Microsoft Edge 112 ships with security fixes and improvements

Microsoft has released Microsoft Edge 112, a new stable version of the company's web browser. Edge 112 is a security update first and foremost, that follows the regular Chromium release schedule. Google published Chrome 112 earlier this week and addressed a total of 16 different security issues in the browser.
Microsoft Edge 112 includes 16 security fixes for the desktop versions as well, but two of them are specific to the browser. While Chrome and Edge share the same core, which is called Chromium, they do contain code that is not necessarily open source but unique to a specific browser.
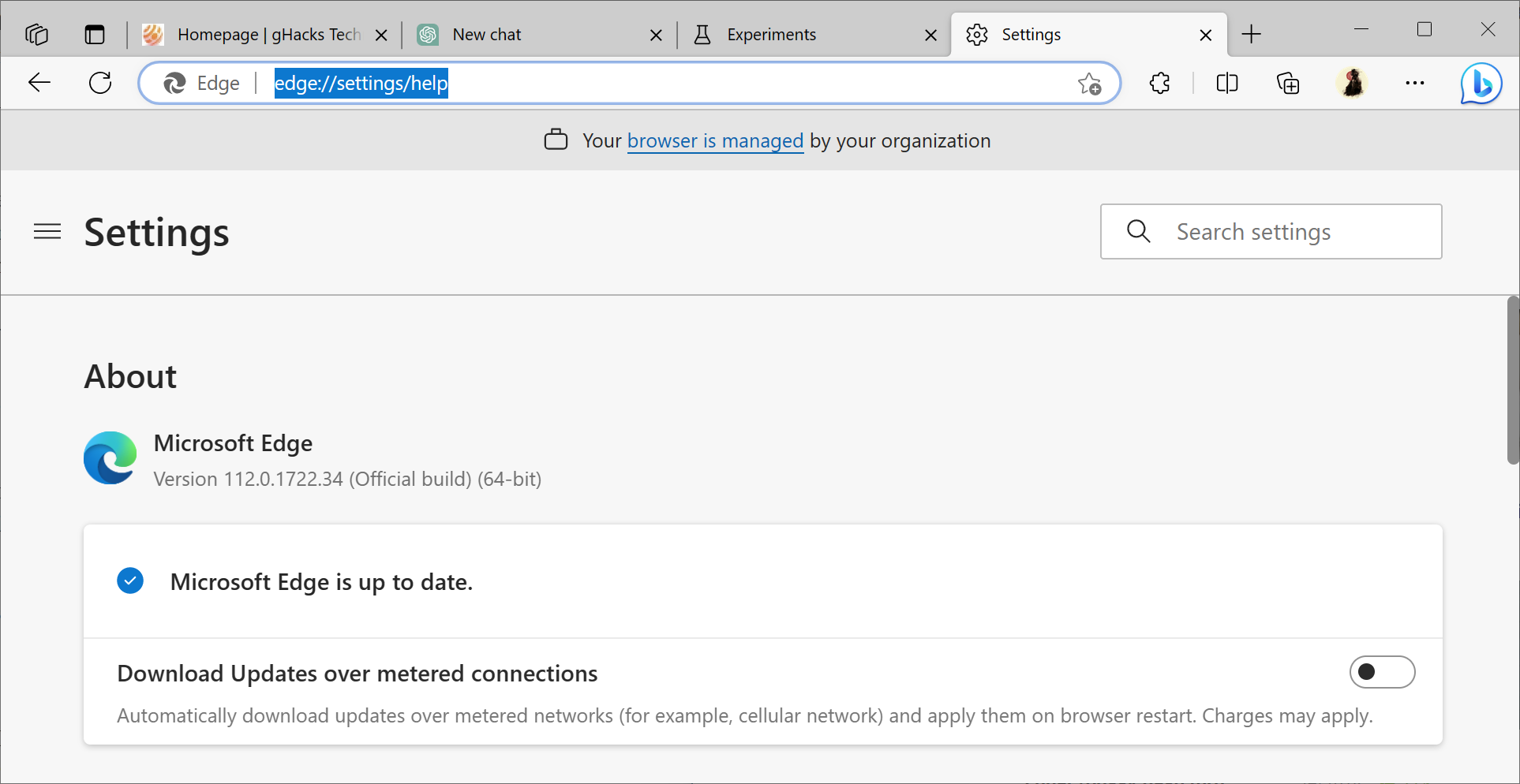
Microsoft Edge updates itself automatically on most systems. You may load edge://settings/help to display the current version or use Menu > Help & feedback > About Microsoft Edge to open the page. The page executes an update check, and any new version is downloaded and installed automatically at this point.
