Clean a PC Manually with Autoruns
Malware as it is comes in many forms. Sometimes there are viruses that will lock your antivirus program and render it unusable. What do you do to escape this? There are several options, of course. This is a way to use a free program called Autoruns. Autoruns allows you to manually remove infections. This does take some work. In the end, you will be glad that you took the time to remove those sneaky viruses that disable your other options for cleaning the PC. Aggressive malware will usually resist automatic removal and evade detection. A solid manual clean-up is something that any good geek should know about. Anti-spyware utilities are unreliable and are often malware download programs themselves.
Simply download and unzip Autoruns from the link below. It is a standalone utility that does not require installation. Add it to a flash drive for portable use and easy access.
http://technet.microsoft.com/en-au/sysinternals/bb963902.aspx
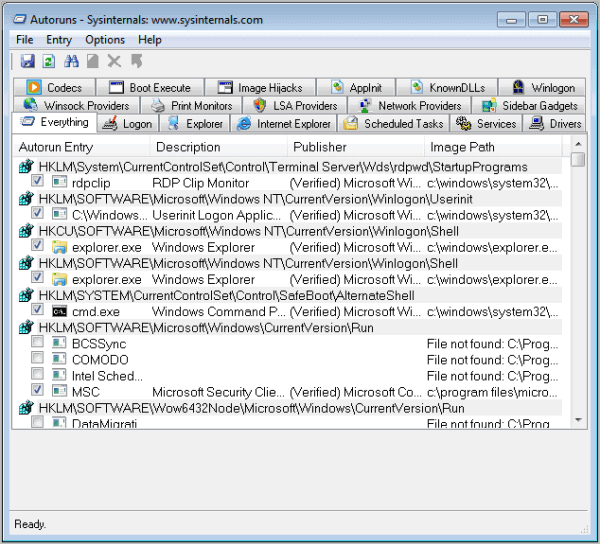
From the Zip file, double-click the autoruns.exe Application listed first. The application opens quickly, and you should see a tabbed interface.
This is the main window for Autoruns. The list shows all software that will run when you start your PC. Most of the programs presented are legitimate and are not malware. It takes some practice to identify malware processes. To disable a program from launching temporarily, uncheck the box next to the entry. To permanently prevent a program from launching, highlight and delete it. You will have to uninstall the program from your computer, as this deletion does NOT remove the software. If you recognize the software name, it is most likely legitimate. Check the Logon tab, as this is where malware will most typically appear. You may want to check the Hide Microsoft and Windows entry setting under Options to hide operating system files from being displayed. This reduces the list you have to go through significantly.
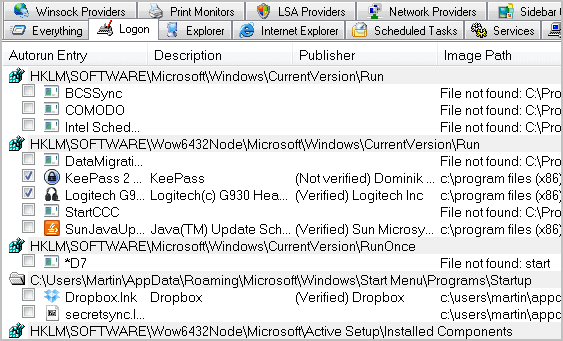
It should be noted that malware will adopt recognizable software names. One way to spot malware is by looking under the Publisher column. If there is no entry or if the publisher’s name is something that you do not recognize, then it is probably malware. If you suspect a recent infection, open the EXE or DLL file for the software and look at the “last modified†date. If it is a recent date and you have not installed any software recently, that is malware. Updates will have a Publisher clearly listed and are confined to operating system updates. These will have recent dates but are not malware. Generally, malware can be found in the C:\Windows folder or the C:\Windows\System32 folder.
This is what a malware entry will look like. In this case, Diskfix and SearchHelper are the culprits. These were not intentionally installed; they were installed by a Trojan downloader. Note that they have generic icons and the filenames are random characters. This is the mark of malware.
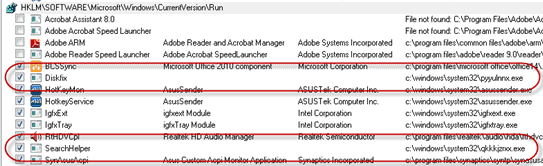
These two executable files were found in the C:\Windows\System32 folder using Autoruns.
Once the malware has been identified, you can temporarily disable them, permanently delete them, find them in Task Manager to terminate the processes, delete the files from your hard drive, or move them to a folder that will confine them from restarting. Do all of the above if you are sure that it is malware. Once you have made the changes, reboot the computer and start Autoruns again to see if the programs are still listed there. Next, check the Task Manager to see if they are running. If everything is clear on those fronts, you have succeeded in manually cleaning your PC of hidden malware and your locked antivirus program should be running well again.
If you are not sure about a specific program or file listed in Autoruns, you could use an online virus scanner like Virus Total to scan it. Another option is to research the file name on the Internet.
Advertisement















I’ve been using it for years now. One of the best apps out there. The company (before being bought by M$) had also created other wonderful products. good thing at least they pay for their development now.
Good thing I see a post about Autoruns. It’s an essential tool in my usb memory.
I use it along with Process Explorer, ExplorerXP and Everything Portable (by Voidtools).
When checking an infected PC, I just open them all, kill explorer.exe, locate the garbage with autoruns, kill its process with process explorer and find it instantly with everything, and then I rename it (or delete it when I’m positive it’s useless).
I honestly don’t know where I learned to do that. But it has proved to work better than some malware removal tools.
AUTORUNS is particularly useful for spotting and recovering/resolving files not found .
When I am unsure about where an entry is/was from, I tend to restore the file from backup if I can or from another location on my disk.