Microsoft Security Bulletins For January 2016
Welcome to the Microsoft Security Bulletins overview for January 2016. It is the first patch day of the year by Microsoft and also the last day Microsoft's Windows 8 operating system is supported by the company.
This means that Windows 8 systems won't receive any more security updates, and that systems that are still running the operating system need to be updated to Windows 8.1 to continue receiving these important updates.
Microsoft will retire several versions of its Internet Explorer browser as well today. Only the latest version available for supported operating systems will remain supported, while all other versions of Internet Explorer will receive no future updates on those systems.
It affects Windows 7 and 8 systems the most, as Internet Explorer 11 may not be installed yet on those systems as it has been made available as an update only.
Microsoft will deploy a special update on versions of Windows that have older versions of the browser installed even though a newer version is available.
The guide starts with an executive summary after the introduction which highlights key information. It is followed by distribution information listing how Microsoft Windows operating systems and other Microsoft products are affected this month.
The next part lists all security bulletins released by Microsoft on this January Patch Day, as well as security advisories and updates, and non-security updates released by the company since December 2015's Patch Day.
Download instructions and resources that provide additional information make up the last part of the overview.
Microsoft Security Bulletins For January 2016
Executive Summary
- Microsoft released 9 security bulletins in January 2016.
- Six of the bulletins have an aggregate severity rating of critical, the highest rating. The remaining bulletins one of important, the second highest rating.
- All client versions of Windows are affected by at least one critical vulnerability and exactly two important vulnerabilities.
- Other Microsoft products affected by security issues in January 2016 are Silverlight, Microsoft Office, Microsoft Exchange and versions of SharePoint.
Operating System Distribution
All Windows client and server systems are affected in the same way. The exception to this is Windows 10 and its 2 critical bulletins. The reason why Windows 10 is affected by another bulletin as the only client system is because of its two system browsers Internet Explorer and Microsoft Edge.
- Windows Vista: 1 critical, 2 important
- Windows 7:Â 1 critical, 2 important
- Windows 8 and 8.1: 1 critical, 2 important
- Windows RT and RT 8.1: 1 critical, 2 important
- Windows 10: 2 critical, 2 important
- Windows Server 2008:Â 2 important, 1 moderate
- Windows Server 2008 R2: 2 important, 1 moderate
- Windows Server 2012 and 2012 R2: 2 important, 1 moderate
- Server core: 2 important
Other Microsoft Products
All versions of Microsoft Office, as well as other Microsoft products such as Silverlight or Exchange Server are affected by vulnerabilities.
- Microsoft Office 2007, 2010, 2013 and 2016: 1 critical
- Microsoft Office 2013 RT: 1 critical
- Microsoft Office for Mac: 1 critical
- Microsoft Office Compatibility Pack Service Pack 3, Microsoft Excel Viewer, Microsoft Word Viewer: 1 critical
- Microsoft Silverlight: 1 critical
- Microsoft SharePoint Server 2013: 1 important
- Microsoft SharePoint Foundation 2013: 1 important
- Microsoft Exchange Server 2013 and 2016: 1 important
- Microsoft Visual Basic Runtime 6.0: 1 important
Security Bulletins
MS16-001 - Cumulative Security Update for Internet Explorer (3124903) - Critical -
Remote Code Execution
This security update resolves vulnerabilities in Internet Explorer. The more severe of the vulnerabilities could allow remote code execution if a user views a specially crafted webpage using Internet Explorer.
An attacker who successfully exploited this vulnerability could gain the same user rights as the current user. If the current user is logged on with administrative user rights, an attacker who successfully exploited this vulnerability could take control of an affected system. An attacker could then install programs; view, change, or delete data; or create new accounts with full user rights.
MS16-002 - Cumulative Security Update for Microsoft Edge (3124904) - Critical - Remote Code Execution
This security update resolves vulnerabilities in Microsoft Edge. The vulnerabilities could allow remote code execution if a user views a specially crafted webpage using Microsoft Edge. An attacker who successfully exploited the vulnerabilities could gain the same user rights as the current user.
