LastPass: some users report compromised accounts

Some users of the LastPass password manager revealed this week that they have received emails from LastPass stating that logins to their accounts using the account's master password were blocked. The first of these reports was published on Hacker News.

Update: LastPass issued another statement on December 30, 2021. In it, vice president of product management, Dan DeMichele, suggests that at least some of the security alerts were sent out in error to users. End
The emails that are sent out by LastPass state that LastPass blocked a login attempt. In the case of the thread starter, the login attempt came from Brazil.
Login attempt blocked
Hello,
Someone just used your master password to try to log in to your account from a device or location we didn't recognize. LastPass blocked this attempt, but you should take a closer look.
The emails are legitimate emails from LastPass, not phishing emails. The attackers managed to gain access to the master password of the customer. It is unclear how the attackers managed to obtain the data, possibilities include malware that is running on user systems, old data from past breaches, data that was used in other online accounts that were compromised, or a new security issue.
Bleeping Computer published a comment from LogMeIn Global PR/AR Senior Director Nikolett Bacso-Albaum, which suggests that the data comes from third-party breaches and that the attacks are coming from bots.
LastPass investigated recent reports of blocked login attempts and determined the activity is related to fairly common bot-related activity, in which a malicious or bad actor attempts to access user accounts (in this case, LastPass) using email addresses and passwords obtained from third-party breaches related to other unaffiliated services.
LastPass has no indication that accounts were successfully accessed or that its service was compromised, according to the response.
