How to surf anonymously on the Internet
Before we look at techniques that allow you to browse the Internet anonymously, we should take a moment to answer the question why someone would want to do so in first place.
Why would someone with no illegal intention want to browse anonymously at all? I can think of lots of reasons, here are a few:
- You come from a country where free speech is only a theory. Countries include China, North Korea, most predominantly muslim countries, Germany and France for instance.
- You work in an environment that prohibits access to parts of the internet.
- You write about a certain situation and want to make sure no one knows that it's you, for instance you blog about your current job or the situation in your home town.
- You dislike that the government tries to track everyone and everything on the internet.
- You are paranoid
Hope that's settled now. Let us start with the methods and technology to stay anonymous.
Before I start I would like to remind you to use common sense as well. It does not help you if you use a proxy to post on a message board but use your real identity there. The same principle is valid for all other means of communication. Don't mention information about you that someone else could use to track you down.
I will discuss the following methods to stay anonymous on the internet: a) web proxies, b) proxies, c) tunneling software, d) cookies, spyware and the like.
Update: VPN added to the list of options
VPN Services
A VPN, or virtual private network, is basically another computer system that your traffic gets routed through. Most VPN services are paid, but there are some free ones available but those are usually limited.
The server you connect to using VPN software sits between your device and the Internet. Any service or site you access interacts only with the VPN and not with your computer directly; this means that these sites and services don't interact with your device's IP address but with that of the VPN server.
Downsides to using VPNs are that you have to pay usually to use them (and figure out a way to make the payment).
Check out the VPN Comparison chart for information on many VPN services.
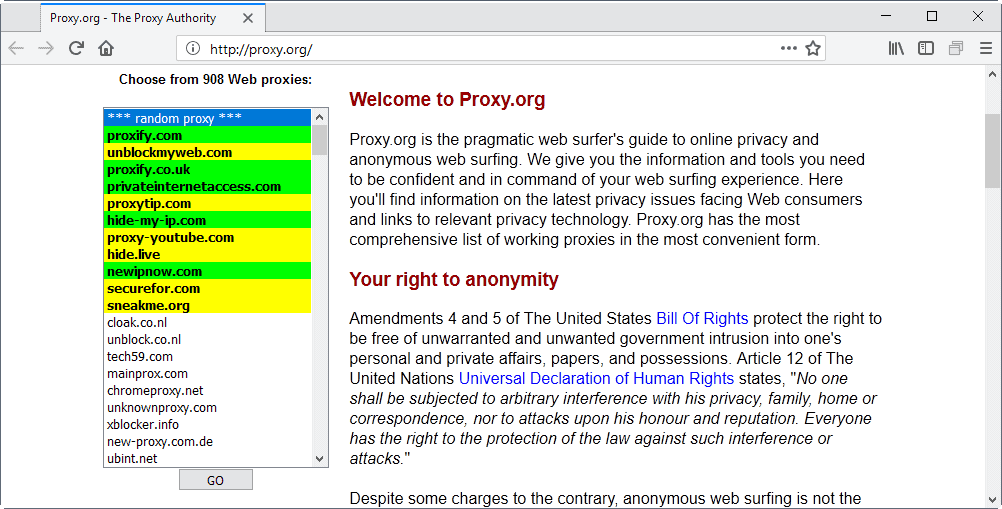
Web proxies
Web proxies are a great way to stay anonymous with almost no work required on your side. You open the url of the web proxy, enter the url you want to visit and visit the site you want to visit using the IP of the web proxy. Easy and fast method that has some problems as well.
First, it might not support all scripts that the site you want to visit uses.This does not necessarily has to be a problem, as it may only affect the site's design or a functionality you do not use at all. Sometimes however it may render features of the site useless so that you can't use it for whatever activity you want it to use. If that's the case try different web proxy server.
The servers can easily be blocked by a firewall or other means of blocking scripts / urls. If that is the case you can try and setup your own web proxy. All you need is web space that supports php / cgi. You then have the advantage that only you or a few people know about this proxy and it's less likely that it will be banned. You can try cgi proxy or php proxy or search the web for more scripts.
A word of advice. Don't pay for a web proxy service. Most payments can be tracked. Good lists of web proxies can be found at ghacks.net and proxy.org
Another disadvantage of web proxies is that you don't know usually who operates them. This is a problem, especially since you don't know whether logs are kept or if your activities are logged.
