How to modify your browser's fingerprint so that it is no longer unique
Tracking is one of the things that Internet users are exposed to no matter where they go. Websites use analytics software to track them, advertising companies use tracking to make more money because of targeted ads, and social media sites too may know where you have been almost at all times because of buttons and scripts that are installed on the majority of websites.
There are less obvious ways to track users though, and one of them comes in the form of a browser's fingerprint. When you connect to a website, information about your system and browser is made available to the server you are connecting to. The information may be used to fingerprint the browser; this may work really well, especially if enough identifiers are known. Considering that the remote server has access to information such as the browser's user agent, headers, time zone, screen size and color depth, plugins, fonts and a number of other data points, it is quite possible to generate fingerprints and use these in addition to other tracking methods.
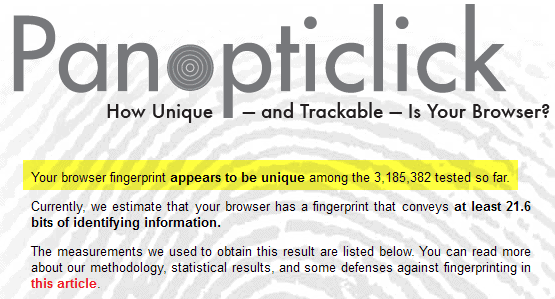
Panopticlick
The idea behind Panopticlick was to provide Internet users with the means to look up how unique their browser's fingerprint really is. To find out, simply load the website and run the test on it. You end up with a score in the end that tells you if your browser is unique among the browsers that have been tested so far, or if it shares the same fingerprint with others.
Unique is a bad thing in this test, as it means that no other tested browser shared all characteristics with yours. With that fingerprint created, it is theoretically possible to identify you on websites that you visit, provided that your browser got a unique score.
That score changes when parameters change, however, and there is always the chance that another browser may have the same fingerprint.
Note: While the score is displayed as unique by the test, it does not necessarily mean that it is indeed unique, considering that the majority of Internet users have not tested their browser on the site.
Tweaking your browser
If you do not like the idea of your browser having a unique score, you may be interested in tweaking it to reduce the identifying bits of information that it reveals when it connects to websites.
This may sound easy at first, but is not really because of the following. Some information cannot be disabled, as they are always transferred no matter what you do. Disabling certain features, like plugins, can also be used for the fingerprinting. If you run your browser without plugins, then this is a clue that websites can use as well for the fingerprinting but it is better than revealing unique plugins to sites.
So how do you get your browser from having a unique fingerprint to one that shares its fingerprint with other browsers?
The idea here is to modify settings such as the user agent or screen size and depth so that they match the largest percentage of browsers. Instead of using a Firefox Nightly user agent for example, you may use a user agent that is more commonly used.
One option that Firefox users have for that is the Random Agent Spoofer extension. It has not been updated in a year but it is still working fine. It changes settings to common values so that your browser's fingerprint turns out to be less unique than it actually would be without.
Probably the most interesting option that it provides you with is its random mode. Fingerprint tracking can only work if the browser's fingerprint does not change. If yours is random, because of changing information, then it is not really possible to identify all those random fingerprints as belonging to a single browser, unless other tracking technologies are used in addition to that.
Note: The user agent used by the extension is an old Firefox user agent. The reason why it works that well in the test is likely that other users who have installed the extension in Firefox have taken the test on the Panopticlick website in the past.
Closing Words
If you are not using Firefox, your options to reduce your browser's fingerprint may be limited. You can try and install a user agent modifier and switch to a common one, disable plugins such as Java or Flash to avoid them providing websites with a list of fonts your system supports, but that is about it.
Have another tip on how to cope with browser fingerprinting? Let me know in the comments.


















AEZAKMI is a browser fingerprints builder for multi-accounting. The main advantages of this tool: quick setup, ease of use, security and accessibility.
In addition, AEZAKMI is adapted for working with Facebook.
