Run Windows Update on Windows 10 manually only
Windows Update Mini Tool Wrapper Script, or short WUMT Wrapper Script, is a free script for Windows 10 to control Windows Updates.
Microsoft seems to tinker with the Windows Update service with every release of Windows 10. The company introduced and removed options to block Windows Update from several editions of Windows 10, added pause and defer options, ran into problems with driver updates, and made a mess of something that was pretty easy to manage in previous versions of Windows.
The company wants its customers to be up to date at all times, and tries to enforce this by making all those changes which make it difficult to stay in control of updating on Windows 10.
Even if you disable the Windows Update, you may notice that Microsoft enables the service again at times.
Windows Update Mini Tool Wrapper Script
You can download the complete package on Majorgeeks, or only the Wrapper script and the Windows Update Mini Tool instead (link below in the summary box).
First thing you may want to do is open the command script in Notepad or another plain text editor to make sure it is only doing what it is supposed to do.
You will notice the following:
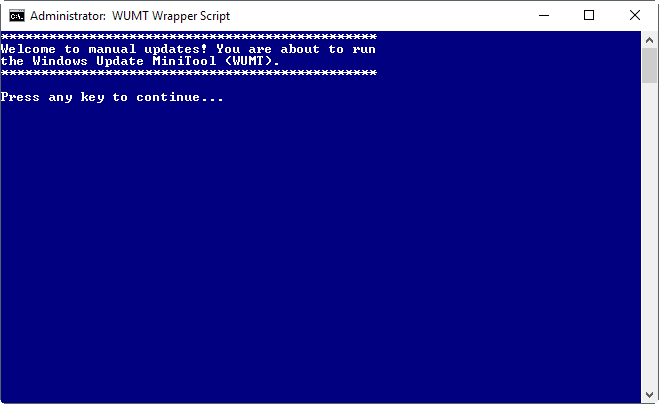
- It gets elevation for the process.
- Starts the Windows Update Service.
- Runs Windows Update Mini Tool afterward and runs a check for available updates.
- All updates are displayed in the interface afterwards. You may select none, some or all, and download them to the local system, and install them as well.
- When you close the program, the Windows Update service is set to disabled.
To be precise: Windows Update MiniTool Wrapper performs the following operations to make sure that Windows Update is disabled:
- Uninstalls and removes the Windows 10 Update Assistant.
- Renames the rempl folder in %programfiles%\rempl to disable remsh.exe
- Resets and removes permissions from UsoClient.exe, WaaSMedic.exe, WaasMedicSvc.dll, WaaSMedicPS.dll, WaaSAssessment.dll, and SIHClient.exe to disable them.
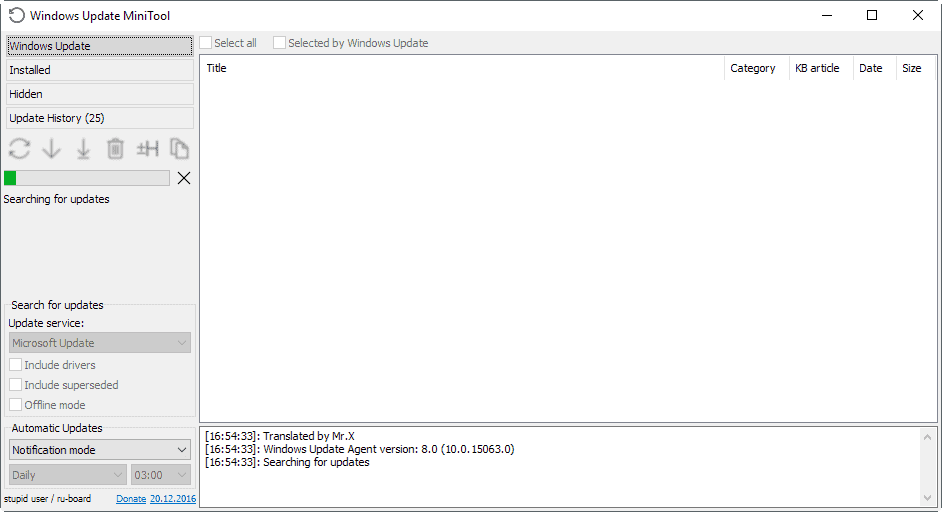
The main benefit of running the wrapper script is that you don't need to enable and disable the Windows Update service manually each time before and after you check for updates using this tool or any other program designed for that purpose. It makes sure that Windows won't check for or download updates unless you actively initiate the process.
