Change your password day needs a counterpart
February 1 is change your password day; while not official, many tech sites advertise the day to their readers. Users are asked to change passwords on that day to improve security.
While there are certainly times where changing passwords makes sense, e.g. after a breach of an online service, a successful virus attack, accidental sharing, or to increase the strength of a password, generally stating that one should change all passwords on that day never made a lot of sense.
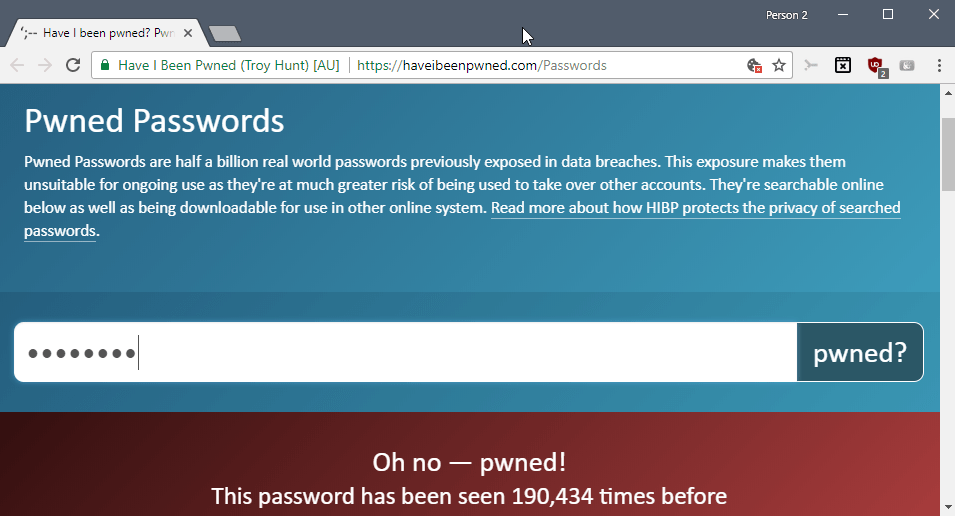
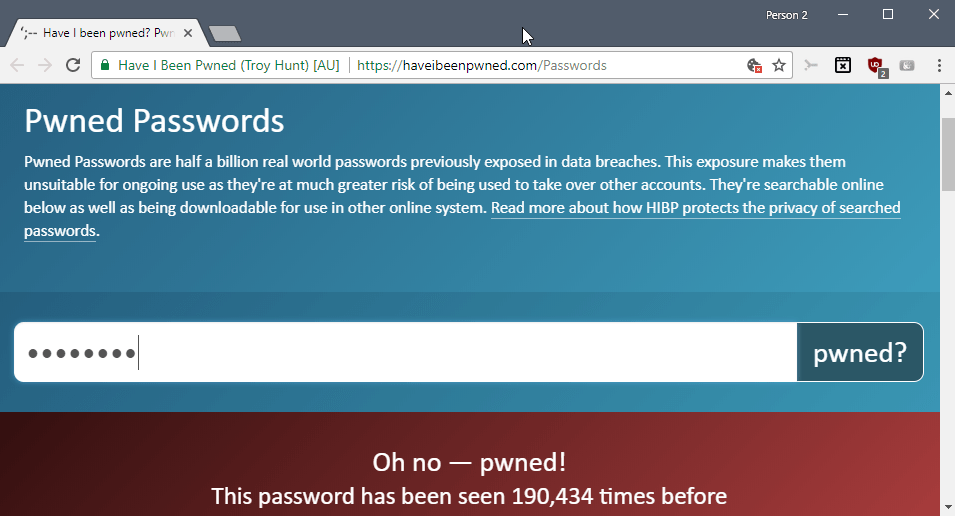
I'd prefer the day to be renamed to "check your passwords day" instead. Users could test their passwords against the Have I Been Pwned database (locally), and change passwords that were leaked to the Internet.
Users could also check the strength of passwords and change passwords that are considered weak by the strength checking algorithms, or start using a password manager if permitted in the environment.
Two-factor authentication and other advanced security options, if available, are also worth considering.
Check your server security day
I propose a counterpart to change your password day: check your server security day (loosely based on Jürgen Schmidt's article on Heise), my own On Password Security article from 2012, and password security: what users know and what they do. While it is certainly the case that brute force attacks or targeted attacks may steal user credentials, one of the biggest threats comes from company servers that get hacked.
Whether the hack is successful because of social engineering, improperly configured servers, unpatched security vulnerabilities, out of date libraries or components, or 0-day vulnerabilities is irrelevant from a user's perspective.
Billions of password sets are available freely on the Internet. These sets, Have I Been Pwned lists 6.4 billion pwned accounts alone from 340 sites, are just the tip of the iceberg. They come from successful breaches and are either published right away on the Net, offered for sale, or used without them ever being leaked publicly.
A companies reputation suffers if they are attacked successfully but it appears that most go back to "business as usual" pretty quickly after breaches.
Companies should use the "check your server security day" to improve security. It is probably not enough to do this once a year but the day could be used to run thorough tests and to improve security, e.g. by implementing new forms of security or improve existing ones.
Even if you, as a user of a service, select the strongest password imaginable, you may still find it fall in the hands of criminals that dump password databases.
All I'm trying to say is that companies need to take responsibility. It is not enough to reset account passwords after a breach and be done with the whole situation; companies need to improve security proactively and check server security regularly to block certain attack vectors outright.
Now You: Should companies better secure their servers?


















