How to avoid the latest LastPass Phishing Attack
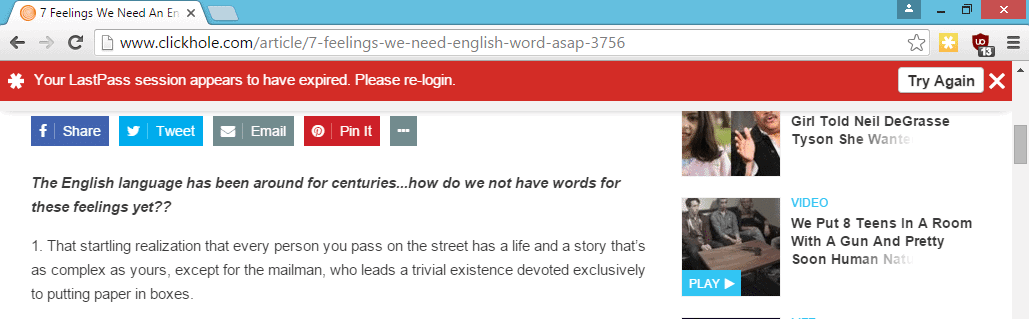
Sean Cassidy discovered recently that the popular password manager LastPass is vulnerable to a phishing attack that takes advantage of the way messages are displayed to users of the service.
The method that he describes on his blog works in Google Chrome, and to a degree in Firefox as well.
The main difference between the two browsers is that fake messages displayed to Chrome users on attack sites look identical to the message the LastPass extension would display to them, while that's not the case if Firefox is being used.
So how does the phishing attack work?
LastPass displays messages to users in the browser's viewport to which websites that are open in the browser have access to as well.
A malicious site would draw the LastPass notification after checking that the password manager is being used. According to Cassidy, they could even log out the user before they display the message to make it look more real.
The message would ask users to enter their username and password, and if configured, two-factor authentication code.
Obviously, the information can then be used by the attacker to gain access to a user's vault allowing them to access all account information, notes and other sensitive data saved in it.
Have you been hacked?
You can verify account access on the Account History page. There you find listed all recent log ins.
Do the following to get there:
- Click on the LastPass Icon.
- Select My LastPass Vault.
- In the left-menu that opens, select Tools > View History.
Each event is listed with a date, IP address, DNS and method used for the access.
How to prevent getting hacked
LastPass is working on a fix according to Sean Cassidy who disclosed the issue to the company last year.
The attack can be detected easily however.
- If you are using Firefox and get the log-in window, try to switch to another tab. If that works, it is a fake login prompt.
- If you are using Google Chrome, make sure the page where you are entering the credentials starts with chrome-extension://
Generally speaking, you may want to sign in on the LastPass website directly, and not via the extension. Once you are signed in on the site, the login gets picked up by the extension so that you can use its functionality as well.
Now You: How do you sign in to LastPass or other online password managers?



















So does the LastPass icon change when this attack occurs?
In the screenshot above…the icon is yellow…or is this just a staged screenie?
You can also enable “Show notifications below browser” through Preferences > Notifications, which will instead show messages at the bottom of the screen. If a message appears at the top while this is enabled, I’d assume there’s a high chance of it being a phishing attack.
And, at the risk of being a bore, I will repeat my mantra… learn to use keystroke pattern or password formulas that incorporate something unique about the site’s domain name. You can memorize one keystroke patter or passwords formula and apply that formula to every passworded account you have, modifying it in some way using the account name or domain name element as the modifier that makes each password or pattern unique to the site/account.
Using this method, you only need to memorize one pattern or password forumla. The modifier makes each application unique in some small way. I’ve been using this method for years. I have many, many online accounts and I don’t need a password manager.
I do, however, keep a password protected document handy for which I keep a log of coded hints, in case something goes wrong. I challenge anyone to guess my password from this hint, which is one of the hints in my password hints document:
the pattern: Yn>< c
the length: 13 characters
keys used in the pattern: 5
upper and lower case, alpha numerical
the the c is my modifier and is based on the second letter of the domain or account name. The Y and the c are given to you… they are the actual characters used in the password pattern. Try to guess the characters in between the Y and the c.
1. LastPass users should keep the program up-to-date. To do so, enable the “Auto update” settings in the “More Options” section.
2. Never save your very sensitive information online.
3. A user should consider changing or upgrading the password irregularly.
I’ve said this so often before, I hope you won’t dismiss me as a bore now. But please, please, let this get to your heads: all password managers (and certainly those that save your encrypted data in the cloud) are intrinsically unsafe. Should I repeat this as a mantra?
All – Passwords – Managers – Are – Intrinsically – Unsafe.
Sure, they do give you some more convenience, yes. But both on a theoretical process level and in daily usage practice it’s near-impossible to make password management more “convenient” without at the same time sacrificing some degree of security. And the developers’ rightful concerns about this will always lead to just more complex algorithms, which in turn will keep creating new vulnerability risks again. This is almost like a law of nature.
