Windows Defender System Guard in Windows 10 Spring Creators Update
Microsoft added a new security feature called Windows Defender System Guard to Windows 10Â versions when it released the Fall Creators Update version of the operating system back in October 2017.
Windows Defender System Guard was designed to " create the condition that the integrity of the system can’t be compromised" to protect against boot-level attacks such as rootkits or bootkits.
The new defensive system includes features to protect, maintain and verify the integrity of the Windows system during start up and while it is running using local and remote attestation.
Microsoft introduces the Secure Boot feature in Windows 8 as a counter-measure against boot-level attacks. Secure Boot is a feature of the Unified Extensible Firmware Interface (UEFI). Secure Boot added a hardware-based root of trust which prevented that code could be run before the Windows bootloader.
Secure Boot moved the first opportunity to attack a Windows computer during the boot phase to the phase in which the other Windows components are loaded.
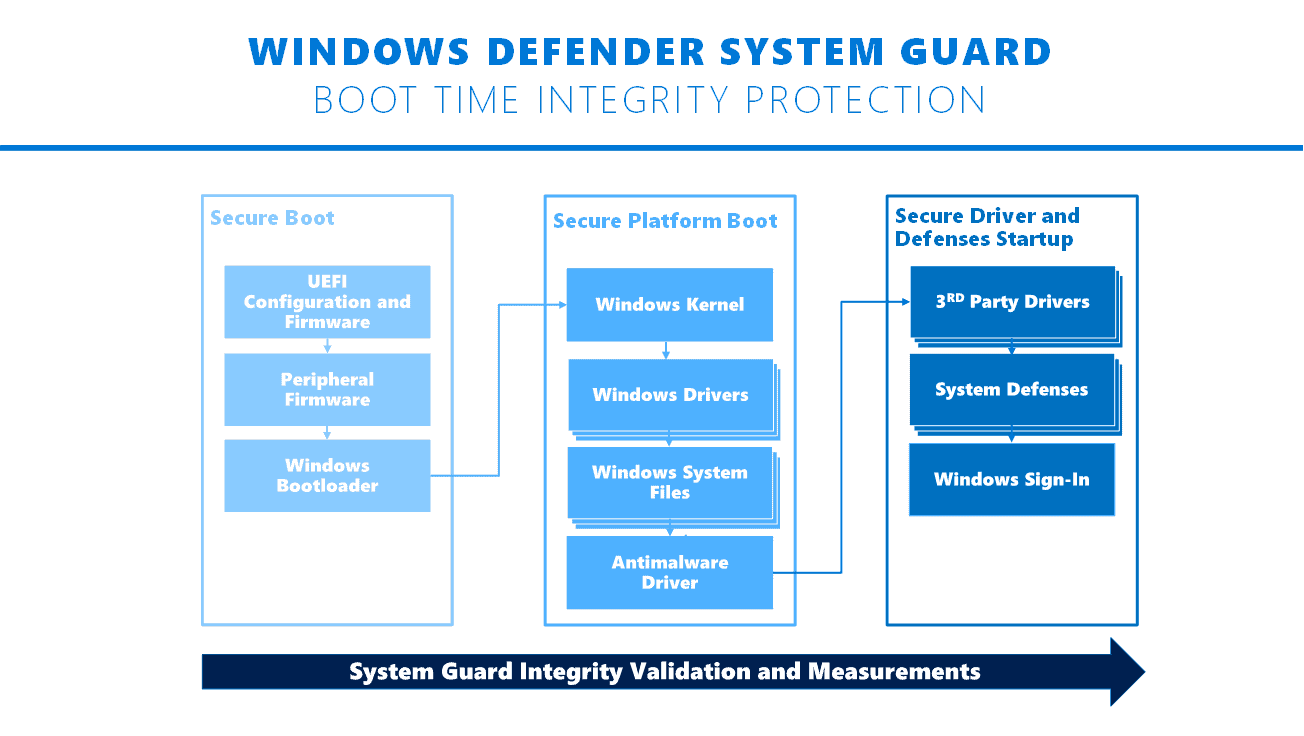
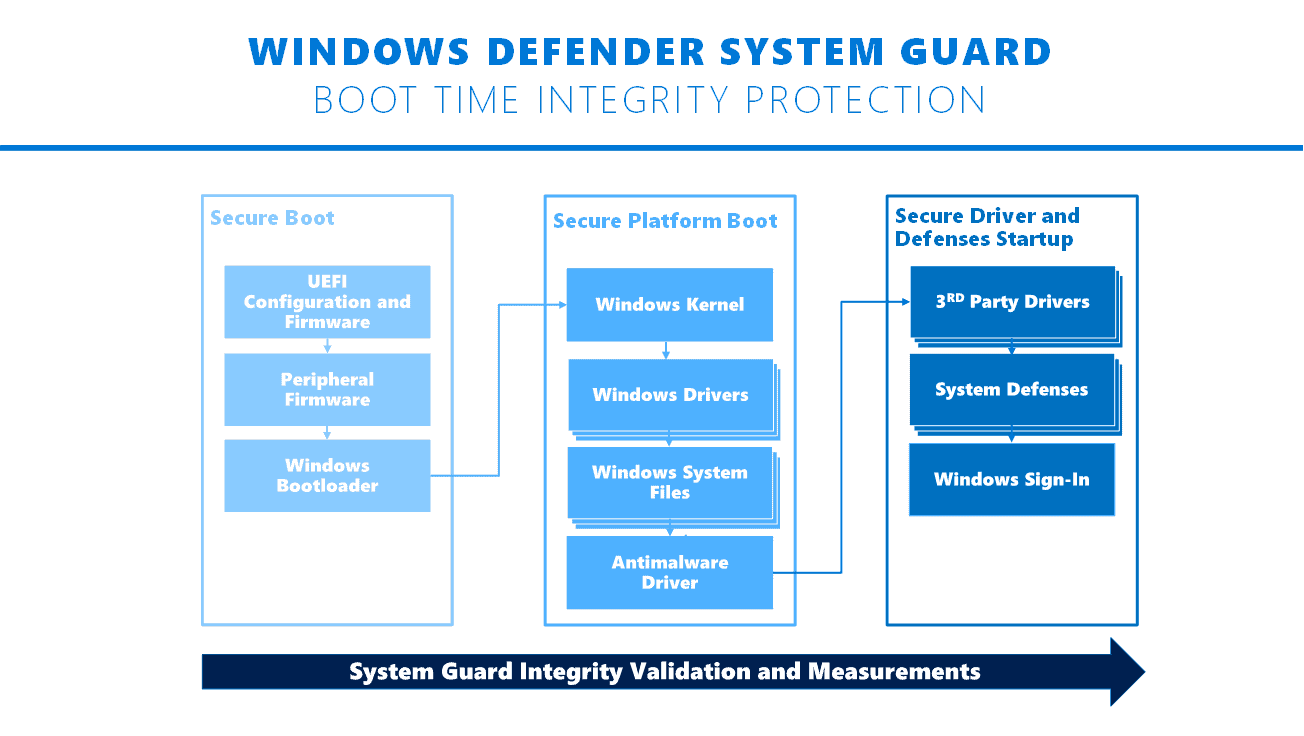
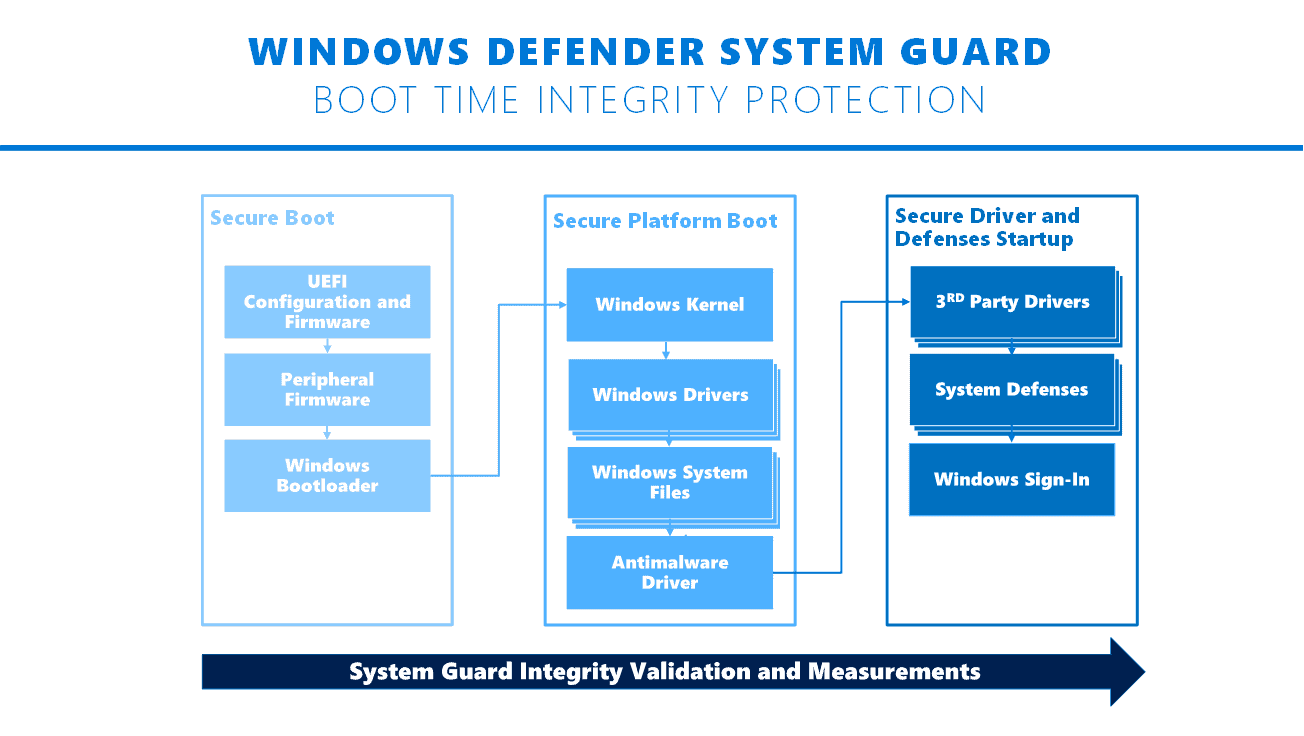
Windows Defender System Guard protects this phase of the boot process:
This is where Windows Defender System Guard protection begins with its ability to ensure that only properly signed and secure Windows files and drivers, including third party, can start on the device.