What can be done with AEZAKMI:
– set up and save a new fingerprint profile in 5 clicks;
– import cookies in JSON format. FvckBookShop branded Facebook accounts are loaded in two clicks;
– AEZAKMI has a function for receiving Facebook ads token;
– connect the main types of Proxy;
Besides:
– automatically set up GEO by proxy + manual GEO settings;
– save running sessions, cookies and histories in the Local Storage of each browser profile;
– save and transfer customized profiles with running sessions, cookies, logged in login forms; load saved profiles on other PCs;
– use a large database of fingerprints of real network users;
– experienced users can customize the created fingerprint whatever they want;
https://aezakmi.run/
There is a software called Kameleo that is meant to do it exactly. It is a market leader in browser fingerprint spoofing.
Check out: https://kameleo.io/
Defeating JavaScript fingerprinting technologies
Beating Canvas fingerprinting technology
WebRTC spoofing
Simply start a session with 100% privacy
Saving and reloading profiles with it’s cookies and history
Notes and attachments included to your profiles
Proxy management for super privacy
Automatic updates on the defender technology
I realize that this article was written four years ago and FF settings have changed in the meantime, but I tried the extension a few days ago. Although it does the job it also resets Firefox ESR 52.3.0 cookie settings to accept third party cookies.
There’s also one other preferences setting that it changes which is to checkmark the option to enable sites to use their own fonts.
For those two reasons I stopped using it.
You are right, Steve!!! The only browser I know of, which is going that way, is the Brave browser. It stops ads and trackers on default. But it is still in development.
Browser’s are way to open and is developer faults why that happens !!! The solution would be some sort of firewall built in filter and no execute all of nasty java script cookies and so on and it should be a part of browser !!!
Due to the fact that Flash is mostly needed for sites like Youtube, it may be worth while to disable Flash from sending your System Fonts. This can be done by creating / editing a mms.cfg file (MM for Macromedia) and adding the line DisableDeviceFontEnumeration = 1 to that file. Sites like Panopticlick on EFF will simply get an empty list of your system fonts.
This file will be different for Chrome and needs to go in a different place.
Please note that both Java and Javascript still send your System Fonts back to websites for Fingerprinting.
When the system and browser settings change 2 or 3 times every week (like mine), it’s not really a fingerprint guyz. Somebody is selling you some deep-lake real estate here. They can id you better with an IP address than they can with these ever-changing system settings (which could never stand up in court). Get a VPN to switch your IP at will. Get a mac-address switcher and turn your modem off/on periodically. The numbers of configurations in their databases are growing exponentially, so they’ve got a little problem trying to track people by these system configurations.
If you really want anonymity, install Tails into a virtualbox, and run it in bridge mode. Then run the browser from that environment. If you like windows then use Comodo and configure your firewall so nothing leaks out, and use OpenDNSCrypt so your DNS lookups do not leak.
The only thing you got wrong is OpenDNSCrypt. Why in the world would you use a U.S company for DNS? If you want to get away from the U.S than what you all need to do is use a EU DNS with no EU Gov oversight, preferably BlockAid DNS.
And don’t use this if you use any online service requiring a login like Outlook or a webmail page.
They won’t load messages with stripped info.
Been using “User Agent Switcher” http://chrispederick.com/work/user-agent-switcher/
There was a “what is my ip address” website out there that said, you need to change your user agent, and so I found this extension. Been using it for at least a year now.
I use this one to check my opera browser
http://ip-check.info/?lang=en
Theni adjust settings accordingly
https://anonymous-proxy-servers.net/wiki/index.php/Opera_Browser_en
What’s a Java and Flash font?
I only have Flash enabled, and it said no Flash or Java fonts. I have Better privacy installed in another profile so that could be why I guess.
An interesting bit.
With JavaScript enabled for that page
21.6 bits
and without
14.35 bits
Gotta love NoScript
I can’t imagine add-ons affecting anything or exposing anything unless they connect to a site or service or something like that.
