Beware: new sophisticated Gmail phishing attacks
Researchers have discovered a new phishing attack that is currently underway that is targeting Google Gmail accounts in a sophisticated way.
What's interesting about this specific attack is that it uses a new method, one that could even lure tech savvy users into its trap.
The attacks begin with compromised Gmail accounts. The attackers use the compromised account to send emails to email addresses in the compromised account's address book.
These emails come from a legitimate address therefore, and the attackers seem to use legitimate email messages for the attacks. They contain what looks like an attachment, a PDF or spreadsheet for instance, something that may have been sent in the past already.
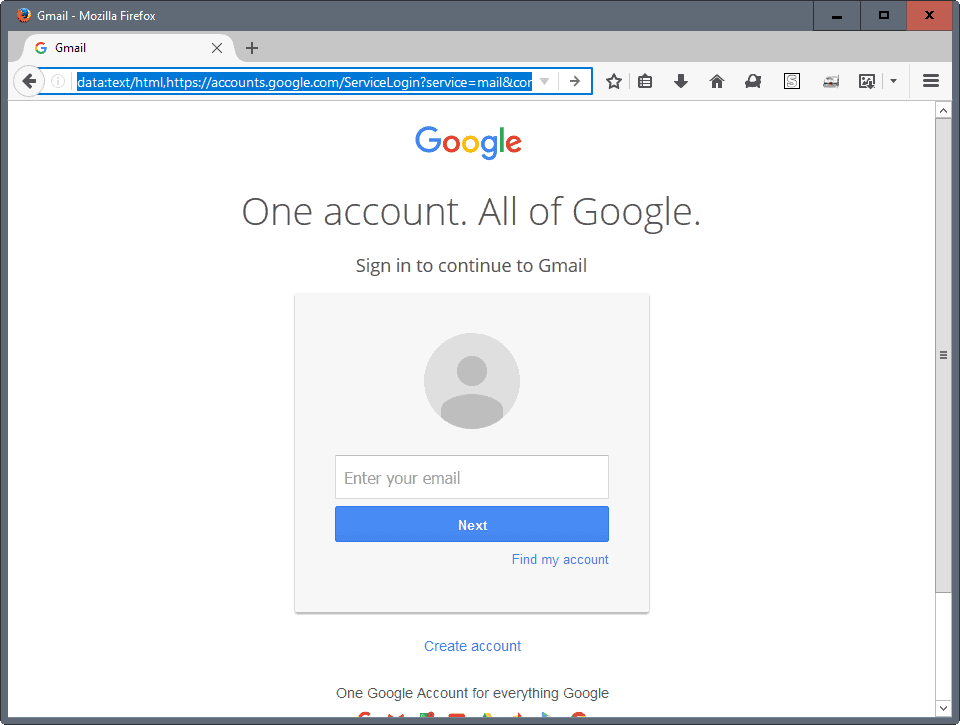
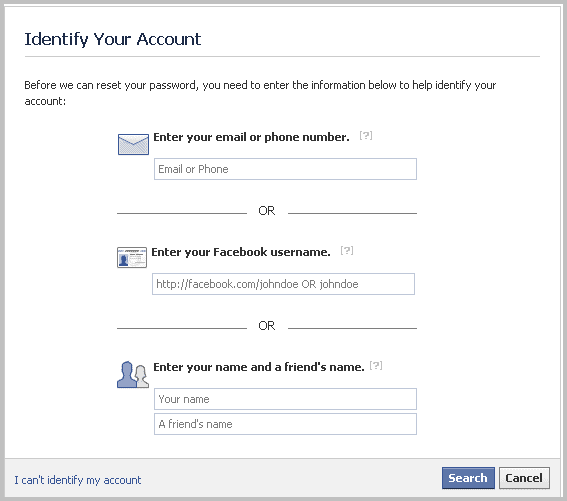
When you click on the attachment, you are taken to a Gmail login page on a new tab in the browser.
This page looks like Google's Gmail login page, and the only indication that something is wrong comes from the address field.
It does not begin with https://accounts.google.com/, but with data:text/html. Also, since the page is not HTTPS, you don't get a green or red indicator either. Those are the only indicators that something is wrong. If you copy and paste the URL, you will notice that it contains whitespace after the official Gmail URL, and then an obfuscated string.
The main issue that helps the attacker is that it happens that Gmail may ask you to sign in again to your account at times, and that the actual Gmail address is listed in the address bar as well.
If you just glance at it, you may see https:// accounts.google.com/, and think that everything is alright.
You should be save if you follow the basic rules when it comes to phishing, as one of them is that you have to check the address of the page at all times before you do anything on it.Â
In short, if the URL does not start with https:// it is definitely fake, at least in the case of Gmail and any modern service that supports https://.
I can see how even experienced users fall for that trap though, considering that the emails come from a legitimate contact and not some fake address.
It may also be easy enough to overlook the fact that the attached PDF is an embedded image instead. You may notice that something is wrong when the attachment takes you to another page.