Proxies
Unlike web proxies, proxies are mere IP addresses that route your request to the destination. The important factor if a proxy can be used to hide your identity is if it spills your IP. It does not make sense to use a proxy to stay anonymous if the destination sees your IP and not the proxy IP.
That means you will have to check proxies before you are using them. A program that does this is charon by my friend rhino. It checks the proxies for speed and anonymity. Now, all is left is to add the proxy to your browser and check a site for your IP. If it shows the IP of the proxy you are surfing anonymously. Beware that certain scripts and plugins, like Java, are may still reveal your real IP to the server you are connected to even if you are using a proxy.
Firefox has some great proxy extensions like Proxy Switcher. You probably would like to know where you get the proxies that you check in Charon? You can perform searches for proxy lists, visit irc or scan for yourself for example.
Tunneling software
Proxies have a big problem. If one monitors the proxy one does know what anyone who uses the proxy is doing. It's a good idea to use a proxy server that is not located in your home country. The US government will have problems asking a North Korean proxy server owner for their server log or access to it. It's not likely that this is ever going to happen, but still possible.
But, the possibility exists and it's always good to be on the safe side. Tunneling tools allow you to use software on your computer that do not support proxies in first place so that they can be used with proxies. Some simply require you to enter a proxy in the tunneling software and you are free to go, others encrypt your data transfer and route if through several servers to make sure no one is able to find out about the source and destination and the data itself.
Tor is one of those products and it could be a good idea to take a look at the software which is hosted at the eff website. Jap anonymity and privacy is another tool that might be worth looking at
Cookies, spyware and the like
This should be common sense but I thought I add it anyway to the article. Other tracking methods exist that do not rely on the IP address. This includes cookies for instance: take a look at the excellent wikipedia article about cookies if you want to find out more about cookies.
Spyware is another threat that may track your movement on the Internet: make sure you scan your system regularly with up to date security software such as Spybot Search and Destroy or Malwarebytes Anti-Malware.


















How to surf anonymously online? Has good points and bad points. Some people argue that the only people that would want to do such a thing in the first place is because they have something to hide.
J7LpWy hi! how you doin?
I and my children have been receiving abuse /harrasment mail from this service for the past 3 year and I would like it to stop .I have had to change my email details many times.it is an invasion of privacy. it is stalking !
Hi,
Until today I was using https://secure.vtunnel.com as a web based proxy for checking my yahoo mails, gmail and orkut. But now it seems that the url is blocked. I have tried many other proxies too, but it seems that they too are blocked. Can you please help me?
Another thing I wanted to ask is what is the difference between http and https ?
Thanks and Regards
Debopam
funny that you think I´d be from the USA..
great to read the thoughts of americans abaut germany and france.
but please don’t try to introduce free speech in our countries.
thanks man ^^ n greeting from Malaysia where free speech is also
prohibited,but we will keep kicking ass man ! ^^
You can use Tor that is easy to use.
http://tor.eff.org/
First of all, great site, it helped me feel secure online again. :-)
Secondly, I don’t think you should put Germany and France in the same category as China.
They’re both EU countries so freedom of speech is not only a theory (far from the other countries you mention).
Ok, French organizations LICRA and UEJF sued Yahoo for allowing the sale of Nazi memorabilia on its auction sites and cases similar like this are going on in Germany (sensitive issue).
I agree that this is wrong, but i wouldn’t say they are actively censoring parts of the internet like China and Korea do.
And what has dvd copy software (directly) to do with freedom of speech and censoring peoples thoughts?
(banning software isn’t censoring)
See: http://en.wikipedia.org/wiki/Internet_censorship for some really bad censoring stuff.
Don’t get me wrong i agree with you 100%, but i had to say this after seeing China and Germany in the same sentence.
well free speech is a theory because certain websites are banned in germany / parts of germany and france.
Take a look if you are german or can translate it http://www.odem.org for instance is a good site that covers the topic.
You can get sued in Germany for instance for posting a link to dvd copy software that copies the dvd although it has a copy protection.Many websites are banned already from major search engines like google. Some are even banned using dns.
and whats your definition of free speech :-)
why is free speech in germany and france only a theory?
Very informative post…. Great work, thanks. Oh, and do keep it up…