Microsoft releases Fix-It for latest 0-day vulnerability.
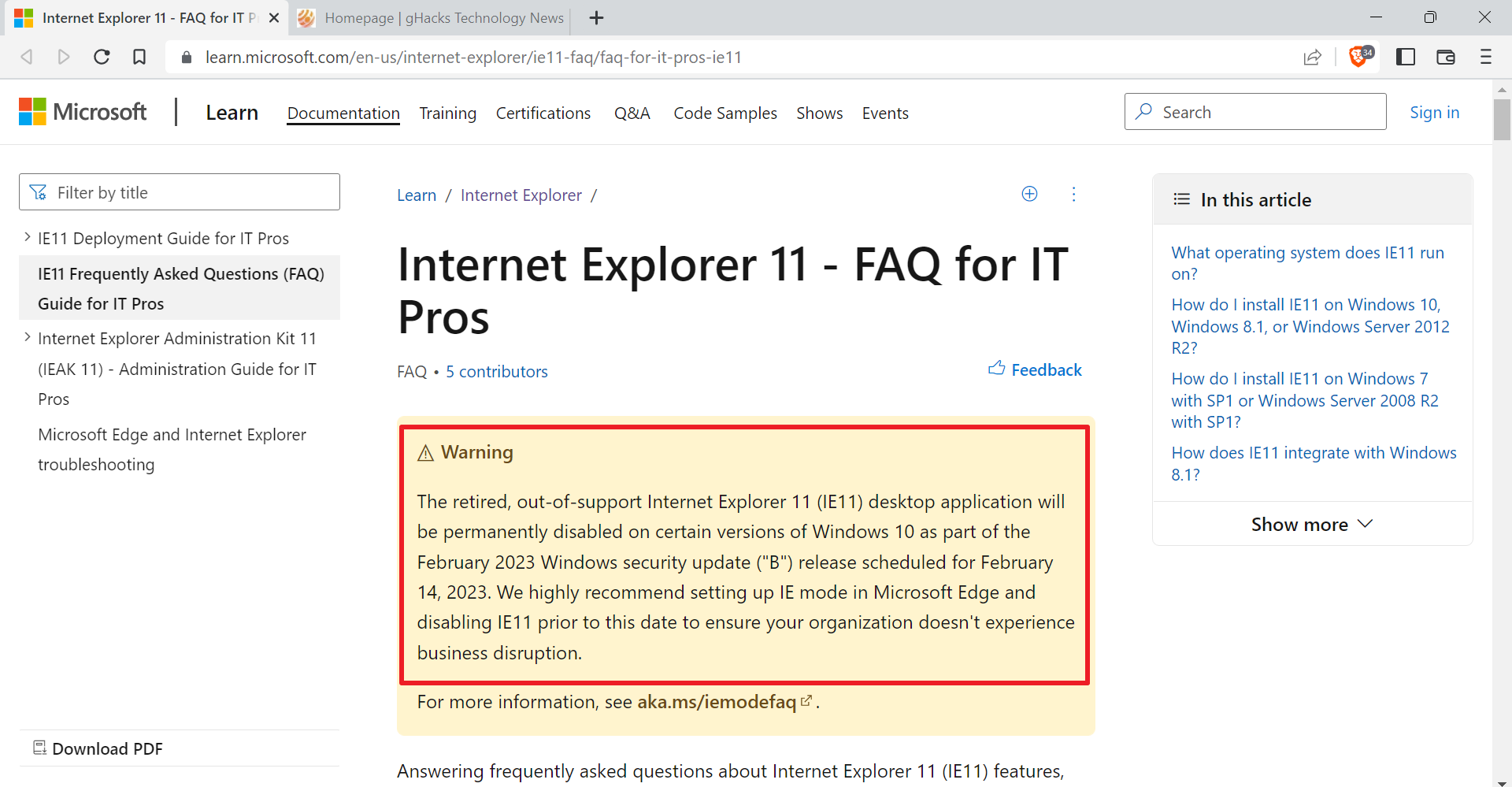
A few days ago a new 0-day vulnerability was discovered that affects all versions of Microsoft's Internet Explorer - but Internet Explorer 10 - on all recent versions of the Windows operating system. Microsoft suggested workarounds like installing the company's own excellent mitigation tool or setting the Internet and Intranet security zone to high to block the exploit from executing. Third parties recommended to not use Internet Explorer until a fix is released by Microsoft.
