The Hidden Threat: Bitwarden Password Manager Targeted by Phishing Scams

Scammers are targeting users of cloud-based password managers, including Bitwarden, with phishing attacks. And the mode of attack was malicious ads.
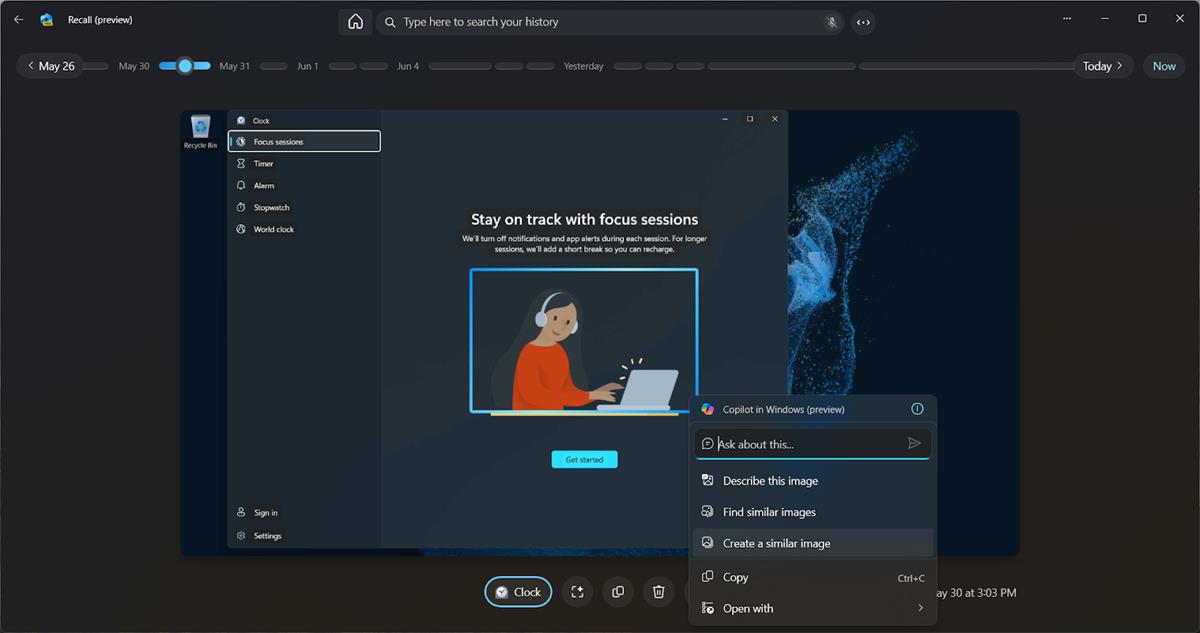
Users have reported that they have seen fake advertisements for Bitwarden on Google, the links in the ads were however not related to the password manager's websites. The above image is from a reddit user who posted it a couple of days ago. This particular website closely resembles Bitwarden's login page. Now what would happen if a user entered their username and the master password that unlocks their vault, and the scammers get hold of that information. The attackers could try using the obtained credentials and login to the accounts on Bitwarden's servers, to steal the contents of the password vault. But these phishing campaigns are actually a little more sophisticated, hackers often steal authentication tokens too.
