Dr.Web CureIt! 8 on-demand virus scanner released
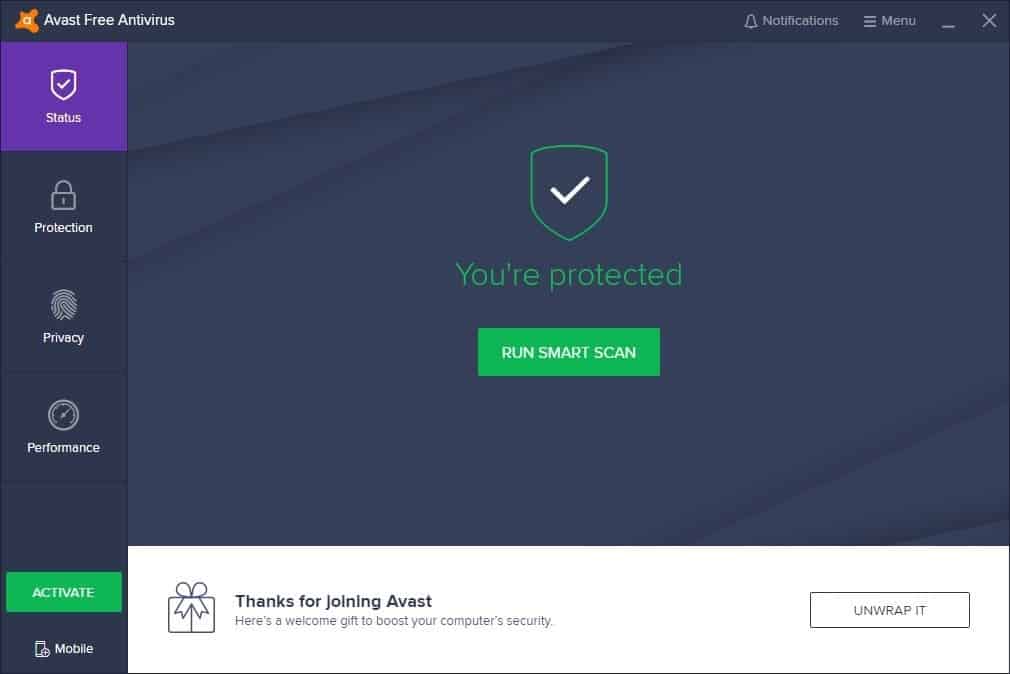
Dr.Web CureIt! is a program that I have been holding in high regard for several years now. The program is an on-demand scanner that I use to get a second, or third, opinion in regards to malicious software on my computer systems. While I run up to date antivirus software, I make sure to scan my system regularly with Dr.Web CureIt! and Malwarebytes Anti-Malware just to be on the safe side of things.
Dr.Web CureIt! 8 has been released recently introducing support for Microsoft's Windows 8 and Windows Server 2012 operating systems among other things. While that is interesting in itself, several of the new features introduced in this version of the virus scanner demand highlighting:
- Implemented a rootkit search subsystem.
- Added options to scan the BIOS of the PC for so called bioskits that have infected the BIOS of the computer.
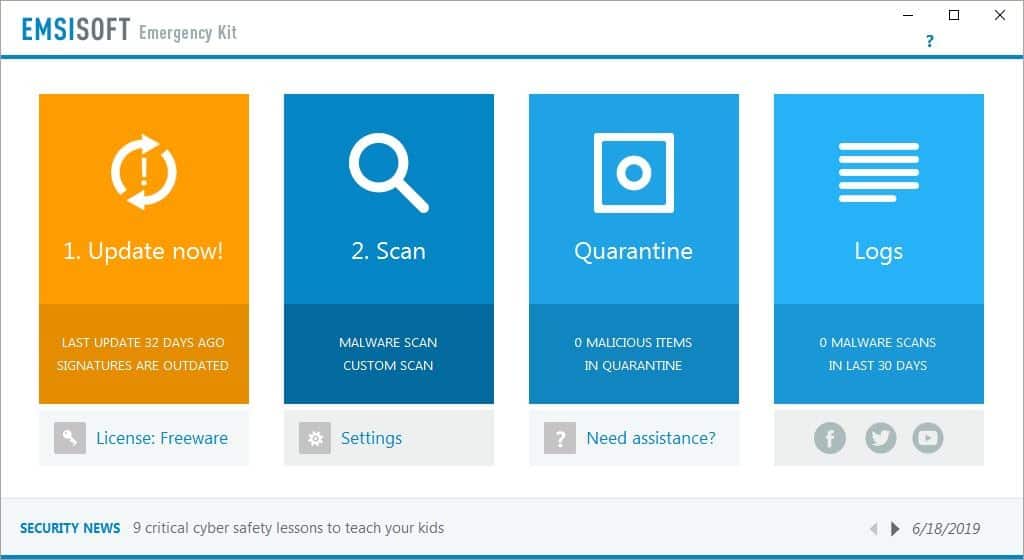
- Added a native quarantine manager.
- Added an option to block all network traffic during scans.
- Added an option to shut down the system after the scan.
- Added an option to block low-level file operations.
- New custom scan feature to scan specific areas of the system only, for instance boot sectors, startup objects or the memory.
- Scanning speed increase and support for multi-threaded scans to utilize multi-core processors.
