NetStalker checks and notifies you of Internet connections in real-time
Do you know which programs and processes access the Internet on your computer and why? While it is easy enough to tell for programs that won't really work without Internet, web browsers for instance, it is often the case that the sheer number of system processes and programs that connect to the Internet is surprising.
I like to check these on my machines regularly to make sure only those that I'm comfortable with happen. One of the programs that I use for this is the excellent CurrPorts by Nirsoft.
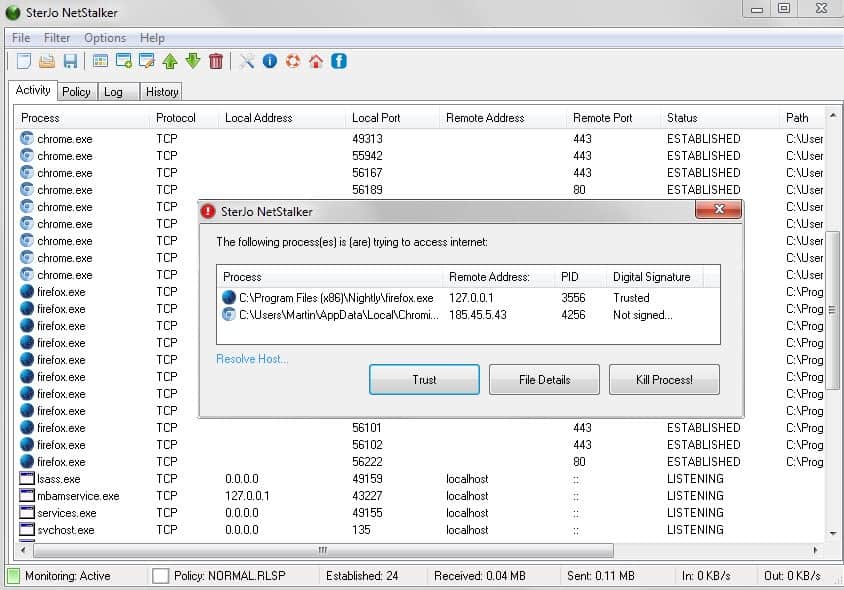
NetStalker feels in many regards like an improved version of CurrPorts. It displays all network activity on start but instead of refreshing the list on demand only, it is refreshing it in real-time to make sure it catches new connections as they happen.
Attention: The installer will install third-party programs without prompt. In particular, it installs Health Alert and Wajam on systems. The portable version is clean and won't do that. We suggest you use the portable version of the program because of this.
Apart from that, it displays prompts whenever it catches a new program connecting to the Internet to give you options on how to handle it.
The main program interface lists process names, protocols, local and remote addresses as well as the process' location on the system.
A right-click on a row displays a context menu with options related to that process and connection. This includes options to kill the process or close the connection, to resolve the host or copy the remote address, and to create a new rule which enables you to allow or block connections permanently.
Rules and policies work independently from other security software that you may use or have installed on your system.
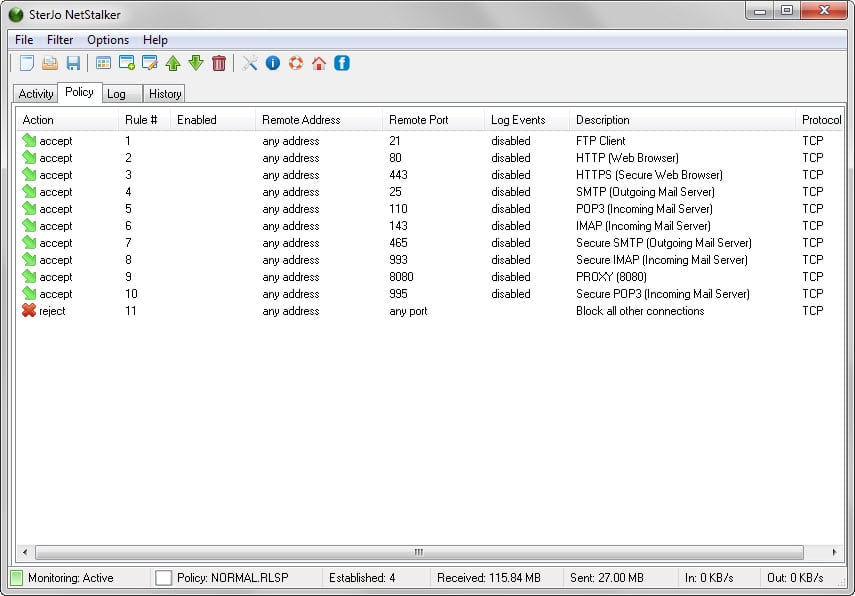
The program ships with two policy files that consist of a number of rules that determine which ports and addresses are allowed and rejected. You will still receive prompts if programs try to access the Internet using any of the select address/port combinations but will notice that everything else is rejected outright.
It is important to make sure all required ports are accepted by the program and that ports that may not be required are not.
This can be done under Policy in the program interface. The program uses a normal policy file by default but ships with a high policy file as well which you can load. The core difference is that fewer ports are accepted by default by the high policy file.
NetStalker ships with options to pause the real-time monitoring of connections or the filtering at any time via the filter menu. There you find the list of filtered processes which lists all programs that tried to access the Internet while the program was running.
Policies can be saved and you may create new ones as well from within the program. This can be useful if you want to import the set of rules on another machine.
Closing Words
What I like the most about NetStalker is that it goes beyond the reporting of processes with network connections. While that is certainly useful, the notification prompts it displays, the real-time monitoring and the option to block or allow certain address/port combinations makes it that more useful.
The main difference to a firewall is the program's simplicity when compared to most firewall solutions for Windows. Plus, it is available as a portable program that you can run from any location on the system.

