Customers whose accounts are configured to have fewer user rights on the system could be less impacted than those who operate with administrative user rights.
MS16-003 - Cumulative Security Update for JScript and VBScript to Address Remote Code Execution (3125540) - Critical - Remote Code Execution
This security update resolves a vulnerability in the VBScript scripting engine in Microsoft Windows.
The vulnerability could allow remote code execution if a user visits a specially crafted website. An attacker who successfully exploited this vulnerability could gain the same user rights as the current user.
If the current user is logged on with administrative user rights, an attacker who successfully exploited this vulnerability could take control of an affected system. An attacker could then install programs; view, change, or delete data; or create new accounts with full user rights.
MS16-004 - Security Update for Microsoft Office to Address Remote Code Execution (3124585) - Critical - Remote Code Execution
This security update resolves vulnerabilities in Microsoft Office. The most severe of the vulnerabilities could allow remote code execution if a user opens a specially crafted Microsoft Office file.
An attacker who successfully exploited the vulnerabilities could run arbitrary code in the context of the current user. Customers whose accounts are configured to have fewer user rights on the system could be less impacted than those who operate with administrative user rights.
MS16-005 - Security Update for Windows Kernel-Mode Drivers to Address Remote Code Execution (3124584) - Critical - Remote Code Execution
This security update resolves vulnerabilities in Microsoft Windows. The more severe of the vulnerabilities could allow remote code execution if a user visits a malicious website.
MS16-006 - Security Update for Silverlight to Address Remote Code Execution (3126036) - Critical -
Remote Code Execution
This security update resolves a vulnerability in Microsoft Silverlight. The vulnerability could allow remote code execution if a user visits a compromised website that contains a specially crafted Silverlight application.
An attacker would have no way to force users to visit a compromised website. Instead, an attacker would have to convince users to visit the website, typically by getting them to click a link in an email or instant message that takes users to the attacker's website.
MS16-007 - Security Update for Microsoft Windows to Address Remote Code Execution (3124901) - Important - Remote Code Execution
This security update resolves vulnerabilities in Microsoft Windows. The most severe of the vulnerabilities could allow remote code execution if an attacker is able to log on to a target system and run a specially crafted application.
MS16-008 - Security Update for Windows Kernel to Address Elevation of Privilege (3124605) - Important - Elevation of Privilege
This security update resolves vulnerabilities in Microsoft Windows. The vulnerabilities could allow elevation of privilege if an attacker logs on to an affected system and runs a specially crafted application.
MS16-010 - Security Update in Microsoft Exchange Server to Address Spoofing (3124557) - Important - Spoofing
This security update resolves vulnerabilities in Microsoft Exchange Server. The most severe of the vulnerabilities could allow spoofing if Outlook Web Access (OWA) fails to properly handle web requests, and sanitize user input and email content.
Security Advisories and updates
- Microsoft Security Advisory 3123479 - Deprecation of SHA-1 Hashing Algorithm for Microsoft Root Certificate Program
- Microsoft Security Advisory 3118753 - Updates for ActiveX Kill Bits 3118753
- Microsoft Security Advisory 3109853 - Update to Improve TLS Session Resumption Interoperability
- Microsoft Security Advisory 2755801 - Update for Vulnerabilities in Adobe Flash Player in Internet Explorer and Microsoft Edge
Non-security related updates
- Update for Windows 7 (KB2952664) - Compatibility update for upgrading Windows 7. This update helps Microsoft make improvements to the current operating system in order to ease the upgrade experience to the latest version of Window.
- Update for Windows 8.1 and Windows 8 (KB2976978) - Compatibility update for Windows 8.1 and Windows 8. This update performs diagnostics on the Windows systems that participate in the Windows Customer Experience Improvement Program.