Dr. Web is a portable program that you can run right from the location you have downloaded it to. Note that the free version makes the sending of statistics to the company mandatory. The file has a random name to bypass malicious software that blocks certain known security software processes from starting up on the system.
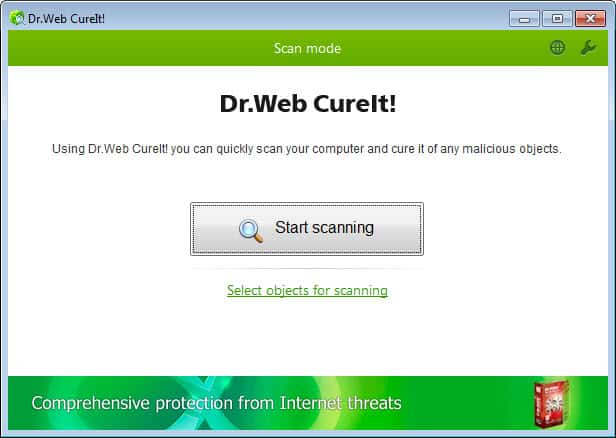
You can now run a scan of the system or use the new "select objects for scanning" option to scan only subsystem instead. The scan itself should not take long and you are taken to the results screen regardless of whether something has been found or not.
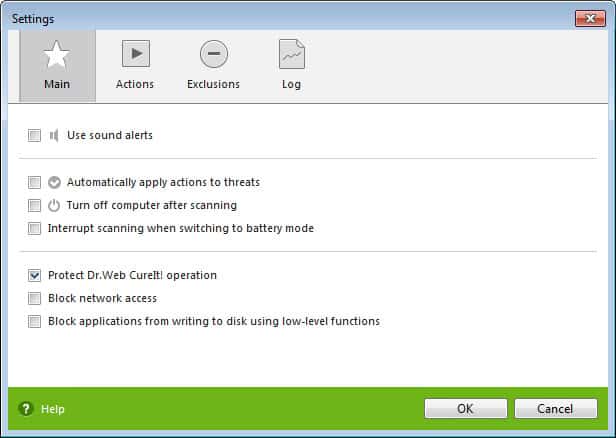
You find several of the new options in the program settings. Here you can enable the network access block or the blocking of disk writes using low-level functions as both are not enabled by default.
The actions tab may also be interesting as you can use it to define default actions for specific types of malware and the three file statuses infected, incurable and suspicious.
The exclusions tab in the settings enables you to prevent the scanning of specific files or folders on you system, and enable the scanning of files inside archives as well.
Verdict
Version 8 of Dr.Web CureIt introduces several great new features to the program that regular users of it will certainly appreciate. While you may need to configure them before they become available, they may aid in the scanning and recovery of a system after a successful malware attack on it.
Update: Note that the program may identify a modified hosts file as malicious even though it may have just been modified by the user of the system. Make sure to exclude it from the cleaning process.
Advertisement















Yes, be very careful as this will ID a false-positive on your hosts file. Same here, I opened mine with Notepad after it said there was an issue and all entries are ok and file is ok. I’m making a copy of the file before it finishes.
Well, just noticed, this program wiped out my host file also, left only 4 entries out of the mvs host file.
Thanks to God hates Fags for bringing this to my attention.
This flagged a false positive:DFH.HOSTS corrupted, so shan’t use again.
It advised deletion but only realized it had reduced my Hosts file to Nil when I got stacks of ads showing up.
Back to normal & ad free now after readding zeus,malware domain list,hpHosts & Cameleon etc.
That’s bad. Did it give you an option to not go ahead with the change, or did it modify the hosts file right away? Also, how did you restore the hosts file?
Hi ,it recommended immediate removal which I did & a restart after which Hosts was reduced to nil.
After that I opened HostsMan,& deleted all data from C:\ProgramData\abelhadigital.com\HostsMan
I then reinstalled my Update Sources using HostsMan from scratch & everything was back to normal again listing 33,549 Hostsnames.
Thanks for the explanation. I have added an update to the end of the article that warns users about it.
It was able to run after bypassing Facebook and executing the program.
I didn’t run it in enhanced protected mode but it ran about 3+ hours on
my Win 7 Ultimate, dule core 3.3 ghz intel and both cores were near
100% all the time it was running so nothing else was able to run
alongsiee it. It did point out some files that. needed deleting and some
other files referring to my Facebook block program that I choose
not to delete.
You have to be careful when you use this.It opens up in Enhanced Protected Mode{which it recommends}.Doing this will LOCK-UP your computer for the entire time of the scan.The screen is blacked-out{except for Dr.Web CureIt window}and you can’t use your computer at all during the entire time that the scan is going on{even your internet clock is frozen during this time}! If you don’t want this,click-on the cancel button,as this will cancel the enhanced protected mode and will put it in ‘standard’ mode and then you can use your computer while the scan is going on!
the download link generates a 404 error. hmmm.
Dr.Web CureIt! 8.0.6 [2013-04-07]
Just get it from: ftp://ftp.drweb.com/pub/drweb/cureit/cureit.exe
No hassle, no Facebook…
Note: this program will redirect you to the Facebook webpage upon commencing the download. I have Facebook blocked on my home network for the simple reason that my 13 year old daughter is addicted to Facebook and her grades were starting to show that. Although Facebook is blocked the download continued and it is quite large (110 MB). I am hoping that blocking Facebook will not prevent me from using this software as it appears to be very good.
.