The security advisory confirmed that targeted attacks were carried out on the Internet, with users only having to visit a website with a vulnerable version of Internet Explorer for the attack to take place. The Poison Ivy trojan was installed on a successfully exploited system, and for some days researchers assumed that it was the only threat.
Today it became known that other exploits have also been used in the last couple of days, making it even more important to fix the vulnerability as soon as possible.
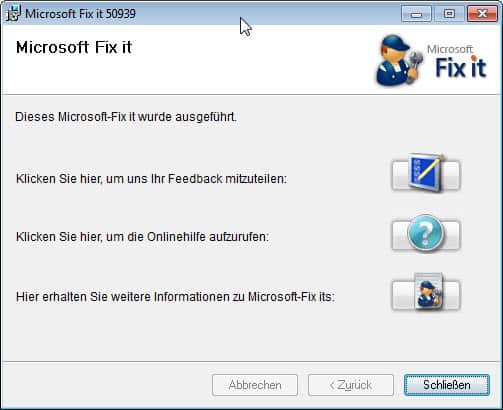
Microsoft today as well has released a Fix IT to patch Internet Explorer and protect the browser and thus the underlying operating system from the 0-day vulnerability. A Fix it is a lightweight portable program that can modify the operating system or programs installed on it. This particular Fix It resolves the 0-day vulnerability for 32-bit versions of Internet Explorer.
Before you apply the patch you need to make sure that Internet Explorer is fully updated. Once done, download the Fix It from this Microsoft Support page and run it once it is on your computer. Just follow the instructions on screen to patch your system and protect Internet Explorer form being vulnerable to attacks exploiting the vulnerability. Again: this only works for the 32-bit version of Internet Explorer. It is therefor recommended to run this version only for the time being until a security update resolves the issue complete. The Fix It support page offers a second program that you can use to disable the fix again.
It may come as a surprise to many that Microsoft reacted that fast, considering that the company in the past has often taken its time before it released updates to the public. The quick patch may have been designed with Windows users in mind, but it certainly may have also had something to do with the bad press that Microsoft received after the vulnerability was discovered. (via Dottech)
Advertisement











@Morely Dotes
“And how many years did it take them to get their act together on this one, Martin?”
Microsoft wouldn’t have found it in million years. It were the hackers who found the exploit
in IE and used it to spread trojans. It was a 3rd party security firm which identified the trojans
and tracked it back to the exploit.
Even the lastest Nitro botnet pre-installed on Windows PCs hasn’t been found by Microsoft.
It was found by a customer buying an infected PC.
This is a temporary fix as Microsoft will issue out-of-band IE update tomorrow Sept.21
This security hole , and many others, in IE6-9 (and Windows OS) just shows
how Microsoft “innovate” by copying code for 10 years, from browser to browser without
any QA and security checks.
Microsoft:
This is an advance notification for one out-of-band security
bulletin that Microsoft is intending to release on September 21,
2012.
The full version of the Microsoft Security Bulletin Advance
Notification for September 2012 can be found at
http://technet.microsoft.com/security/bulletin/ms12-sep.
Seems they have really got their act together on this one.
And how many years did it take them to get their act together on this one, Martin?
Let’s face it, the only legitimate uses for Internet Explorer are (1) to download a better browser to use on the Internet; (2) Windows Updates; and (3) Intranets that rely on the built-in security holes, because they are using Microsoft servers such as Sharepoint.
Anything else is simply asking for trouble.