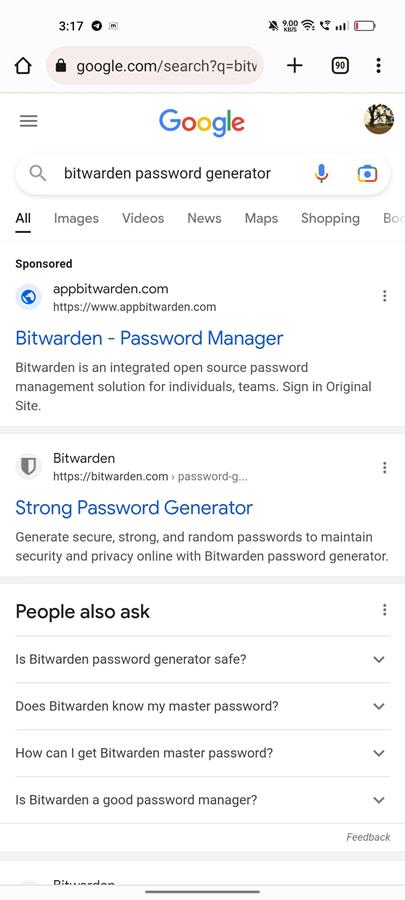
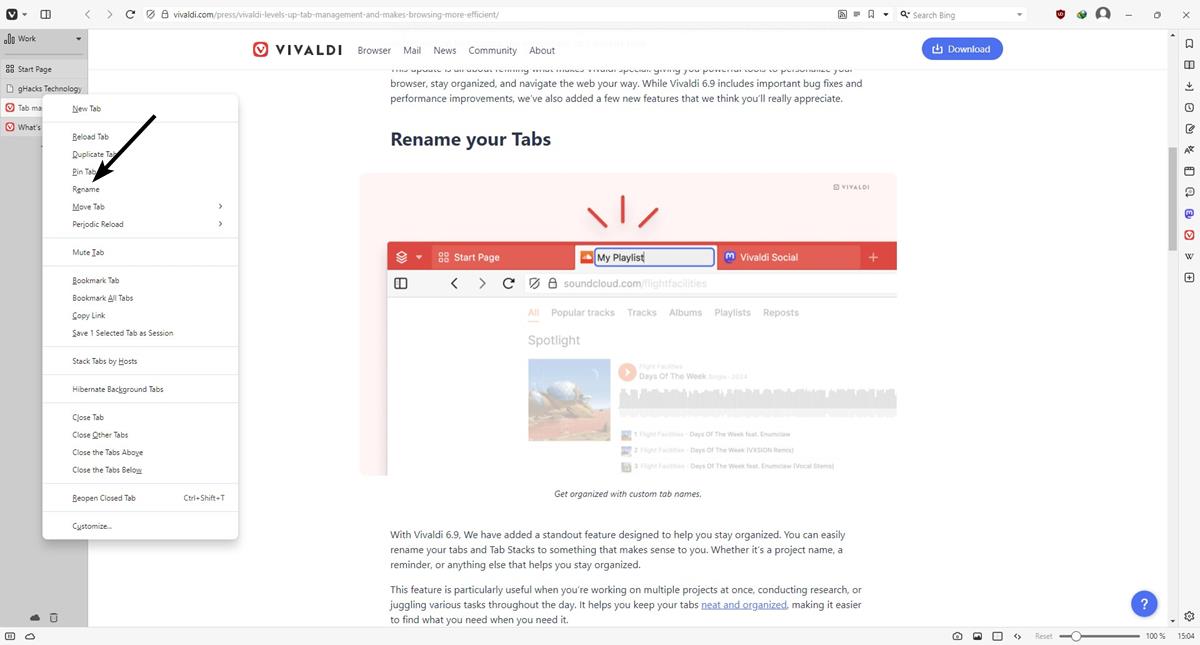
Here's a look at the malicious ad (h/t reddit), shockingly these malicious pages were placed at the top of the search results, above the legitimate URL itself. Do you see what happens when you don't use an ad blocker? uBlock Origin is my recommendation, feel free to check AdGuard or something else that fits your bill, just make sure it's a reputable extension/app, do your homework.