- Update for Windows 7 (KB2977759) - Compatibility update for Windows 7 RTM. This update performs diagnostics on the Windows systems that participate in the Windows Customer Experience Improvement Program.
- Update for Internet Explorer Flash Player for Windows 8.1, Windows RT 8.1, Windows Server 2012 R2, Windows 8, Windows RT, and Windows Server 2012 (KB3133431) - This update resolves a problem in which Adobe Flash Player does not load correctly in applications that are running in Internet Explorer or Microsoft Edge and that have Flash Player embedded.
- Windows Malicious Software Removal Tool - January 2016 (KB890830)/Windows Malicious Software Removal Tool - January 2016 (KB890830) - Internet Explorer Version
- Update for Internet Explorer Flash Player for Windows 10 (KB3133431) - This update resolves a problem in which Adobe Flash Player does not load correctly in applications that are running in Internet Explorer or Microsoft Edge and that have Flash Player embedded
- Cumulative Update for Windows 10 (KB3124200) - This update offers improved functionality for Windows 10 Version 1511.
- Dynamic Update for Windows 10 (KB3124260) - Compatibility update for upgrading to Windows 10 Version 1511: December 17, 2015
- Update for Windows 8.1 and Windows 7 (KB3035583) - Update installs Get Windows 10 app in Windows 8.1 and Windows 7 SP1
- Update for Windows 10 (KB3122962) - OOBE update for Windows 10: December 15, 2015
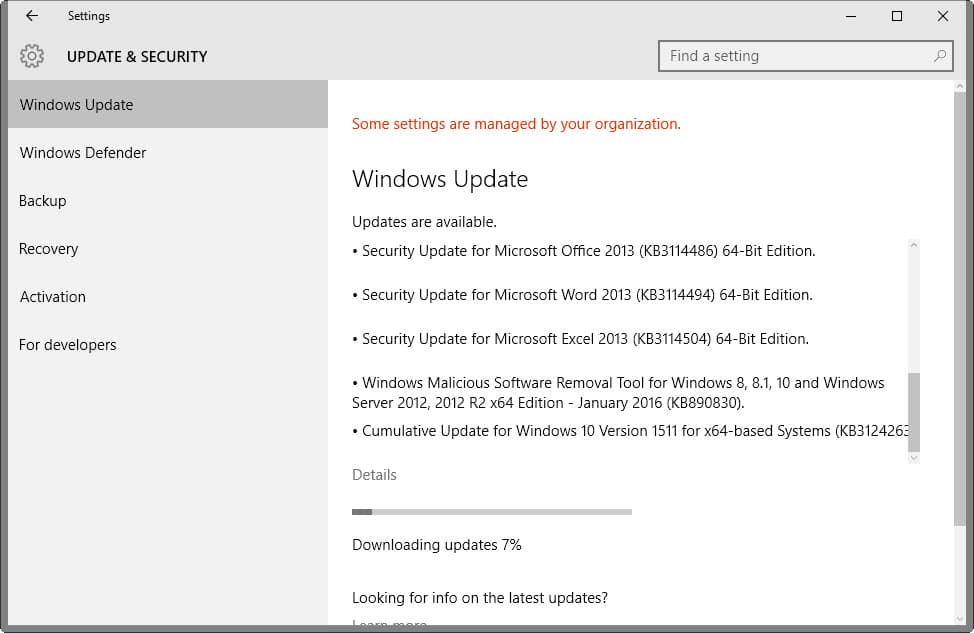
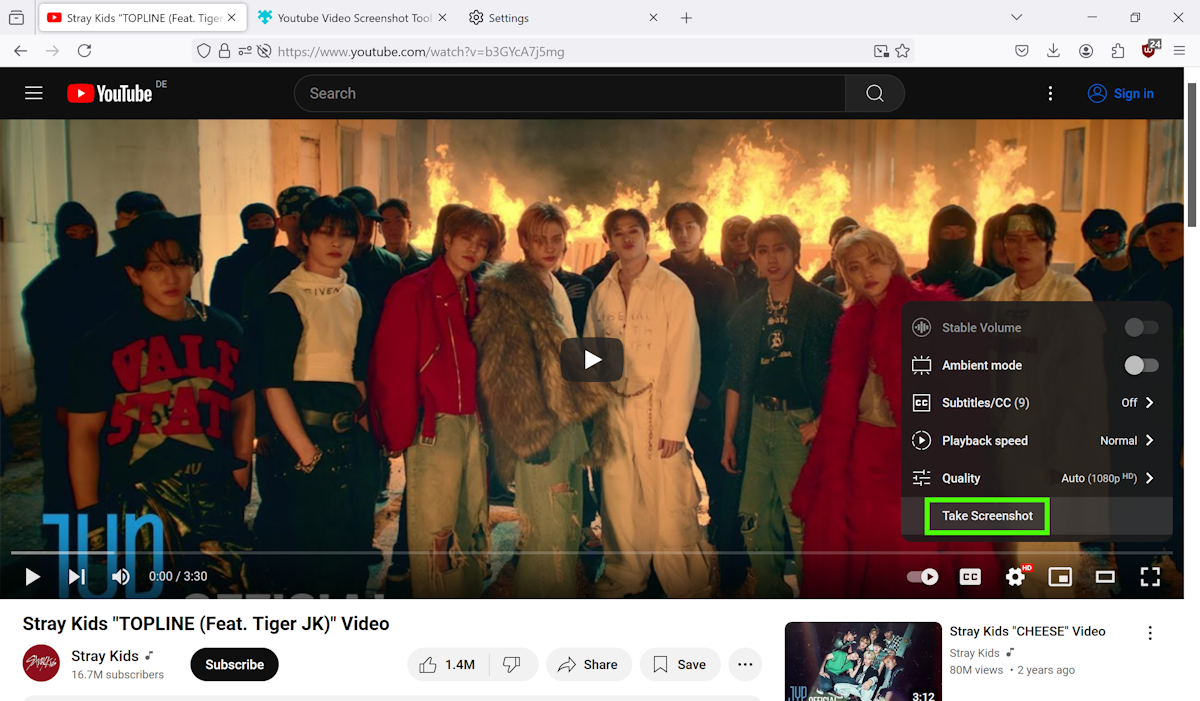
How to download and install the January 2016 security updates
