HelloTalk app reportedly installed a malicious app called HT Coin on Android devices
HelloTalk is a popular community-driven language learning app that is available on the Google Play Store. It has over 10 Million downloads. A couple of days ago, a reddit user claimed that a notification displayed by the app downloads a malware.
To be precise, it downloads a file called HTCoin.APK. This file seems to have been triggered as a malicious one. Interestingly, the HT Coin app is not available on the Play Store, which means HelloTalk downloaded it via a direct link from an unknown server.
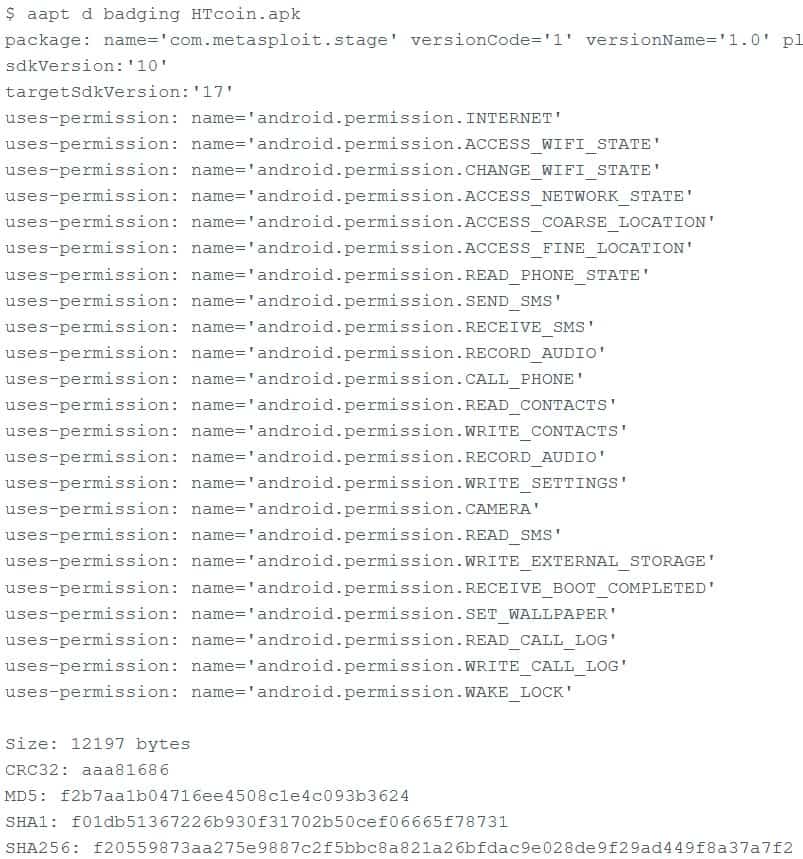
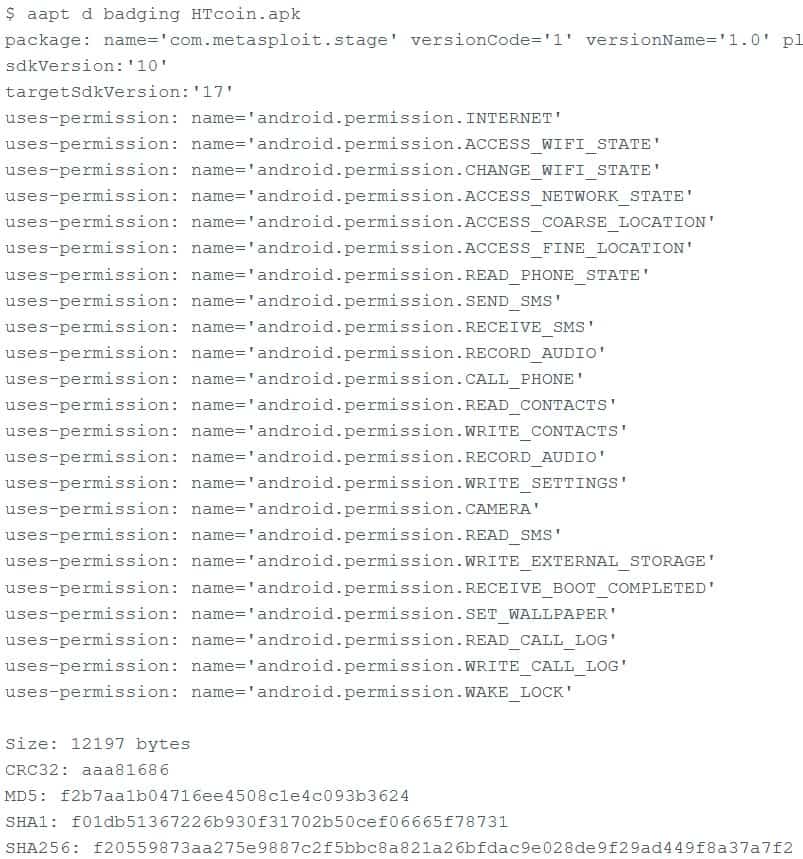
The redditor shared some details about the app in question, and it appears to have requested several unwanted permissions. More importantly, the app seems to have been based on Metasploit. For those unaware, Metasploit in itself is not a malware, it is a cybersecurity framework used for testing networks, especially penetration testing. While it can be a handy tool for white hat hackers, the open source framework can also be misused for exploiting code, and injecting malware.
