List the trackers that apps use on Google Play
Google Play is the primary application store for Android applications. Most Android devices ship with Google Play installed by default and most Android users use it to browse, find and install applications and application updates.
While there are other stores available, F-Droid for instance, Google Play is the dominating store when it comes to user numbers and activity.
Google Play reveals little about listed applications. You can click on "view details" on the desktop or tap on "permission details" on Android to display the list of permissions. What Google Play does not reveal, however, is whether an application uses trackers or analytics components.
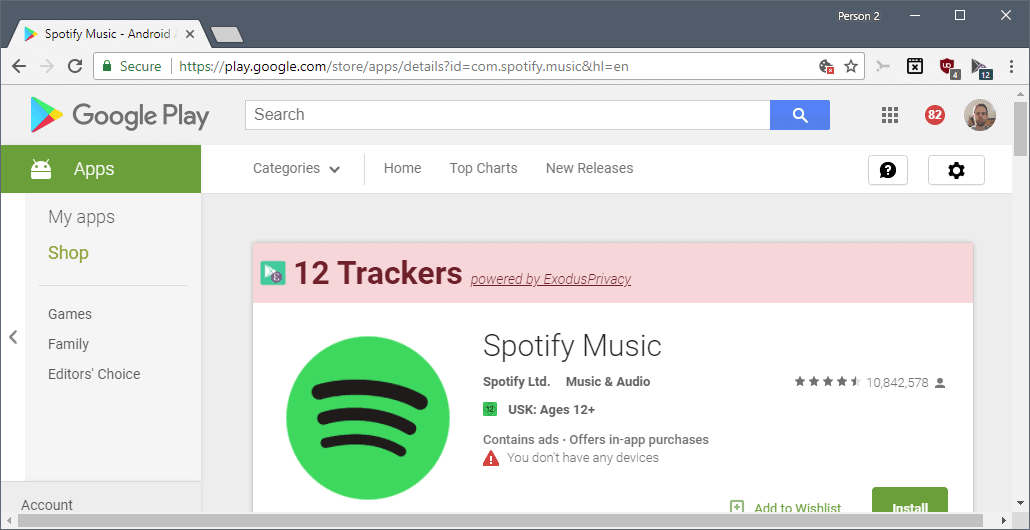
Show the trackers that apps use on Google Play
Enter Exodify; the free browser extension for Google Chrome and Mozilla Firefox is powered by Exodus Privacy, a French non-profit organization that "discloses trackers in Android environment applications".
Note: The extension should work in browsers that share the code with Chrome or Firefox. While I did not try running the extension in Opera or Vivaldi, it should run just fine in those browsers.
The development team of the non-profit released the alpha Android application Exodus Privacy earlier this year and maintains a website that offers search capabilities among other things.
The browser extension requests permissions to access Google's Play Store URL and the own URL only which is refreshing. It displays the number of identified trackers in applications that you open on Google Play.
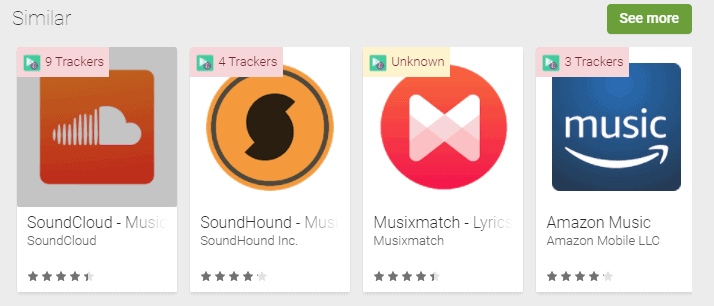
A click on the "powered by" link opens a history page of the app on the Exodus Privacy website listing identified trackers and requested permissions for each version of the app that was analyzed in the past.
Another click on a specific version of the app opens the apps profile page on the Exodus website. It lists all trackers found in the applications' code as well as all requested permissions on that page.
Permissions have a risk rating associated with them and you may hover over the rating to better understand what specific permissions grant.
All trackers are linked as well. If you click on a tracker, say Google Ads, Facebook Login or Adjust, you get a list of all apps that use that tracker.
