Google now lets you create Passkeys for your accounts, here's how to set it up

Google has announced support for Passkeys for user accounts. You can now log in to your Gmail account, or any other Google service, without typing your password.
The Mountain View company had worked with Apple, Microsoft and FIDO Alliance to co-create a platform for Passkeys. Apple already supports the feature on macOS 13 Ventura and iOS 16.
What is a passkey, and is it safe?
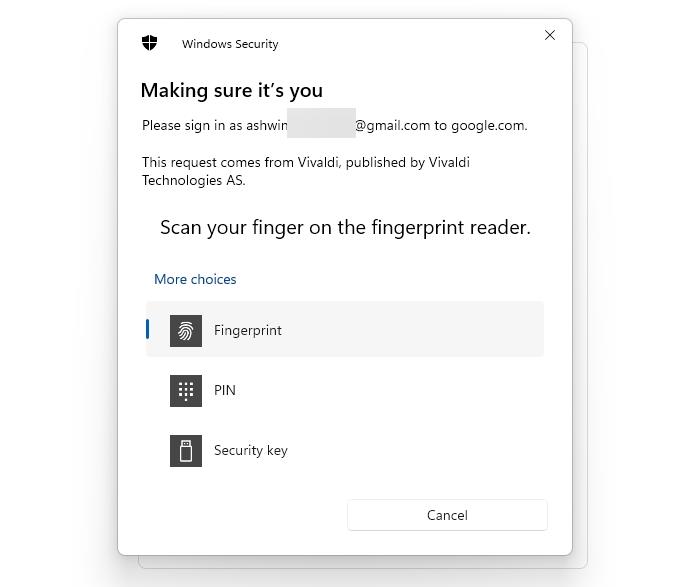
A passkey allows you to sign in to your online accounts without using your password. Instead, it uses your device's screen lock, i.e. PIN or device password, or your biometric data such as a fingerprint scanner used by Windows Hello or macOS TouchID, to authenticate the ownership of the account. The same applies to your Android mobile or iPhone's screen lock methods.
The passkey is created and stored locally on your device, i.e. a mobile phone or a computer. The data is encrypted to prevent unauthorized access. When you try to log in to your account, the server asks the device to verify the credentials associated with that account. The device in turn prompts you to enter your screen lock code to approve the request, and once you enter the code or use your biometric sensor, the device checks it with the data stored locally, and gives the green signal to the server to grant access to the account.
Passkeys provide a quick and easy way to log in to your account, you just have to enter your username, you don't have to key in your password. The fact that it completely negates passwords is what makes it special. Passkeys will bypass authenticator apps or other 2FA methods that you may have enabled on your account. Does that mean that your Google account is no longer protected by 2-step verification? No, your account is still protected by 2FA, you may continue using your username and password along with your authenticator app to log in to your account, the Passkey is just an extra option that you can enable.
You could say that a passkey acts as a combination of your password and two-factor authentication, rolled into one feature. And since the passkey never leaves your device, it is a secure way to log in to your account. Google says that passkeys are more resistant to phishing attacks, and are more secure than one-time codes that are sent over SMS text messages.
