A Serious Security Risk: Three Zero-Day Vulnerabilities You Need to Patch Now!
Microsoft released security updates for all client and server versions of Windows that it supports yesterday. Among the 30 or so security issues that each version of Windows is affected by are three zero-day vulnerabilities that are exploited already.
It is interesting to note that all three of the zero-day vulnerabilities have received a severity rating of important. Each version of Windows is also affected by critical vulnerabilities, but none of these critical issues seem to be exploited currently.
Microsoft Publisher Security Features Bypass Vulnerability
The first vulnerability that is exploited in the wild affects Microsoft Publisher. The ID is CVE-2023-21715, and it affects systems on which Publisher, a Microsoft Office application, is installed on. Microsoft specifies further that only Microsoft 365 Apps for Enterprise are affected by this.
The exploit targets the recent change in macro use in Microsoft Office. Microsoft implemented a security feature in Office recently that blocks macros in documents that come from untrusted sources, including the Internet.
The exploit may be used to bypass these macro protections, so that documents with malicious macros may still be used to attack Windows devices.
An attacker would have to convince a user to run a specially crafted Office document on the target machine. It could be distributed via websites or through other means.
Windows Graphics Component Remote Code Execution Vulnerability
The second vulnerability, filed under CVE-2023-21823, is rated important as well. It is a remote code execution vulnerability in the Windows Graphics Component.
Microsoft notes that an attacker who manages to exploit the issue may gain SYSTEM privileges on the target device. Microsoft's description lacks clarity, as it lists a number of affected products, including client and server versions of Windows, but also Microsoft Office for Android and iOS.
One of the FAQ entries on the support page suggests that the issue could be related to OneNote, as Microsoft mentions OneNote for Android specifically there.
Windows Common Log File System Driver Elevation of Privilege Vulnerability
The third and final vulnerability, CVE-2023-23376, that is exploited already is an elevation of privileges vulnerability in the Windows Common Log File system driver.