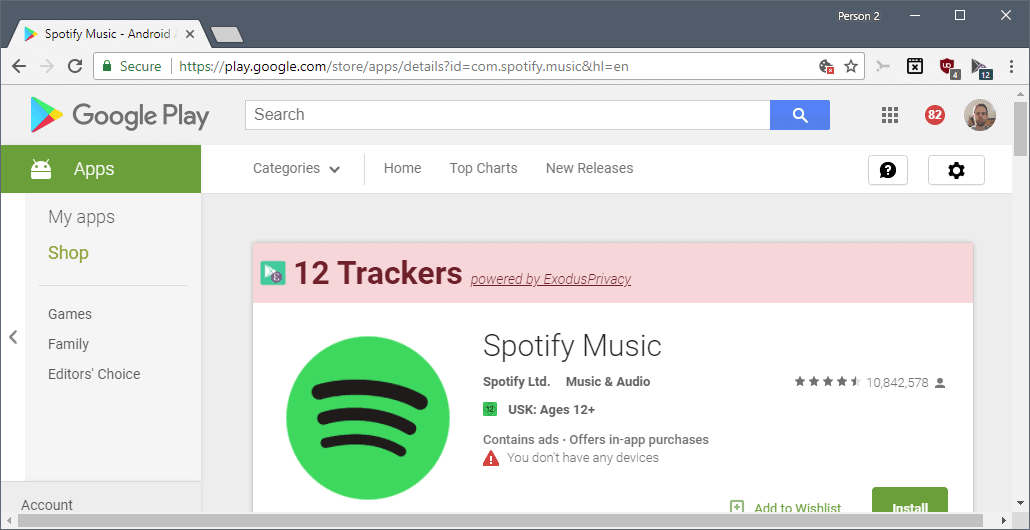
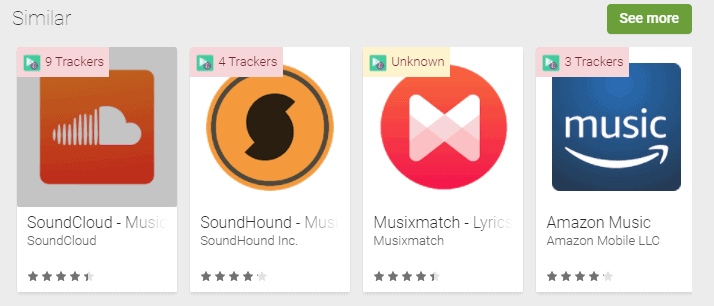
Back to Google Play; Exodify displays the number of trackers for individual applications you open on the site but also for application suggestions that Google displays on the same page.
The database offers tracker related information for many popular apps, but you may see "unknown" listed for others.
When you open an application that has not been scanned by the service at this point, you get an option to have it analyzed by Exodus Privacy. Just click on the "Would you like to let ExodusPrivacy analyze it" link to open the Exodus website. You may run a scan right then and there to find out about integrated trackers and permissions.
Scanning did not take longer than a minute during tests and I ran into a single "can't decode APK" error during that time. You can open the report right away to access the scan results.
Any user of the extension or the application benefits from the new database entry once a scan completes.
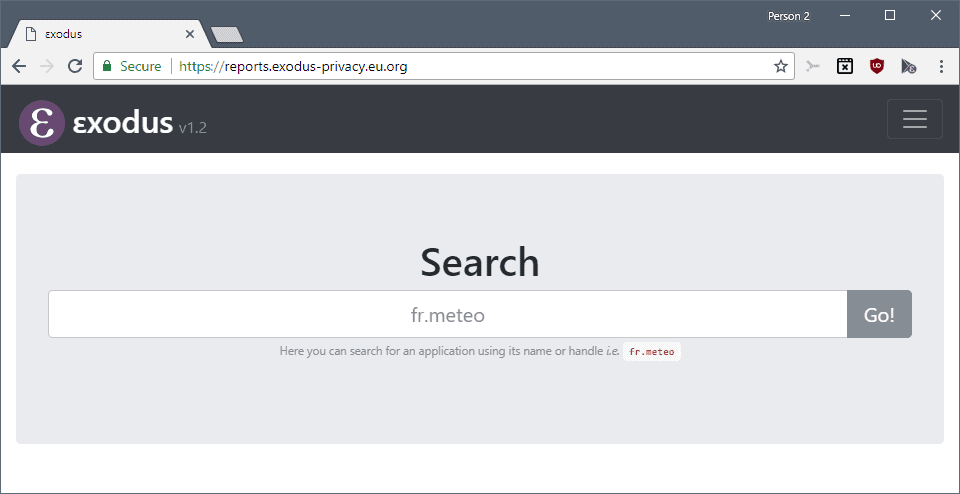
Tip: You can look up applications using the built-in search without installing one of the extensions or the application. Just head over to the main reports page and type the name of the application or its handle.
