Why you shouldn't turn on Google Authenticator's cloud sync feature

Google Authenticator is a popular two-factor authentication app to create codes for authorization processes. Up until now, Google Authenticator did not sync codes across a customer's devices, which meant that customers had to install and set up these solutions manually on each device.
Google introduced support for syncing two-factor authentication codes via its Google Authenticator app this week. The new feature improved the usability for multi-device users of the app. Google customers could sync codes across iOS and Android devices using the feature.
While many users may have enabled the feature already, it is advised to keep it turned off for now. Here is why: the data, which contains highly sensitive information, is not end-to-end encrypted. Analysis of network traffic reveals that the data is not encrypted properly, and this means that Google and likely also anyone who gains access to the Google Account may gain access to the secrets.
The secret, in this case, is the seed that is used to generate the one-time codes. It is essential for two-factor authentication. In other words, anyone with access to the secret may create one-time codes for the linked service. Often, information about the linked service and an account name may also be present in the data.
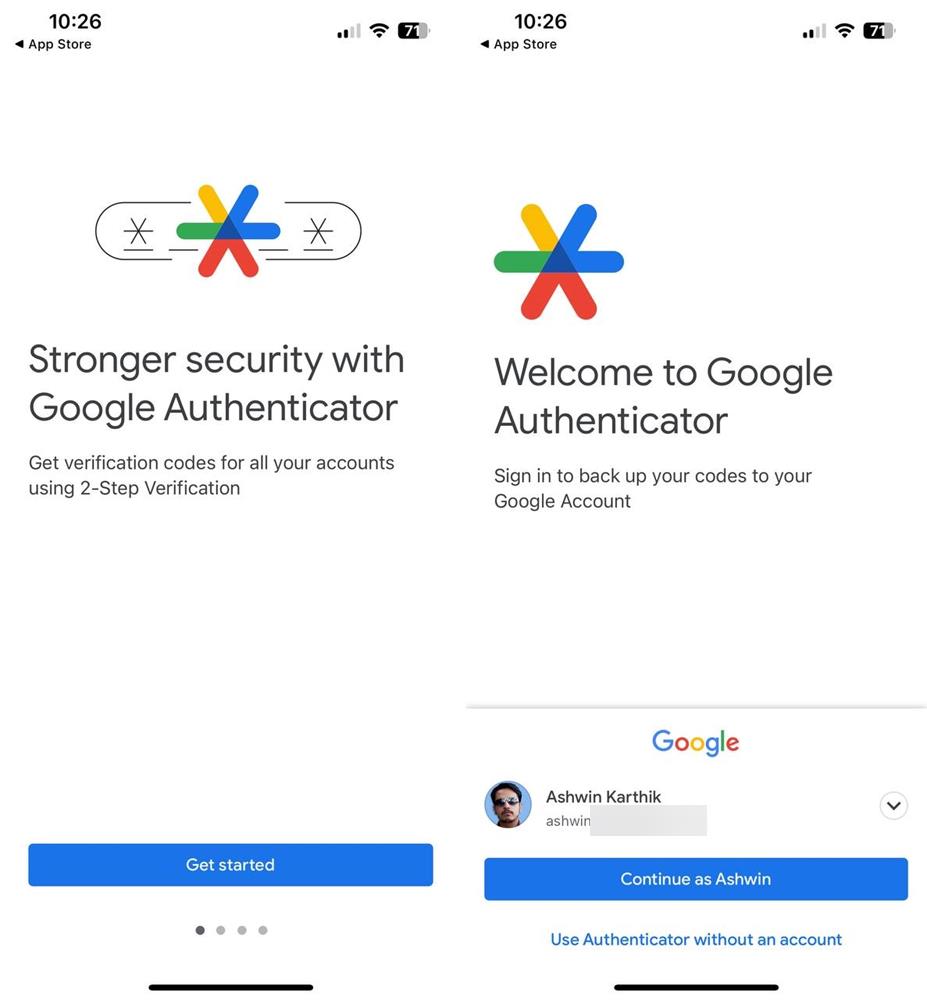
Mysk discovered the issue and made it public here. They recommend keeping the sync option disabled for the time being, at the expense of convenience, to keep the data secure.
They stated: "We analyzed the network traffic when the app syncs the secrets, and it turns out the traffic is not end-to-end encrypted. As shown in the screenshots, this means that Google can see the secrets, likely even while they’re stored on their servers. There is no option to add a passphrase to protect the secrets, to make them accessible only by the user."
Google might, at one time, introduce support for a passphrase that users may specify to protect the data when it is transferred to the company's cloud servers.
Another issue that may arise out of this is that Google might provide the information when requested to do so legally. With end-to-end encryption enabled, Google could not provide the requested data.
You can check out Ashwin's guide on the best Authenticator apps for Android and iOS here.



















How do I turn this feature off. I inadvertently pushed the cloud icon and now I can figure out how to turn it off and delete my secrets stored somewhere in a secret Google cache
“Stronger security with Google Authenticator” ahem
Microsoft Authenticator also syncs to the cloud. Does anyone have an idea if this issue affects it too?
I would be too glad if services moved to hardware form of authenticator like requiring a Yubikey or something similar but few services do that.
People furiously go on and on about Google invading their privacy, and then they give them all their passwords. /facepalm
> People furiously go on and on about Google invading their privacy, and then they give them all their passwords.
Good grief!
That’s a totally misguided bullshit!
Passwords are exposed because of the “unawareness” of the user.
Because many people are looking for “convenience and easy only.” Such people believe in Google. So it can be said that Google (is making users blind to the fact that) is the root of the problem.
Google’s proposed “Google Authenticator (2FA)” uses ClientID.
We are told not to worry because “data collected by Google will be anonymized,” but are we really not worried?
There is data that falls under the category of personal information (‘Unique Identifier’ or ‘Persistent Identifier’) as defined in the CCPA. One of them is the ClientID.
https://www.cookiebot.com/en/google-analytics-ccpa/
ClientID is a unique ID stored in a cookie and used by Google to identify individual users.
Google uses authentication methods to collect and profiling “unique personal information” and must take these big tech speculations into account.
Some browsers are entirely designed to collect your data. If you use a big tech company’s web browser, ask yourself the following question: what is their business model? This comic is a fun (well, not fun, but you get it) read on the subject. As the comic artist and digital rights activist Leah Elliot puts it: “Chrome collects your IP address, the words you search for, the videos you watch, the pages you visit, the ads you click, your purchase activity, the network of people you’re in touch with, and much more. All facets of your life are scrupulously collected, analyzed and assembled into an intimate profile: a data text that aims to describe what makes you you.”
And there are several other browsers today that limit things like third-party-based tracking. However, as a result of this, advertisers and others interested in capitalizing on your behavioral data have invested in other tactics for tracking users around the web.
with browsers blocking third-party resources and cookies are under legal attack, advertisers and other data gatherers are looking for other solutions.
Above citation source:
https://mullvad.net/en/browser/things-to-look-for-when-choosing-a-browser
always create an encrypted backup of your sensitive info and passwords.
Dont trust google so much on this.
Folks use a dedicated password manager and save your 2FA tokens there. Always maintain an encrypted backup of that data and keep it safe or upload it – it is encrypted FFS.
For those who use only Google dedicated solutions.
Just use Aegis or any good F-Droid based authenticator. Yes local storage for all the backups as you say.
The cloud is a botnet.
Wow, this is kind of shocking, and seems really irresponsible of Google. I’m certainly glad that I don’t use this app.