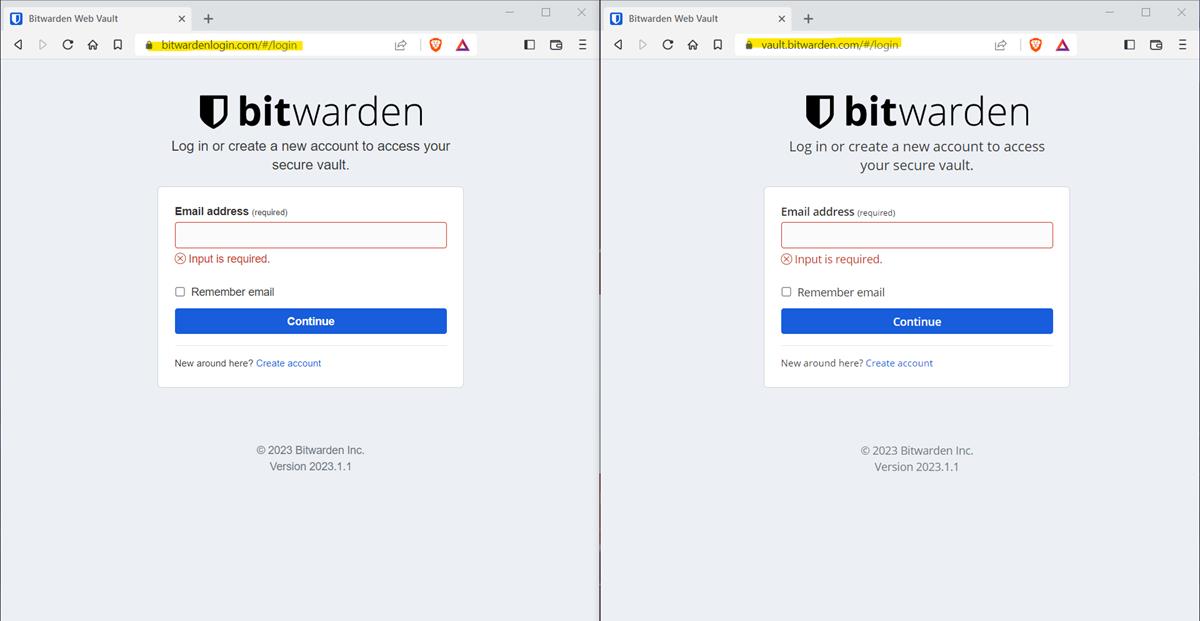
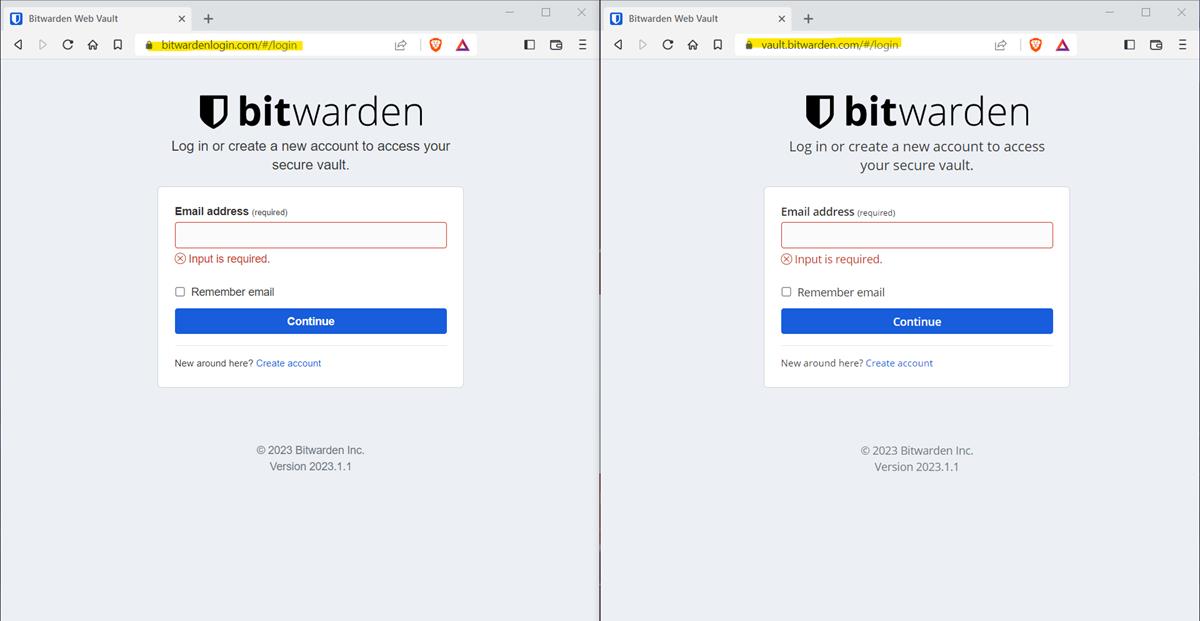
Another Bitwarden user created a thread on the company's support portal, to alert others about the website that was trying to impersonate the official website's login page. It is quite alarmingly similar, isn't it? Everything from the fonts, icons, and other elements on the phishing site looks identical to the original login page.
