How to enable Windows Defender's potentially unwanted programs protection
One of the latest additions to Windows Defender Antivirus' arsenal of protection tools blocks potentially unwanted programs, short PUPs, from landing on the system or being installed on Windows PCs.
Note: Potentially Unwanted Programs (PUPs) and Potentially Unwanted Applications (PUAs) refer to the same type of potentially unwanted software.
Microsoft improved the defensive capabilities of the built-in antivirus and security tool Windows Defender significantly for Windows 10.
The company added features such as Windows Defender System Guard and Application Guard, Network protection, Controlled Folder Access, or Exploit protection in recent years to the tool. Microsoft even published Windows Defender Browser Protection for Google Chrome.
Some features are reserved for Enterprise editions of Windows 10 but some are also available in Home editions.
Windows Defender's PUP protection
Windows Defender may block potentially unwanted programs from being downloaded or installed on Windows 10 systems. The feature is not enabled by default and can only be enabled using PowerShell, InTune, or System Center.
Potentially Unwanted Programs are not classified as malware usually; these programs may come as extra installation offers during software installations on a Windows PC or as standalone programs that don't provide a lot of value, if at all.
Microsoft gives the following examples of typical PUA (Potentially Unwanted Applications):
- Various types of software bundling
- Ad-injection into web browsers
- Driver and registry optimizers that detect issues, request payment to fix the errors, but remain on the endpoint and make no changes or optimizations (also known as "rogue antivirus" programs)
Windows Defender Antivirus does not block potentially unwanted programs by default. You can check the protection on Microsoft's Demo Scenario site to test a system's protection against various threats.
Just click on the link under Scenario to test the protection. This should work with Windows Defender and other antivirus software installed provided that they are configured to block PUPs.
The protection works in the following cases:
- The file is downloaded in a browser.
- The file is in a folder with "downloads" or "temp" in the path.
- The file is on the user's Desktop.
- The file is not under %programfiles%, %appdata%, or %windows%, and does not meet any of the conditions above.
Windows Defender Antivirus places files identified as PUP in the Quarantine. Users are informed about the identification of PUPs on the system similar to how they are informed about other threats detected by Windows Defender.
Admins and users can check the Windows Event Viewer for event ID 1160 as potentially unwanted program events are recorded under it.
Enable the potentially unwanted programs protection in Windows Defender
Note that the following instructions apply to Windows 10 only and that you need elevated rights to make the change.
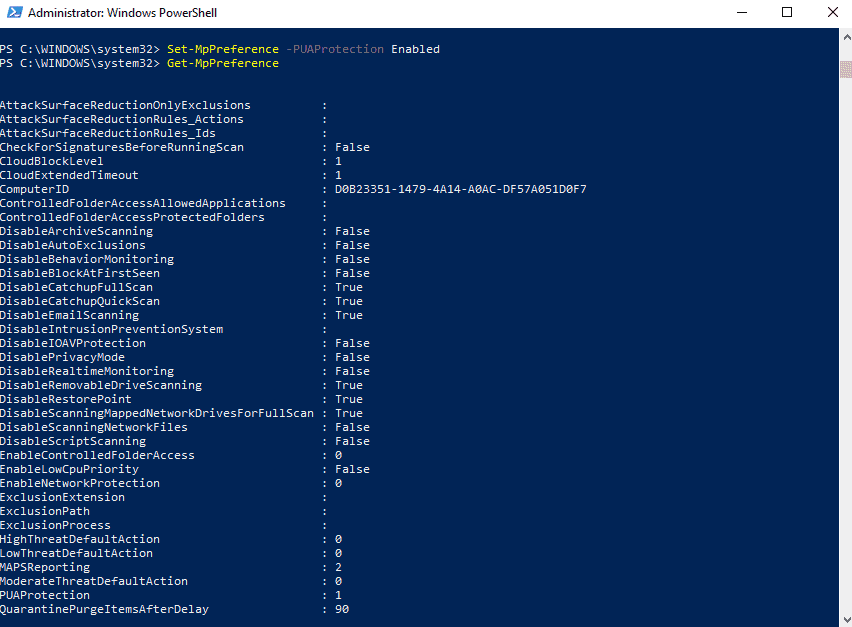
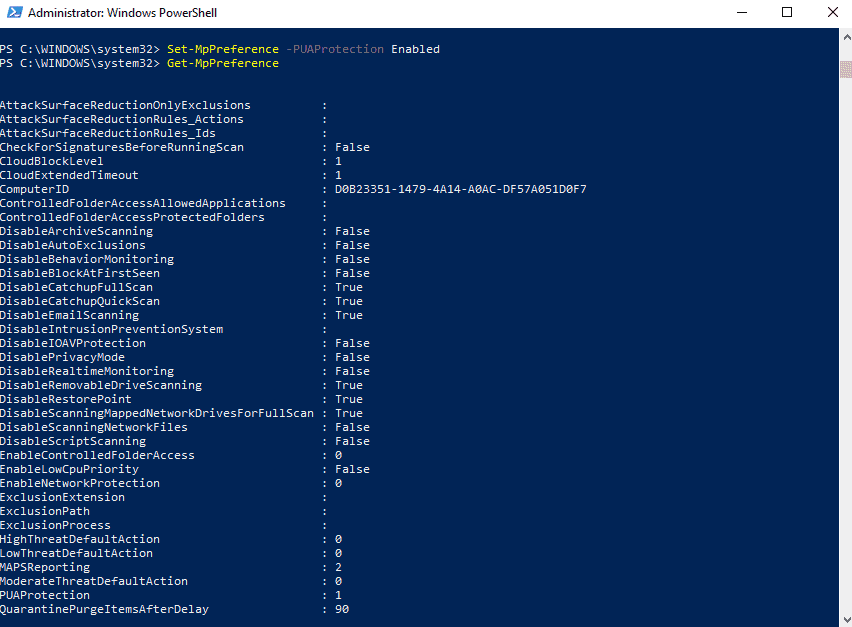
- Open Windows PowerShell with Windows-X and the selection of Windows PowerShell (Admin) from the context menu.