All security updates for Windows are made available via the operating system's update service Windows Update provided that they have been released for the version of Windows installed on a device.
Since Windows Update does not check in realtime for updates, you may want to run a manual check for updates as soon as Microsoft releases patches on Patch Tuesday.
It is advised to create backups of the system before installing any of the patches, and to research each and every one of them before installing them as they may introduce features or changes that you may not want on the PC.
- Tap on the Windows-key, type Windows Update and hit enter. This should open the Windows Update window.
- Click on the "check for updates" link displayed there to run a manual check for updates.
Alternatively, you may download all patches released for all versions of Windows by downloading security ISO images that Microsoft makes available, directly from Microsoft's Download Center where they are made available individually, or by using third-party tools.
Additional information
- Microsoft Security Bulletin Summary for January 2016
- List of software updates for Microsoft products
- List of security advisories of 2016
- Our in-depth update guide for Windows














This is their way of forcing Windows 10 on everyone. I’m not upgrading to Windows 10. I’m keeping Windows 7. My computer is not compatible for Windows 10 and I do have an antivirus so I’m not losing sleep over the discontinuation of Microsoft updates for Windows 7 and 8. And with all the issues in Windows 10 I wouldn’t upgrade if my computer WAS compatible. It’s not worth it. I think it will be a blessing in disguise. No more hangs, crashes and other system destruction.