All you need to do is run this one script, select the updates you want to download and install, and wait for the process to complete. This gives you full control over the updates that get installed on the machine you run the script on.
This method prevents automatic restarts that interrupt work among other things as well. Since you are in control, you may run the script whenever you have the time to download and install updates, and restart the computer afterwards.
One downside is that you need to run the script regularly to install security updates that Microsoft releases. You could create a Scheduled Task for that on Windows, add the second Tuesday of each month to the calendar (or any time after the official Patch Tuesday happened in a month), or simply remember to run the program regularly for that.
Closing Words
Windows Update Mini Tool Wrapper Script is a solution for advanced users who want to be in control when it comes to Windows Update. The main benefit of the script is that it makes using the Windows Update Mini Tool exclusively for updates more comfortable, as you don't have to toggle the state of the Windows Update service each time before and after you run the program.
The program interferes with system files on the other hand which some users may not like. Users who want to use Windows Store or download Windows Defender updates need to run Configuration.cmd.
Restoration is possible by running uninstaller.cmd which is included in the program directory as well.
Now You: How do you handle updates on your system?

























I was a fan of WUMT for my Win7 and Win10 machines but it started to fail to work correctly each month. Replacing WUMT each time did fix the issue but I decided to go back to deferring on my Win10 machine then manually install just before the next patch Tuesday rather than allow Windows to ruin the update process on my behalf.
Windows 7 still allows full control :) So I am testing WSUS Offline Update on it. So far, other than using a lot of disk space, there is nothing negative to report.
Before using WSUS offline, the first thing I researched was how to exclude unwanted patches (e.g. Telemetry and the downloads that ‘broke’ Excel 2010 Workbook_Open code on my PC – seemingly, nobody else has the issue). From memory, there are at least two ways to do this. One excludess download. The other prevents installation of downloaded updates. I can’t find the article that gave full details but here is an extract from an unnecessarily long article on WSUS update:
“It is possible to prevent the installation of individual updates, such as when it becomes known that a specific patch causes problems. To do so, enter its KnowledgeBase ID into the “exclude-list.txt” file in the \client\exclude folder on the basis of the pattern 123456. The installation script will skip over any updates indicated there, recording that it has done so in the log file.”
Actually, the folder to put it in is the Custom folder a level below the Exclude path.
Just enter one relevant KB number on each line of the file and save.
I use this PowerShell code to perform command-line Windows Updates on all my servers and workstations, in case anyone is interested in another option: https://www.powershellgallery.com/packages/PSWindowsUpdate
Still better to use WSUS Offline once a month. It’s slow but I know I’m not getting telemetry filled rollups from it.
I don’t use it anymore. Because it seems that this program broked my Windows Update=It was permanently disabled. I had to reinstall Windows…
This used to work for me but no longer does. It starts and looks for updates, but just gets in a loop and never finds anything. This has been the situation both before and after Creators Update. I started to try to implement what Karl O. was talking about but could find no such places in my registry to input that command.
At present I use WinUpdatesDisabler to block updates until patch day, then use it again to enable updates and manually update using W10Privacy. Every change of setting with WinUpdatesDisable requires a restart, and W10Privacy is sluggish, but it informs me what each update is and lets me choose which ones to update.
Maybe your use of the WinUpdatesDisabler has removed the keys Karl O. stated. The binary value “NoAutoUpdate” is already associated with both keys on my system.
Still adding
‘NoAutoUpdate’ with value ‘1’ to
HKLM\SOFTWARE\Policies\Microsoft\Windows\WindowsUpdate\AU
and
HKLM\SOFTWARE\WOW6432Node\Policies\Microsoft\Windows\WindowsUpdate\AU
works on Creators Update to disable Windows autoupdates.
After that you can check on your own for updates the usual way.
Another great tip!