Some of the users who reported the issue online stated that their master passwords are unique and not used elsewhere, which, if true, eliminates the third-party breach scenario.
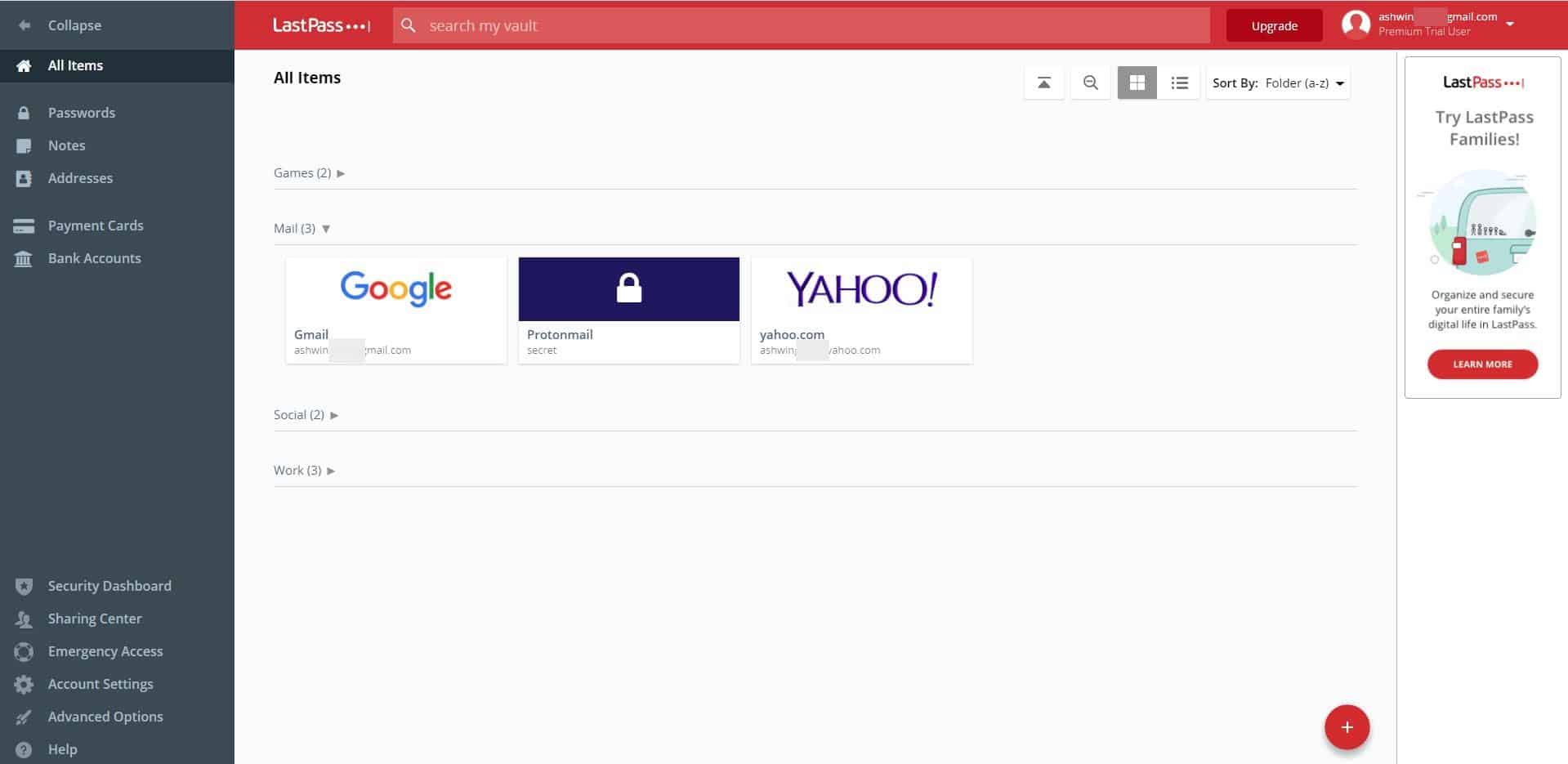
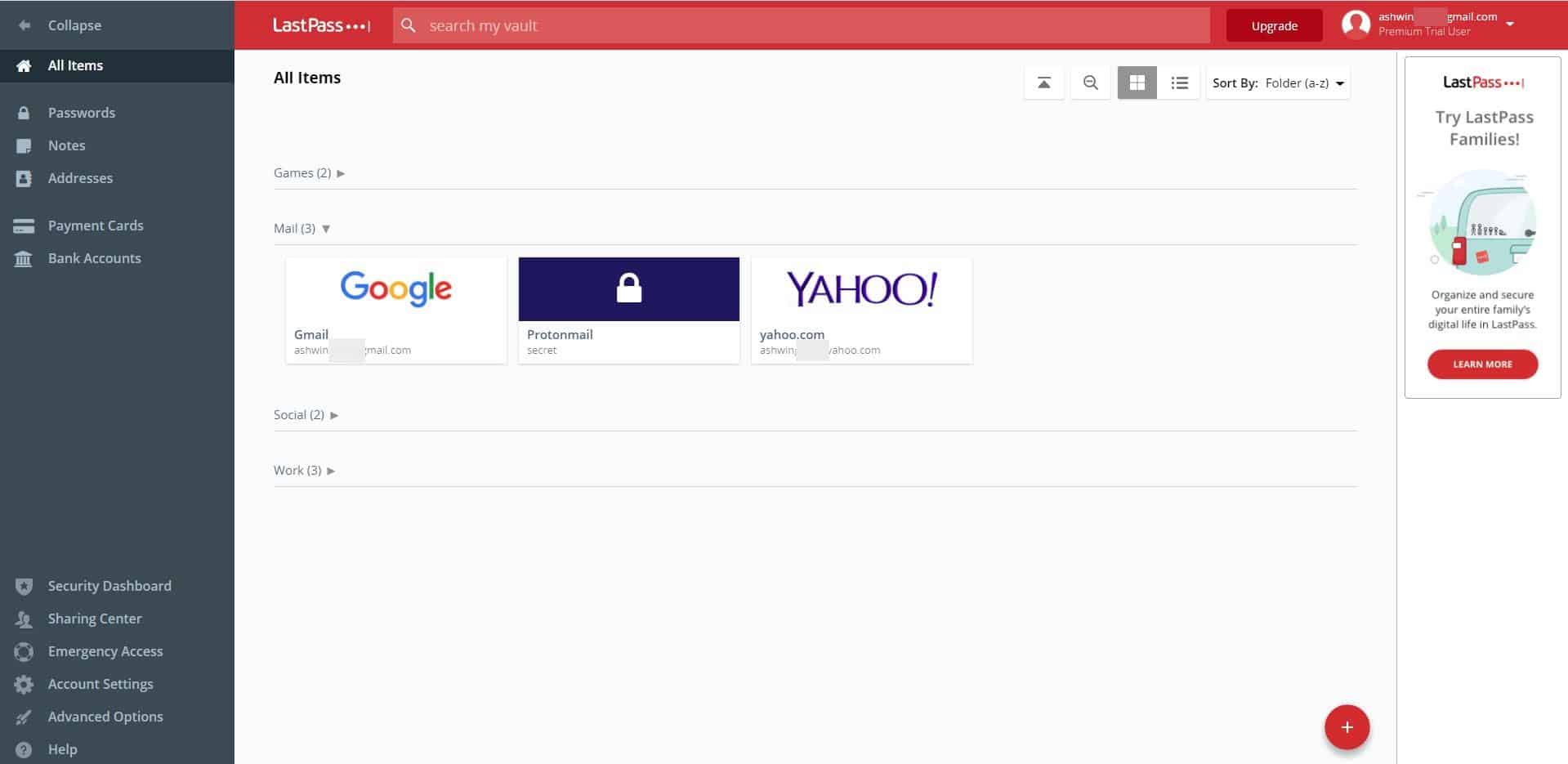
LastPass is an online password management service; customers may sign-in online to access their account using a master password. Options to protect the accounts with two-factor authentication are available as well.
LastPass customers may want to add two-factor authentication to their accounts to better protect it against unauthorized login attempts. Changing the master password may also be an option, but only if the leak comes from a third-party source and not LastPass directly.
Online password managers offer comfortable options to sync passwords across all devices, but they add another attack vector when compared to local password manager solutions such as KeePass.
Now You: do you use an online password manager, or a local one? (via Born)

















I’ve been a KeePass user for a long time. I keep the authoritative copy of KeePass on my PC, with a daily batch file that copies it to Google Drive and Dropbox (in addition to my regular backup strategy). Having a current copy in the cloud lets me get to it from my phone using KeePass-Droid. The password I use to open KeePass is quite long – 6 random words/numbers generated with the diceware method. Then you make up a little story for yourself so you remember your words. I know everybody sets things up differently, but this has been reliable for me.
Bitwarden or Keepass are better, no excuses.
I ditched Lastpass when they made cross-platform usage premium.
If you live on one computer, Keepass or any of the local solutions are the best. But if you travel or have multiple systems, and need passwords to be up-to-date across systems, or when visiting someone who lends you a desktop, then you’re probably going to have to use a cloud password storage solution — carefully. I use both Bitwarden *and* Keepass for these reasons. BTW, if you do use a “loaner” computer, install an alternative browser for your own exclusive use. I will often choose Firefox Developer edition or Brave Nightly for this purpose. Then, when I am done, I logout, clear cache, and delete the browser — all without intermixing my work with my host’s.