- If you don't see Windows PowerShell (Admin) listed there do the following instead: open Start, type Windows PowerShell, right-click on the result, and select "run as administrator".
- Confirm the UAC prompt that is displayed.
- The console that opens should being with "Administrator".
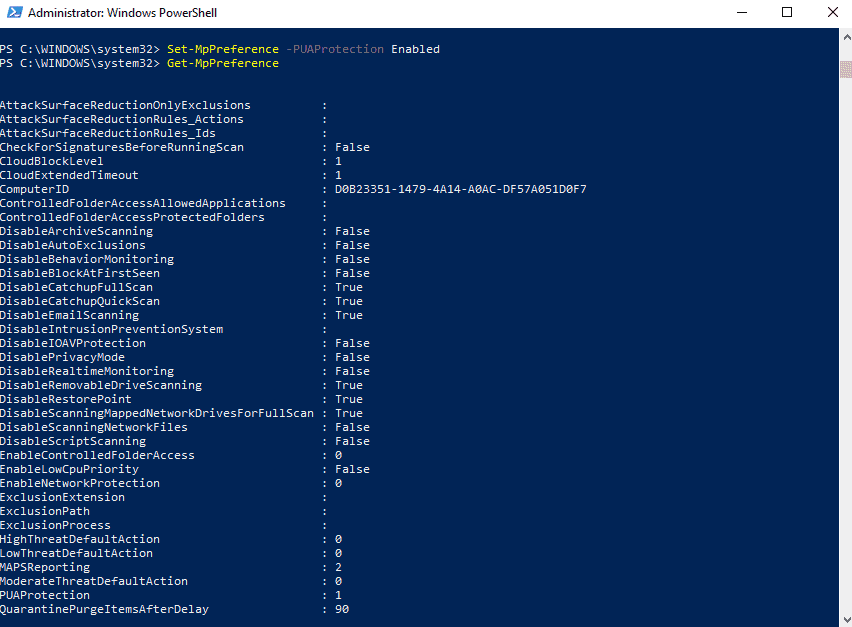
- Type Set-MpPreference -PUAProtection Enabled and hit the Return-key.
Nothing is returned when you run the command. You can run the command Get-MpPreference to check the status of preferences of Windows Defender Antivirus. Find PUAProtection and make sure it is set to 1 (which means that it is enabled).
Tip: You can disable the protection again at a later point in time by running the command Set-MpPreference -PUAProtection Disabled. It is furthermore possible to set the feature to audit mode. Audit mode records events but won't interfere (read block) potentially unwanted programs. To set audit mode run MpPreference -PUAProtection AuditMode.
I recommend that you run the test scenario that Microsoft published to the demo site linked above to make sure the protection is enabled correctly.
Admins who work with Microsoft Intune or System Center Configuration Manager find instructions on enabling the Potentially Unwanted Applications protection of Windows Defender Antivirus on Microsoft's Doc website.