Jan 28th Updates installed automatically ( Windows 7 ) and when I turned my computer on the next day went through the boot process it just stopped dead. Restored computer to earlier checkpoint and booted ok. Left overnight ( before shutting down installed important updates ). Tuned computer on in morning a same thing again. Restored again and works fine. I’ve had to disable updates.
Thanks, Janny – I’ll give it a whirl.
There’s something very odd about these updates, or maybe the Cumulative IE one in particular – I just went to do the Windows Update process on a non-networked standalone Win7Pro x64 laptop, and opted to just install the Cumu IE update (following the previous issue with network updates).
After reboot, I then went to run Win Update again in order to install the remaining updates, but WU just hung at the 0% downloading updates stage – so I decided to reboot again.
Noticed the Yellow Exclamation Mark icon on the Start button, looked in WU and no updates selected (except for the darn Windows 10 optional one – which I unchecked) but when I clicked on Shutdown it said “installing 1 of 2 updates”.
This is weird behaviour IMHO- I could just about imagine maybe the Cumu IE update having to run again or do a second stage, but that does not explain a second update being there, not to mention the fact that all updates in WU were UNchecked.
With Windows 10 updates being mandatory, I can see Microsoft getting into deep do-do if they don’t improve their QA of updates – preferably back to the level of quality they were at a couple of years back
There must be something specific to particular computers, though – as only a few are affected. Otherwise, there’d be more incidents. I manage well over a hundred workstations over several independent networks, and only have one with an issue.
Anyhow, I got the updates to install, but only one at a time, except 3110329. It stalls at 12% and then rolls back. I had to hide/decline it.
Windows Malicious Software Removal Tool – January 2016 (KB890830) it has installed 6 times on my laptop, im using smelly vista home addition…. weird how it doesnt reconise that ive already got it 6 times, now it prompting me to install it again… really ??
Major issues here, using WSUS on SBS2010 to install following patches on regularly updated Windows 7 Professional network.
In short, when PCs rebooted, got messages about ‘failures’ and these did not install – never had so many failures in one session:
KB3124000
KB3108664
KB3109560
KB3110329
KB3121918
KB3121212
KB3124001
KB3124275
KB3123479
Any ideas?
Thanks
Hi Janny,
I have one Win7 pro x64 behind SBS2011 WSUS that fails on installation of these as well. I viewed it as a workstation issue until now – but after looking at your post I’m wondering if it’s an SBS or SBS/WSUS issue. Other workstations installed the updates successfully though.
I wasn’t able to resolve it by resetting all the update components on the workstation. I don’t have access to the affected workstation at the moment, but as I recall the error was referencing a connectivity issue.(800705b4 – but I may misremember). I found it odd, as there does’t seem to be a connectivity issue with WSUS, and even manual downloads and installs failed with the same error. I was going to look at a possible malware infection next.
Did you find a resolution?
Hi – yes, after hours of experimenting!
Go into Windows Update on the affected computers and uncheck all the 9 updates, then reselect the Cumulative IE update.
Get Windows Update to install, then reboot.
Now apply the other 8 updates same way.
If that also works for you, let us know.
I recieved different numbers for my windows 7.
KB3108664, KB3109560, KB3110329, KB3121461, KB3121918 all seem to be about the same and when looked up they point to the MS 16-007 security bulletin.
KB3121212 points to MS 16-008.
KB3123479 is for Microsoft Security Advisory
KB3124000, KB3124001 point to the same thing, MS 16-005
My question is should i click on all those updates that point to the same thing or just choose one of them?
Torro I have the same updates. I haven’t checked them out much yet but I’m thinking since the updates that point to the same thing are all different sizes they probably each do something different. I’m still going to do just one at a time every few days or so.
I’m starting to hate update day. It’s like a battle now.
Torro and Noswal, I have those updates, too. I installed all of them and lost 3GB on my SSD. I uninstalled the updates, but didn’t regain my space. Luckily, I made a system image the day before and restored that. From now on, I’ll only install the critical updates.
