InAppBrowser reveals if TikTok, Instagram and other apps with browsers inject their JavaScript
Earlier this month it was revealed that popular mobile applications with integrated browsers injected custom JavaScript into visited sites. Facebook, Instagram and TikTok all use code injection techniques to virtually track anything that app users do on any website that is opened in the in-app browser.
The companies that own the offending applications benefit from this in several ways. First, because everything happens entirely behind the scenes, without most users suspecting any of that. Second, because the in-app browsers do not support content blockers or reveal privacy information when used.
Most companies use in-app browsers and code injections for tracking and monetization purposes, but some may use code to monitor all user activity, including all keystrokes.
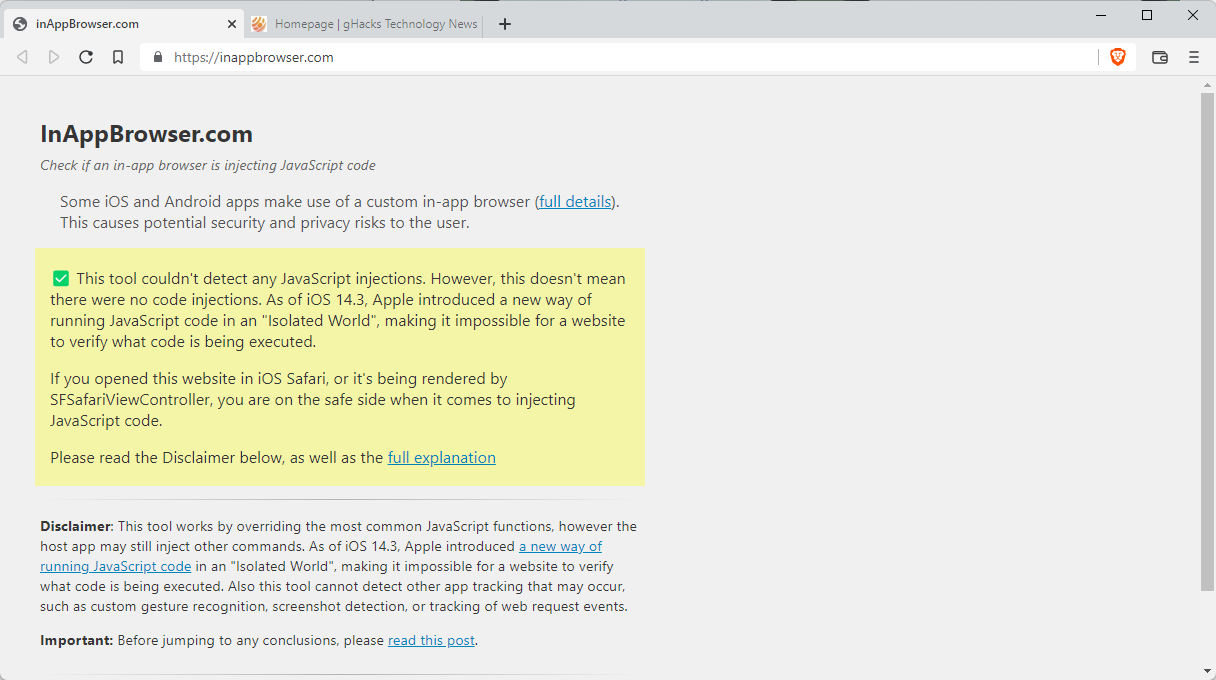
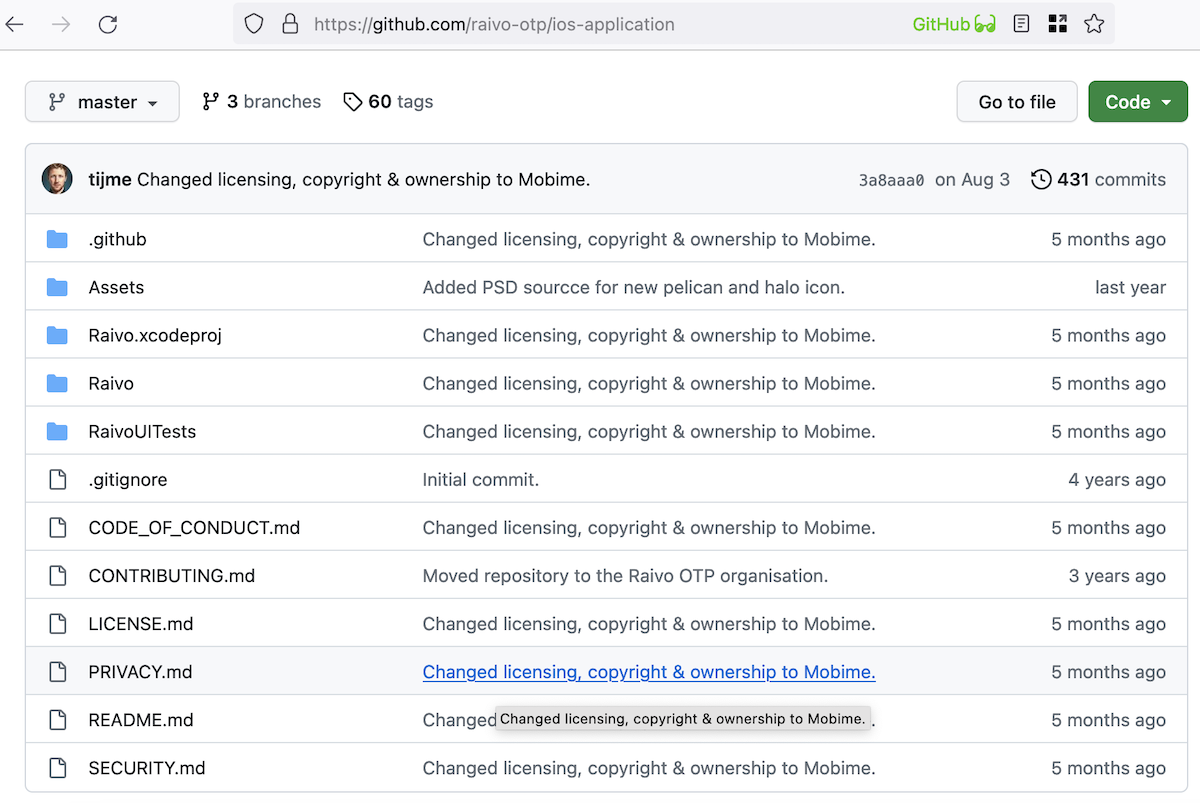
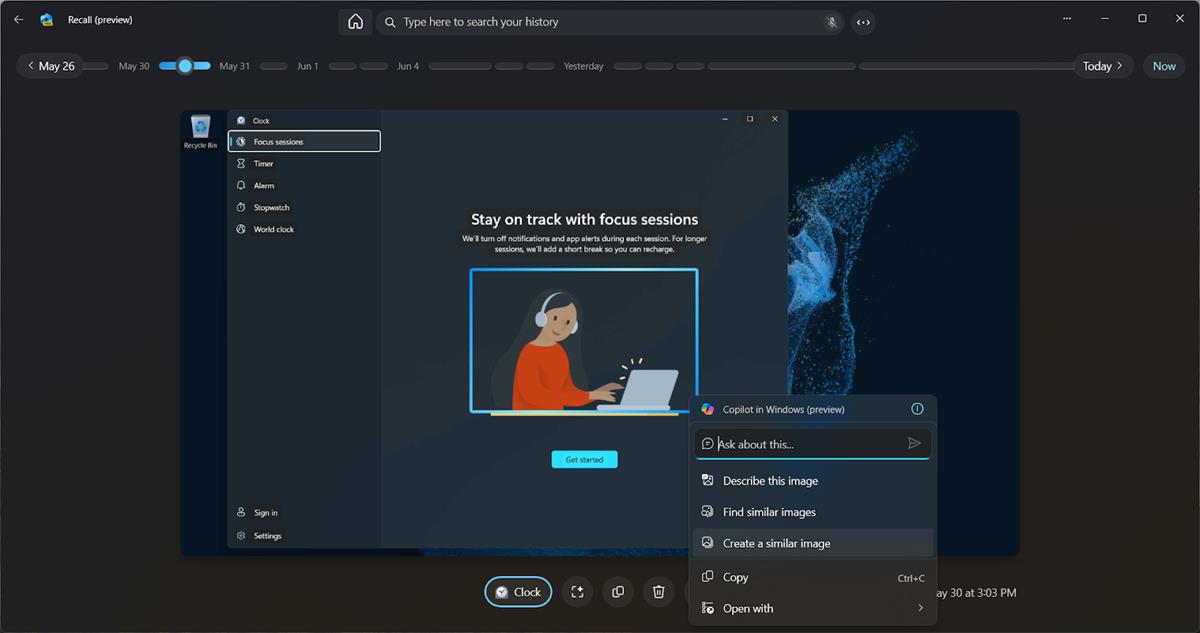
Felix Krause created the website InAppBrowser, which is designed to reveal to the user if an in-app browser is injecting code.
Here is how it works:
- Open the application that you want to analyze.
- Use share functionality inside the application to get the link https://InAppBrowser.com into the app. You may DM a contact or post publicly.
- Open the link that has just been shared or posted.