Enable Reputation-based protection in the Settings
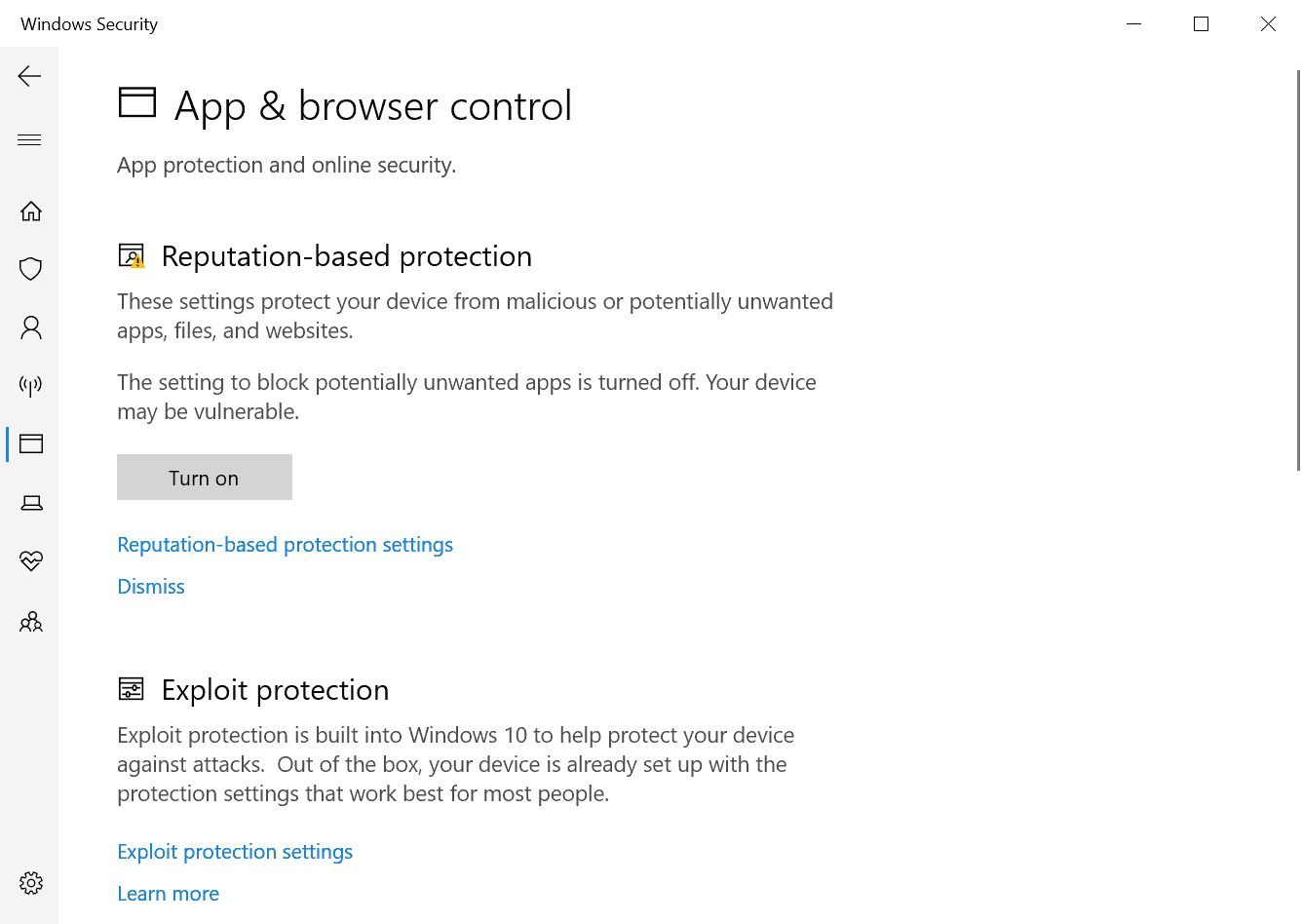
You can enable the protection against potentially unwanted programs in the Settings as well. Here is how that is done:
- Select Start > Settings, or use the keyboard shortcut Windows-I to open the Settings.
- Go to Update & Security.
- Select Windows Security.
- Activate the button Open Windows Security.
- Select App & Browser Control.
- Hit the Turn On button to enable the protection.