Is there some firewall like this for ubuntu or linux mint?
https://www.softperfect.com/products/networx/
Netwworx is also a good and free alternative to count bandwidth, it can also detect UMTS/Modem connection while Windows 7/8.1 can’t. The GUI is a bit confusing but for a free product it’s not bad at all.
A “Google Safe Browsing alert” did pop up when I tried to download the software. Likely due to the included Ad-ware/Crap-ware in the installer version (I tried to download the portable version btw).
Meanwhile the site shows the following message: “We are having some issues while downloading files with Google Chrome. Please use another browser like Mozilla Firefox or Internet Explorer to download this file.”
Its not true that installer tries to install some software without a prompt! There is a decline button on each offer and you are not forced to install anything thats not related with the software. Unlike most free software where you have no other option, here you can choose that.
Really bad call, Martin. This installs a bunch of bad crap along with it: something called “HealthAlert” and some other piece of crud . Not appreciated. Trying to sanitize my system with Revo Uninstaller, Malwarebytes, and then a virus scan. Tried to install a Firefox extension, my entire explorer.exe crashed — seriously, man. Now I’ve got HealthAlert popups even after running Malwarebytes … definitely not going to trust your recommendations again. You’ve lost a reader.
Mike, I’m sorry to hear that. I just tested the portable version and it was clean. I did check the installer on Virustotal and it was clean as well.
A test I ran just now confirms that it installs two programs without prompt that have nothing to do with it.
I have added a warning to the review and reduced the rating of the app because of this.
… I don’t know if you’ve lost a reader, but good GOD am I angry …
I recall that, during installation, the AVG Internet Suite software found 2 instances of PUP or “malware” which contained the name Ad-ware (or something similar); I opted to have it removed before continuing installation, however, the following “Reports” details for the 2 items are described as: \NetStalker _ nirsoft\netstalker_setup.exe.
.
Inspection of malwarebytes Antimalware’s Quarantine page indicates the following which I plan to delete:
Vendor Date Type Location
picture of
a bug …eckOffer …015 1:44 PM File …Local\Temp\nsl25AA.tmp\nsCBHTML5.dll
While I installed this software, it contained several instances of malware which were detected and removed using the AVG antivirus software; Antimalwarebytes software initially also detected bad stuff. Am attempting to determine whether I will be able to confirm the Ghacks claims.
As I said, I scanned the program at Virustotal and it came up as clean. Can you please post the findings?
Netstalker install malware: beware!
Can you be more specific than that? Which antivirus solution detect the malware and what is its name?
Virustotal reports it as clean: https://www.virustotal.com/en/file/350ffec26aa736e97795653be6ecb3bc95dd5e8ade5dca1347d0900f1561a873/analysis/
Cool. Anyway I am curious if it shows connections of rootkited software.
The program want’s to make connections let alone the PUPS
Will not install.
Hmmm based on these articles
I have many choices
https://www.ghacks.net/2014/08/25/glasswire-helps-you-monitor-your-computers-internet-activity/
https://www.ghacks.net/2012/04/19/process-network-activity-monitor-procnetmonitor/
https://www.ghacks.net/2013/01/14/find-out-if-programs-are-connecting-to-the-internet/
https://www.ghacks.net/2010/10/02/display-programs-that-open-connections-with-moo0-connectionwatcher/
https://www.ghacks.net/2014/07/23/analyze-programs-internet-connections-minute/
https://www.ghacks.net/2014/12/31/portexpert-monitors-tcp-and-udp-communications-on-windows/
https://www.ghacks.net/2009/08/19/realtime-network-connection-monitor/
Today this article showed up top-of-page, as though it’s a new article.
something buggy going on with dates applied to updated articles, eh
“By Martin Brinkmann on July 11, 2015 in Software – Last Update: July 4, 2015”
I was on vacation until today and have written articles in advance to release them on schedule. That’s the reason why the last update date differs from the publication date (last update date is the date I wrote the article).
Haha that’s what I been doing Martin, but that time has come to an end. The rule I have, at least one article a month on the count that I’m not a serious blogger. Ho, really nice to hear that you were/are enjoying yourself, same hear.
Yes, I have also been noticing something funny with the dates of articles, and the order in which articles are appearing, for the last week or so.
Word press allows you to release articles on schedule, so he can write and save it for a rainy day :)
Nothing wrong with him writing stuff in advanced as long as it is new.
Well, didn’t Martin say he’d be going on vacation? I’m guessing that is the reason. He is cleverly giving us articles even though he is gone. Hope he’s having a wonderful time. :)
Norton says Netstalker is unsafe..
lol Norton is the new McAfee, I seen Norton’s database on VirusTotal throwing up false positives the last couple of months.
We are having some issues while downloading files with Google Chrome. Please use another browser like Mozilla Firefox or Internet Explorer to download this file.
Thank you for your understanding.
Watch out for – and Decline – the 2x optional installs that are part of the current installer.
It is available in portable form as mentioned if you dislike the bundled crap.
Was also wondering if we can just use something like Peazip to extract all the files contained in the non-portable downloaded file and then just selectively run the installation on only the wanted program. I have done that before with bundled installers.
One can also just download the portable version. It is clean and won’t install anything shady.
Hello Martin, I use Glasswire software to block certain software from accessing internet,but it is heavy for my system, can I use this program instead.If Yes then how can I block a software.
Do I have to block software whenever I start netstalker.Please help
if you decide an download this to try out watch carefully as you click you get multiple accepts as it try’s to give you crap-ware also
Cool find Martin!
The fact that nowadays pretty much every program connects to its developers website means that (for me) a proper firewall is a must have. This program however seems like a good, free alternative.
The amount of data collection many modern programs do is simply outrageous…
too many “additional” programs try to install along with it. bad bad bad…