How to set up a Passkey for your Google account
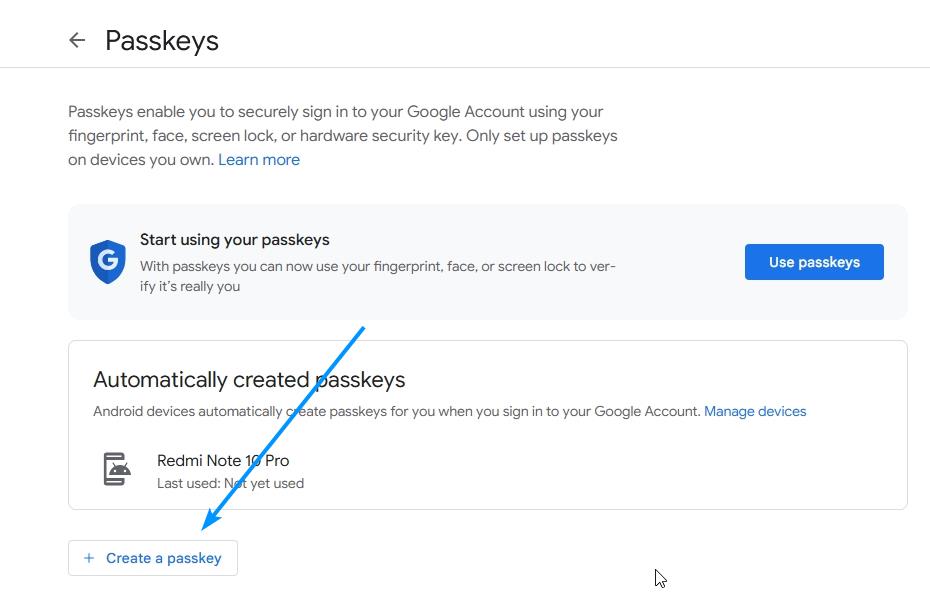
1. Visit Google's Passkey creation page.
2. The website will prompt you to enter the password for your Google account.
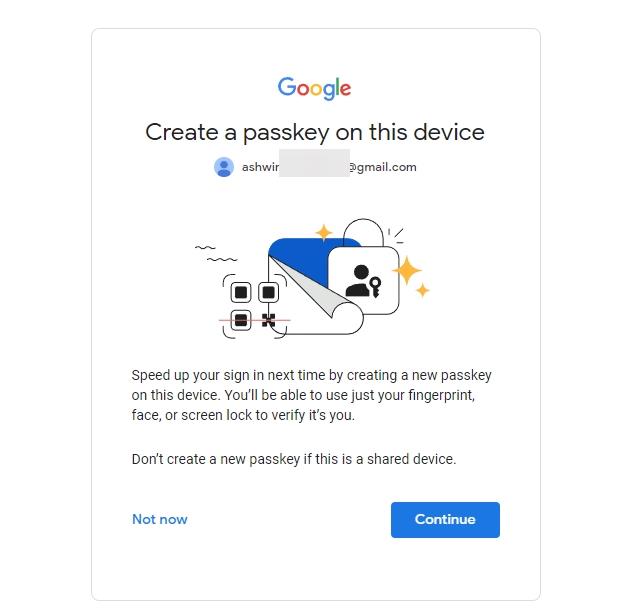
3. Click on the Create a Passkey button.
4. Google will ask you to choose the device that you want to use for creating the Passkey. You can use your computer or mobile phone to create a passkey with your fingerprint, face, or screen lock.
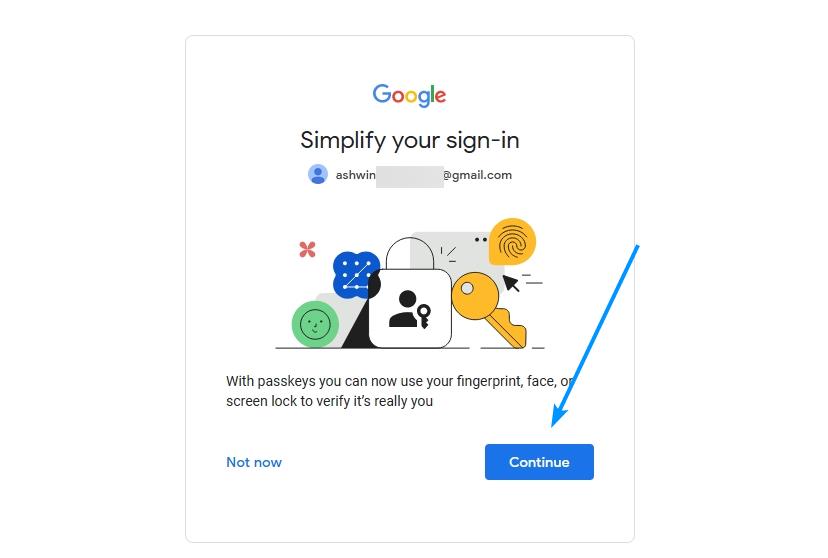
5. Hit the continue button to proceed. Google will ask you to confirm the process by entering your device's screen lock code, or biometric data. That's it, you've set up a passkey.
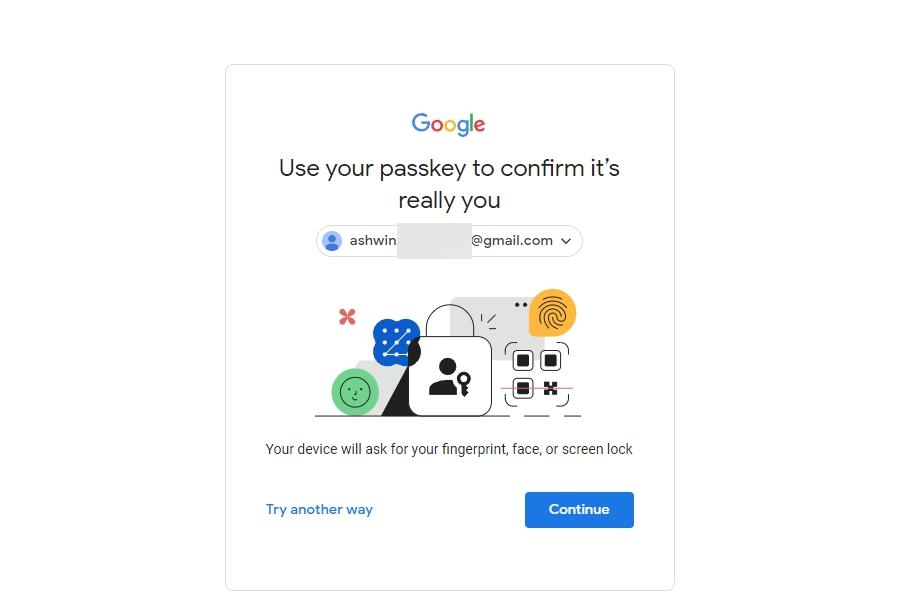
Try it now. Log out of the account in your browser and sign in again with your passkey. No password required, that's pretty cool.
