SSL Traffic Analysis Reveals What You Are Looking At On Google Maps
The general consensus is that https connections to web sites protect your data from being spied at by users in the same network. That's why all major web services such as Facebook, Twitter or Google have started to enforce the use of https on their websites.
Most users do not know that it may still be possible to find out what a user is looking at on a specific website, even if https is enabled.
Shuo Chen, Rui Wang, XiaoFeng Wang, and Kehuan Zhang of Microsoft research released a paper titled Side-Channel Leaks in Web Applications: a Reality Today, a Challenge Tomorrow back in 2010 that mentioned this threat to user privacy.
Vincent Berg a few days ago published a proof of concept demonstration (in form of a video) on the IOActive Labs Research that showed how Google Maps was vulnerable to SSL Traffic Analysis.
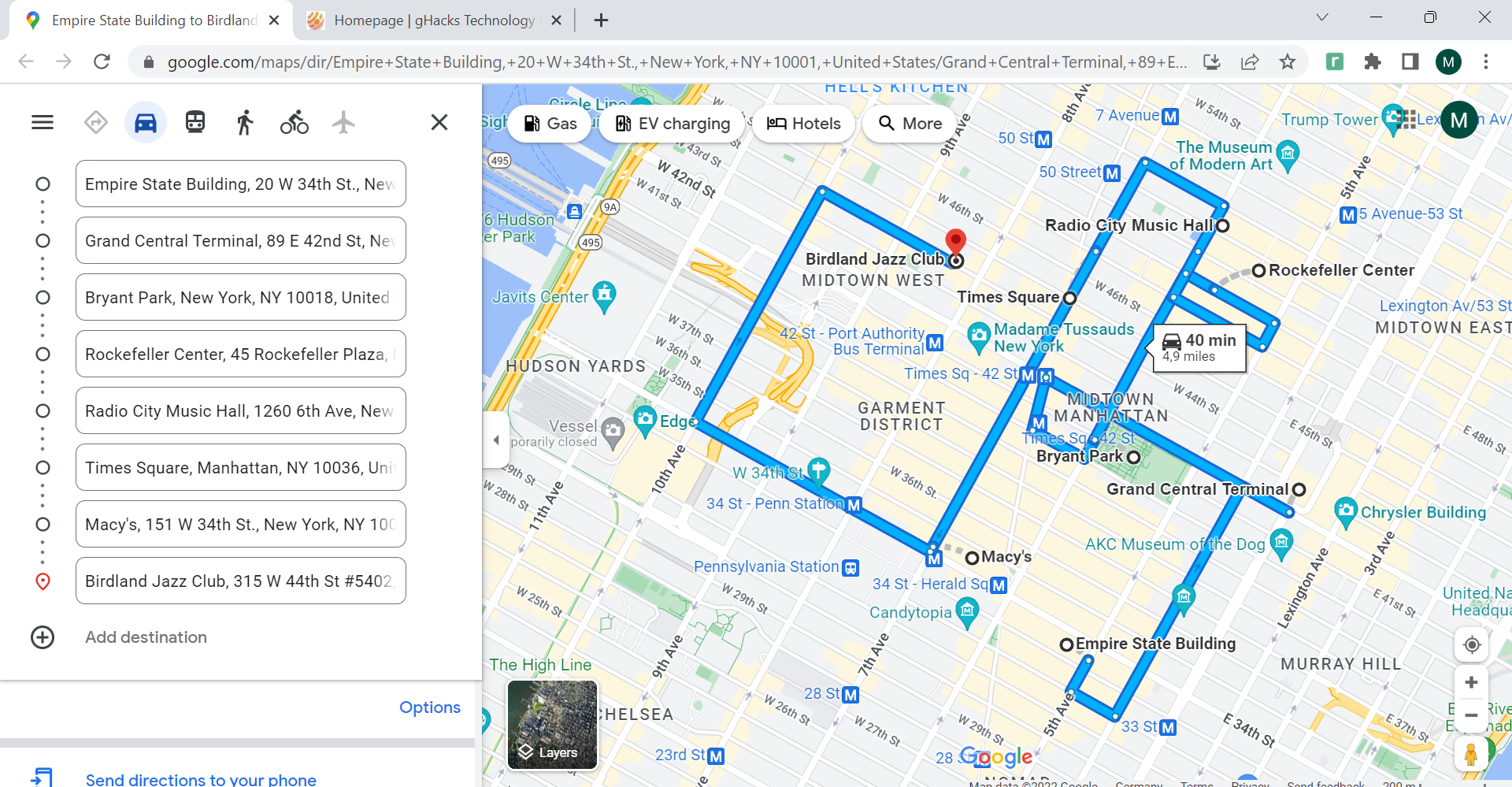
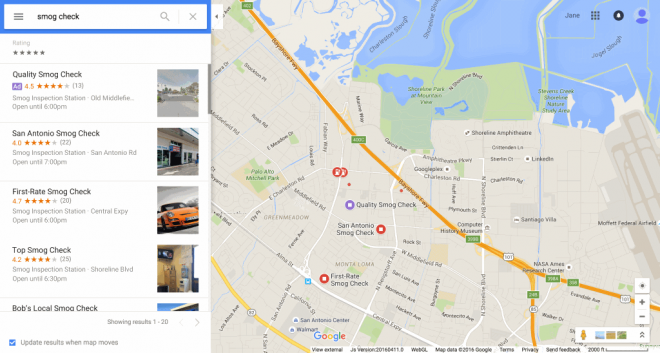
He first analyzed the JavaScript used by Google Maps using Firefox and the excellent Firebug extension to discover that google Maps was using "a grid system in which PNG images are laid out". These PNG images had different file sizes which were added to a database.
