Phishing Protection Tips

It is time to update the phishing protection article that we published some time ago (see Phishing explained) with the recent news that thousands of Hotmail users (and apparently Gmail users as well) fell pray to yet another phishing scam.
What is phishing? Phishing, which stands for password fishing, is a popular technique to collect data from users without their knowledge. This data is usually sensitive, like credit card information or usernames and passwords.
Phishing involves getting unsuspecting users on specially prepared websites that often look identical to the website the user expects. Phishing evolved in recent time as well thanks to the rise of apps in particular. Apps may also be used to steal account data from users.
Think of this example: A user receives an email from PayPal or a bank which states that the account was comprised and that action needs to be taken to protect the account.
A link is provided, and many users will click on that link to get to the website fast. The website looks like the real PayPal or bank website which adds to the trust the user has in the process. Even the web address may look similar.
The website asks for authorization, and most users will enter the data without hesitation. The data that is entered is collected by the attackers and is then used in criminal activity.
What is phishing
- Phishing always requires a user to visit a specifically prepared website (most of the time through a link that is added to emails or messaging) or install software or app.
- The fake website looks a lot like the real website (there are ways to detect fake websites, primarily through the URL).
- The goal of the attacker is to get the user to enter the data that they are after.
Phishing protection
The most powerful weapon against phishing is common sense and the following rules that every user should oblige to.
- If you are not a customer of the site delete the email immediately. Don't click on the link or reply.
- If you are a customer and you are not sure if the email is legit do one of the following:
- Contact the institute by phone or use contact options at the official website ( do not use the email link of course) and ask if the mail is official.
- Instead of using the link provided load the website by using your favorite browser to open it manually. The site should have news about the email on the starting page. (most of the time).
Thankfully though there are quite a few tools out there to aid and protect the user against phishing attacks.
- Most web browsers these days come with phishing protection enabled. The lists that they use are usually updated several times a day. It has to be noted though that they only detect phishing websites that are already on the list and that they don't offer 100% protection.
- Several email clients, like Mozilla Thunderbird, but also online email services, like Gmail or Yahoo Mail, make use of phishing protection lists as well.
- Internet security programs do come with phishing protection as well.
- Password managers can be an excellent aid. If you have saved the login for a website in the password manager, you usually can log in automatically (Last Pass, for example, supports that option). The password manager will only work on the real website and not the phishing website.
The most powerful protection again is the user's common sense. Here are a few pointers on how to detect if a website is real or a phishing site:
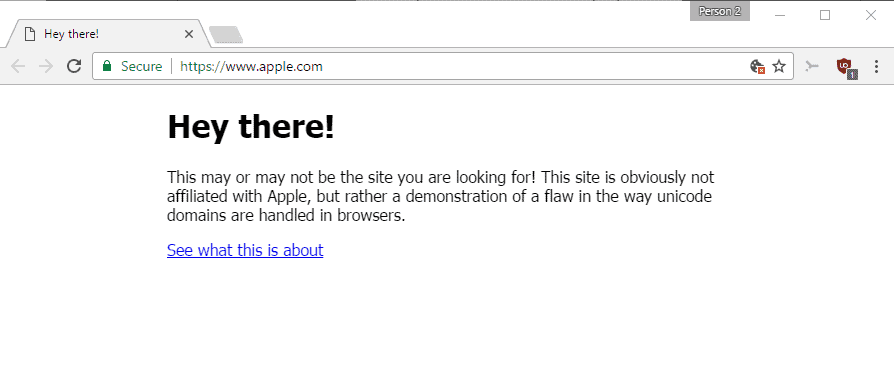
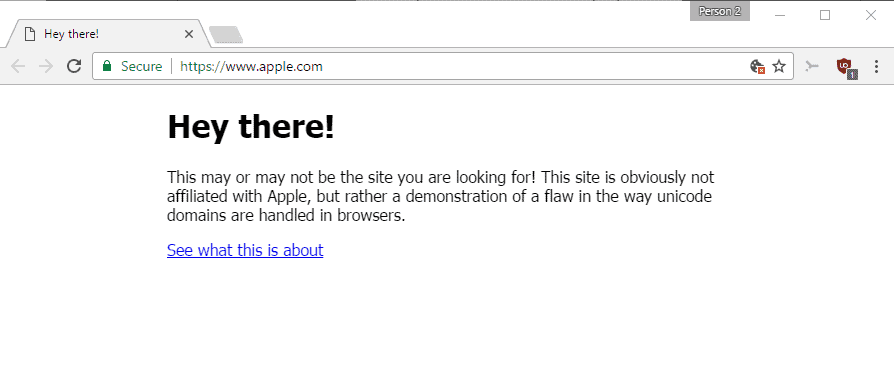
- Check the URL in the address bar. Is it pointing to the right website? Make sure you look close at chars that look similar, e.g., o and 0. See this article on Punycode Phishing attacks.
- Is it an https website? Is the certificate valid? Update: The rise of HTTPS and free HTTPS certificate services have made this method unreliable.
- Does the website look different? Open another web browser tab to enter the URL manually just to be on the same side (if you have opened an external link).
Firefox users can check if the phishing protection of their web browser is working. Do you have additional phishing protection tips?
Related Resources:
- Beware: new sophisticated Gmail phishing attacks
- Fell Prey to Google Docs phishing scam? Do this
- How to avoid the latest LastPass Phishing Attack
- Steam: How to protect yourself against phishing and scamming


















This may sound crazy, but write your passwords down! Yep. Write them down. http://www.f-secure.com/en_US/security/security-center/security-stories/cyberawareness.html
Mitto (http://mitto.com) is a great password manager. They write an article about how using their service helps you to avoid phishing schemes: http://mitto.com/blog/2009/2/3/how-mitto-protects-users-against-phishing-and-identity-theft.html
Well regarding the password management tools, I am using Sticky Password. It has all I need – password generator, secure database, only one password to rembemer.
http://www.stickypassword.com
“The most powerful protection is the user’s common sense”
Until someone invents a common-sense add-on for the human brain, phishing will flourish.