for years i have used password safe. nothing online. usually work off of flash drive, sandboxed. in addition to long, complicated passwords, some of the digits or symbols are phony. i copy the password, paste it to form, minimize password safe which clears the clipboard. then i delete the symbols that are phony and clik and i am in. just takes a second and no passwords i have anywhere are the correct ones. zero problems and zero worry. my kind of setup. Clas
I really like Password Safe and use it as my main password & general information system (like keeping track of various licenses & which PCs they are associated with). We use Macrium Reflect to backup the database daily.
The only thing I really liked about LastPass (as a supplement to Password Safe for online access) is when they Coud auto log you in … but more & more sites are preventing that in various ways, so they become less useful all the time.
My theory is that the “some users” affected also happened to use similar passwords on other online services. And since Lastpass is the largest online password repository out there, it stands to reason that hackers would try out the collected passwords on Lastpass as well. Until we know more specifics of these breaches, it would be well to not jump to conclusions.
Seems to be a good guess — just Hackers trying ALREADY compromised username/password combinations, with LastPass (to its credit) detecting it:
https://appleinsider.com/articles/21/12/28/lastpass-master-passwords-may-have-been-compromised
The emails were sent in error. There was no breach. https://www.howtogeek.com/776614/lastpass-says-security-alerts-were-sent-in-error/
” As previously stated, LastPass is aware of and has been investigating recent reports of users receiving e-mails alerting them to blocked login attempts.