- Check the report that is displayed.
The website reveals if it detected JavaScript code injections and how it rates these injections. For TikTok, the website reveals the following:
- Adds CSS code, allows app to customize appearance of website.
- Monitors all taps happening on websites, including taps on all buttons & links.
- Monitors all keyboard inputs on websites.
- Gets the website title.
- Gets information about an element based on coordinates, which can be used to track which elements the user clicks on.
Instagram, another popular application, injects JavaScript code as well. While it does not monitor keyboard inputs, it does monitor all JavaScript messages and all text selections, and injects external JavaScript code.
All detected JavaScript commands are listed as well for deeper inspection.
You can check out the blog post, which offers additional details.
Krause notes that the site may not detect all code injections or all executed JavaScript commands. Also, it does not detect native code, which apps may use as well.
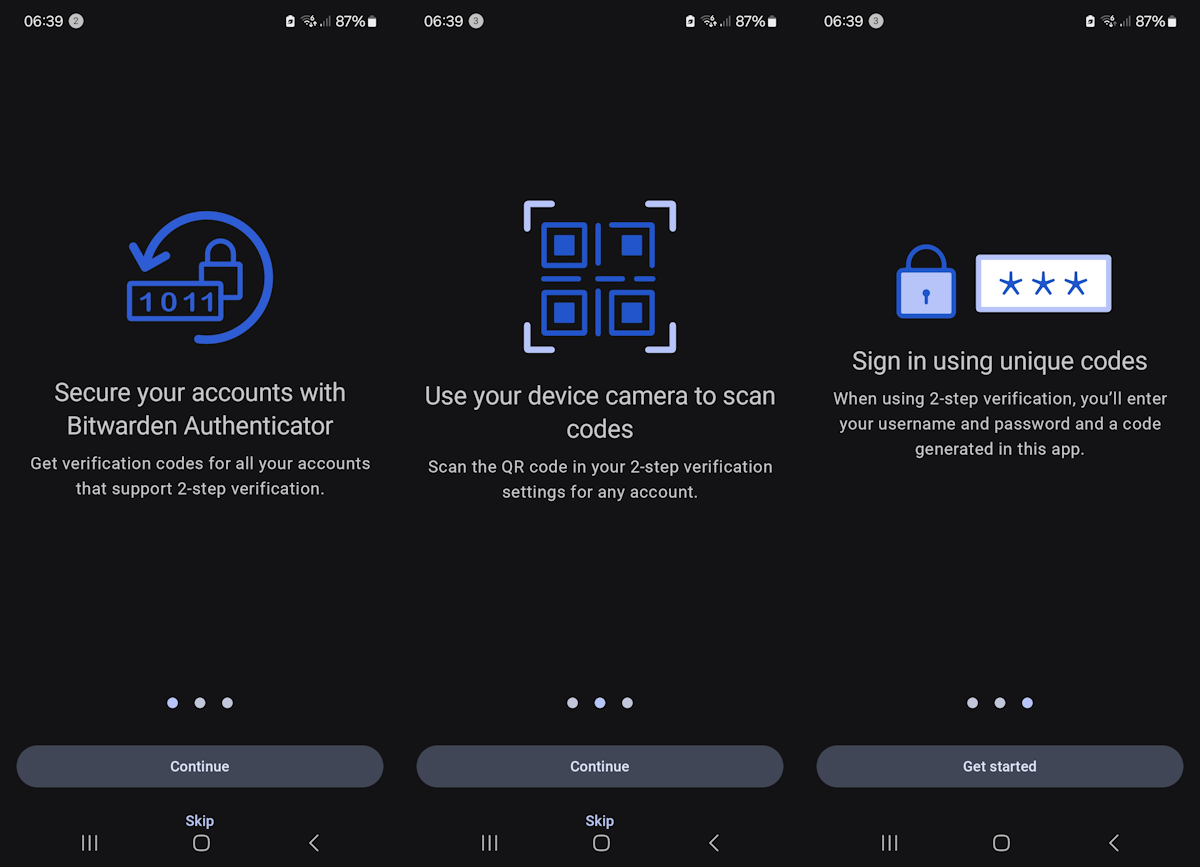
Protection against invasive in-browser apps
Mobile app users have just a few options. Besides the obvious, removing the app from the device, they may be able to redirect links to other browsers on the device. Not all apps support that though. The use of DNS-based content blockers may not help as much either, at least not against the potential reading of keystrokes or other activities unrelated to the display of ads or tracking.
