Microsoft Security Updates January 2017
It is the second Tuesday of the month, and that means it is once again Patch Day over at Microsoft.
The company has released security updates and non-security updates for client and server versions of its Windows operating system, as well as for other company products today.
Our guide provides you with information on these updates. It lists all security bulletins that Microsoft released this month, and all non-security updates and security advisories.
It starts with an executive summary that highlights the most important information, and lists who all client and server operating systems, and other Microsoft products, are affected this month.
Last but not least, it provides you with information on how to download the updates, direct links to major updates, and links to resources that provide you with additional information.
Microsoft Security Bulletins January 2017
Executive Summary
- Microsoft released 4 security bulletins in January 2017.
- 2 of the bulletins are rated critical, the highest severity rating.
- Vulnerabilities affect all client and server Windows versions that Microsoft supports with the exception of Windows 8.1 and Windows Server 2012 R2. Therefore, no Security Only Quality Update or Security Monthly Quality Update was released for these operating systems.
- Other Microsoft products for which updates were released include Microsoft Office, Internet Explorer, and Microsoft Edge.
Operating System Distribution
Only Windows 8.1, Windows 8.1 RT, and Windows 10 are affected by a critical vulnerability on the client side. The only server operating system affected by a vulnerability rated critically is Windows Server 2016.
All are affected by MS17-003, a bulletin that patches Adobe Flash Player. That's also the reason why Windows 7, Vista and Windows Server 2008, 2008 R2 and 2012 are not affected by the vulnerability.
It is also interesting to note that Microsoft rates MS17-001 as important, even though Microsoft Edge on Windows 10 is affected by the vulnerability critically.
- Windows Vista: 1 important
- Windows 7: 1 important
- Windows 8.1: 1 critical
- Windows RT 8.1: 1 critical
- Windows 10: 1 critical, 1 important
- Windows Server 2008: 1 important
- Windows Server 2008 R2: 1 important
- Windows Server 2012 and 2012 R2: 1 moderate
- Windows Server 2016: 1 critical, 1 moderate
- Server core: 1 important, 1 moderate
Other Microsoft Products
- Microsoft Office 2016: 1 critical
- Microsoft Office Services and Web Apps: 1 critical
Security Bulletins
Red = critical
MS17-001 -- Security Update for Microsoft Edge (3199709)
This security update resolves a vulnerability in Microsoft Edge. This vulnerability could allow an elevation of privilege if a user views a specially crafted webpage using Microsoft Edge. An attacker who successfully exploited this vulnerability could gain elevated permissions on the namespace directory of a vulnerable system and gain elevated privileges
MS17-002 -- Security Update for Microsoft Office (3214291)
This security update resolves a vulnerability in Microsoft Office. The vulnerability could allow remote code execution if a user opens a specially crafted Microsoft Office file. An attacker who successfully exploited the vulnerability could run arbitrary code in the context of the current user. Customers whose accounts are configured to have fewer user rights on the system could be less impacted than those who operate with administrative user rights.
MS17-003 -- Security Update for Adobe Flash Player (3214628)
This security update resolves vulnerabilities in Adobe Flash Player when installed on all supported editions of Windows 8.1, Windows Server 2012, Windows Server 2012 R2, Windows RT 8.1, Windows 10, and Windows Server 2016.
MS17-004 -- Security Update for Local Security Authority Subsystem Service (3216771)
A denial of service vulnerability exists in the way the Local Security Authority Subsystem Service (LSASS) handles authentication requests. An attacker who successfully exploited the vulnerability could cause a denial of service on the target system's LSASS service, which triggers an automatic reboot of the system. The security update addresses the vulnerability by changing the way that LSASS handles specially crafted authentication requests.
Security advisories and updates
Microsoft Security Advisory 2755801 -- Update for Vulnerabilities in Adobe Flash Player in Internet Explorer and Microsoft Edge
Non-security related updates
KB3213986 -- Cumulative update for Windows 10, OS Build 14393.693
- Improved the reliability of Groove Music playback in the background, App-V, video playback and Remote Desktop.
- Addressed issue where after successful fingerprint authentication on a device with the screen off, the screen does not turn back on.
- Addressed issue where only one input device works when you connect two similar input devices to the same machine.
- Addressed issue in the App-V Connection Group that allows users to have access to pieces of functionality that they were not designated to for access.
