Tricking antivirus solutions into deleting the wrong files on Windows
Security research Or Yair discovered a method to trick antivirus and endpoint security solutions into deleting legitimate files on Windows systems. Yair found out that he could manipulate endpoint detection and response and antivirus programs so that these programs would function as data wipers on Windows devices.
The discovered security issue can be exploited from unprivileged user accounts to delete system files and other files the user has no delete permissions for. The exploit could be used to remove important files from a system and this could result in an unbootable system or a system that lacks certain functionality.
Classified as a data wiper, a class of malware designed to erase data on computer systems, its main purpose is destruction. Wipers are commonly used in cyber warfare, often to support physical aggression or to target the enemy's infrastructure.
Wipers need to bypass certain protections, including those provided by a user permission system but also defenses that are in place to protect against unauthorized deletions of files. Additionally, to make sure that files can't be recovered, wipers need to overwrite file contents.
Endpoint security and antivirus solutions would make excellent file wipers, if security issues could be exploited to use their privileges and capabilities. Yair had several ideas in this regard, but most were not practicable. Some required elevated privileges, others write access to the files in question.
The main idea that he came up with was to create a malicious file in a temporary directory, and to redirect it to an important file on the system between the time the security solution detected the threat and deleted it. This method did not work out as planned initially, as some security solutions prevented access to detected files while others detected the deletion of the file and dismissed the pending action.
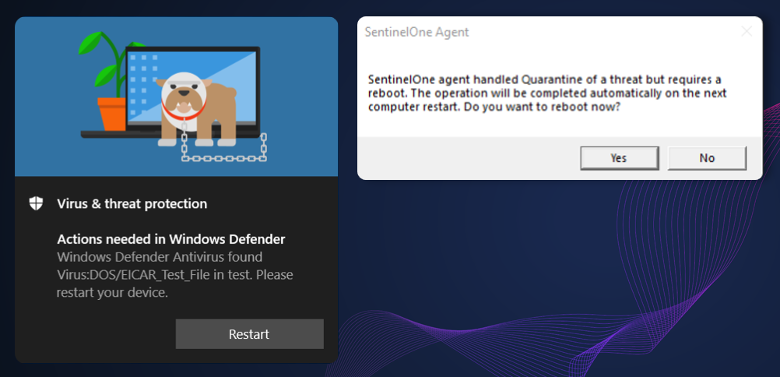
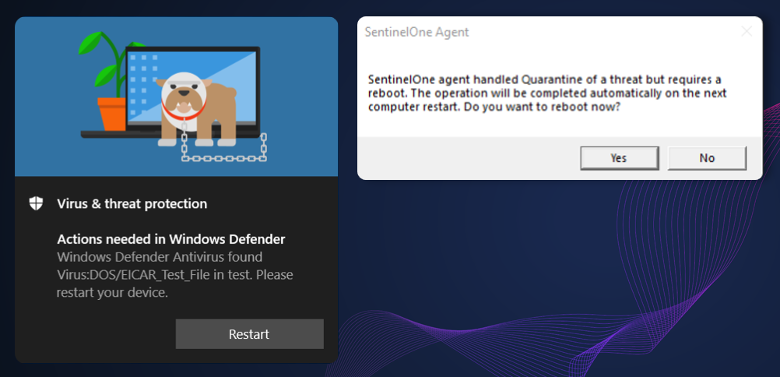
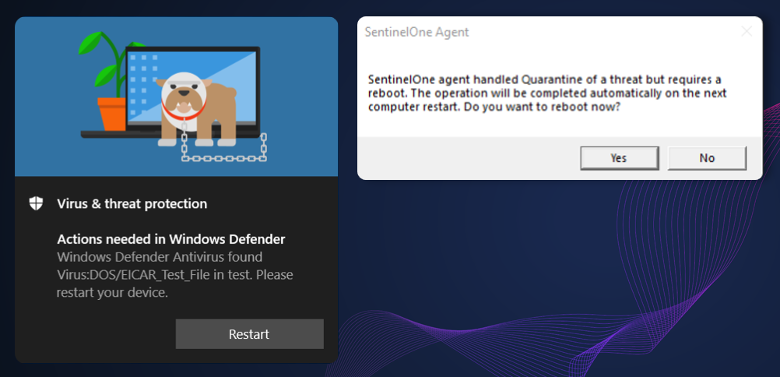
Yair's solution was to keep the file open, so that it could not be deleted by the security solutions right away. The security programs would prompt for a reboot in that case so that the malicious file could be accessed and deleted. Files are added to a specific key in the Registry, so that Windows knows what to delete during the boot phase. Yair discovered that the deletion process would follow junctions, created to point the delete operation to a legitimate file.
In other words, all it took to delete legitimate files on Windows was the following:
- Create a malicious file on the system using a special path.
- Hold it open so that security solutions can't delete it.
- Delete the directory.
- Create a junction that points from the deleted directory to another.
- Reboot.
