Build a Quick and Reliable Firewall with fwbuilder
Network security is tantamount to retaining your sanity. Be it at home or at your place of business, a firewall is often a necessity (especially when you have Windows machines on your network.) With the Linux operating system there are a number of ways to build a firewall. Back in the day I used to hand-build a firewall using the now-outdated ipchains (replaced by iptables). It wasn't a time-consuming, difficult task but one that lead to a very strong firewall.
That was then, this is now and in the now there are graphical front ends to help you build a firewall without having to issue a single command from the command line. One of those tools is fwbuilder. The fwbuilder tool builds iptables rulesets but does so by treating each element of the individual rule as an object, a service, or a time. Objects are addresses. Services are protocols or (as the name implies) services. Time is just as it says, time (such as day of the week or a specific time.)
To start up fwbuilder you will find the menu entry in Applications | Administration (under KDE) or in System | Administration (under GNOME). When you fire up fwbuilder you might find yourself thinking "Where do I start?" The first thing to do is go to the File menu and select New Object File. You have to give your object file a name and then save it.
Once you have done this you are ready to start building. As you can see, in the image to the left, the drop-down icon to the left of the User drop-down is what you click to insert a new object into your object file. Click that drop-down to reveal the list of all object to insert.
The first object you must insert into your object file is the Firewall. When you select that a wizard will open up asking for a name for your firewall, what software will run the firewall, and what OS the firewall will run on. I will name my firewall "Example_Firewall", I will choose iptables from the software list, and Linux 2.4/2.6 for the OS.
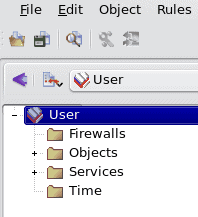
Now, if you want to go the really easy route you can select to insert preconfigured template for your firewall. If you select this you will have to choose your template. Once you have taken care of this information click Next.
Once you click next you will see a list of different templates available. Each template serves a different purpose. As you click on each template a full description will reveal itself in the bottom pane.
After you select the proper template click the Finish button. Now fwbuilder will be open so you can view your template.
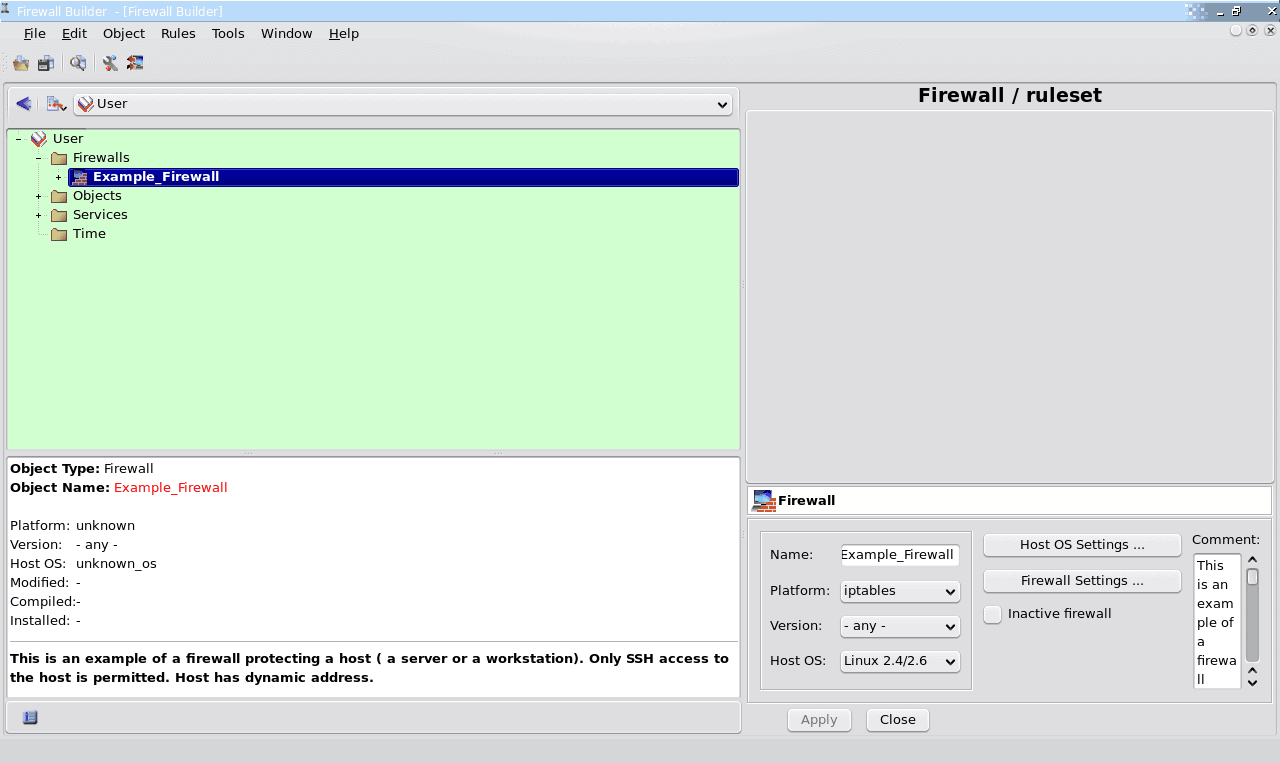
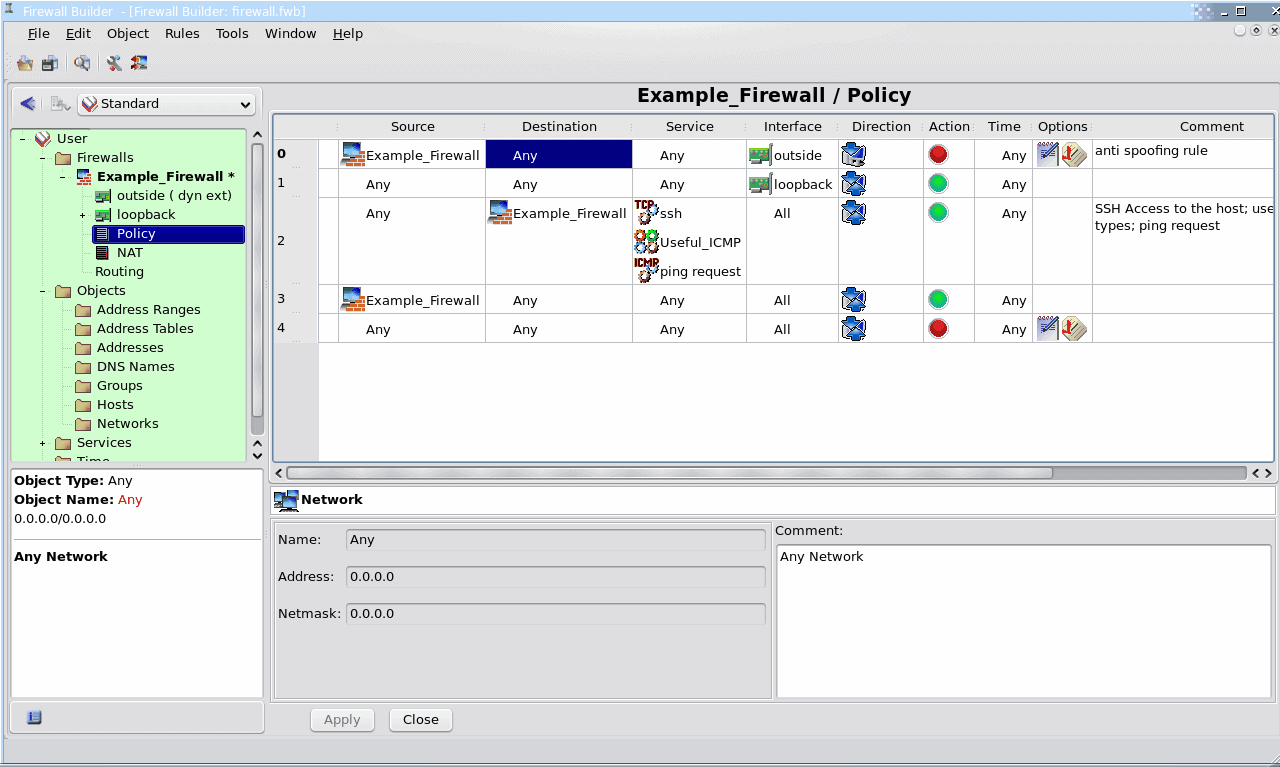
The first thing you can do is expand the name of the firewall (in my example I would Example_Firewall) and select the object you want to view. Say you want to view the Policy of this firewall (remember this was created from a template so there are already rules applied). To do this click the "Policy" listed (once you expand the firewall) which will reveal the policy in all its glory.