So, it is not exactly surprising if something that contains Metasploit, is detected as malicious. But the real question is, why does the HT Coin app use it? And why does a language learning app need to side-load a different app in the first place?
This also leads to the question, what is HT Coin? To understand more about it, I installed the HelloTalk app and set it up with a temporary email address in the Bluestacks emulator. The Me section in the app has an option for an in-app purchase for virtual currency by the name, HT Coin. Tapping on the option allows you to purchase the IAP, and the payment options for buying the HT Coins are WeChat and Alipay, both of which are popular payment platforms based in China.
HelloTalk displayed ads occasionally, including full screen ads and gender-targeted ads. But I did not get the HT Coin notification while testing the app, so I couldn't tell for certain whether the HT Coin app is malicious or if it even exists.
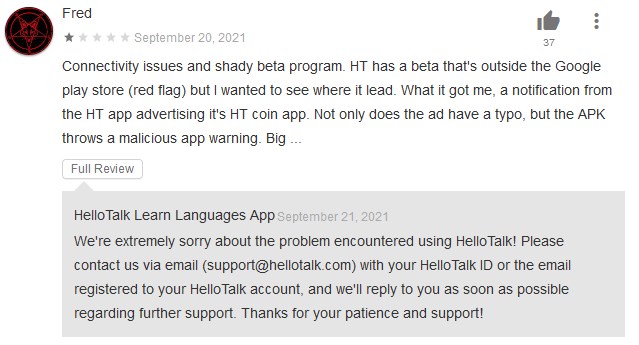
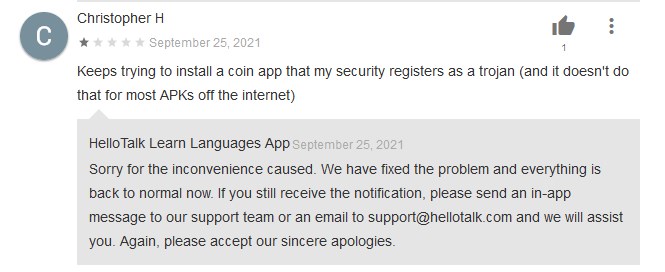
However, looking at some reviews on the Google Play Store, there are a few users who have reported that HelloTalk installs the HT Coin app, and that their phone detected it as malware.
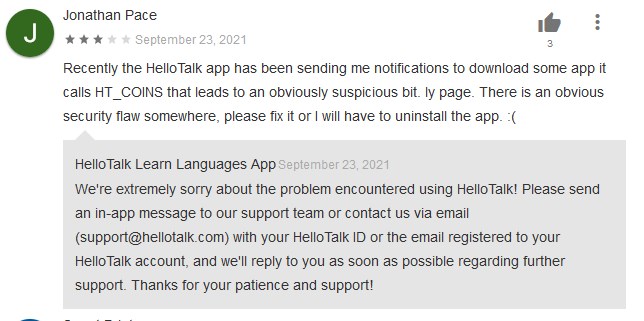
The developer replied to one of these reviews, stating that the issue has been fixed, which basically confirms that the issue was real. This could explain why I never got the notification. The app was updated since the 24th of September, while the post on reddit was dated the 25th. So, it's probably a server-side change done by HelloTalk's team that seems to have "fixed the issue".
The app could now be devoid of malware, but the fact that it downloaded an APK outside the Google Play Store is in violation of the terms and services. It's been over 2 days since the user shared the news on Reddit (and reported it to Google), but the HelloTalk app is still available on the Play Store. Then again, this is not the first instance of an app turning out to be malicious. Google should review apps more strictly to ensure the security of its users, but it does not seem to be a priority for the company.
Do you use HelloTalk? Have you had a similar experience with other apps, share your comments with us.





















I’m a Hellotalk user on Android and I’ve never seen any side app called HT coin or something. I admit I didn’t use Hellotalk a lot in September. Maybe the “fix” patch was already in place when I started using it again later than that time? Also I’m not aware of any of their internal currency as if you want to pay for their membership, you simply pay directly without buying their “tokens” or anything. Perhaps they wanna develop their token system to make more money out of it in the future?
What’s with the posting delay here now?
It hardly encourages reader participation if the comment you just posted won’t be read by anyone for five hours. By then everyone has moved to other topics.
Smooth move gHacks.
True. It’s strange that the posting delay exists. It can only make people think all comments left are for censorship later.
“It’s been over 2 days since the user shared the news on Reddit (and reported it to Google), but the HelloTalk app is still available on the Play Store.”
Google itself is the number one security threat for most of Google product users and it’s already funny that they market themselves as “ok we’re evil but at least you’ll have security with us [against attackers who are not us and that we did not approve either]”.
Of course even that is a myth. Sure those companies have plenty of resources that *could* be used for that, but it doesn’t mean that it would be profitable for them to do it. That’s why with software developed by lower resources but ethical organizations not only we’re less exposed to the number one security problem (Google itself and similar), but in addition we’re safer against such secondary security threats, contrary to what Google pretends.
The only way we’re going to pull Googles teeth is if white hat hackers get really serious about getting reliable, affordable and easy to obtain (AOSP) de-googled phones to a critical mass of users. Enough to support alternative infrastructure outside of Google services that app developers would be sure to include in their to-do list of where to post their apps.
This would help both end users and developers as it would remove Google’s monopoly stranglehold on them all.
This wouldn’t even be dream on Apple’s offerings because they own and control all of their products in perpetuity. iGulag phones.