- Addressed issue that prevents users from selecting multiple certificates simultaneously through the UI.
- Addressed issue where the Request Control function does not work with Remote Assistance if the user being assisted is on Windows Server 2008 R2 or Windows Server 2012.
- Addressed issue that prevents a smart card module from pairing with a contactless smart card reader.
- Addressed issue with license conversion of Server Core from evaluation version to a retail version.
- Addressed issue that prevents users from opening Internet shortcut (.URL) files with Internet Explorer when Enhanced Protected Mode is enabled.
- Addressed issue that prevents users from logging on if a device has been away from the corporate network over a period of time.
- Addressed additional issues with Microsoft Edge, clustering, Internet Explorer, Windows Update, input devices, facial recognition, Logon, Hyper-V, PCI bus drivers and Windows Kernel.
KB3212646 -- January 2017 Security Monthly Quality Rollup for Windows 7 SP1 and Windows Server 2008 R2 SP1
- MS17-004 Security Update for Local Security Authority Subsystem Service (3216771)
KB3212642 -- January 2017 Security Only Quality Update for Windows 7 SP1 and Windows Server 2008 R2 SP1
- MS17-004 Security Update for Local Security Authority Subsystem Service (3216771)
KB3210063 -- Update for Windows Server 2012 R2 -- "0x000000D1" Stop error with update rollups on Windows Server 2012 R2
KB3210083 -- Update for Windows 8.1 and Windows Server 2012 R2 -- iSCSI disks are lost on upgrade for StorSimple appliances after update 3172614 is installed on Windows Server 2012 R2
KB3210694 -- Update for Internet Explorer -- Internet browser page becomes blank after you install security updates 3185330 in Windows 7 SP1 or security update 3185331 in Windows 8.1
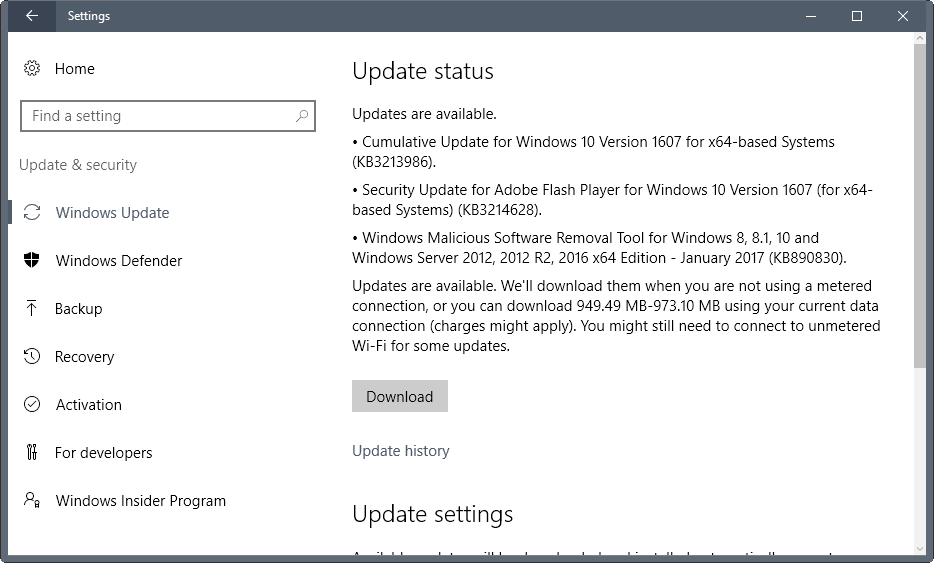
How to download and install the January 2017 security updates
Microsoft releases individual patches for Windows Vista, and cumulative updates for Windows 7, Windows 8.1 and Windows 10.
This means that options are limited when it comes to updating systems running Windows 7 or newer versions of Windows.
Patches are provided via Windows Update. Please note that the full security and non-security rollup updates are provided through Windows Update, but not the security-only rollup updates. If you only want security updates, you have to download them from the Microsoft Update Catalog instead.
Download links are provided in the next section below.
To check for updates on Windows Update, do the following:
- Tap on the Windows-key on the keyboard, type Windows Update, and select the result of the same name.
- Click on the check for updates link on the page that opens if that is not done automatically.
Updates are also made available on Microsoft's Download Center and through the Microsoft Update Catalog. Microsoft stopped releasing monthly security releases in August 2016 apparently.