We quickly worked to investigate this activity and at this time we have no indication that any LastPass accounts were compromised by an unauthorized third-party as a result of this credential stuffing, nor have we found any indication that user’s LastPass credentials were harvested by malware, rogue browser extensions or phishing campaigns.
However, out of an abundance of caution, we continued to investigate in an effort to determine what was causing the automated security alert e-mails to be triggered from our systems.
Our investigation has since found that some of these security alerts, which were sent to a limited subset of LastPass users, were likely triggered in error. As a result, we have adjusted our security alert systems and this issue has since been resolved.
These alerts were triggered due to LastPass’s ongoing efforts to defend its customers from bad actors and credential stuffing attempts. It is also important to reiterate that LastPass’ zero-knowledge security model means that at no time does LastPass store, have knowledge of, or have access to a users’ Master Password(s).
We will continue to regularly monitor for unusual or malicious activity and will, as necessary, continue to take steps designed to ensure that LastPass, its users and their data remain protected and secure.”
Yeah… “some users report” this means few, but makes the news because bad news are better than no news or good news. How many million Last pass users exist? and how many got “compromised”?
People are dumb and people will fall for the “Nigerian princess” money, they will send money to strangers, give their crypto wallet address to anyone, they use the same password or weak ones for important information, etc etc. So I would doubt it was like amazing hackers getting some master passwords or hacking Last pass for the information. Obviously people did something wrong installing weird crap, replying to some phasing email with their info or something like that.
Not Last pass fault, and people should stop making drama about it, like, yeah once you are plugged to network all your information can get leaked, so those are the risks, today it will be their “master password” tomorrow will be their credit card and so on, the next day will be something else.
People should not use these type of services if they can’t handle it, or should just be careful and stop blaming others for what they do, the good thing is always to have so 2FA, but some people don’t even enable that when available.
I’m not sure how many more examples of compromised cloud service providers and/or businesses holding our data we are going to need before it becomes painfully clear that this is not the way to go. If it’s in the cloud, it will be compromised. The only question is when.
Unfortunately, unless you are paying cash, you are at the mercy of just how serious the business you are buying from is about the security surrounding your credit card/debit card info, and any other personal data you may need to supply. So far the track record has been dismal with just about every large business having one or more breaches. And this lax security posture applies to all the other entities you deal with as well.
Not to mention, no system is un-hackable, period. So your data is at risk all the time.
Although there is no perfect solution, one suggestion I give to my user base is to come up with a single formula for generating a password that can be used at the majority of sites that need passwords. Now they only have to remember one thing. Done appropriately, they’ll have complex passwords that can be easily remembered.
And lest you think once the password is hacked, the attacker will now know all your passwords, it usually doesn’t work that way. Most passwords are stored hashed so the original characters are not retrievable. And for those situations where the original password is retrieved, the attacker would need to understand the significance of the numbers and letters you used.
For example – a simple formula (for a US person): take the first 3 characters of the entity asking for a password, upper case the middle letter, remember the last 4 digits of your childhood zip code, and pick two symbols to use all the time – maybe “!” and “@”. Now make your password using the 1st character of the entity+ first symbol+zip+next two chars of entity+last symbol. And if you also need something that works in situations where the entity forces you to change passwords at some interval, integrate that component in as well – perhaps (for a quarterly update) – you use yqy (1st digit of year, quarter as a letter -a,b,c,d, last digit of year). For example 2021 1st quarter would be 2a1.
Result:
amazon.com – a!2345Ma@
tdbank.com – t!2345Db@
twitter.com – t!2345Wi@
and maybe Dell, as an employee, password changed quarterly…
d!2345El@2b1
And so on.
You can make the formula as complex as you want since you only have to remember one formula.
Using a formula is clever.
You also need to have different email ids for your various accounts, otherwise, if a determined hacker got hold of one password, they can programmatically hack the pattern (e.g. characters shared with service’s url, zipcodes, etc.) and have access to all accounts tied to that email id.
