Linux users, take action against the "Looney Tunables" now

A new and potentially devastating Linux vulnerability has surfaced, aptly named ''Looney Tunables''. This security flaw poses a significant threat to Linux systems, as it allows local attackers to attain coveted root privileges by exploiting a vulnerability within the GNU C Library's ld.so dynamic loader.
At the heart of most Linux-based systems lies the GNU C Library, or glibc, a critical component responsible for providing essential functionality. This includes vital system calls like open, malloc, printf, and exit, integral for the smooth execution of programs. Within glibc, the dynamic loader, ld.so, plays a pivotal role in preparing and executing programs on Linux systems utilizing glibc.
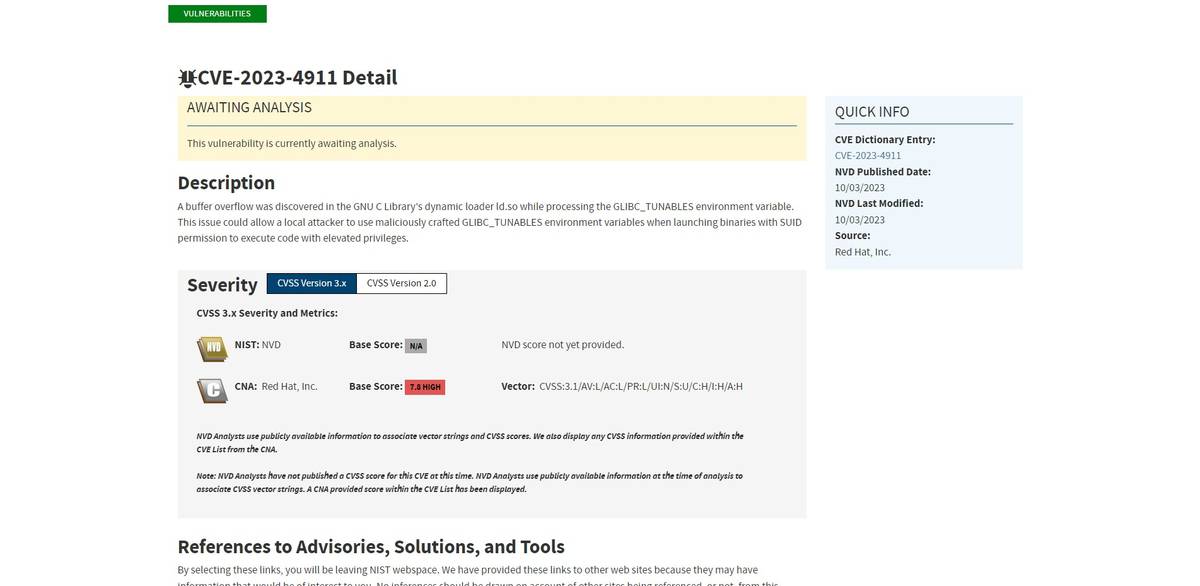
CVE-2023-4911 or the ''Looney Tunables'' affects GNU C Library and poses a serious threat to Linux users.
What is ''Looney Tunables''?
The ''Looney Tunables'' vulnerability, identified as CVE-2023-4911, was brought to light by the diligent work of the Qualys Threat Research Unit. It first appeared in April 2021, introduced with the release of glibc 2.34. This vulnerability originates from a commit aimed at fixing SXID_ERASE behavior in setuid programs.
Saeed Abbasi, Product Manager at Qualys' Threat Research Unit, emphasizes the gravity of this discovery. Successful exploitation of ''Looney Tunables'' grants attackers full root privileges, a scenario that has been demonstrated on major Linux distributions like Fedora, Ubuntu, and Debian.
The ease with which this buffer overflow vulnerability can be weaponized underscores the potential for other research teams to develop and release their exploits, amplifying the risk across Linux distributions.
The ''Looney Tunables'' vulnerability is not an isolated incident too. In recent years, Qualys researchers have uncovered other high-severity Linux security flaws, enabling attackers to gain root privileges within the default configurations of many Linux distributions.
These include vulnerabilities in:
- Polkit's pkexec component (dubbed PwnKit)
- Kernel's filesystem layer (dubbed Sequoia)
- Sudo Unix program (aka Baron Samedit)
Read also: Google confirms CVE-2023-5129 is the hidden threat in Libwebp.
Don't waste any time
System administrators are urged to prioritize patching as a matter of utmost importance. The vulnerability is triggered during the processing of the GLIBC_TUNABLES environment variable on default installations of Debian 12 and 13, Ubuntu 22.04 and 23.04, as well as Fedora 37 and 38. Alpine Linux, which employs musl libc, remains unaffected. Attackers with minimal privileges can exploit this high-severity vulnerability, and it does not necessitate user interaction.
Featured image credit: kjpargeter on Freepik.
Advertisement














I will not.
What??? No messed up comments anymore? Great!