Though the steps to set up a passkey are identical across all platforms, there are some differences in the way the feature works on computers and phones. The important thing to note here is that your passkey is not synchronized across your devices. Google doesn't support passkey sync, unlike Apple does with iCloud Keychain.
But when you sign in to your Google account on a secondary device, i.e. one that does not have a passkey stored on it, the web page will offer to create a passkey on that device. You may choose to add it by confirming the device's screen lock code. Adding a secondary device is optional, Google advises users not to create passkeys on shared devices.
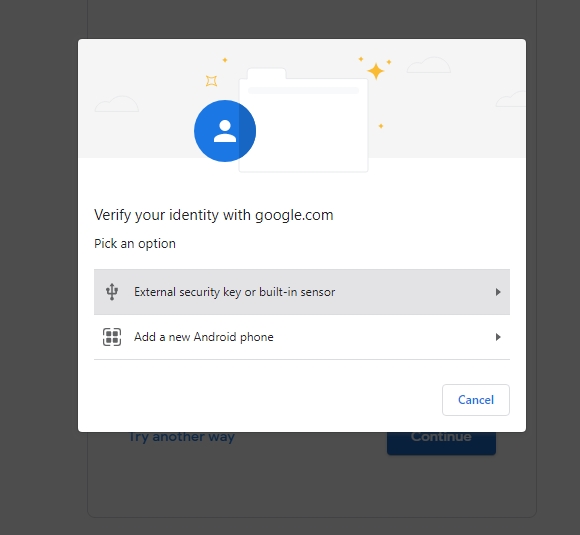
Wait, how do you log in on a desktop browser if you created a passkey on a phone? Google's login page will display an option that lets you "add a new phone". Select it and the site will display a QR code on the screen. Use your mobile's camera app to scan it, and approve the login process.
A few things to note
Google Passkeys are supported on devices that run on Windows 10, macOS Ventura, ChromeOS 109, iOS 16, Android 9 or above. It is also compatible with hardware security key that supports the FIDO2 protocol. A support page on the company's website claims that Passkeys are only supported on the following browsers: Chrome 109 or above, Safari 16 or up, Edge 109 or later. In truth, it works perfectly fine on all modern browsers, I actually created the Passkey using Firefox. I was also able to use it on Vivaldi, so it should work fine with other Chromium-based browsers.
The Passkey login page that I mentioned above displays options to sign in with an external security key (like Yubikey) or a fingerprint sensor, or to add a new Android phone. The third option can be a little confusing, as you're not adding a new device. Don't worry, it works with iPhones too, just point your camera app at the QR code on the screen and an option to "sign in with passkey" will appear on the screen. Tap on it, and it will authenticate the process using Face ID.
What if you lose your device? A thief wouldn't be able to access the passkey without the device's screen lock code/biometric authentication. You can remove the passkey from the device remotely via your Google account on another device. Please refer to the official support page for more details.
To opt out of signing with passkeys, go to your Google Account's Security page, and disable "Skip password when possible".