I took the tick out of KB2976978. But loaded the other updates. did I do right ?
With today’s batch, among the other-than-security updates for Win 8.1 x64 I also got an unspecified one that Martin didn’t mention in his post: KB2976978.
Looking it up, I saw this one is a “compatibility update” that “performs diagnostics” (only if you participate in the privacy-invading Customer Experience Improvement Program, it claims). But if you read the description carefully, you’ll see that this one is designed to phone home in order to tell Microsoft exactly how well your system is prepared for an upgrade to Windows 10. Quote:
“These diagnostics help determine whether compatibility issues may be encountered when the latest Windows operating system is installed. This update will help Microsoft and its partners ensure compatibility for customers who want to install the latest Windows operating system.”
I myself never wanted to have anything to do with the Customer Experience Improvement Program that would send Microsoft my user data. Also, for several reasons (such as, I cannot afford to lose Windows Media Center, and I distrust Windows 10’s “telemetry” that cannot be switched off completely) I just do not want Windows 10, nor any updates related to upgrading my system to Windows 10.
Therefore, instead of allowing KB2976978 to install, I unchecked and hid it.
Apparently Martin also got the stubborn KB3035583 again, that tries to install the “Get Windows 10” nuisance app. I had to hide this one two times in a row, but this time I was lucky and did not to get it again.
I have the gut feeling that most non-security updates released for 7 or 8 are only designed to get users to upgrade to Windows 10. There are so many of them, and they tend to come back fairly regularly as well.
I can guarantee it Martin. I had to install a few updates 3x because I kept apply a self-made registry file that blocks Windows 10 GWX from loading up. I would run the reg file before restarting the computer and sometimes it was needed afterwards also. When I stopped doing that, and restarted after the initial restart, it wasn’t making me install a few of those “Updates” again. Ran the reg file and it reblocked GWX. Worst part is, I have it setup (be group policy and reg edit) to now allow OS upgrades. Seems they reset those key values.
Henk, I add this one and others asap. Microsoft did not update its website in time for the article to reflect these updates.
Oh, and I just saw that this KB2976978 that I hid today, in fact was among the updates that I had already hidden before. So this is yet another update that Microsoft keeps pushing even when users already specifically blocked it. It seems there are now at least three such “stubborn” Win10-related updates that may keep returning, even after you expressly did hide them:
KB2952664
KB2976978
KB3035583
Watch out next time!
Kind of worrying that MS16-007 addresses a problem of allowing remote login via RDP to accounts without passwords, normally accounts without passwords are meant to be local only.
Hi Mr Brinkmann,
I just wanted to share info about a brand new MS toy to convince user to go Win10 for Windows 7 Pro. It is served under a critical “recommended” (at least thats what a caption in description pane; of windows update says) patch KB2952664.
BR
I get this KB2952664 systematically proposed since July 2015, systematically hidden by me and systematically proposed again on every Patch Tuesday.
Microsoft is very systematic.
From what I’ve read, MS is not unhiding the ones we’re hiding, but rather changing the file slightly and releasing the same KB as a slightly different version. The effect of course, is the same. They are willfully bypassing our hidden ‘get win 10’ updates.
Best I can tell the ONLY ones they ever do this with are the ones pertaining to Win 10. (5583 and 2664 primarily). How long till these clowns simply force Win 10 on us with no option to reject it? I wouldn’t put it past them.
Thanks for the update.
Grand work as ever. Q. Were the sharepoint patches pulled ? I cant see them and note MS016-009 is absent.
Directly from the Microsoft Bulletin email I get from our Microsoft rep each month…
Note: bulletin identifier MS16-009 was skipped intentionally. This is not a misprint.
Yeah the missing MS16-009 is quite the mystery, probably pulled by MS before release.
That bundled Flash Player plugin that you can’t uninstall (from what I remember, maybe something has changed) – is like turning user’s PC into Adobe-MS hostage