Why Websites Never Need Your Password
It is common knowledge that a website, such as PayPal or eBay, will never ask for your password. They do not need it, but rarely do we hear about why that is the case. There are actually a few possibilities.
Please note, if you ever get an e-mail requesting your username and password, it is phishing for it. See our phishing protection tips for some tips on how to protect yourself. There is also a phishing flowchart to help you identify phishing. In addition to this, Gmail has a lab that will verify PayPal and eBay e-mails.
Websites Already Have it
While one would hope passwords are encrypted and kept out of harm's reach, that is not always the case. In many systems security is an after thought. Sometimes security policies and programs are not seen as necessary until after a breach. Important customer information is not always protected the way that it should be.
In a system like this your password my not be encrypted. It may be stored in plain text (sometimes called "clear text"). There may not be proper access controls in place either.
With the usernames and passwords so easily accessed, no one from the company needs to ask you for them. The company, or a number of employees within it, has access to them. This is a part of why it is important to use different passwords on different sites.
Top Level Staff May Have Access
A system with good security will encrypt your passwords. Even if someone who was not supposed to have access to the file containing passwords gained it, it would look like gibberish. There are ways get around this under certain circumstances, but over all the encryption keeps people from being able to read customer information.
That said, there will be people higher up who have access to the key which can decipher passwords. If a legitimate need for the information arose, such as a court order, then a ranking company official would be involved, not you.
While not directly relating to passwords, Dropbox works in a similar fashion. All data that Dropbox stores is encrypted, protected from staff and general misuse. The higher-ups are able to access the data, but only under special circumstances. They can give access to authorities, but it must be by court order. It is an example of how an encrypted system is still controlled by someone in the company.
Your Password May Not Be Stored Verbatim
Some sites and systems may use a cleaver trick to log you in. You would think, when you login, a server compares the username and password that you send with a username and password on record. That is not always the case.
Some systems will use your password and a random number, put them into a formula, and get a crazy looking code of letters, numbers, and symbols. This code is virtually perfectly unique to your password. The site stores this code and the random number.
virtually perfectly unique
http://blogs.msdn.com/b/tomarcher/archive/2006/05/10/are-hash-codes-unique.aspx
Unlike encryption, where the password can be retrieved if a key is used, the created code cannot be unlocked to reveal your password. It is a one-way process designed to make your password unreadable. It is difficult to figure out the password based on the code. The point to a system like this is that they do not want to know your password.
When you login again, you send your username and password. The system takes the password you send, puts it and the random number back in the formula, and forms the crazy code again. It then compares that code to the code on file. If they match, you are allowed in; if they do not match, you get an error. Voila, login without a stored password.
The crazy code has a special name: a hash value. Sony disclosed their use of hash values after the Play Station Network was brought down by hackers.
The System May Force Resets
Some systems will give limited tools to IT personnel (by policy, access, or design). In these cases, the only tool they may have available is a password reset. This is done to remedy the frequent problem of lost passwords. Passwords can be safely encrypted or hashed, yet access can be easily restored.
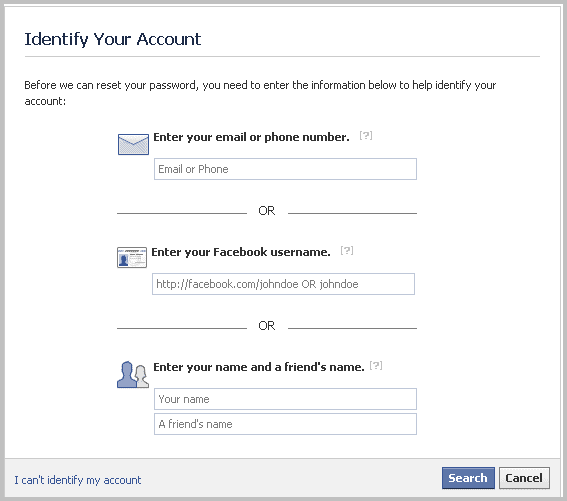
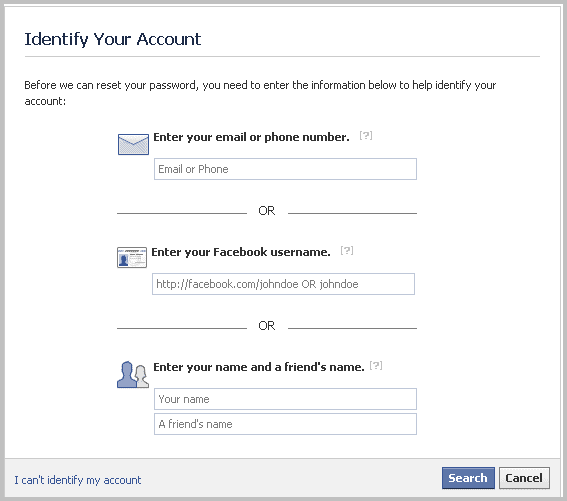
Facebook uses this system. You have to tell the website something about yourself first, but it will reset your password after you have. This automates the process so you do not have to wait for tech support.
Many Functions Do Not Require Your Password
In most systems, the employee logs in, is verified by the system, and has the appropriate access for the role they play in the company. The software they use may be able to modify your contact information, account balances, length of service, view your history with the company, etc. Heck, sometimes they can outright delete you. Think about how a bank teller can deduct money from your account when you ask for cash. By far, their username and password trumps your username and password. There is nothing legitimate that a bank could need your password for.
In Summary
As it has been stated by every reputable company, there is never a reason to give someone your password. The company will never ask for your username or password. These occurrences prey on ignorance. If you know someone who you think might fall for a ploy like this, educate them. They should be less likely to give the information out if they know why it is never needed.
Advertisement
















How do I recover my passwords and logins if I acadently deleted them on my fire fox account