Kaspersky uncovers ongoing Operation Triangulation

Operation Triangulation has come to light as Russian cybersecurity firm Kaspersky reveals a series of ongoing attacks on iPhones. The campaign utilizes an iOS vulnerability and exploits iMessage zero-click techniques to install malware without any user interaction.
Kaspersky, in its efforts to combat this threat, has named the operation "Operation Triangulation" and is urging individuals with information to come forward and collaborate.
This article delves into the details of the campaign, its impact, and the subsequent accusations made by Russia's FSB intelligence and security agency.
Operation Triangulation exploits iOS vulnerability
According to Kaspersky's investigation, iPhones connected to their network have fallen prey to hackers employing an iOS vulnerability, leveraging iMessage zero-click exploits.
These techniques enable the delivery of malicious code to the devices without requiring any user interaction. Exploiting this flaw, attackers can discreetly download additional malware from their servers. While the initial message and attachment are swiftly erased, a concealed payload with root privileges remains, allowing the perpetrators to collect sensitive information, execute remote commands, and maintain persistence.
Operation Triangulation provides an in-depth analysis of the malware
In response to the challenges posed by iOS's closed system, Kaspersky utilized the Mobile Verification Toolkit to conduct an extensive analysis of the malware. By creating filesystem backups of infected iPhones, crucial insights into the attack process and the malware's functionality were uncovered. Despite the malware's attempts to erase traces of its presence, indicators of infection persist. These include modifications to system files hindering the installation of iOS updates, abnormal data usage patterns, and the injection of deprecated libraries.
Further examination of the collected data revealed that signs of infection were first observed in 2019. Notably, the most recent version of iOS targeted by this malicious toolset was 15.7, while the latest major release at the time of analysis was iOS 16.5. It is essential to consider that subsequent iOS updates may have addressed the vulnerability exploited in these attacks, mitigating the risk for devices running the latest versions.
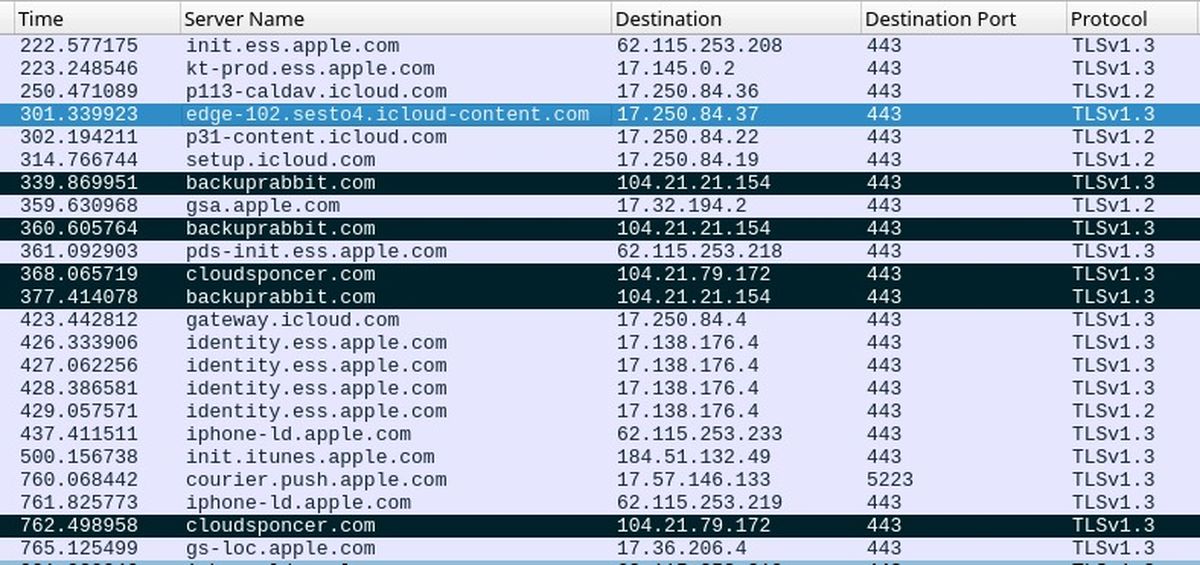
Domains associated with malicious activity
Kaspersky has provided security administrators with a list of 15 domains associated with the Operation Triangulation campaign. By analyzing historical DNS logs, administrators can identify potential signs of exploitation on their devices. Once the malware escalates privileges, it downloads a comprehensive toolkit that grants the attackers control over executing commands, collecting system and user information, and fetching additional modules from a command-and-control (C2) server.
It is worth noting that the APT toolset used in these attacks lacks persistence mechanisms. Therefore, a simple reboot of the device effectively terminates the malware's operations. However, as the analysis of the final payload is still ongoing, specific details about the malware's functionalities remain limited.
Russia accuses US
Coinciding with Kaspersky's report, Russia's FSB intelligence and security agency has made allegations suggesting Apple's collaboration with the NSA. The FSB claims that Apple deliberately provided the NSA with a backdoor, enabling the infection of iPhones in Russia with spyware. They further assert that numerous devices belonging to Russian government officials and personnel from various embassies have been found to be compromised. However, the FSB has not provided concrete evidence to support these claims.
Previously, the Russian state advised its presidential administration and government employees to transition away from Apple iPhones and avoid American-made technology. Kaspersky confirmed the impact of the attacks on its Moscow headquarters and employees in other countries. However, the company clarified its inability to verify a direct link between its findings and the FSB's report, as it lacks access to the government's technical investigation details. Nevertheless, Russia's CERT has issued an alert aligning the FSB's statement with Kaspersky's findings.
Advertisement


















“According to sources, the requirement to abandon the iPhone is associated with security considerations: in their opinion, these gadgets are more susceptible to hacking and spying from Western experts compared to other smartphones.”
https://www.kommersant.ru/doc/5886759
Never use anything Apple.
https://en.wikipedia.org/wiki/PRISM#/media/File:Prism_slide_5.jpg
I trust Kaspersky. Have trusted them for a long time. I have not fallen for the anti-Russian propaganda.
Kaspersky is like a pyromaniac firefighter. Suuuure, we believe you “found” this vulnerability and thank GOODNESS you are the good guys letting us know all about it and saving the day!!! I shall now most certainly buy all your products and tell my friends and family to do the same. Always trust a Russian! Ask anybody.