The safest way to manage your user names and password combos is to simply keep them on your own computer in a data file that is hidden within another file, a container that is kept well-encrypted using something like Veracrypt.
This container file should (by its name, extension, location, and creation/access date) be well-disguised as some quite ordinary system file, so that even when some intruder manages to get full access to your PC, he would not even have a clue where to begin to look for your encrypted passwords container. Meaning he will never even get to the point where he can start trying to decipher your encrypted password files.
Is a setup like this too cumbersome, too much trouble for you in daily use? OK, fine. But in that case, you really shouldn’t complain about the always-recurring security problems with password managers and/or cloud storage. In this case you should accept that when it comes to handling your passwords, it’s unavoidable that for more convenience you also pay with more risks.
I myself am happy to accept a little more fuss, with a little more security in return.
Henk, I disagree that all password managers are “unsafe”. I would instead say that all password managers “have security risks”. This is much more accurate than your sweeping statement. I think jasray was trying to make the point that every human activity has an element of danger in it, but we still undertake most activities because we have reasoned (rightly or wrongly) that the dangers are within our acceptable limits. (I won’t get into a discussion of judgment errors in risk assessment, although that’s a very interesting topic in its own right.)
If we are to assess the dangers of password managers fairly, we must first of all recognize that they do not all face exactly the same set of dangers. Cloud-stored password managers face different dangers from locally-stored ones. With the cloud, you have a much larger, juicier target for hackers; the possibility of MITM attacks intercepting passwords; and the risk that the service provider or some shady government entity will have access to the passwords. On the other hand, with locally stored passwords, we have the danger that a computer could be stolen or “borrowed” with all the passwords accessible. Both cloud and local password managers are at risk if an inept, virus-prone user continously makes bad online decisions that compromise the computer. (For that matter, your folder-in-a-folder method faces this risk too.)
You have the right attitude about accepting “a little more fuss, with a little more security in return”. This is my mantra too! It’s a question of where to find the tipping point between security and convenience. I believe that for most computer users, a locally-stored password manager is ideal. In the first place it avoids the pitfalls of cloud storage. But also it actually improves security because it permits people to create really long, complex, non-memorable, non-pronounceable, random or pseudo-random passwords, rather than to constantly re-use “123456” and “letmein” passwords. Yes, you lose a bit of security because of the risks faced by storing passwords on your computer, but you gain so much more security that the net result is very beneficial. Of course, for a fairly narrow group of people, more secure storage methods may be necessary (including memorization or pen and paper – but then we’re back at those tradeoffs again. Complex passwords are rather hard to write down.).
As for cloud-based password managers, I’ve said it before on this site (even last week): I believe they are TERRIBLE FOR EVERYONE ALWAYS. People like you and I were not surprised when this LastPass hack was announced. We won’t be surprised when the next one is announced, either.
“All – Passwords – Managers – Are – Intrinsically – Unsafe.”
Mantra–okay, so exchange a few words here and there:
All activities that we enjoy in life are intrinsically unsafe.
All women are intrinsically unsafe.
[Sure, they do give you some more convenience, yes.]
All politicians are intrinsically unsafe.
All Life Forms are intrinsically unsafe.
All websites are intrinsically unsafe.
All guns are intrinsically unsafe.
All Men are intrinsically unsafe.
Henk van Setten is a Man.
Therefore Henk van Setten is unsafe.
Do we trust and allow unsafe people to live in our society?
No!
I think Hitler never studied Logic, either. It would have been “too cumbersome, too much trouble for [him] in daily use.”
Oh my dear.
Jasray, I really fear you yourself are intrinsically illlogical. End conclusion, according to your own reasoning: you probably don’t even exist ;-)
Anyway, whatever weird rules of reasoning you want to follow, I do wish you some safety! Even, if it must be, from the burden of thinking clearly.
Lastpass?, since they decided to keep nagging me for their Premium service, I stop using it and switch to KeePass
with KeePass the only why to login is using the desktop app, so i guess it’s immune to this kind of attack.
Martin,
Great advice!.
But I need a clarification…
When you say:
“If you are using Firefox and get the log-in window, try to switch to another tab. _If that works_, it is a fake login prompt.”
Question:
what exactly do you mean by:
“if that works”?
I’m not clear on what specific “danger” symptoms I should be looking for,
when I “try to switch to another tab”…
Thanks!
Trek, if the login prompt prevents you from switching tabs while it is open, it is the real deal. If you can switch tabs, it is not.
Martin,
Very clear now!
Danke/ Thanks
and have a nice evening.
Great work!
Never assume that handing security to others is anything, but a con. In other words its designed as convenience only to those who do. The rest should be considered as filler or worse. If you think i’m writing in word salad jargon it’s just security feature.