Installing VeraCrypt in GNU/Linux
For those of you unfamiliar with it, Veracrypt is a successor to the encryption software Truecrypt. Truecrypt was suddenly abandonded by the creators, and others decided to take up the responsibility by forking the application and creating Veracrypt.
Veracrypt leaves many things untouched from the last working Truecrypt version, however they have added some new features that really bolster the level of security one can make use of. More information about Veracrypt can be found on their website at https://veracrypt.codeplex.com/
The Installation
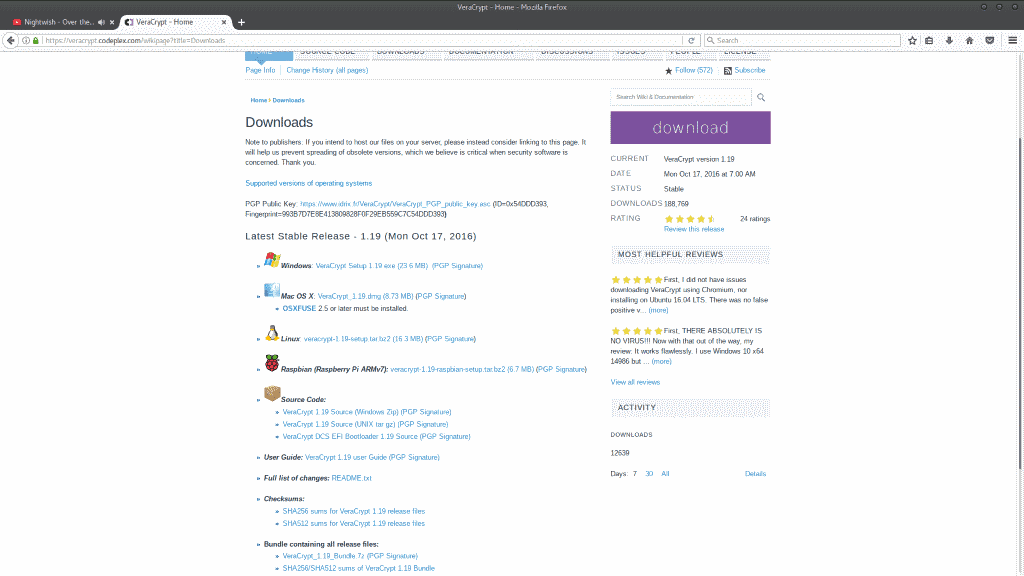
Installing Veracrypt is extremely simple, and only requires roughly five minutes of your time. Navigate your browser to the downloads page here and select “VeraCrypt Linux Setup 1.19†which is the latest version at the time of writing this.
Save the file anywhere you wish, such as your Downloads folder, and then pop open your terminal.
Next, we need to extract the setup files
- cd Downloads
- tar -xf veracrypt-1.19-setup.tar.bz2
- ls
You should see a bunch of setup files, you’ll want to run the GUI setup for your Architecture.
- ./veracrypt-1.19-setup-gui-x64
Then press 1 and hit enter to start the installation, followed by “Q†when the terms and conditions pop up, followed by “Yes†and enter once more. You will then be prompted to enter your root/sudo password, and the installation should only take a brief moment thereafter.
That’s it! But, since that was so easy, why don’t we set ourselves up an encrypted container while we are at it?
Setting up an encrypted file storage container
How I find myself describing to people what a container is, is the computer version of a safe, but a safe that you can design to look like something else. You theoretically could make your safe APPEAR to be an .mp3 file, a .JPG, or a text document if you wanted (granted if you have a container that is 20GB in size, that’s an awefully large jpeg...)
Setting up a container can take as little as five minutes, or absolute hours depending on some of the choices you make throughout this, and the power of the machine you are using. My intel i5-4210U will process cryptographic processes like a ferrari compared to doing the same thing on a Core2Duo, for example.
Pop open your applications menu and find VeraCrypt, usually under “Accessoriesâ€.
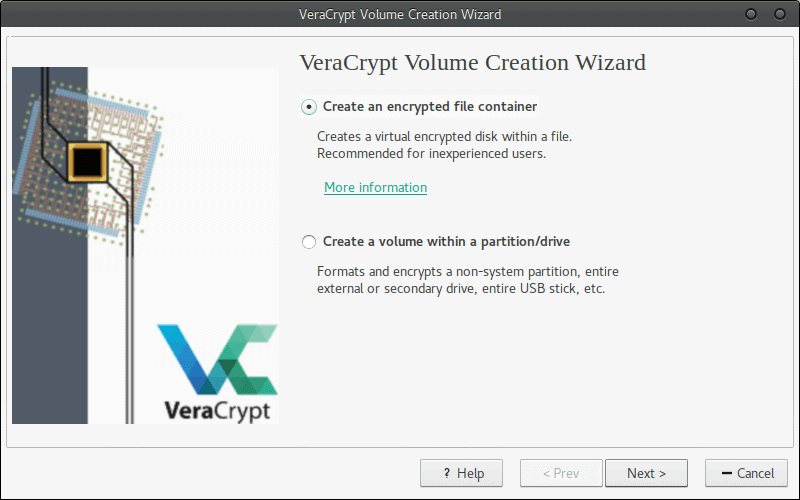
Next, we want to click Volumes > Create New Volume.