BleepingComputer says it ran some tests by entering some credentials on the site, but once it accepted them, the malicious web page redirected users to the official Bitwarden site. The writer states that they were unable to test the phishing page with real login information, or authentication tokens, as the site was taken down by then.
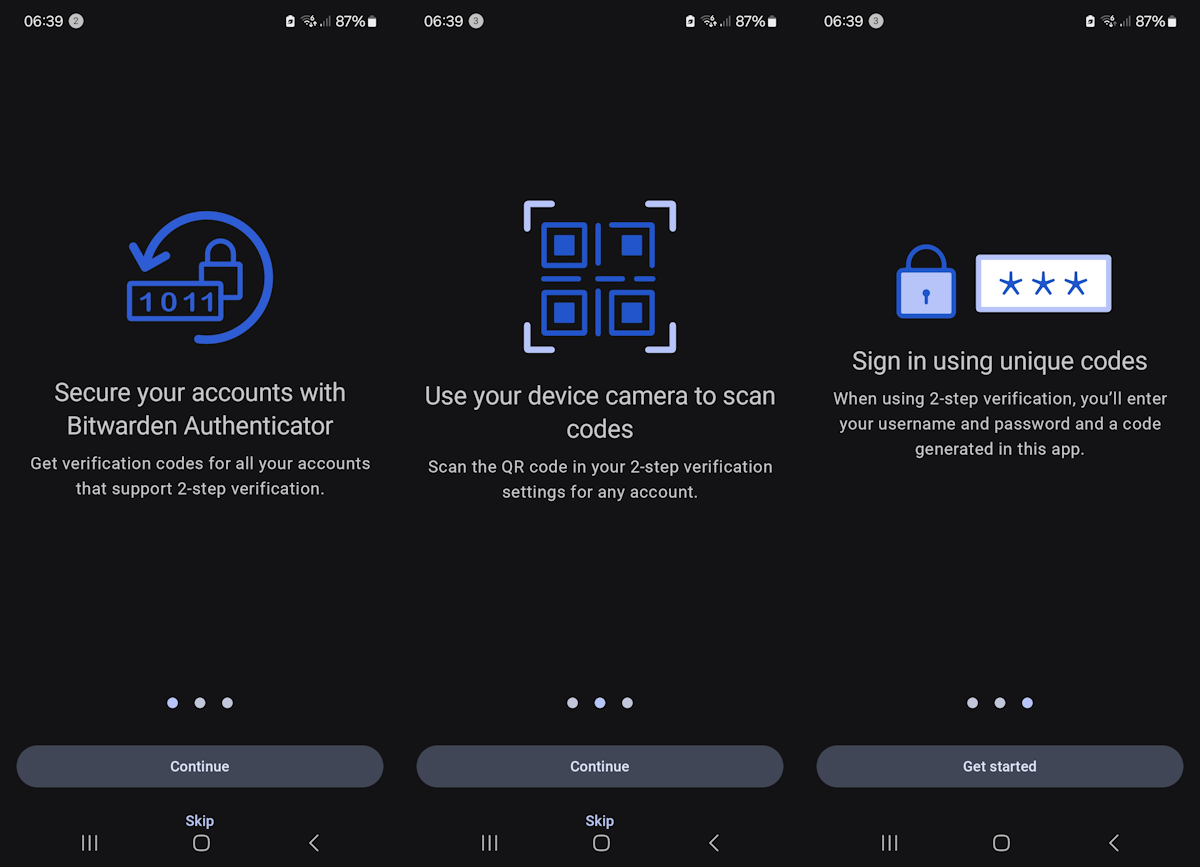
I suppose users might still be safe if they have 2-factor authentication enabled for their accounts, but still, this is pretty scary. It emphasizes the need to check the URLs with a close eye. If you want to access your web vault, you can use the Bitwarden Desktop app's Help > Go to vault option to access the correct web page, which is https://vault.bitwarden.com/. You may want to save that to your browser's bookmarks. Users of the Bitwarden browser extension for Firefox and Chrome can access the page by clicking the add-on's icon > Settings > Bitwarden web vault. Make sure you use a strong and unique master password, enable two-factor authentication (2-step verification) on your account, and pay attention to the web page that you are on before providing your username and password to it.
Malvertising and phishing attacks could happen to any cloud-based password manager or any cloud service for that matter, Bitwarden users aren't the only ones who have been targeted by these, MalwareHunter reports that a similar phishing campaign was used to lure and trick 1Password users, also using malicious ads on Google. This is a serious problem. Recently, Norton Password Manager users were victims of a password stuffing attack. The biggest password manager breach in recent times (biggest in history?), was of course the LastPass incident, which resulted in hackers gaining access to cloud servers that contained the password vaults of the company's users.
I'm never going to stop recommending KeePass to people who are afraid of cloud services. KeePass is free, open-source, works offline, supports physical security tokens, has excellent forks and ports for iOS, Android, Linux, macOS and Windows. What's not to like about it? Even if you do use cloud-based services, you should consider exporting a copy of your password vault and import it to KeePass. This way, even if the cloud-app suffers an outage, you won't be locked out of your accounts.












