Malware found in over 100 signed Windows drivers

Yesterday's security updates for Windows and other Microsoft products came with an advisory regarding the malicious use of Microsoft signed drivers.
Security researchers at Sophos, Trend Micro and Cisco informed Microsoft about malware in signed drivers in February 2023. The researchers discovered that drivers "certified by Microsoft's Windows Hardware Developer Program were being used maliciously in post-exploitation activity".
The researchers identified 133 different drivers, the majority certified, by multiple developer accounts and reported their findings to Microsoft. Some of the signed drivers date back to April 2021 according to Sophos.
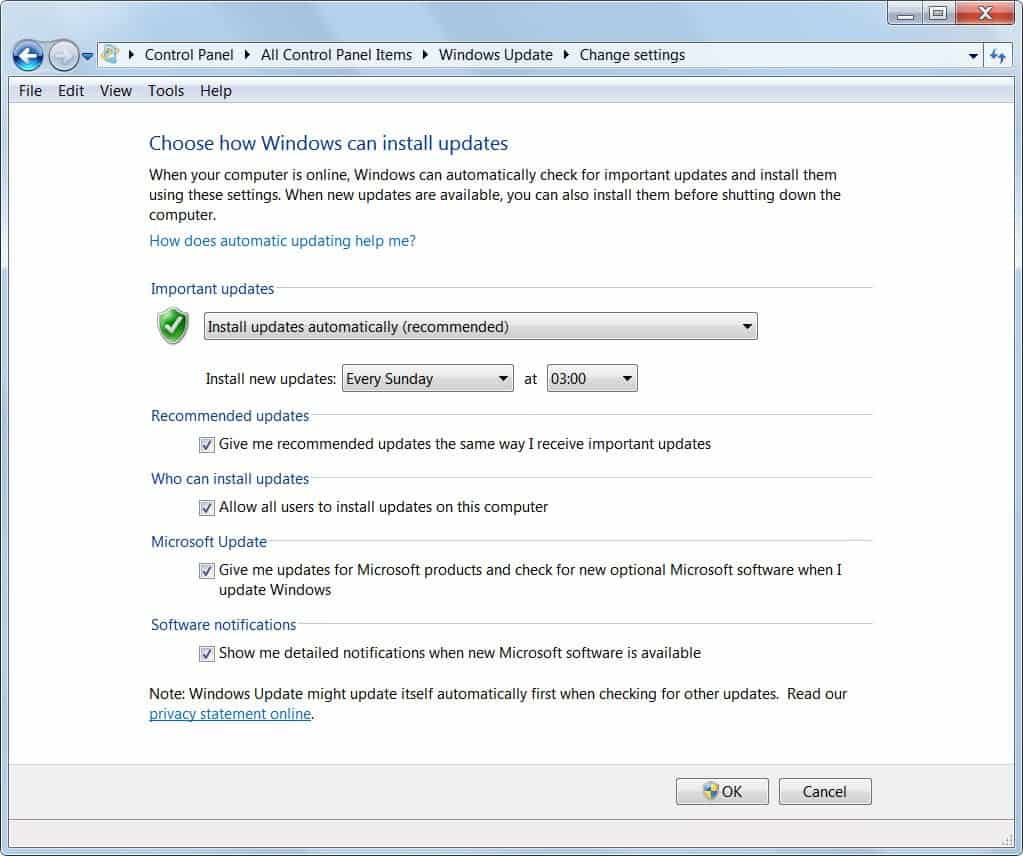
Microsoft is blocking the malicious drivers and has closed the responsible developer accounts. The drivers have been put on the Windows Driver.STL revocation list; this list prevents them from being loaded on Windows devices. The revocation list ships with Windows and is updated regularly via Windows Update. Microsoft notes that the list is not part of Windows and that it can't be disabled, removed or manipulated.
Windows administrators should make sure that the latest Windows updates are installed and that third-party security software is up to date as well. Administrators should run offline scans on their devices to detect malicious drivers that were installed before March 2, 2023. Sophos has published hashes of the malicious drivers on GitHub.
Other Microsoft services, including Microsoft 365, Azure or Xbox are not affected by the issue according to Microsoft's advisory.
Microsoft introduced a policy in Windows 10 version 1607 that required a valid digital signature for kernel drivers. Windows systems with Secure Boot enabled load only these drivers and refuse to load any drivers not digitally signed.
Sophos notes that several of the digital certificates appear to have their origin in China, which it bases on the company names associated with the certificates.
Sophos researchers discovered two main types of drivers. Some fell into the "Endpoint protection killer" category, which were similar to maliciously signed drivers discovered in 2022. Others had rootkit-like capabilities and were designed to run silently in the background.
These drivers could only be installed by accounts with elevated rights. The rootkit drivers had network monitoring capabilities using the Windows Filtering Platform. It allowed the malicious actor to monitor incoming and outgoing Internet traffic.
At least some of the rootkits belong to known Windows rootkit families according to Sophos' analysis and many included command-and-control server functionality, which gave the malicious actor even more control over infected devices.
All malicious drivers that Sophos reported to Microsoft have been invalidated and revoked by Microsoft as of July 11, 2023. Microsoft Defender 1.391.3822.0 and newer versions of the built-in security tool detect the malicious drivers as well.



















this is normal, windows is the virus.
And I’m still using windows 7
C’mon… keep moving… nothing to be seen here… it’s just the usual “security” M$ so much boasts about… keep moving…
That’s bad. It reminds me of a Windows 10 computer a friend asked me to fix a few weeks ago. Back in about January, their USB ports suddenly stopped working. Then a couple of months later the USB ports started working again, but the hard drive slowed to a crawl, and eventually it would not boot at all. I assumed the hard drive had gone bad and replaced it with a small, cheap SSD. Since the person only needed it for web browsing, I just put a GNU/Linux distro on it that I knew would install quickly.
I wonder if all their previous USB problems and hard drive problems were related to malicious drivers? And if so, I wonder if by replacing the hard drive the rootkit will be gone, or if it has found a way to reside in the computer’s circuitry? And if so, would it have any effect on a GNU/Linux system?