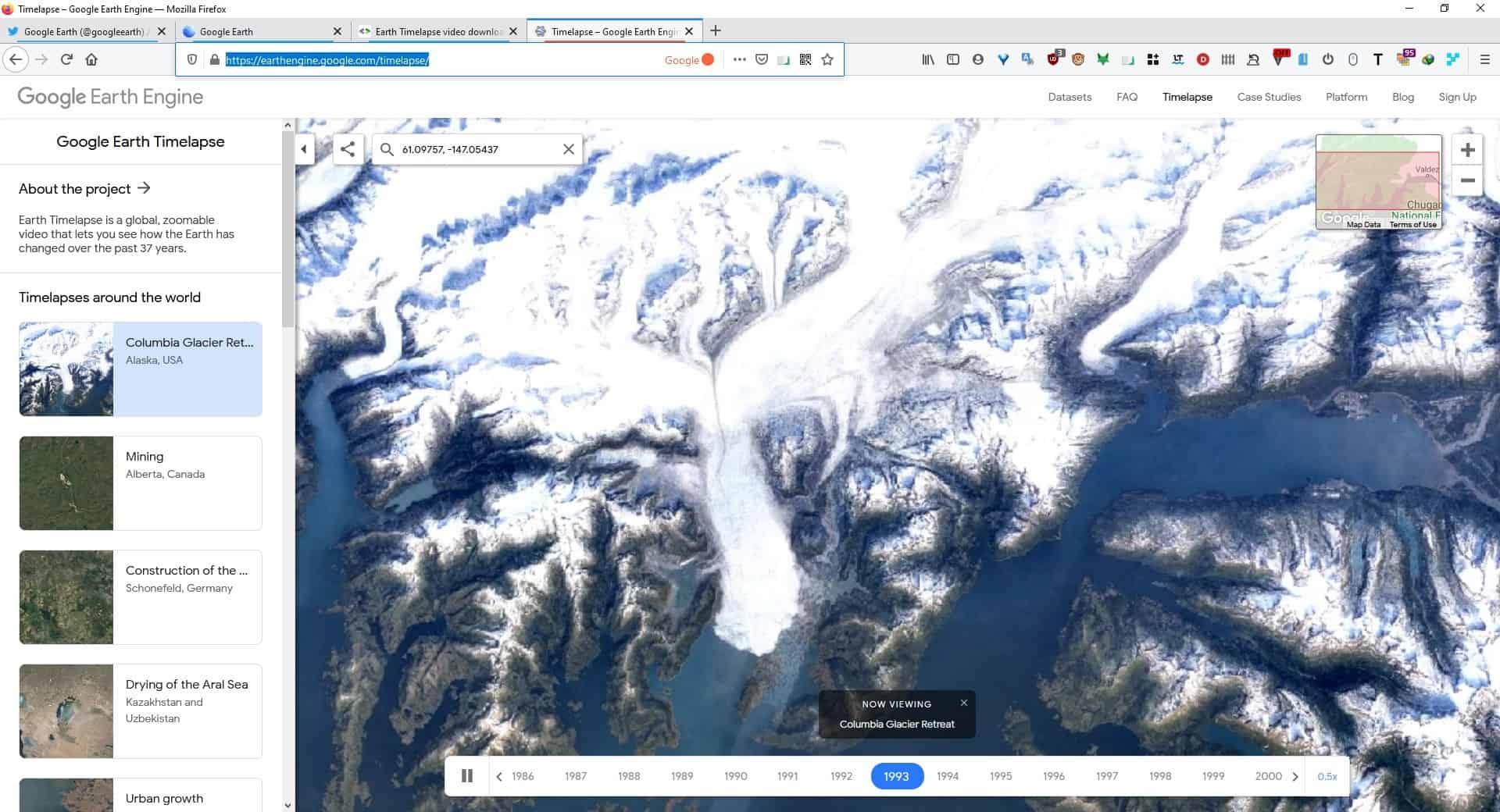
Vincent Berg then built a tool that was able to approximate the sizes of images by monitoring the encrypted traffic. The software then tried to match the estimated size with the size in the database to find a matching region in the world. Several city profiles were created, as it was not realistically possible to create database information for all map tiles.
The video below demonstrates the workings of the tool on the right side, and the user actions on Google Maps on the left. It basically shows how both Paris and Berlin were identified correctly by the program.
Not all web applications can by analyzed with SSL Traffic Analysis, but those that do can pose a privacy and maybe even security risk for users thinking they are safe since they are connecting to the service via https.
Users could protect their connection by connecting to an encrypted virtual private network like VyprVPN. Even that may however be prone to analysis according to the author of the blog post.
Advertisement










Does google offer HTTPS for google maps? It always goes to HTTP when I visit Google Maps.
Yes, just enter https://maps.google.com/
Speaking of SSL:
Flaw Found in an Online Encryption Method
http://www.nytimes.com/2012/02/15/technology/researchers-find-flaw-in-an-online-encryption-method.html