Direct update downloads
Windows 7 SP1 and Windows Server 2008 R2 SP1
KB3212642 -- January, 2017 Security Only Quality Update
KB3212646 -- January, 2017 Security Monthly Quality Rollup
Windows 8.1 and Windows Server 2012 R2
None this month -- January, 2017 Security Only Quality Update
None this month -- January, 2017 Security Monthly Quality Rollup





















Ever since these security updates I have been plagued with dns failures ……Nothing suggested so far has fixed it. some help would be appreciated.
Same problem (see January 22 2017 post) has happened after installing Cumulative Security Update for Internet Explorer 11 for Windows 7 for x64-based Systems (KB 3185319)
Regards
Richard
After installing KB3212646 on a friends Windows 7 Home Premium laptop, when I open Internet Explorer 11 my home page loads but then a separate window opens, entirely blank, which probably is wanting some response from me before I can proceed. Being blank I have no idea what it wants. There is no way to close this window (no X) and I can’t close or do anything with the normal window with my homepage on because Windows just dings to show the separate window is the active one. Have had to do a system restore and will have to put KB3212646 into hidden updates for now (or tell friend to use another browser).
Regards
Richard
I installed KB3212642 and KB3212646 yesterday, and immediately after rebooting I noticed an issue with my mapped network drives. All of my mapped network drives (Which are mapped by a logon script) now show up in a “Disconnected” state. However, when I double click on the drives, I can access the contents of the network shares.
When I manually try to delete/disconnect the drives then re-map them, the drives do not disappear. I’ve tried disconnecting the drives via the GUI, and command line using a net use drive: /delete command.
This problem happened immediately after rebooting once these patches were installed, and I see this behavior on 10 machines (Windows 7 SP1).
Is anyone else seeing similar behavior after installing January 2017 Microsoft patches?
Thanks,
Mark
trying to get into sky go’ comes up saying “check your device is in correct time zone”,
will not play, right click brings up Silverlight what do I do ?, going around in
circles here.
i’m on Windows 8.1
since the first of this year every second Tuesday i’v had trouble getting updates from Microsoft it takes me over 2 days for Windows updates to even see’s any updates
the green line under checking for updates just keeps going and going for days no error just keeps going
just because i did not jump on there Free Win 10 is all i can think is why
lol
:)
I have found a better or faster solution on fixing Windows 7 x64 stuck at checking for updates issue.
1. Download and install KB3020369 https://www.microsoft.com/en-us/download/details.aspx?id=46817
2. Download and install KB3172605 https://www.microsoft.com/en-us/download/details.aspx?id=53332
(Or the other way around.)
And you are done. :) I dont know if it will work on windows 8.but it did fix the long checking for update problem for me.
MS already forgot their new policy of not superseding Security Only updates with Security Monthly Quality updates. The January 2017 full update supersedes the October, November, and December 2016 Security Only updates. Another day in the life… Thanks MS
See this article on update supersedence if you want to know more about it: https://www.ghacks.net/2016/12/12/changes-to-windows-update-supersedence/
I asked about it on the Blog post by MS and looks like they fixed this issue. After a catalog sync, the Security Only updates are back to normal.
Scott Breen:
As far as I know they aren’t supposed to be superseded! I’ll let you know what I find out (if anything).
Looks like it’s resolved. Synchronise your ConfigMgr / WSUS to see the changes
Yes, and that is exactly what they broke this month. January, 2017 Security Monthly Quality Rollup for Windows 7 (KB3212646) replaces December, 2016 Security Only Quality Update; November, 2016 Security Only Quality Update; and October, 2016 Security Only Quality Update. According to the image under “The Fix,” these are not supposed to be superseded by the Rollup.
Thanks for the info Martin. No security updates for 8.1? That’s got to be a first!
I simply accept and download all updates for Windows 10 without any question. No research required…. If Win 10 needs patching…patch it…and thank you very much for doing so!
All January 10 2017 Patch Tuesday updates downloaded and installed successfully. Now I can worry about matters other than my OS 14393.693. Thank you Microsoft…loving Windows 10.
Many thanks Martin for this article and all the previous ones about Microsoft updates. Your work greatly simplifies the research I always do before I apply any patches from Microsoft on my Windows computer.
Best regards.