At the end of the Windows boot process, System Guard will start the system’s antimalware solution which scans all third party drivers, at which point the system boot process is completed. In the end, Windows Defender System Guard helps ensure that the system securely boots with integrity and that it hasn’t been compromised before the remainder of your system defenses start.
Microsoft revealed recently that devices running Windows 10 will get a feature it calls runtime attestation when they are updated to the next feature update of Windows 10 (Spring Creators Update or April Update).
In Windows 10 Fall Creators Update, we reorganized all system integrity features into Windows Defender System Guard. This move allowed us to continually make significant innovations in platform security.
Windows Defender System Guard runtime attestation, which is built into the core Windows operating system, will soon be delivered in all editions of Windows.
Runtime attestation may help in the following scenarios (among others) according to Microsoft:
- Detecting kernel tampering, rootkits, and exploits (or artifacts thereof).
- Provide signals for antivirus vendors and endpoint detection and response.
- Running banking apps or using trading platforms.
- Enhancing device security-based access policies
- Anti-cheat scenarios in computer games.
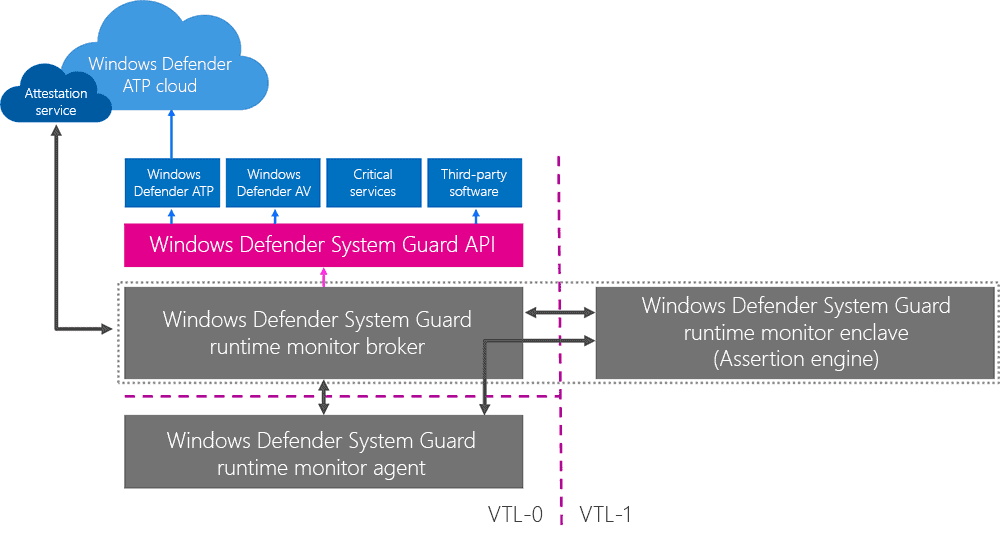
Microsoft is working on an API that security vendors, manufacturers and other parties can make use of to "attest the state of the device at a point in time".
The next feature update of Windows 10 includes the first phase of Windows Defender System Guard runtime attestation according to Microsoft.
With the next update to Windows 10, we are implementing the first phase of Windows Defender System Guard runtime attestation, laying the groundwork for future innovation in this area. This includes developing new OS features to support efforts to move towards a future where violations of security promises are observable and effectively communicated in the event of a full system compromise, such as through a kernel-level exploit.
Related articles
- Add file or folder exclusions to Windows Defender with Defender Injector
- Configure Windows Defender Network protection in Windows 10
- Windows 10 Pro: Windows Defender Application Guard support coming
- Windows Defender ATP support in Windows 7 and 8.1
- Windows Defender Browser Protection for Google Chrome first look

















Seems pretty cool actually.
From what I have read, this for now is applicable just to Enterprise and Pro users. Windows 10 version 1803 Home users are left out for now.
Win 10 = nanny OS
COOL!!
Is this a scheme to block all 3rd party anti-virus….software ? Example ; Kaspersky’s KIS/KAV demand disabling of Windows Defender (and other real-time anti-virus.. apps).
â– Anti-cheat scenarios in computer games.
So no more Nuke Trooper and Photon Man in Age of Empires DE? 😛