Because this is a template you can not edit the objects. This is one of those that you chose based on a specific, yet simple, need.
In the image to the right you can see the details of the policy included with the single interface firewall template.
If you want to create a custom firewall you would go through the same process but, at the point where you are defining your firewall you wouldn't choose the Preconfigured Template. Instead you would leave that option unchecked and then, in the next window, choose to "Configure Interfaces Manually". At this point you would add objects as needed and configure those objects to suit your needs.
Once your firewall is built you must then save the firewall, compile the firewall, and install the rules. Here's the kicker with configuring your firewalls manually. You will need to know the MAC addresses of your interfaces. Fwbuilder has built in SNMP discovery which will help to map out the various interfaces on your network. To use that tool go to the Tool menu and select Discovery Druid. This tool should keep you from having to manually find and associate MAC addresses.
Final Thoughts
The fwbuilder tool is an outstanding means of creating firewalls for any situation. This article gave you a cursory glance at this powerful tool. Give it a try and build a firewall. Try the templates and, once you are familiar with the tool, build your very own customized firewall.
Advertisement















Paul’s got it down. Most users, even experienced user’s aren’t ready to program their own firewalls. More importantly a simple transport layer port blocker is no longer enough. An application aware firewall is my recommendation for most users. Having the ability to allow Firefox to access the Internet while blocking Internet Explorer from doing so is invaluable. Additionally being able to treat local “trusted” (I use that word very loosely) networks differently than untrusted or Internet networks is just as important. The Best solution I’ve found (for windows) is Kerio firewall (originally tinyip firewall). I don’t use the latest version (except on my laptop required for wireless nic support). I use v4.2.2 (you might be able to find it here by a search: http://www.oldversion.com/)
I do NOT recommend this for most users. It requires a user to pay attention. For friends and family they get to pay for Norton 360 v3 (which installs in under 90 seconds!).
But for those who can manage their own firewalls it works great. I go to many customer sites as a consultant and each time a new network is detected I can choose whether it is trusted or untrusted and treat it accordingly (like disabling rpc on untrusted networks). I find it very easy to use. It never gets the highest ratings but it does exactly what I need it to do without taking over my system.
-Joe
Great tip jack, Looks not to hard.