Now You: Do you use apps with in-app browsers?














I have a smartphone which is six years old already. Apart from phone calls, I’ve switched to using Signal (open source and recommended by Edward Snowden) for chats and video calls these days.
It’s not so much fun as the Line app with its unique animated stickers, but Line has become much too bloated now and often fails to relay even simple text messages let alone images.
Amazon has been bugging me just lately with warnings that someone just logged into my account from a certain IP address which later turned out to be the IP for my Android phone. But I never use it to browse their site with and only use my Windows laptop for anything financial.
Also the phone is on a different network than the one I use for my laptop. Don’t know what to make of that, but I’m forced to change my 140-bits password every time it happens.
Do you use apps with in-app browsers?
No, I have never used in-app browsers specifically because I have always thought the main app they are from can see everything you do in them. I thought this was common knowledge already.
Otherwise I only use the Samsung web browser. I also highly limit installed apps to only those absolutely necessary (same with my computers) and never install any social media ones as I consider them spyware in nature.
As to those eschewing smartphones, you are throwing out the baby with the bathwater. A smartphone is just a tool and like any tool can have many great uses as well as many bad ones if not used properly or responsibly.
Other than the default apps that came with the iPhone I use no 3’rd party apps at all because of this kind of things that they do…even the default iphone apps I have removed off my phone.
I replaced all my apps with open-source ones. My bank app is the only thing that’s not.
Only a simple mobile for phone and sms exclusively. I do not intend to ever buy a smartphone. Moreover a wide screen with performant audio is in no way comparable to a few square inches and lousy sound. I dislike the very concept of 24/7 connected. At home the PC, elsewhere my eyes and ears, plus the mobile for whatever plain phone call. Smartphones are the ultimate spying vector, at least for most of us. Not to mention the myriad of connected devices, GPS to start with. We’ve managed for years to find our way with paper maps so don’t tell me that the average planetary IQ is lowering in such a way hat kids need a calculator to add & multiply and adults a GPS to know which way to go. Carpe diem : enjoy the planet and forget filming it.