Password managers have come a long way in helping secure passwords (and make login a lot faster and easier). However when I thought of changing all my passwords… this left me wondering if there’s a tool to modify passwords all at once?
This is a great article, I also agree the companies should be more responsible. As for password generator programs I’m not to sure about them. I have had a couple different ones. After I stop using them all my passwords went back to what the where before using them. I would of thought that after using the programs I would of had to change them all. If the programs change them all while I used the programs how did they go back to what they where before using them.I just uninstalled the programs and passwords went back as they where as if the programs had never change them. I am going to go to the two-factor authorization. Anthony Craig Hutzler
Allow me to share this quote found on another blog:
Naturally it is only at the front-end where security is beefed up.
Your back-end penetrability is their business model. — andreas5
I agree, much better advice. If the password/hash has not been leaked, it makes very little sense changing it. Asking the user to just change the password for the sake of doing so is not a great advice at all. All it does is inconvenience the user for no reason at all
“Now You: Should companies better secure their servers ?”
No. Okay, just joking…
You’re absolutely right that “change your password day” is an obsolete meme. Unless you have a single one for all sites, and then it still should not be “change your password day”, but “password manager day”.
I’m not aware of stats for password manager usage, but my feeling is only a minority use them. That’s one of the simplest, most effective and cheapest decisions one can take to dramatically increase one’s security (if not downright free).
Companies deserve to be relentlessly hounded and shamed on Twitter by experts such as Troy Hunt (or you ?). Troy regularly exposes the preposterous security faults of many a well-known company, which a child would know to avoid.
Sometimes, it seems the bigger the brand, the most glaring the security oversights.
Regarding my credentials policy and namely passwords,
– Never shared, one password of its own for each login;
– By default, 32 characters including custom (12 is a minimum I think).
Regarding companies,
– It’s improving but still too many sites don’t impose a minimum of password complexity;
– Still too many (but lesser) sites not offering secure (https) login environment;
Regarding users,
– I wonder how it is possible that some of us still use kindergarten passwords and moreover re-use the same from one place to another after the amount of caution published here and elsewhere. Stunning. Browsers nowadays offer login management, external managers are numerous but some users behave as if one basic 4-8 character password never saved anywhere else than in their brains and repeated everywhere was a more secure approach. If so : change your password; otherwise check them. Nevertheless I still consider changing my specific 32-character passwords one in a while and regularly for sites limiting the password length (yeps, I even met places refusing passwords longer than 8 characters, amazing…).
@Tom Hawack: “still too many sites don’t impose a minimum of password complexity;”
Whether or not imposing this is a beneficial thing is a matter of a great deal of controversy. Enforcing complex passwords on people makes an awful lot of them choose vulnerable passwords that still meet the minimum complexity settings. “Oh, ‘password’ doesn’t work? Then I’ll make it ‘P4ssw0rd12345678!'”
The question is, which approach results in a larger number of strong passwords? There is little evidence to base any conclusions on at this point.
The real problem is how to get people to be less lazy about their passwords. No amount of mandated complexity or enforced password changes can cure that problem. Personally, I think that encouraging the use of password managers (and letting them generate the passwords) seems like the most fruitful approach — but then we’ll have to fight the laziness of people when it comes to backing up their passwords.
I think there’s a simple solution to that. A sizeable amount of sites have shown that it’s quite easy to embed a password strength manager, rejecting bad passwords at sign-up.
Sites need only to add a testing module that checks against a database of such bad passwords — there are plenty. They could also include a test against Troy Hunt’s database of hacked identifiers haveibeenpwned. Problem solved.
For the moment, they just detect that you have enough characters, and probably a mixture of letters, digits and special characters. Passwords such as P4ssw0rd12345678! pass that test, but they are to be found in plenty of databases of most-hacked passwords. Just exclude them at the start.
@Clairvaux:
I think that you’re underestimating the ingenuity that people have when it comes to thinking up unique and weak passwords that pass password strength algorithms.
Your approach has been tested many times before, and — like almost all such solutions — it works for a while, but then people learn how to work around it.
This is an extremely difficult problem (I mean authentication in general, not passwords specifically) to solve, and so far no effective solutions that are tolerable by normal people have been developed.
2FA is a reasonable attempt, but then it brings a whole host of other problems, such as privacy.
@ John Fenderson
I don’t underestimate anything. You didn’t understand my point. It does not matter that bad passwords are not defeated by algorithms. I don’t propose an algorithm, I propose a database. On top of the algorithm.
You know those nice articles about how stupid people are ? The worst passwords lists that are the basis for such articles come from hacks. Just put those lists on your site (they have thousands of items), and check proposed passwords preventively against them.
Go one step further, and take Troy’s Hunt API, or whatever those things are called, and check the proposed password against millions which are already in the wild.
Is there still a possibility that an easy to guess password has not been hacked yet, and it will be allowed, then hacked ? Of course there is. Of course it’s possible you won’t be able to read this answer because you already died in a car accident. Of course there’s no 100% warranty of nothing bad happening in life. Quite the reverse, in fact.
However, if a majority of big sites adopted my suggestion, there would be a dramatic increase in non-hackability as far as password strength is concerned. That’s only one part of the equation.
Anyone, without even being a security expert, can realise many sites, even of big reputable organisations, are dramatically reckless when it come to authentification. When a security expert such as Troy Hunt investigates this professionally, the results are even worse.
We’re talking about progress here, not perfection. That’s something you can’t have.