Whitelist blocked PUA applications
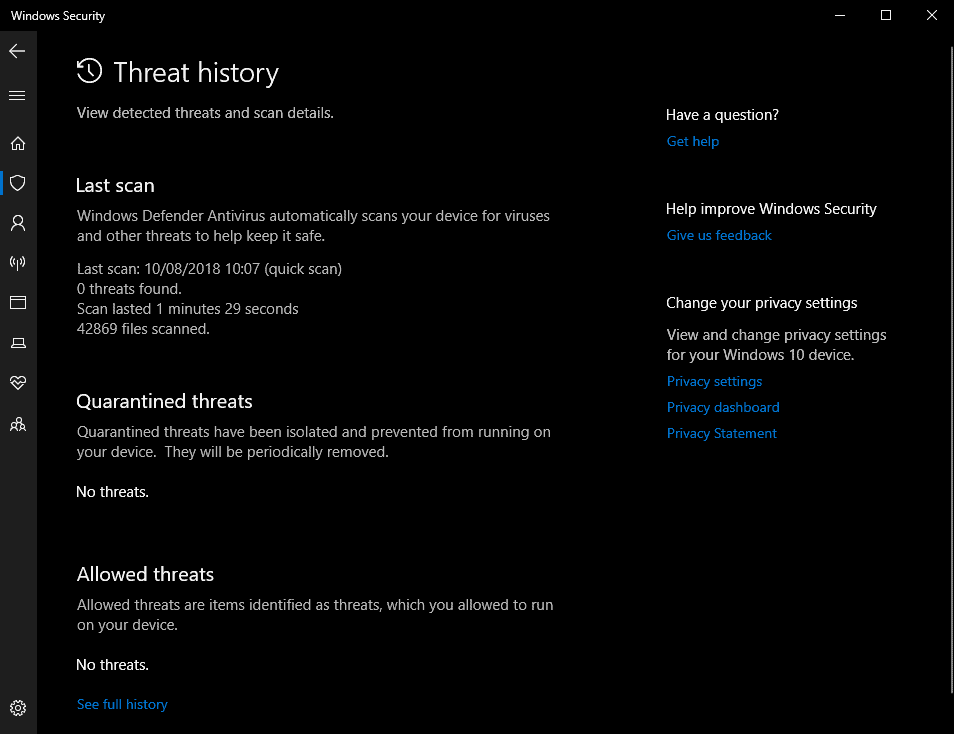
Detected PUAs are moved to the Quarantine of Windows Defender automatically. It happens that you want to keep a program that Windows Defender identified as a PUA.
You can restore any program that Windows Defender put into Quarantine and potentially unwanted programs are no exception to that.
- Use Windows-I to open the Settings application.
- Go to Update & Security > Windows Security.
- Select "Open Windows Security".
- Go to Virus & threat protection.
- Click on "Threat history".
- Select the threat that you want to recover and then restore.
- If you don't see the threat listed there, as only some are displayed there, select "see full history" to get the complete listing.
Windows Defender restores the file to its original location, e.g. the Downloads folder. You should be able to run it from there then without any issues.
Now You: Do you run antivirus software with PUP protection? (via Windows Central)

















should users of 3rd party av solutions toggle this on? (you know… use 3rd party av but have periodic wd scans turned on)
Piles of garbage and anti-garbage. The wonderful world of a truly free end-user software market ;-)
The “latest additions to WD”….. that’s funny since third party AV have had the ability to block PUPs for the past five years at the very least.
Yeah but it doesn’t have a chance of f-ing up your computer unlike 3rd party antivirus
I just use an app called unchecky.
https://unchecky.com/
I use Unchecky as well but its use has no direct bearing on the problem discussed here. Further, the registry change is not useful or needed if you use the latest Windows 10 x64 1803 Home, latest Chrome x64 beta, latest Defender, and latest Chrome extension Windows Defender Browser Protection extension. Using the test at https://www.amtso.org/feature-settings-check-potentially-unwanted-applications/ results in a successful Defender action per its message in the Notification area in the taskbar.
I hope you guys realize PUPs aren’t just malware and worthless crapware, it also flags totally legitimate software like Cheat Engine, game trainers, Iobit’s and NirSoft’s things, some less known setup engines, etc.
I always need to uncheck at least one “false positive” when running MBAM, SuperAntiSpyware and Spybot on-demand scans.
Well, I could recall this GHacks article:
https://www.ghacks.net/2015/11/30/add-adware-protection-to-windows-defender/
So it seams enabling the same protection is still also possible via registry.
Windows Registry Editor Version 5.00
[HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender\MpEngine]
“MpEnablePus”=dword:00000001
Thanks to both Martin and my memory:)
Very useful, thank you! :)
Simple enough, thanks!
Are the files checked locally or remotely ? If remotely this is a privacy issue.
In that case, is there any risk that sometimes personal documents are checked too as they could be files part of a PUA ? If yes this has the potential for a massive privacy issue, especially in case files or sensitive metadata are sent to Microsoft for further analysis.
I find the description of the feature by Microsoft suspiciously uninformative.
PUPs? PUAs? Given the way MS moves these days, is this any more than a list of 3rd-party software that Microsoft begrudges us installing?
Not accusing – just asking…
‘Set-WinPreference -10Protection Enabled’ and You are back to XP or Windows 7…..LOL !
What, no group policy settings? Ugh.
Any ideas on how to mass implement this without System Centre or InTune?
Essential article, thank you Martin! PUA protection enabled! :)
Me too.
Me Too.