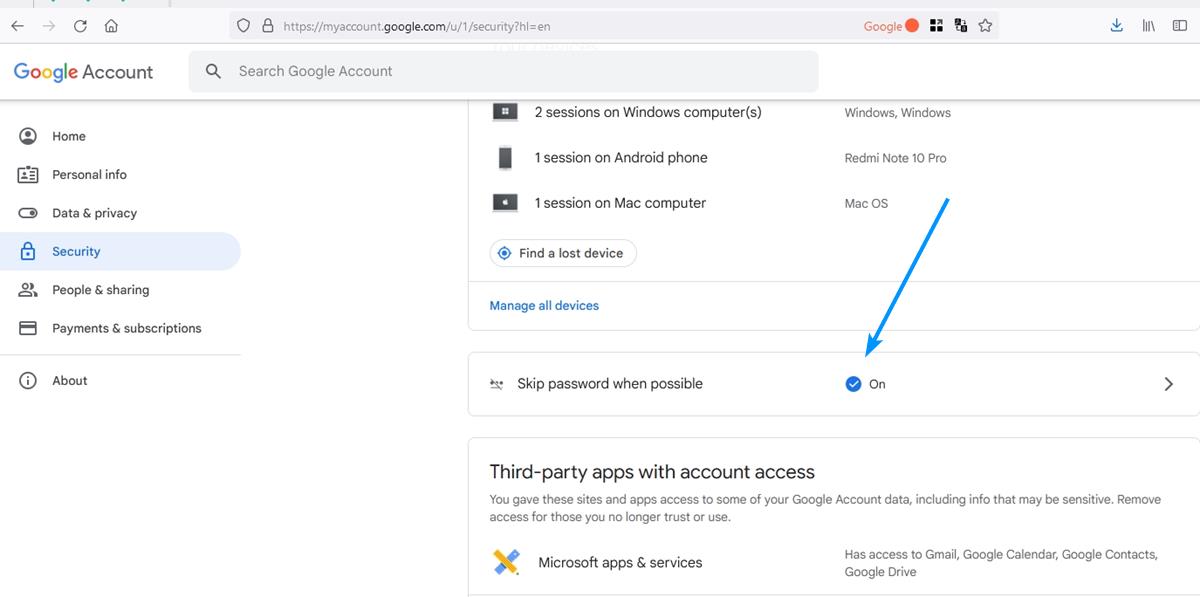
Note: Google says that Android devices will automatically create passkeys when you sign in to your Google Account. You have to opt out of it, by removing the device from your account from the Manage Devices page.
A few websites, such as PayPal have already added support for passkeys, and so have some password managers, it is only a matter of time before more of them adopt the protocol. I guess the passwordless future is here.
Have you tried Passkeys?





















Using a 2nd device to log into the 1st device, instead of just typing a password on the 1st device, which I’m obviously already using, is simpler?
Seems to me it’s just another attempt to get my phone number.
“Passkeys provide a quick and easy way to log in to your account, you just have to enter your username, you don’t have to key in your password.”
But . . .
“When you try to log in to your account, the server asks the device to verify the credentials associated with that account.”
Someone please explain what I am missing here; I don’t have to enter my password, but I do have to enter my passkey.
What makes it THAT much easier than entering a password?
And if I forget my passkey?
Your device holds the passkey and shares it with the server when you authenticate with your device using biometrics or a PIN.
I wish all of these large corporations would f off with all of this nonsense. This requires additional hardware that is expensive. Yubikey is overpriced garbage. I only want to log in with my username and password. There’s nothing on Google that I’m concerned about being stolen or hacked.
You are free to keep doing that. The article makes it clear that this is an extra option, not something that replaces passwords.
Err, many folks use gmail as their primary client and a compromised email is a bad thing. Also, the ‘Sign in with Google’ thing on multiple sites and it becomes a hot mess.
About time. Hooked up mine..it works flawlessly
I never type passwords. I simply copy/paste them from my password manager. So why invest in additional expensive hardware which may only save you a millisecond or two to login somewhere.
No thanks, this is simply another trick to push you to upgrade your software, operating system, and hardware every year.
Firefox and Linux are not supported. Versions of Windows before 10, Edge, and Chrome prior than 109 are not supported. Android versions 8 and earlier are not supported. So, Linux users are out of luck?
Will they send us free YubiKeys when passwords are no longer available? I’m not going to pay $50 per household member for a piece of overpriced plastic from Yubico. Not only that, but these hardware keys now require “FIDO2”, after which they will require “FIDO3, FIDO4, etc. in the future… Spending an additional $50 per user every year on plastic that will probably die out in a year because you are constantly shoving this thing in and out of your USB port daily. I’ll stick with my bad password over this BS. I believe it would be simpler to close my Google account and use alternatives.
@Fingerprinting
Okay miss out on mathematically proven security and comfort. And there are more vendors for FIDO2 than yubico. It also cannot used for fignerprinting as each site and account have their own ECC key.
Usually the biggest opposers to progress are people who don’t understand the protocols and/or hardware.
@Frankel
The stupidest are those who think that they are clever. The hopeless slaves are those who are happy to be slaves and who would do anything to preserve their slavery.
This works both ways, but thank you. I’m on the side with algorithms and methods proven secure by actual mathematicians, not someone on the internet.
/Q.E.D.
I like how he jumped straight to calling someone a slave on a tech discussion site. Adding support for a new mechanism doesn’t mean the old is going away. Those that have a hardware key (available from multiple vendors) can use the additional service. Also, Google has supported hardware keys since before, so it is nothing new on that front. It is just adding support for Passkeys. Hate on the newly added Passkey support if you have to, why hate on something that has already been supported for quite some time.
> “methods proven secure by actual mathematicians”
We all know that Mathematicians never make mistakes.
Nugae. *cough* SHA1 *cough* *cough*
> “…a piece of overpriced plastic from…”
…
> “…these hardware keys now require “FIDO2”, after which they will require “FIDO3, FIDO4”
Agreed.