Closing Words
Exodify is a useful browser extension for Android device users who browse Google's Play store regularly. Others may prefer to look up information about applications they are interested in using the search on the Exodus website as it reveals the same information.
Now You: Do you analyze apps before you install them?
Related articles
- Clueful scans your Android phone for privacy risks
- Haven turns old Android phones into privacy-respecting home security systems
- Lumen Privacy Monitor monitors Android apps tracking
- PrivacyHawk: risk analysis for Android apps
- PrivacyGrade rates Android app privacy and informs about third-party use


















The only way to insure privacy on a “smart phone” is to destroy it. These devices main purpose is to track and analyze you and send that information back home.
The fact they can make phone calls is just a ruse to trick you into owning one.
That being said, I do have one. I’m aware of the built in Chinese spyware and all the rest of the data collection. I use it to send text and photos, make phone calls, and pop up a map from time to time fully aware that none of it is kept private.
“The only way to insure privacy on a “smart phone†is to destroy it”
The only way to ensure privacy with anything that communicates to the outside world is to destroy it. However, it’s entirely possible to achieve a balance between privacy and functionality. What makes a good balance is a personal decision.
Unfortunately the website comes to false conclusions, like every analyzers. A tracker is only dangerous when it’s activated (assuming it really violates some user rights), some apps including them in order to get useful information and just because there is an ‘analytics’ tracker doesn’t mean he collects information which expose you. A good example is SDMaid pro (same like free version) it includes trackers which you can opt-in or opt-out manually if you like. So that it means because it includes it it’s dangerous? No definitely not, SDMaid is also open source. Even if you enable the tracker it doesn’t collect information which expose you.
I think such pages doesn’t explain this because it’s some kind of clickbait these days to get your 10 minutes attention. All of these pages are mostly designed by people which are not involved in any security related topic otherwise they would notice their users that this is in most of the case worthless.
> All their ‘security’ cares about is blocking non-Google apps. I’ve installed (and uninstalled) dozens of PlayStore apps with so many trackers it was clear what their main business was.
I call this totally wrong, Google terms of use are very clear for everyone and integrating an tracker or ads system doesn’t mean automatically there bad. While including no ads doesn’t mean it’s automatically safe.
> Use NetGuard and set it to whitelist mode so only apps you allow can access the internet.
Doesn’t solve anything since almost every app these days require internet, the idea is good but especially apps which are involved in the whole internet part are pointless to block, instead I recommend to use Xprivacy Lua which allows you to take control over the permissions (you don’t like).
https://github.com/M66B/XPrivacyLua
It isn’t a matter of right or wrong, fact or fiction – it’s a matter of CHOICE – a choice that’s not only increasingly denied but increasingly obfuscated by claims like yours that assaults on privacy are all OK really – what are you afraid of if you’ve done nothing wrong. A message as old – and as dishonest – as history. In fact, much of the time, the problem isn’t just the data mining/surveillance – it’s the apologists for what is unacceptable behaviour.
Well said, Wayfarer!
> All of these pages are mostly designed by people which are not involved in any security related topic
Did you really check who are the people behind this project?
Please check esther’s resume (https://esther.codes/about-me/) or mine (https://imirhil.fr/), both co-founder of Exodus.
We contribute to many security system and build our own security project (hootspot, cryptcheck…). We are well involved in project like Tor or cryptoparty movement.
Not at all people “not involved in any security related topic”…
<3
“assuming it really violates some user rights”
What rights do you consider a user to have? Personally, I demand the right to not be tracked.
“some apps including them in order to get useful information”
Of course, but that’s not really relevant.
“just because there is an ‘analytics’ tracker doesn’t mean he collects information which expose you”
I disagree — I think it means exactly this. But I understand that reasonable people may disagree, so I offer that this point isn’t the most important. The most important point is that if I don’t want it to happen — for any reason — then it shouldn’t happen.