From there, select that you wish to create a container, and make it standard not hidden on the next screen as well.
At this point it’s time to create the file you wish to use as a container. I tend to make mine usually just gibberish names, like “dmbe7363†or something personally; but ultimately you could name it, “Top secret files I want to hide from the government†if you wanted to as well.
Once that’s finished, it’s time to select the Algorithm we want to use. I personally am on the viewpoint of, “I’d rather it be as secure as possible.†After all, why am I going through all this trouble, just to make my container something that can be broken into...? So, for my own container I chose a cascade suite of cyphers; AES first, Twofish next and then finishing with Serpent. I’m not going to get into a huge explanation about these, but the general point to get across to you is, “AES is what your SSL and TLS certificates typically use, and is the industry standard military grade encryption.
Twofish is even more powerful and complex, albeit a little slower to decode, and Serpent is the grandaddy of slow but beefy encryption.†This suite means that IF an adversary somehow managed to break the AES encryption or find a way past it, they still have Twofish and Serpent in their way, making it extremely unlikely (as long as the rest of this setup is done properly) that anyone will EVER access this file by force.
For my Hash Algorithm, I use SHA-512 or Whirlpool typically. SHA-512 was designed by the NSA and is widely considered one of the more secure algorithms for password hashes while maintaining great speed. Now, for the paranoid minded, yes, I did say made by the NSA, however; there is no evidence of any backdoor to SHA-512.
The next couple screens are fairly self explanatory, selecting the size of the container you wish to make, and the filesystem used. Simply put, FAT is fine as a filesystem, unless you plan to put files that are larger than 4GB themselves into the container, then you’ll want to select a different format (Although if you selected that option, VeraCrypt will pick one for you!)
When asked about creating a password it is absolutely crucial that your password is secure. Your password should be 20+ characters, with no words or repeated phrases or numbers.
An example of a secure password is: F55h$3m2K5nb2@$kl%392@j3nm6^kAsmxFC^75$
There are various methods for creating and actually remembering passwords like that to be found on the internet. How you create your password is up to you, but remember that the strength of the encryption is absolutely irrelevant if your password is “password123†or something simple!
The next screen is going to ask you to move your mouse as randomly as possible within the window. Simply do so until the green bar is completely filled, and then click “Formatâ€.
Once that’s done, your container will be set up, and will be ready to go...sooner or later.
Once that’s finished, let’s mount the container so we can drop a file into it!
First, select a slot and then click “Select File†on the main VeraCrypt screen, and then click “Mountâ€.
Select the file we created, and enter the password.
Once that is done, your file will be mounted like a drive, in your file manager! Treat it just like a thumb drive, drag and drop or copy and paste anything you want into it! Once you are done with it, make sure you go back into VeraCrypt and dismount the container!
Congratulations! If you followed this guide properly you now have an extremely over-secured and nearly unbreakable as far as we are aware; encrypted container!

















Very informative article and motivating an install. But the Achilles heel is still the password. I counted 39 characters of intentionally non-memorable sequences. So how do you deploy it? Using the article’s analogy of a safe, it’s like having a light but impenetrably strong safe that requires a massive key to open all the locking mechanisms, so you can’t easily prevent it being stolen.
This is the encryption conundrum I have never managed to get past to make the effort seem worthwhile.
Good article! Looking forward to a follow up on FDE.
One quibble: their website is actually https://idrix.fr/VeraCrypt (that is the URL they list on the official twitter account, https://twitter.com/VeraCrypt_IDRIX). Binaries are hosted both on CodePlex and SourceForge. Though the CodePlex page informs that CodePlex is shutting down in December 2017.
VeraCrypt is ok, but you could also just use dm-crypt which is already built into the Linux system. As far as I know VeraCrypt in Linux will not do Full Disk Encryption (that’s a Windows-only feature), whereas dm-crypt can do that. No extra software to install, and if you’re using Ubuntu (or a derivative) you can set it all up during the initial system setup.
Of course there are pros and cons to Full Disk Encryption compared to encrypting just a container. Users should research the differences and decide what suits them better. Personally I find it easiest to just set up FDE in one shot and be done with it.
Whatever method you choose, please remember to BACK UP YOUR HEADERS (MASTER KEY) on a separate physical drive. If you don’t know how to do this (or what this even means), be sure to find out or you’ll be risking 100% unrecoverable data loss if your drive malfunctions.
Jason,
You’re entirely correct that Veracrypt does not do FDE in Linux, and that using dm-crypt/LUKS is the way to go for that.
However, something to keep in mind is that FDE is only useful if your machine is turned off. Once you enter that password, your system is vulernable to an adversary who gets their hand on your machine.
The perk to using containers, is your computer can be running, but the container not mounted, and the files within it are safely stored. It’s good practice to keep containers unmounted when not transferring files into them for this reason. If someone kicked in your door and stole your laptop while it was turned on, but the container wasn’t mounted; you’re safe!
Thanks for your comment, there is actually an article in the works about Full Disk Encryption sometime in the future!
veracrypt is available in both Arch and Manjaro repos, no need to download and install external tarballs if you use these distros.
If you dont mind PPAs
sudo add-apt-repository ppa:unit193/encryption
sudo apt update
sudo apt install veracrypt
Thanks. I honestly didn’t even realize VeraCrypt ran on Linux. Duh.