Phishing scams are the Darwin awards of the internet. Those who are so utterly clueless even today about clicking on shady emails, not using a freaking adblocker and lastly, not even bothering to check the name of the website they’re going to (appbitwarden dot com vs bitwarden.com? Really?) totally deserve to get hacked and lose their data.
The public internet will have its 30th anniversary today. To remain so ignorant about online scams that date to the early 00s is like a licensed car driver who doesn’t know the difference between the brake and the accelerator pedal and claims that it is ‘too technical’ to learn.
The gullibility of some people is incomparable, indeed. I wouldn’t say that they ” totally deserve to get hacked and lose their data.” because gullibility is not a sin. It remains a pity that being hacked for such reasons is the only way for some to learn their lessons, those of being aware. Not to mention the impact on all : like drugs, no demand, no offer. Because in a certain way not being aware is a demand for troubles.
There needs to be a ‘how to be safe on the internet 101’ updated course for these people, before they ever start using the net.
@Ashwin. The term is not “Bitwarden Password Manager Targeted by Phishing Scams”. The target is not Bitwarden but aspiring users.
> Even if you do use cloud-based services, you should consider exporting a copy of your password vault and import it to KeePass. This way, even if the cloud-app suffers an outage, you won’t be locked out of your accounts.
Bitwarden stores an encrypted copy of your vault on all clients, just like Keepass.
If the cloud-app suffers an outage, the only thing that breaks is sync between devices. Bitwarden works as well as Keepass does during any outage.
TBF the article is talking about Web page access rather than extension/desktop app, so vault wouldn’t be cached.
OTOH keepass *requires* the desktop app so a fair comparison would be to the bitwarden desktop app, in which case, quite right.