The attackers try their best to hide the that fact, as they use the page title "you have been signed out" which users may focus on instead of the actual web address they are on.
Another thing that should let the alarm bells ring is that the page that opens asks for the user's email address and password. Google usually won't when that happens.
Accounts with two-factor authentication are better protected against these phishing attacks. It is however possible for attackers to request the two-factor authentication code from the user as well if they attack the account in real-time.
Google seems to consider adding a "not secure" tag to data: and blob: elements in the address bar, but nothing is set in stone yet.
Data is not entirely new when it comes to phishing. We reported about data being used for phishing attacks back in 2014, and that is probably not the first occasion it was used for that.
The attackers target Gmail currently, but nothing is stopping them from moving on to a different email provider.
Now You: Would you have fallen for the attack?




















i have seen this data/text page open up when torrenting,, always a blank page with this address beginning with data/text… glad i switched to protonmail for important mails, gmail/hotmail are just spam collectors these days
This extension is offered by Google (IMO should be built into Chrome):
Password Alert
offered by google.com
Password Alert helps protect against phishing attacks.
If you enter your Google Account password or Google for Work password into anywhere other than Google’s sign-in page, you’ll receive an alert, so you can quickly change your password if needed.
Password Alert also checks each page you visit to see if it’s impersonating Google’s sign-in page, and alerts you if so.
Thanks Martin for the heads up! It is more clever than many other phishing attempts so I fear many may fall for it.
This part of your article could use a clarification
“They contain what looks like an attachment, a PDF or spreadsheet for instance, something that may have been sent in the past already.”
It was an image with a hyperlink in the email html body made to look like the attachments field at the end of gmail emails. Famous science youtuber Tom Scott who almost fell for it has a good screenshot of the image here https://twitter.com/tomscott/status/812265182646927361
Some of the other ghacks commenters discuss if experienced users could fall for this or not. I think that is the wrong way to think about it. No user is perfect regardless how experienced. Things like stress, sleepiness, distraction and so on affect how alert we are. Everyone can slip up. We should help each other out to avoid phishing and not be too harsh on those who get caught by it.
One question I’d like to ask Google is how often there is legitimate use for data hyperlinks in gmail? Google should autodetect all such hyperlinks and at the very least embed a warning.
The most worrying part is that they can open up a new tab and load a fake login page just by clicking a PDF or Excel attachment from inside Gmail?! I would like to see detailed steps of how that works.
@Clairvaux: “I erase mails as soon as I have downloaded them”
The only consequence that you can be sure of when you delete data from a cloud service (which EVERY commercial email system always has been), is that YOU won’t have access to the data from then on.
That the data will actually be erased by the cloud service, immediately or later, is pure presumption.
No need to be aggressive like that, TimH. That’s more or less what I wrote. If you want to help, why don’t you suggest a way to keep one’s mail private ?
It’s called encryption. Been around for years. But the end-to-end email variety requires additional actions on the part of BOTH the sender and receiver for it to be effectively implemented.
I almost never connect to my Gmail accounts. I use Outlook on the desktop. Having an open connection to Google means you agree to being spied on. Also, it’s impossible that I run out of space in my Google accounts, because there’s nothing in them. I erase mails as soon as I have downloaded them. This also means (hopefully, with a certain degree of uncertainty, and given a certain delay) that Google cannot give my mails to the police, which is the way I prefer it to be.
Well outlook has many open areas where scammers will use your email to get information. Anything you give to Microsoft can also lead to opening your computer in another computer. This is 100x worse than losing a google account, you could lose your whole rights to use the computer.
Not sure what you mean by that. You do realise I was speaking of Microsoft Outlook desktop software, which is a mail client, and not of Microsoft Outlook.com webmail service ?
If one does “lose one’s rights to use one’s computer”, which nowadays happens mostly through ransomware, there’s a magic remedy : restore from the backup that (presumably) you have safely stored away in several copies.
Compared to that, reclaiming a hacked Google account is never guaranteed, and since the service is free, you should expect minimal help from Google. That holds true for any free mail service. Hence the importance of having a local copy of all your mails — and other data that you might have stored on Google, or on a similar service.
Glad I use Thunderbird email client. No signing in. Done automatically. Change passwords often too.
“I can see how even experienced users fall for that trap”
I can’t. You have to make two related mistakes: login from a link in an email, and not check the URL.
Exactly this. I’m not sure what Martin’s definition of tech savvy is, but I would be highly suspicious of logging into a link derived from an email attachment, and I always check the address bar when asked to log in to something.
I might call it elaborate (and simplistic at the same time), but not sophisticated–more of a misdirection perhaps.
One can also benefit from–in Gmail–checking the Details of last account activity once or twice a day (beginning and end of day) to see if there’s any unusual activity within the past 24 hours. Most users will get a notification from Google if something looks unusual, but what’s unusual for you make look usual to Google, esp. if you’re often mobile.