VeraCrypt 1.24 encryption software update released
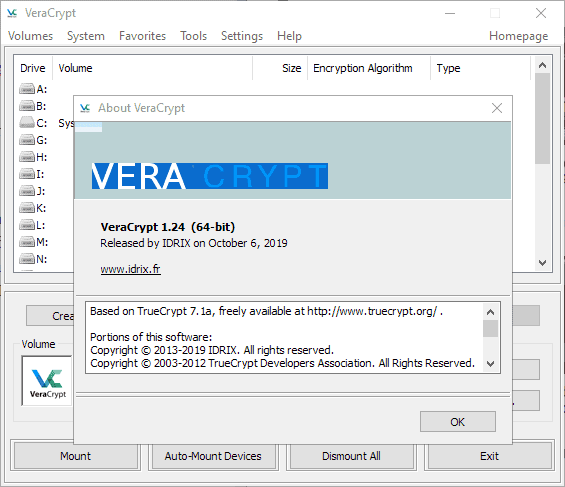
The developers of the open source cross-platform encryption software VeryCrypt released version 1.24 of the software on October 6, 2019 to the public.
We reviewed a beta version of VeraCrypt 1.24 in March 2019 and highlighted the major features that were integrated in the beta version already. The final version unlocks the update for production environments.
VeraCrypt does not support automatic updating which means that administrators need to download the latest client version and upgrade manually. Windows users can download a portable version or installer to their system. The installer will upgrade the current version automatically, the portable version needs to be placed in the same directory to upgrade. Linux users can check out Mike's guide on installing VeraCrypt on Linux.
Tip: check out this guide on using a PIM in VeraCrypt to improve security.
VeraCrypt 1.24
Most changes of VeraCrypt 1.24 apply to the Windows version of the client but there are some that apply to all (Windows, Linux, Mac) and some that apply to Mac OS X or Linux exclusively.
As far as changes for all clients are concerned, VeraCrypt 1.24 increased the maximum password length for non-system volumes to 128 bytes in UTF-8 encoding, improved the performance of XTS mode on 64-bit machines using SSE2 (about 10% faster according to the developers), and fixed the detection of certain CPU features.
Windows users benefit from a huge number of changes including several security improvements. The new version of the encryption software supports RAM encryption on 64-bit machines. The feature is disabled by default and needs to be enabled in Settings > Preferences > More Settings > Performance and Driver options > Activate encryption of keys and passwords stored in RAM.
Doing so adds a 10% overhead on modern CPUs according to the developers and disables hibernation of system encryption is used.
Several security improvements are active by default. VeraCrypt is configured to erase system encryption keys from memory when the machine shuts down or is rebooted; this helps mitigate certain cold boot attacks according to the developers. Mitigations protect the application's memory against memory attacks by non-admin users.
Another new security feature is the option to erase all memory-stored encryption keys if a new device is connected to the system. The option is not enabled by default and needs to be enabled under Settings > Preferences > More Settings > System Encryption Settings > Clear encryption keys from memory if a new device is inserted.
Both bootloaders, MBR and UEFI, have been improved in the new encryption software version. The MBR bootloader determines the boot loader memory segment dynamically in the new version, and it features a workaround for an issue that affected the creation of hidden operating systems on some Solid State Drives.
The UEFI bootloader features a new timeout option for password input (three minutes by default and default action set to shutdown) and several Rescue Disk improvements including an option to start the original Windows loader from the menu.
Other improvements include a new option to use CPU RDRAND or RDSEED as additional entropy sources for the random generator if available. Users may enable the option in the Preferences under Performance and Driver Options > Use CPU hardware random generator as an additional source of entropy.
Mac OS X and Linux versions feature a new --no-size-check parameter that disables that disables the new verification of available storage size when creating file containers.
Check out the full release notes here and the download section to download the new version.
Closing Words
VeraCrypt 1.24 is the first stable release of the encryption software in 2019. It includes several important fixes and improvements, and administrators should consider upgrading to this version as soon as possible.
As always, it is recommended to make sure that you have created a rescue disk and backed up the volume headers before you install the upgrade on the system.
Now You: which encryption software do you use, if any?





















“as the previous team abandoned it without account.” To be fair it’s free, so it’s reasonable for developers to just quit. Perhaps the downside of free software, although plenty of commercial outfits have just dropped a product.
Any reason one couldn’t run both, say a Veracrypt container inside a TC container( or vice versa)? Personally, I don’t see the need but some might feel better by doing so.
Yeah. I’d been using TrueCrypt for years to run the Haller Portable Thunderbird in a container.
I went with VeraCrypt, sadly to admit, because it was new. And because it had a team who promised to support it. Which they’ve done much to their credit and community gratitude as the previous team abandoned it without account.
In reading the changelog for 1.24 I realize the app has grown way beyond my needs and I’m going to stay with 1.23. Heck, I see no reason to upgrade Thunderbird beyond 52.9.1 either.
This is not to dismiss the efforts in building the new features in 1.24 as they are surely needed or welcomed by more advanced users.
VeraCrypt serves in the protection of about 25 years of professional and personal email against the low life who would break into my home and steal my PCs.
Should authority present a warranty, I’ll hand over my PIM and 16 character password. I have nothing to hide as I’ll insist upon from my holding cell…
Thanks for another great article, Martin. It helped considerably in my decision.
And a bit belated, Good Luck in your association with Softonic!
> RAM encryption
And how would that work? I mean the keys to decrypt the RAM have to be inside the RAM…
I didn’t upgrade from Truecrypt because I figure any attempt to crack will be aimed at Veracrypt.
Does anyone know why the Truecrypt team quit so suddenly but Vera seems to go on being developed?
George, the true reason was never revealed (if there was any). VeraCrypt picked up the source, it is a completely different team.
Does it protect anymore as we have learned recently there are some serious quantum computers already out there, just wondering.
In all honesty, I am still using last ever 7.1a of Truecrypt, and don’t plan to change. My reasoning is that there are no state secrets, and by far, surely….99% of anyone trying to break into one of my Truecrypt containers would be likely most UNsuccessful.
So, having the latest-greatest Veracrypt never took my fancy.
Thanks for details though!
Ditto, like you I’m still using good old Truecrypt (in my case for some infrequently used encrypted file containers, not for system-level encryption). And just like you, I see no real-world safety dangers that would necessitate installing Veracrypt.
In fact, a couple of years ago I read a rumor that explained the strange sudden stop of Truecrypt development and its succession by Veracrypt by suggesting that the Truecrypt developers had refused to yield to government pressure to hide a secret decryption backdoor in their software, while the subsequent Veracrypt version did include such a backdoor.
Of course rumors of this kind are usually not true. This one looked just like an unsubstantiated conspiracy theory to me. Still, at the time it set me thinking: why would I replace some trusted software that, for my own modest needs, was working perfectly fine?
I still don’t see the need.
The only reason I can see for switching to Veracrypt is if you envision a scenario where you’ll need the hidden volume function to work against a highly knowledgable attacker, because there’s an unpatched vulnerability that makes it possible to detect, with a very high degree of certainty, the presence of a hidden volume in Truecrypt.
Of course, if your secrets are really that valuable, encryption software would be the least of your worries.
Same here, exactly.
VeraCrypt does support TrueCrypt which means that migration is easy enough. Note that TrueCrypt does have known vulnerabilities that are fixed in VeraCrypt. I guess there is little danger for most when it comes to continuing to use TC though.
You mean that the government “tells” us there are vulnerabilities. I’d always recommend using 7.1a Truecrypt, the switch to Veracrypt was far too shady for my liking.