“Google terms of use are very clear for everyone ”
They’re also not terribly meaningful.
“Doesn’t solve anything since almost every app these days require internet”
I don’t know about that — I use a fair number of apps, and nearly all of them are firewalled off from the internet. They work just fine. When I encounter an app that doesn’t need internet access to perform its function, but won’t work without it anyway, I just uninstall the app and switch to one that’s more reasonable.
I’m with other commmenters here. Anyone who believes PlayStore gives a damn about user security is delusional. All their ‘security’ cares about is blocking non-Google apps. I’ve installed (and uninstalled) dozens of PlayStore apps with so many trackers it was clear what their main business was.
And that’s even before the whole host of manufacturers who don’t give a damn about Android updates once they have your money. Or the retailers who sell devices with Android versions so old they ought to be illegal.
Updated
[edit] Oooops, make that “Scoundrel”
Don’t believe everything you see on the Play Store.
I heard about this App a week or so back and checked the Play Permissions for it. It said “other” and generally that means pretty benign stuff.
So, turned off the radio, side-loaded the APK onto my LineageOS, v14 and guess what? Lineage shows five Permissions.
I can’t remember all but Read-SMS and read Contacts were among them. Hasty removal before even trying it.
So, is this a false positive from Lineage or deception? Pretty sure I know which and it will stay removed.
On the subject of your question Martin, I tend to look at what permissions an app requires before installing it. If it wants to access something which I don’t think is relevant, I simply dump it altogether.
It doesn’t surprise me though that each of them would have a large number of trackers attached to them.
mama, i wannabe Ghostery when i grows up…
Uh…uhmmm, you might recall Martin’s article on Cliqz which acquired Ghostery recently: https://www.ghacks.net/2017/10/06/mozilla-to-launch-firefox-cliqz-experiment-with-data-collecting/
Sounds to me like Ghostery is a tracker in its own right.
Ghostery is open source, now….. I don’t know if that really makes a difference — but still!
Ooch, so many trackers…
Interesting to see the crazy amount of trackers some apps have. The next question is what can you do about the built in, impossible to remove trackers from the likes of Samsung?
Use NetGuard and set it to whitelist mode so only apps you allow can access the internet.
github.com/M66B/NetGuard
NetGuard
2 trackers
10 permissions
Get the .apk from github not play store.
Here’s what I do — I have a firewall installed and configured to block all traffic to and from apps unless I specifically allow it. That way, it doesn’t really matter how many trackers are installed — they can’t talk to anything.
The best way to do this is to root your device and use an app that configures the built-in Linux firewall. The second-best way (if you don’t want to root) is to use one of those “fake VPN” firewalls.
For combating in-app tracking alone you just need a phone which supports Xposed module and use Xprivacy Lua, and to have a hosts file blocking known tracking domains. You can go further by install LineageOS or LineageOS for microG (if you have to use apps that depend on Google components) and other apps for the purpose.
If you’re not willing to install LineageOS (which is by far the best solution imo), your option would be to disable said applications.
Does anybody know if LineageOS can be installed on Sony Xperia XA1 . What little googling I did suggested it was difficult due to its using a Mediatek chip ?
Unfortunately, disabling Samsung apps isn’t an option. There’s a Disable button present on each of them, but it’s disabled by default. The only temporary option is “Force stop”, but it re-enables itself eventually.
You can prevent them from being updated by setting “Automatically install updates” to “Never” in the phone’s Settings menu, but that’s about it.
The next phone I buy will be one which has stock Android installed. There’s not many of them around at the moment, but at least you get a barebones version of the OS without all the bells and whistles that companies like Samsung use to overlay Android with their own interface which allows them to limit the way menus and apps work. On a Samsung phone, it’s called Touch Wiz.
Not into the extension, but the website is nice. Btw:
Google Chrome: Fast & Secure | 0 trackers | 31 permissions | v64
Firefox Browser fast & private | 4 trackers | 30 permissions | v59
🤔🤔🤔
“Google Chrome: Fast & Secure | 0 trackers”
You mean no trackers other than Google itself, the biggest tracker of them all? LOL All of Mozilla’s data collection can be turned off.