You might apply a formula for naming those emails too.
Still, not sure if this is stronger than 2FA, as even if a hacker figured out an account and password (even the password manager itself), they’d have to bypass that 2nd Factor (presuming one has this turned on).
But, yes, this is “safe” from a hack of the password management service themselves.
If I was worried about that, I’d also be worried about having my money in a bank. Seems like a parallel non-zero risk.
This is simply a way to remember many different passwords instead of using a service or using the same password everywhere.
2FA or MFA is still also required for the added security it affords. Pairing the two is desirable.
This is why I never store my passwords online…because hackers always look to find a way to hack this third-party Apps..
@JonSnow, you’re not the only one to not store your passwords online. If I do myself I nevertheless have always been convinced that keeping them locally was ultimately the best privacy/security approach. Might be but, according to the following article, locally if you wish but shouldn’t be in the browser :
This nightmare incident shows why you really shouldn’t store passwords in your browser | TechRadar
https://www.techradar.com/news/this-simple-malware-shows-why-you-really-shouldnt-store-passwords-in-your-browser
For me this is a surprise. You learn every day.
Just use pen & paper or try to remember for yourself.
Sometimes, offline security > online security.
Better even : your brains, memory Dept.
She looked deep into my eyes and discovered my thoughts, credentials included.
Seriously, brains or even pen & paper are the two factors which lead to those basic and, worse, redundant passwords which bring that smile to the intruders.
If someone finds that you are storing sensitive company passwords in pen & paper where I work, you will be fired on the spot.
Shittiest security advice ever.
Company is not private space. Hackers can’t easily barge into your house yknow.
If that thing will get you fired, the company should provide way to secure credentials. What does your company do to solve this?
Trusting your passwords to third party?
LastPass is not a better service than Bitwarden, even when it was free. But this is one feature that I liked most in LastPass, basically if you try to login to LastPass from a new device/browser, it will send email containing a link which verifies login attempt. In some ways it is not ideal when you lose all your devices but then there is an option to disable it.
Now in this article, story is bit different and so I’m glad I’m not using LastPass anymore.
I’m using the Bitwarden extension (Firefox). Concerning Lastpass this is not the first time the bloated password manager faces issues, is it? I’ve used the latter several years ago and I remember a complex machinery compared to the light-weight easy to install, easy to go Bitwarden.
About online password management : I’d agree that basically keeping any confidential data online is not my cup of tea, but if I moved from Firefox’s built-in password manager to Bitwarden it is because the former has received too many comments about its deep privacy reliability, reliability which may have improved since.
+1 for Bitwarden, it’s highly configurable, secure (relatively), and being Open Source it has no ties to any company’s oversight.
I don’t think LastPass is a service to be avoided because of some specific weakness, the problem is that any password manager is an example of the long-standing issue of Convenience vs. Security. Too much of one takes away from the other and vice-versa — finding a balance between the two is really complicated.
Deleted my account some time ago and switch to another. For those who wish to do that:
https://lastpass.com/delete_account.php
Whether you are already logged on or not, it will prompt for your master password.
Online is a risk. What provisions do you have if you lose your Keepass data or it corrupts… and your backup?
Never happen, you say. I had two drives fail on the same day. Fortunately, they were alternating backup drives and my main drive stayed working. That’s two thirds of the way to lost anything I physically held. I wasn’t worried. My cloud account has everything important. Hard drives have the advantage of being accessible when internet is out. Cloud drives are also accessible from my other devices or from somebody else’s device (e.g. if the house burns down).
Moral of the story: No matter how you do it, there is risk involved. What suits one may not suit another. Your choice doesn’t make you smarter, just different.
Cloud computing has its own risks: https://www.apriorit.com/dev-blog/523-cloud-computing-cyber-attacks
Personally, I’ll stick to Keepass which I copy to several standalone drives just in case one of them goes pear-shaped.
Thanks for URL. Just deleted all my data and closed account. I transitioned to BitWarden a couple of years ago and never looked back.
KeePass is the way. None of these silly subscription password vaults are worth it.
Storing your passwords online are ya? Hey, I got a bridge to sell you, cheap!