The main thing is, if he dies, his family/estate can control his online accounts – dropbox, facebook, emails etc.
So .. eight copies, on three drives, in two physical locations .. plus the master copy on the PC .. and double that for keys also stored in KeePass .. plus a printout .. and the client doesn’t mess with folders (basically never goes into Windows Explorer) or need to structure/rename things – I essentially futureproofed him. There are some flaws in the backup plan, but this is the best solution for him (knowing what I know and what he has to backup).
Flaws – any virus (eg crypto) can access the externals (i have his automated and plugged in all the time – other clients do it manually and the backup is only plugged in when needed), no way after 7 days to retrieve a deleted/corrupted file (except if lucky on monthly external backup – i.e no version history) and not real-time.
Thanks, very helpful. :)