As far as the Edge-specific security issues are concerned, there are three, but one is specific to Edge on Android. The severity is either moderate or low, and none appear to be exploited in the wild.
- Microsoft Edge (Chromium-based) Security Feature Bypass Vulnerability -- CVE-2023-28284
- Microsoft Edge (Chromium-based) Spoofing Vulnerability -- CVE-2023-24935
- Microsoft Edge (Chromium-based) Tampering Vulnerability -- CVE-2023-28301
Microsoft Edge 112: non-security changes
Microsoft Edge 112 is a rather light release when it comes to new features. The official release notes are published here, and they include five feature updates.
Enhanced Security Mode, is an optional security feature of Microsoft Edge, which is designed to reduce attack surfaces. It does so by disabling the Just in Time compiler and enabling additional security protections, if supported by the operating system.
This feature now supports WebAssembly for ARM64, ensuring cross-platform support across 64-bit versions of Windows, macOS, Linux and Arm64 systems.
As for the other features, there is a new in-browser JSON viewer that includes several improvements, such as a "color-coded tree view with line numbers and the ability to collapse and expand the data". JSON files are opened automatically in the viewer, if they are accessed on webpages. or when local JSON files are opened.
The feature is rolling out over time, but interested users may enable it right away using the following instructions:
- Load edge://flags/#edge-json-viewer in the browser's address bar.
- Set the status of the feature to Enabled.
- Restart Microsoft Edge.
The three remaining features affect policies. The first updates the new tab page policy. The NewTabPageHideDefaultTopSites hides default top sites when enabled. Microsoft extended this to include sponsored quick links as well, which are now also hidden when the policy is enabled.
WebAppInstallForceList is a new policy for Microsoft Edge. It may be used by administrators to "configure a list of web apps that install silently, without user interaction, and which users can't uninstall or turn off".
The third policy, CryptoWalletEnabled, enables Microsoft Edge's Crypto Wallet feature.
Now You: have you tried Edge lately?
















>”WebAppInstallForceList is a new policy for Microsoft Edge. It may be used by administrators to “configure a list of web apps that install silently, without user interaction, and which users can’t uninstall or turn off”.”
Wow, that sounds really unpleasant. I guess Microsoft is more than happy to help companies spy on their employees with keylogger extensions.
I rarely use Bing but when I do I like it to be current. Thanks for info.
JavaScript JIT can also be disabled in other Chromium browsers, however it still affects sites that use WebAssembly. What happened to Microsoft implementing Enhanced Security Mode changes upstream to the Chromium project – have they ditched that idea?
The “enhanced security mode” is one of the worst explained settings of MS Edge. It’s not clear at all what these protection layers do in each different available level because all the three levels are not transitional between them. This means that you can’t set the different optional protection in the levels, just because they are based in other criteria like the number of times the site is visited or other criteria like the “importance” of the site that is open by the user. This security mode must be rebuilt and let the user to choose which layers should be enabled in order to increase the protection by yourself: 1) first layer would JIT of course, 2) second optional layer should be the hardware-enforced stack protection (aka arbitrary code protection), and 3) the last layer should be the control flow protection. This will give you exactly what you should want when applying layers to the visited sites, not letting the browser to choose weird criteria to apply the layers of protection according to some kind of “visited” or “cookies” factors. Thanks for the article by the way!
I noticed that Martin and Ashwin’s articles always have a summery box at the end but none of the newer authors ever do. Why so?
Probably because those two write the articles for gHacks, the others are probably copy-pasted from some other website and the article formats don’t match.