I’ve been noticing many different sites being advertised such as my bank and best buy even that when clicked through look almost identical to the site just in the last month. These phishing scams are getting ridiculously common.
Just enable 2 factor Authentication and you will be fine
Yeah Anon, I was about to say, easiest way to defeat is to either use extensions and desktop app, no need to look for or remember url once set or you can memorize the domain name which is kind of simple, only danger there is I suppose, mistyping, in which case, make a bookmark
Here’s a very easy way to prevent this, use the extensions and desktop apps only
+1 for KeePass.
However, I do recommend Bitwarden for non-techies that want a cloud-based solution. The attack here is easily mitigated if they’re using an adblocker (ideally, at the VPN level), which is always my first recommendation.
Used keepassx for almost 15 years. Switched to bitwarden because concurrency with keepassx is not a thing really. So many times my wife and I making changes to the same shared vault or doing things at the same time causes issues.
If you’re single keepassx with Dropbox or next cloud sync is the best. If you have a family and need to share info bitwarden or 1password are the best I have found with the latter being completely crappy experience on android devices. So self hosted bitwarden is absolutely better than keepassx I’d you have any kind of sharing going about.
Same. Very long time keepass with owncloud/nextcloud user but am now creating a self hosted vaultwarden for sharing those utility accounts with my wife since utilities still only allow one login, and sharing with keepass is not that easy, which makes changing utility providers more difficult.
I’m finding the bitwarden browser extension is allowed at work too, whilst keepassxc is not.
all my accounts are 2FA hw key protected so no fear at all to use a cloud pwd manager. that sai Bitwarden is my preferred choice.
wq!
The only thing I hate about Bitwarden is their use of CloudFlare for online vault. That makes it impossible to check the website validity by examining the certificate.
They do have a self hosted option
Longtime I have some fear to use cloud based apps, most likely also pw managers; not for nothing it seems now.
I am using KeepassXC and are happy with it.
phishing campaign that buy google ads
just like all sponsored post in meta cannot be trusted
There getting into people’s Google accounts to create Ads, it recently happened to me about 7 days ago.
:What’s not to like about it?”
It store passwords in an encrypted file (vault). This file can be hacked, stolen, broken, confiscated, damaged, etc.
The better alternative is to use generated on demand passwords, which are not stored in any place.
https://www.publish0x.com/simple-solutions-to-complex-problems/a-simple-way-to-create-unhackable-passwords-xeenglp
Second reply:
I did a bit of reading about dynamic passwords and came across lesspass.com. This seems like a much more workable solution. However, it still has a lot of usability problems. In its pure form (no profiles, no syncing) you have to give the tool the correct master password as well as the correct website you’re logging in at, and spell out any special restrictions that the website might have for passwords (I would never want to memorize these and they aren’t made clear when trying to log in.) Not to mention you can’t change your master password without invalidating every password you’ve generated with the site (though I suppose you don’t really need to change it if it’s unique since you aren’t ever transmitting or storing it anywhere).
A cool idea but still inferior in usability to a simple synced vault.
If I’m reading this guide correctly, you have two lists of passwords that you Frankenstein together to generate “stateless” passwords for all your services? Instead of remembering the password I have to remember the countless procedures that I used to generate the passwords for my scores of online services…and each time I need to input those passwords I need to have both of those initial lists handy? That might be the least practical password solution I’ve heard of. I can’t think of a single person I know who would be willing to do that, certainly not myself.
An encrypted file vault with one strong password that you have to remember is way, WAY better. It can’t be hacked like you’re suggesting as long as your password is decent, and all of the scenarios you listed are practically impossible or not concerns. We could argue whether it should be hosted on a cloud based service or not but the vault itself is certainly a better solution than dynamic passwords.
KeePass and sync the database with your own services all you really need. None of this Bitwarden, lastpass nonsense.
What about Bitwarden is inherently insecure, pray tell?