It has a rating of important and attackers could exploit the issue to gain SYSTEM privileges on attacked systems. All client and server versions of Windows are affected by the issue. Microsoft does not reveal how a potential attack scenario looks like.
Closing Words
Windows Home users and system administrators may want to address the issues immediately to protect devices against potential attacks. The severity rating of important suggests that Microsoft does not see the security issues as a major threat to a large percentage of the Windows population.
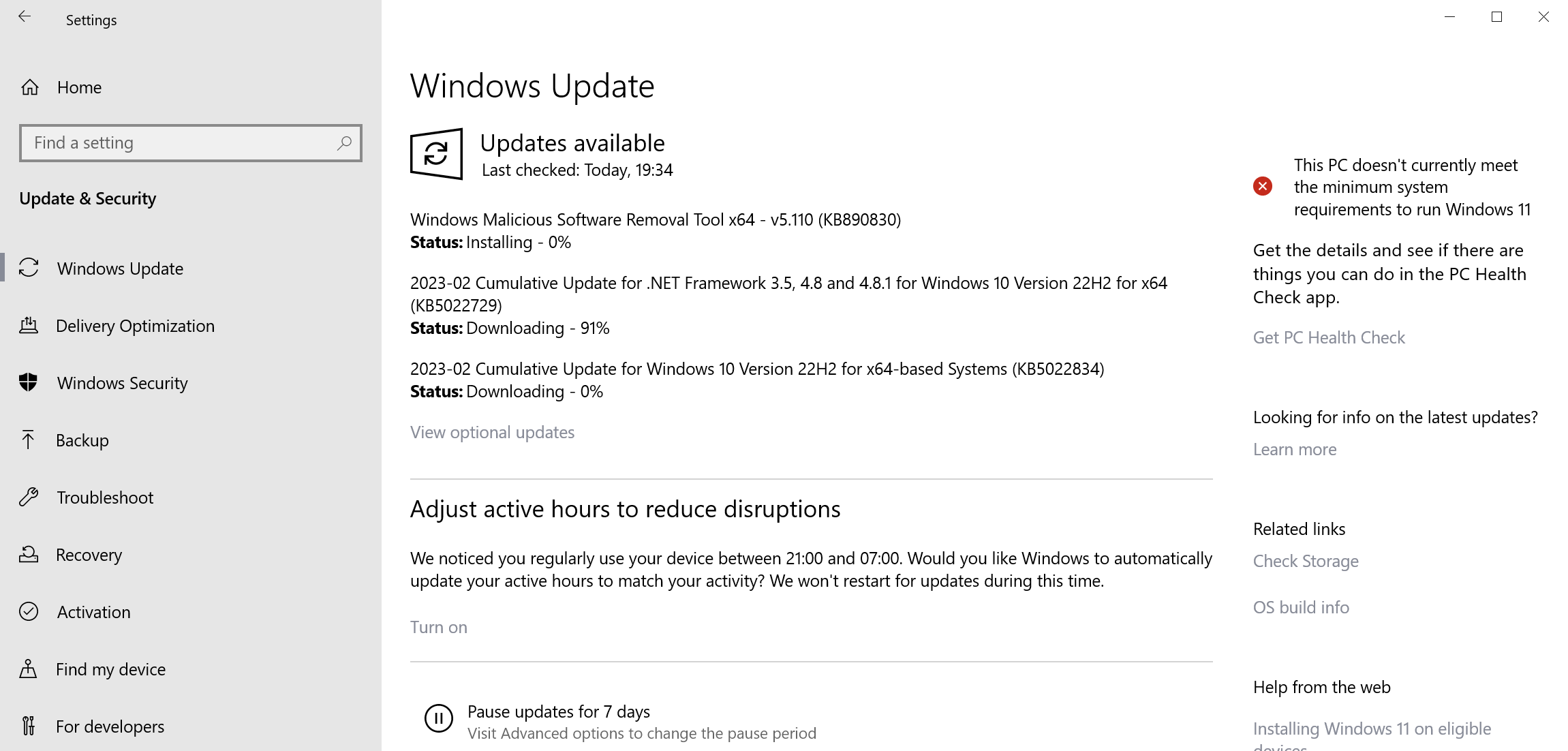
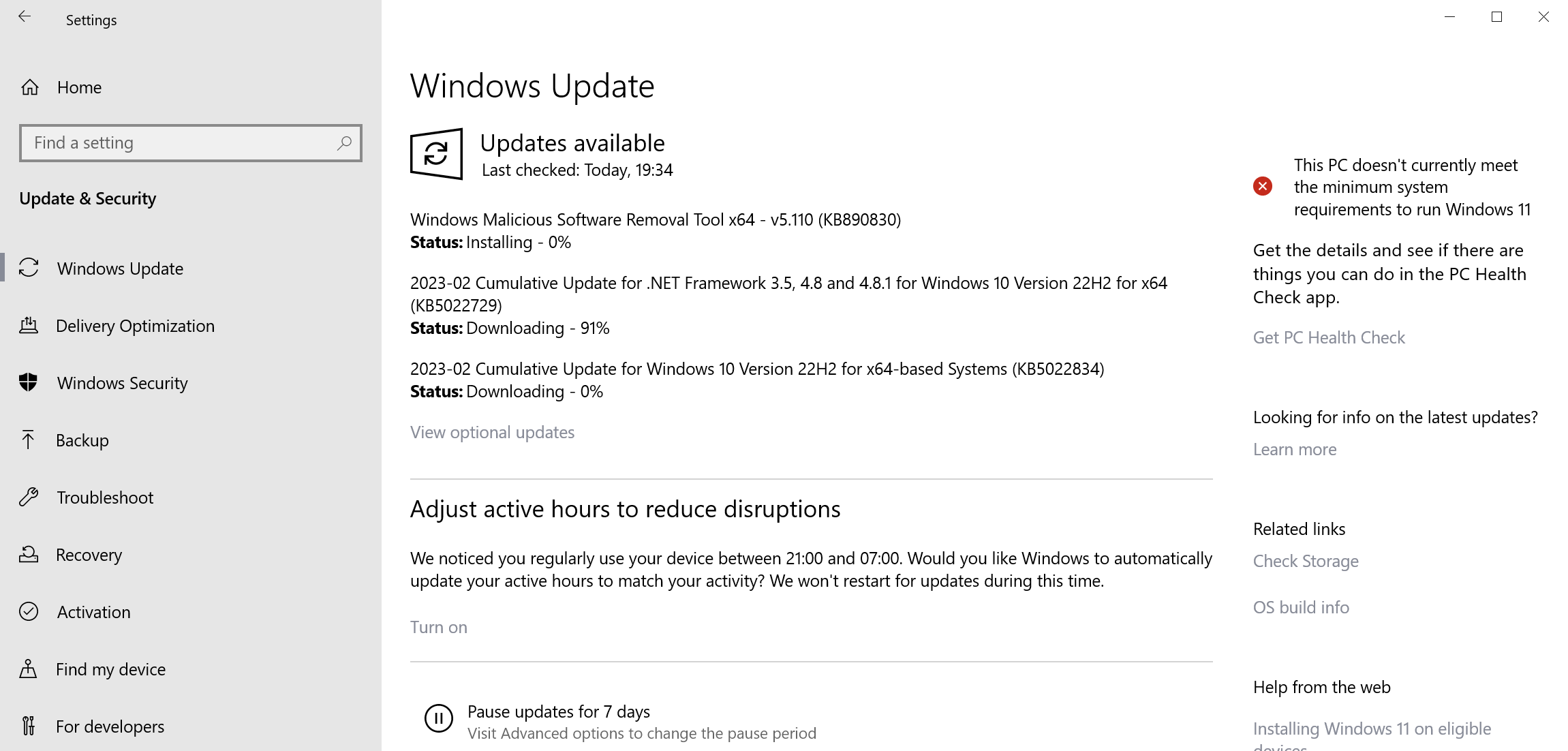
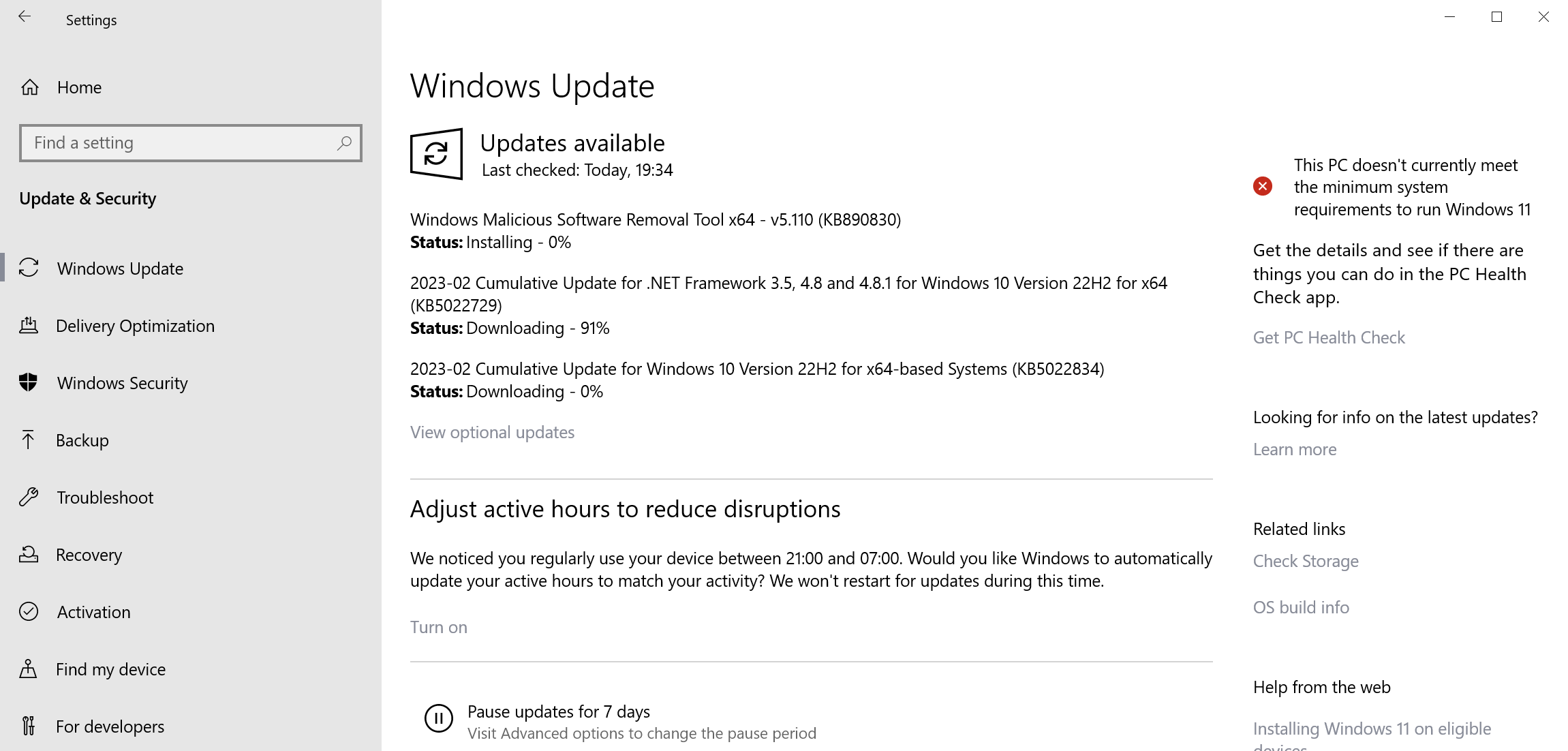
Still, to be on the safe side, administrators may want to install the monthly security patches provided by Microsoft yesterday for all supported versions of Windows.















Don´t worry the system is on regeneration. Possible errors happens but the solution is possible with hard work and determination.Best regards .HNETOCorporation
“Microsoft does not see the security issues as a major threat to a large percentage of the Windows population.”
So why the hyperbolic title?
Just about all of news is now ‘hyperbolic’ because its the best bait to use to grab readers attention.
A security flaw is a security flaw.
^^