That means that the website uses the Java or Flash plugin on your browser to get the list of fonts on your machine. That is powerful since it allows a tracker to further differentiate two machines with almost identical fingerprints.
In fact, some trackers can differentiate two “identical” machines, even if both have the same installed fonts, if there is a discrepancy with the order of installation of fonts. If machine 1 installed Century Gothic before Helvetica Neue and vice versa on machine 2, they can use that.
You can learn more about online tracking on the Panopticlick website, listen to the Security Now podcast ep #264, or peruse stayinvisible.com.
Thanks a lot Dan for that explanation.
Aside from keeping Flash disabled, is there any way to block this from happening?
Just like when the last IE6 install is upgraded, when Flash disappears, we’ll all be so much better off.
I have a good understanding about privacy, tracking, etc, but I’m not an expert on it.
EFF is a great site and organization that fights for us all, like Mozilla.
Your browser fingerprint appears to be unique among the 3,187,706 tested so far.
Currently, we estimate that your browser has a fingerprint that conveys at least 21.6 bits of identifying information.
______________________________________________________________________
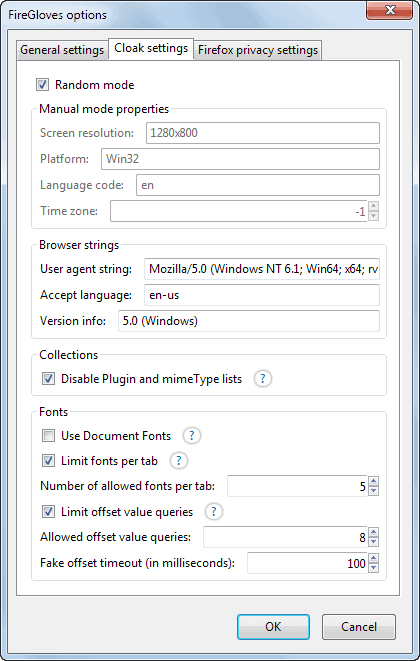
Dear FireGloves users and visitors!
The current version of FireGloves is a proof-of-concept application, which we have created for research purposes (see fingerprint.pet-portal.eu for details). Unfortunately, we can not continue the development of FireGloves due to changes in our team; however, we hope that similar privacy-protecting functionality will be available in mainstream browser in the near future.
With kind regards,
The FireGloves team
You are serious? Like this is supposed to be statistically valid? As in . . . if I showed this to my mathematics professor, he would go, “Wow!” Don’t think so.
Why is there no browser that prevents websites from gleaning info such as fonts, screen resolution, plug-ins, OS version etc? There should also be no useragent. If the websites stick to standards, they will open on reasonably uptodate browsers. If not, the user will be advised to update.
Is there a similar extension for Chrome/Opera15?
i haven’t find one
Martin notes “While the score is displayed as unique by the test, it does not necessarily mean that it is indeed unique, considering that the majority of Internet users have not tested their browser on the site.”
Panopticlick states : “Within our dataset of several million visitors, only one in 1,593,193 browsers have the same fingerprint as yours.”
If I were an analyzer it seems I’d doubt.
this addon, is too much restrictive, we can’t customize very well , and finally, my broswer just crash with some website, uninstalled …
I do not think this is possible to hide fingerprint with 70 extensions like on mine Firefox. If you can find program/extension that can block websites from seeing installed extensions, than we can talk anonymity.
I got 21.6 on every system I tried, different browsers, os, builds, and you got the same score. That all seems like it doesn’t do a thing aside from the attempt to fear monger people.
More add-ons you have less unique your browser is.
Actually the opposite is true. What are the chances that anybody else using the same 70 extensions? Slim if none.
Chrome’s incognito mode by default doesn’t use any extensions (you need to allow them in settings)
and then you won’t be utilising the randomising and hiding functions of those extensions, either :|
So does Firefox’s Private Browsing. That doesn’t actually solve his problem though of trying to hide his extensions while he’s using them.