@Tom Hawack,
+ 1. It is as if you are reading my mind.
+ 1. It is as if you are reading my mind.
Sadly, kids these days can’t even add with the aid of a calculator, let alone without one.
Where do you draw the line? Do you calculate logarithms in your brain? There are enough smart kids these days and you give them no credit. Just because the bad apples are all influencers on youtube and tiktok, the nerds, geeks and freaks never vanished.
@Frankel, I think you weigh a civilization within the widest spectrum, not by the thinnest, so-called elite be it in terms of intelligence, education, social belongings. Of course you’ll always have smart kids, geeks and freaks of all ages. But the average, that of intelligence, education is, IMO, on a gliding path towards lower aptitudes. An interesting article :
“Researchers find IQ scores dropping since the 1970s”
[https://medicalxpress.com/news/2018-06-iq-scores-1970s.amp]
[https://medicalxpress.com/pdf448004095.pdf]
Generally speaking comfort doesn’t help brains, but searching for, inventing comfort does. This leads to an increasing hiatus between those who invent and those who use. I’ll admit this has always been but perhaps is the process empowered in consumerist societies, which I appreciate myself given consumerism become not a god.
But you are missing out there: Threema and Signal are encrypted. Don’t hand the government your unencrypted SMS. No matter how harmless their contents are. They got no business reading these.
[https://www.messenger-matrix.de/messenger-matrix-en.html]
Addendum:
Besides it is super easy to degoogle with LineageOS and GrapheneOS.
@Tachy & Tom:
Yep, me too. I use an LG flip phone for calls & SMS. That’s pretty much it. Internet usage is totally at home w/ three monitors that allow me to spread things out so I don’t loose track of what I’m doing.
A decent GPS can show things that maps do not eg traffic, the neatest filling station etc.
They are far better than regular maps.
Likewise a calculator makes things far easier.
Use the best tools for the job, after all that’s why you have a big screen.
Easiness is a brain-killer. I think it’s all a problematic of pertinence adequacy. Use tools of comfort occasionally, when they truly offer a quick answer to what would be impossible and/or far too long to perform ourselves, though impossibility prevails IMO on quickness. Quickness is often a choice, not always though; impossibility is straightforward : extract a square root is possible with a pen & paper, though very few have ever been able to calculate that without a calculator, even less when it comes to logarithms. But the problem with comfort is that we naturally tend to use its dedicated tools systematically. As for maps, that’ll be traffic, filling stations polluted with ads and the closest MacDo, not to mention that a plain radio can deliver local traffic and that filling stations (except electrical ones) are so frequent that you really must be absent-minded to not correlate anticipation and stations passing by your trip… what I mean is this : we can perform by ourselves the most part of what smartphones supply — most, not all of — and that we could consider using dedicated tools less systematically. And of course, no tracking :=)
Last-minute :
Data Sharing Espionage: A Fraud DiscussionWebinar.
[https://www.govinfosecurity.com/webinars/data-sharing-espionage-fraud-discussion-w-4206]
Avoid smartphones.
Brave injects scripts and code into web content
It’s not just in-app browsers that need to die, but the vast majority of “apps” too.
They should be utilising the mobile web and concentrating on making the mobile web experience good, instead of duping people into downloading an entire app for each website, which wastes storage space on the device and also wastes bandwidth with all these apps needing to update all the time. Not to mention these apps deprive people of features they are used to in their default browser like translation features, etc..
Who forces you to use them? I use a decade old FLOSS RSS reader app and it gives me all the news without the JS
I’m a wierdo, I use my phone to make phone calls.
(really, you can still “talk” to poeple in real time with these devices)
I use a PC to access websites.
PS Ok ok, I text and navigate too but phones are horrible for web browsing, much too slow.