Yair tested 11 different security and endpoint solutions. Six of these were vulnerable to the file wiping exploit, including Microsoft Defender, Microsoft Defender for Endpoint, Avast Antivirus, SentinelOne EDR and TrendMicro Apex One. Microsoft, TrendMicro and Avast/AVG released updates already to address the issue.
Now You: which security solution(s) do you use? (via Bleeping Computer)





















Wipe and install Linux, now that’s the ticket!
“Now You: which security solution(s) do you use?”
HAHAHAHAAHAHAHAHAHHAHAHAHHAHAHA
He said security. LOLz!
Interesting discovery. But like many exploits it requires numerous steps for success. The first and biggest is that one would have to visit a website hosting such a malicious file or receive it via email. Or a bad guy needs physical access to the computer which is game over and it’s no longer your computer. But I digress, the point being the first step would require action on the part of the person behind the keyboard which can be easily defended by utilizing some critical thinking skills so such a malicious file never makes it to the system. Thus why the person behind the keyboard is considered a major layer of defense. But also why it is not good practice to rely solely on anti-malware to keep a system safe. It only gives a false sense of security.
That’s why I only trust DeepFreeze to secure Windows.
A reboot and C:\ would back into previous state. Installation of new programs would be the admin’s responsbility.
After years of problems with Citrix Provisioning, we finally began adopting DeepFreeze.
Really interesting idea. Thanks for covering this
Most interesting article, and relevant : the art of using your opponent’s strength, as with Judo.
> “Now You: which security solution(s) do you use?”
I’m afraid I use none, at least in terms of dedicated security software.
I intensively focus on connections, system-wide. Applications/software are checked carefully before their install as well as their connections if any. 99% of connections are established here via the browser, Firefox in my case, Firefox only, enhanced to the ultimate of what i’m aware of via native prefs plus dedicated extensions, of which the ‘Netcraft Extension’ which I enable when knowing I’ll be either visiting red light districts and/or be in the situation of having to provide confidential data on a new site. Windows defender here on Win7 is disabled.
I’ve used several security applications in the past, mainly Kaspersky ones. I ceased using any the day I realized the authority over Kernel, the power, the deep Registry imbrication these apps/software had, the challenge it was to remove them — fully – from the OS… together with the fact it did slow down my overall device velocity.
I’m not stating in any point that I’m right and I certainly would NOT advise this to any starter, newbie. What I can say though is that I haven’t encountered the slightest intrusion within at least 10 years running the OS free of any dedicated security software … provided all my other global system defenses were and are in place.
If I disappear from the Ghacks radar it’ll be that either i’ve moved on to paradise (the island or up there), or that hell has made its way to the OS :=)
{ Applications/software are checked carefully before their install }
Does nothing to ensure you don’t load a well-designed zero day issue, as I am sure you know. So how do you manage detection of such things post-installation?
FWIW I’ve had nothing other than the CCleaner virus, installed the same day it emerged (but have cleaned up quite a few problems at work). I uncovered CCleaner’s dirty little secret very soon after installation via Autoruns’ VirusTotal scanning.
Well I don’t think this is a scenario one would have to worry about very much in real life, as it does pre-require some active malicious user already having access (physical or remote) to your computer’s file system, so as to create a new file, keeping it open, and creating symbolic links. Unless, of course, you’re in the habit of granting strange outsiders that level of access?
Also, I never let my AV auto-delete files all by itself. I always have it show clearly what it wants to quarantine or delete anyway, with the actual file name(s), so I can check first if it’s not some kind of false-positive. Well, but now I have to admit, perhaps this junction strategy outlined here might circumvent this, by suggesting incorrect file paths instead of the actual ones…
Luckily I use a file manager (Xplorer2) that, in any folders/files list view, makes symbolic link / junction names jump off the screen by marking those in a special color. I always thought this was just a handy time-saving feature, but now it looks like it could be a safety feature too!
Off-topic tip to other Ghacks users: I edited my Ghacks bookmark, setting it to
https://www.ghacks.net/author/martin/
This will give you some semblance of the original Ghacks, as the page will list only the latest posts by the single really interesting author here (Martin Brinkmann) — without showing all this Shaun-Devaney-Microsoft-Softonic spam nonsense that since recently is so unfortunately flooding this site.
@Henk,
Ghacks’ footer ‘About gHacks’ displays 3 names : Martin Brinkmann, Mike Turcotte and Ashwin. A 4th, the Microsoft aficionado, isn’t mentioned. Together with Martin of course Turcotte and Ashwin remain reliable IMO and have provided worthy articles.
I want to trick my antivirus to detect:
– Edge
– Windows Security
– Teams
as viruses and actively delete them as soon as they reinstall.
Interesting article Martin as always, a worthy read.
We for years have trusted ESET (and more importantly, commonsense) on the computers on our network. ninety five percent satisfied. I never would or let any AV/AM make full decisions. I prefer interaction mode with ESET to set policies.
Heidi-Ann